diff --git a/.github/workflows/codespell.yml b/.github/workflows/codespell.yml
index a31ca0e10..3e3fe6be1 100644
--- a/.github/workflows/codespell.yml
+++ b/.github/workflows/codespell.yml
@@ -10,12 +10,6 @@ jobs:
GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
steps:
- uses: actions/checkout@v3
- - uses: actions/setup-node@v3
- with:
- node-version: "16"
- cache: "yarn"
- cache-dependency-path: |
- www/yarn.lock
- uses: actions/setup-python@v2
with:
python-version: "3.9"
@@ -29,10 +23,6 @@ jobs:
- name: Install Python Dependencies
run: |
pip install -r requirements.txt
- - name: Install node modules
- run: |
- cd www/
- yarn install --frozen-lockfile
- name: Run pre-commit
run: |
pre-commit install
diff --git a/www/static/.nojekyll b/website/.gitkeep
similarity index 100%
rename from www/static/.nojekyll
rename to website/.gitkeep
diff --git a/www/.gitignore b/www/.gitignore
deleted file mode 100644
index 5667f22e8..000000000
--- a/www/.gitignore
+++ /dev/null
@@ -1,23 +0,0 @@
-# Dependencies
-/node_modules
-
-# Generated OpenAPI docs
-/docs/reference/REST\ API/
-
-# Production
-/build
-
-# Generated files
-.docusaurus
-.cache-loader
-
-# Misc
-.DS_Store
-.env.local
-.env.development.local
-.env.test.local
-.env.production.local
-
-npm-debug.log*
-yarn-debug.log*
-yarn-error.log*
diff --git a/www/CNAME b/www/CNAME
deleted file mode 100644
index 795296e60..000000000
--- a/www/CNAME
+++ /dev/null
@@ -1 +0,0 @@
-www.firezone.dev
diff --git a/www/README.md b/www/README.md
deleted file mode 100644
index b759d9024..000000000
--- a/www/README.md
+++ /dev/null
@@ -1,33 +0,0 @@
-# Website
-
-This website is built using [Docusaurus 2](https://docusaurus.io/), a modern
-static website generator.
-
-## Installation
-
-```shell
-yarn
-```
-
-## Local Development
-
-```shell
-yarn run start
-```
-
-This command starts a local development server and opens up a browser window.
-Most changes are reflected live without having to restart the server.
-
-## Build
-
-```shell
-yarn run build
-```
-
-This command generates static content into the `build` directory and can be
-served using any static contents hosting service.
-
-## Deployment
-
-Deployment happens automatically when a new version is published. See the
-`publish_www` CI workflow.
diff --git a/www/babel.config.js b/www/babel.config.js
deleted file mode 100644
index e00595dae..000000000
--- a/www/babel.config.js
+++ /dev/null
@@ -1,3 +0,0 @@
-module.exports = {
- presets: [require.resolve('@docusaurus/core/lib/babel/preset')],
-};
diff --git a/www/blog/2022-07-25-release-0-5-0/index.mdx b/www/blog/2022-07-25-release-0-5-0/index.mdx
deleted file mode 100644
index d447c6aca..000000000
--- a/www/blog/2022-07-25-release-0-5-0/index.mdx
+++ /dev/null
@@ -1,115 +0,0 @@
----
-slug: release-0-5-0
-title: Release 0.5.0
-authors: [jamil]
-tags: [release, beta, acme, reverse proxy, docs]
----
-
-## Firezone 0.5 Released!
-
-As the first post on our new blog, we thought it'd be fitting to kick things
-off with a release announcement. So without further ado, we're excited to
-announce: Firezone [0.5.0 is
-here](https://github.com/firezone/firezone/releases)! It's packed with new
-features, bug fixes, and other improvements — more on that below.
-
-### User-scoped egress rules
-
-Rules can now optionally receive a user scope, limiting the rule's application
-only to devices owned by that user. This allows you to selectively allow or
-deny traffic from a particular user to an IP, set of IPs, or CIDR range.
-
-### Auto-renewed, ECDSA-backed, ACME-powered SSL certificates
-
-One of our most-requested features is now available — Firezone 0.5.0 supports
-ACME SSL certificate renewal backed by Let's Encrypt's new ECDSA key type.
-Other providers and key types are available too. See all ACME configuration
-options in our [configuration file
-reference](/docs/reference/configuration-file/).
-
-**Note**: ACME is disabled by default to remain compatible with existing
-Firezone installations. To enable, set the following in your config file:
-
-```
-default['firezone']['ssl']['acme']['enabled'] = true
-```
-
-### BYORP: Bring Your Own Reverse Proxy
-
-Want to disable Nginx and deploy Firezone under your own reverse proxy or HTTP
-load balancer? Well, now you can! We've documented the required headers and
-other configuration necessary to make this happen. [Check the
-docs](/docs/deploy/advanced/reverse-proxy) for some configuration
-examples for popular proxies. In short:
-
-Set the
-`default['firezone']['phoenix']['external_trusted_proxies']`
-configuration variable to a comma-separated list containing the proxies
-you'd like to receive forwarded requests from. If your proxy uses an
-[RFC1918 address](https://en.wikipedia.org/wiki/Private_network), add its
-IP to `default['firezone']['phoenix']['private_clients']` instead of
-`default['firezone']['phoenix']['external_trusted_proxies']`.
-Update your proxy's configuration to point to Firezone, making sure to set
-the `X-Forwarded-For` header and enable WebSocket connection upgrades.
-
-**Note:** ACME support is tied to Nginx. If you disable the bundled
-Firezone Nginx service, you'll need to provide your own SSL certificates
-(or configure ACME renewal manually).
-
-**Additional note:** If you go this route, you'll need to terminate SSL
-yourself — Firezone sets the secure attribute on all cookies and thus
-requires the downstream proxy to terminate SSL.
-
-### Runtime configuration available in the UI
-
-Some Firezone configuration settings are now configurable in the product UI
-under the Security settings. This will override anything you have set in the
-config file. Moving runtime configuration into the application itself brings us
-a step closer to Docker-based deployments (coming Soon™).
-
-### New and improved documentation
-
-Our docs have been migrated from Jekyll to [Docusaurus](https://docusaurus.io).
-Aside from all the Formatting is improved, user guides are updated and many
-pages have been edited for clarify and further detail. As an added bonus, our
-docs are feature improved search thanks to the powerful search functionality
-provided by [DocSearch by Algolia](https://docsearch.algolia.com/).
-Contributions welcome!
-
-### Red Hat and Debian package repositories
-
-If you're on one of our [supported
-distros](/docs/deploy/omnibus/supported-platforms/) (or its
-derivatives), the one-line install script will automatically install Firezone
-from our package repository and track further updates from there. This means
-your Firezone installation can be managed like any other package on your system
-and will be marked for upgrades by the same apt and yum tools you're already
-familiar with. Be sure to check the [upgrade
-notes](/docs/administer/upgrade/) prior to each
-upgrade in case there are any backwards-incompatible changes or manual steps
-involved.
-
-If you've got an existing installation and still want to add our package
-repository for easier package management, just follow the [relevant
-section](/docs/deploy/omnibus) in the manual
-install guide.
-
-### Smaller package sizes
-
-Speaking of packages, we've done a bit of work reducing the size of our Omnibus
-release package. The Nodejs, Python, Erlang, and Elixir runtimes have all been
-removed, reducing the package size by 50% and total installed size by even
-more. There's still lots of work to be done to be done here — we expect
-package sizes to be reduced even further moving forward.
-
-### Custom landing page logo
-
-In the first round of what we hope to be the start of a full-featured
-customization experience, it's now possible to change the landing page logo.
-Upload an image up to 1 MB or specify a URL to an image your end users will see
-when landing at your Firezone portal.
-
-## Conclusion
-
-That's all we've got for now. If you'd like to spin up Firezone to try it out,
-head to the [deploy guide](/docs/deploy) in our docs.
diff --git a/www/blog/2022-10-17-release-0-6-0/index.mdx b/www/blog/2022-10-17-release-0-6-0/index.mdx
deleted file mode 100644
index 3e42097ca..000000000
--- a/www/blog/2022-10-17-release-0-6-0/index.mdx
+++ /dev/null
@@ -1,126 +0,0 @@
----
-slug: release-0-6-0
-title: Release 0.6.0
-authors: [jamil]
-tags: [release, docker, saml]
----
-
-## Firezone 0.6 Released!
-
-Today, I'm excited to announce we've closed the [first public issue
-](https://github.com/firezone/firezone/issues/260) on our GitHub repository,
-more than a year after it was originally opened: Containerization support!
-We're also releasing preliminary support for SAML 2.0 identity providers
-like Okta and OneLogin.
-
-### Docker Support
-
-Docker is now the preferred method for deploying Firezone. Our [
-automatic install script](https://raw.githubusercontent.com/firezone/firezone/master/scripts/docker_install.sh)
-now uses Docker by default, and we even have a new [Docker migration script
-](https://raw.githubusercontent.com/firezone/firezone/master/scripts/docker_migrate.sh)
-that will non-destructively migrate your Omnibus-based Firezone installation
-to a Docker-based one with minimal downtime.
-
-#### How to Deploy
-
-You can now deploy Firezone complete with valid SSL certificates and a
-provisioned administrator in just a couple minutes:
-
-
-
-This also means Firezone runs on any platform that supports Docker,
-like my Mac in the video above. The automatic install script will _probably_
-barf on Windows, though. In that case, try the
-[manual install method](/docs/deploy/docker/#option-2-manual-install)!
-
-#### Why Docker?
-
-Docker offers a number of benefits over the old Omnibus-based method of deploying
-Firezone:
-
-- **Simpler, more robust upgrades**: In most cases, simply pull the latest `firezone/firezone`
- image and restart the container.
-- **Simpler configuration**: Most day-to-day configuration of Firezone can now
- be done in the web UI instead of the `/etc/firezone/firezone.rb` configuration
- file. All other configuration variables can be specified as ENV vars to the
- Firezone container.
-- **Smaller footprint**: The Firezone image weighs in at a couple dozen
- megabytes versus hundreds of megabytes for the Omnibus package.
-- **Portability**: Firezone now runs on any platform that supports Docker.
-- **Security**: Containerization providers better security isolation than
- simply running as an unprivileged local user.
-
-It also makes it easier to build and test Firezone. CI pipelines rejoice!
-No more 4-hour long compiles and intermittent build failures.
-
-#### What about Omnibus?
-
-[Chef Omnibus](https://github.com/chef/omnibus) is a Ruby-based build system
-designed to make building and distributing complex software easier. You define
-your dependencies as source tarballs, configure options, and platform-specific
-build flags, and Omnibus automatically fetches, builds, and links all your
-dependencies automagically, emitting an OS-native installer artifact when
-complete.
-
-Omnibus was a popular choice for distributing self-hosted software before
-Docker was popular -- GitLab and Mattermost are two popular self-hosted products
-that still support Omnibus-based deployments today. It's still used in many
-cases where Docker can't be used (on the \*BSDs, for example).
-
-But, since Omnibus is [effectively EOL in 2024](https://docs.chef.io/versions/)
-due to its reliance on Chef Infra Client, we've decided to deprioritize
-reliance on it, and dedicate those resources to containerized deployments
-instead.
-
-**Note**: Beginning with 0.6, Omnibus support in Firezone is **deprecated**.
-We'll be removing support for it completely in a future Firezone release.
-
-#### How to migrate from Omnibus to Docker
-
-We've written an in-depth migration guide to migrate your instance from Omnibus
-to Docker:
-
-https://www.firezone.dev/docs/administer/migrate
-
-Most instances will migrate without issue. If you're running Firezone in production
-for your team or business, [contact us](/contact/support)
-so we can better understand how we can help with your migration.
-
-### SAML 2.0
-
-Also in 0.6 is preliminary support for SAML 2.0 authentication. You'll need the
-IdP Metadata XML document to set it up. In most cases the identity provider
-will provide it for you. If not, you should be able to build it manually or
-using a tool such as
-[this nifty online IdP builder](https://www.samltool.com/idp_metadata.php).
-
-In general we recommend using OpenID Connect integration over SAML whenever possible.
-It's simpler, tends to be implemented more consistently across identity providers,
-and much easier to debug when things go wrong.
-
-Speaking of OIDC, 0.6 also introduces a couple improvements to make integrating
-your identity provider a more pleasant experience:
-
-- `auto_create_oidc_users` is now a per-provider configuration setting. Enable or disable
- autocreation of users when logging into Firezone via that provider.
-- New web form for entering OIDC details, with improved validation and error checking:
-
-
-  -
-
-#### IdP not supported?
-
-If your IdP isn't supported or you'd like to learn about your options for
-custom integrations, [contact us](/contact/support) to learn more about custom integrations.
diff --git a/www/blog/2023-01-10-first-offsite/index.mdx b/www/blog/2023-01-10-first-offsite/index.mdx
deleted file mode 100644
index b8497ab60..000000000
--- a/www/blog/2023-01-10-first-offsite/index.mdx
+++ /dev/null
@@ -1,138 +0,0 @@
----
-slug: first-offsite-retro
-title: Lessons from Firezone’s first off-site
-description: In December, Firezone organized an off-site in California. Here's what we learned.
-authors: [jason]
-tags: [company, off-site]
----
-
-My first tech job was at [Strong](https://www.strong.app/), a workout journal app that was pretty popular at the time. The founders were “digital nomads,” and the team was fully remote.
-
-Back in 2016, this was highly uncommon.
-
-We spent a lot of time creating processes to work together effectively on opposite sides of the world. One of these was meeting up in person regularly.
-
-
-
-
-
-#### IdP not supported?
-
-If your IdP isn't supported or you'd like to learn about your options for
-custom integrations, [contact us](/contact/support) to learn more about custom integrations.
diff --git a/www/blog/2023-01-10-first-offsite/index.mdx b/www/blog/2023-01-10-first-offsite/index.mdx
deleted file mode 100644
index b8497ab60..000000000
--- a/www/blog/2023-01-10-first-offsite/index.mdx
+++ /dev/null
@@ -1,138 +0,0 @@
----
-slug: first-offsite-retro
-title: Lessons from Firezone’s first off-site
-description: In December, Firezone organized an off-site in California. Here's what we learned.
-authors: [jason]
-tags: [company, off-site]
----
-
-My first tech job was at [Strong](https://www.strong.app/), a workout journal app that was pretty popular at the time. The founders were “digital nomads,” and the team was fully remote.
-
-Back in 2016, this was highly uncommon.
-
-We spent a lot of time creating processes to work together effectively on opposite sides of the world. One of these was meeting up in person regularly.
-
-
-  -
-
-At first, it was by accident. Since everyone was traveling anyway, we would coordinate being in the same city at the same time.
-
-After working in person, we quickly noticed the way we worked remotely improved. People were more comfortable sharing their ideas, better at giving constructive criticism, and happier in general.
-
-It just _felt_ better to work together in person.
-
-## Why try this at Firezone?
-
-If you believe Firezone can take a sizable bite out of the usual suspects of legacy remote access products, we’ll need to use every advantage.
-
-As a startup, our biggest advantage is the ability to move quickly as a team.
-
-This is much easier when everyone is comfortable sharing ideas and engaging in lively debate. Plus, it’s a lot more fun.
-
-So we decided to try it out. After much planning, canceled bookings, and a few long flights, our team met in Santa Rosa, California.
-
-
-
-
-
-At first, it was by accident. Since everyone was traveling anyway, we would coordinate being in the same city at the same time.
-
-After working in person, we quickly noticed the way we worked remotely improved. People were more comfortable sharing their ideas, better at giving constructive criticism, and happier in general.
-
-It just _felt_ better to work together in person.
-
-## Why try this at Firezone?
-
-If you believe Firezone can take a sizable bite out of the usual suspects of legacy remote access products, we’ll need to use every advantage.
-
-As a startup, our biggest advantage is the ability to move quickly as a team.
-
-This is much easier when everyone is comfortable sharing ideas and engaging in lively debate. Plus, it’s a lot more fun.
-
-So we decided to try it out. After much planning, canceled bookings, and a few long flights, our team met in Santa Rosa, California.
-
-
-  -
-
-## What did we do?
-
-Our itinerary included architecture planning, a multi-day hackathon, and plenty of fun activities around the Bay Area.
-
-
-
-
-
-## What did we do?
-
-Our itinerary included architecture planning, a multi-day hackathon, and plenty of fun activities around the Bay Area.
-
-
-  -
-
-The focus of the off-site was building. We each defined a few tasks that could realistically be completed by the end of the trip. So what did we work on?
-
-- A new Firezone gateway (coming in 0.8!) that will eventually allow decoupling the web portal from the WireGuard data plane. A single Firezone web portal will soon be able to manage hundreds or even thousands of little Firezone gateways securing access to their respective private resources. More details to come!
-- A [new REST API in 0.7](https://github.com/firezone/firezone/releases) to allow configuring Firezone in a more automatable way. Users love our snappy web portal, but nothing beats the power of an API for automation.
-- Various documentation improvements to improve consistency between Omnibus and Docker sections, detail logging, and implement a v1 style guide.
-
-Of course, no visit to the Bay Area would be complete without a tour of San Francisco. It rained most of the time, so we missed out on much of the picturesque hiking. But we still managed to snap some photos of the Golden Gate bridge and devour a few In-N-Out burgers.
-
-Of special mention are the team dinners. Remote companies lack that familiar bond typically formed over team lunches in the office, so we sought to recreate that when we met in person. As an added bonus, we also split cooking duties. In many ways preparing food for your teammates is like opening a pull request: make something, request feedback on it, then merge and enjoy.
-
-As someone whose culinary talents rival his passion for building security products, our resident chef [Jamil](https://twitter.com/jamilbk) led most of the culinary endeavors, including a 2-hour drive around Santa Rosa in search of live Dungeness crab.
-
-
-
-
-
-The focus of the off-site was building. We each defined a few tasks that could realistically be completed by the end of the trip. So what did we work on?
-
-- A new Firezone gateway (coming in 0.8!) that will eventually allow decoupling the web portal from the WireGuard data plane. A single Firezone web portal will soon be able to manage hundreds or even thousands of little Firezone gateways securing access to their respective private resources. More details to come!
-- A [new REST API in 0.7](https://github.com/firezone/firezone/releases) to allow configuring Firezone in a more automatable way. Users love our snappy web portal, but nothing beats the power of an API for automation.
-- Various documentation improvements to improve consistency between Omnibus and Docker sections, detail logging, and implement a v1 style guide.
-
-Of course, no visit to the Bay Area would be complete without a tour of San Francisco. It rained most of the time, so we missed out on much of the picturesque hiking. But we still managed to snap some photos of the Golden Gate bridge and devour a few In-N-Out burgers.
-
-Of special mention are the team dinners. Remote companies lack that familiar bond typically formed over team lunches in the office, so we sought to recreate that when we met in person. As an added bonus, we also split cooking duties. In many ways preparing food for your teammates is like opening a pull request: make something, request feedback on it, then merge and enjoy.
-
-As someone whose culinary talents rival his passion for building security products, our resident chef [Jamil](https://twitter.com/jamilbk) led most of the culinary endeavors, including a 2-hour drive around Santa Rosa in search of live Dungeness crab.
-
-
-  -
-
-## Lessons learned for next time
-
-Since this was our first off-site, some things could have gone better. Here’s a small list of hiccups and other things we’d do differently next time.
-
-### Turn on low power mode
-
-
-
-
-
-## Lessons learned for next time
-
-Since this was our first off-site, some things could have gone better. Here’s a small list of hiccups and other things we’d do differently next time.
-
-### Turn on low power mode
-
-
-  -
-
-If you’re booking an Airbnb, check for planned maintenance and outages! We were notified three days before arrival the power would be out during two full workdays.
-
-Fortunately, we had a small power bank and mobile hotspot with unlimited data. Unfortunately, our lead Rust engineer’s beefy Linux machine only gets a single hour of battery life on a full charge.
-
-When his machine died, we migrated to our local coffee shop, where power and WiFi were surprisingly abundant. _Editor’s note: Coffee shops in Santa Rosa are much more accommodating as a makeshift office than most in San Francisco._
-
-When you’re building software, electricity and internet are vital -- splurge for that bigger battery bank and faster hotspot!
-
-### Lumbar support is underrated
-
-You’ll sacrifice some ergonomics when you work out of an Airbnb. Put a premium on large work surfaces, open common areas, and comfortable chairs. After a few days of working hunched over on a sofa, we learned the hard way.
-
-Even better, leave heads down work until after the off-site. Instead, prioritize architecture discussions, brainstorming sessions, and design sprints.
-
-### Stock the right fuel
-
-We got carried away at Costco. Our out-of-town guests had never witnessed the spectacle of an American snack aisle. Fortunately, our talented engineers can turn Funyuns into elegant lines of Rust code (shoutout [@Gabi](https://github.com/conectado)).
-
-All jokes aside, you’ll need the right fuel for your hackathons and deep product discussions. We recommend stocking up with plenty of coffee and healthy snacks.
-
-### Plan ahead: it’ll pay off
-
-As is often the case with startups, we planned the trip on short notice. This meant many last-minute restaurant bookings and trips to the store for basic supplies.
-
-So, make a shopping list, book a few restaurants in advance, and have a backup plan. If you’re looking for a template, take a look at this [guide](https://posthog.com/handbook/company/offsites#how-to-plan-an-offsite-in-8-weeks---a-checklist) from our friends at PostHog. A great checklist is hard to beat.
-
-## What’s next?
-
-In a few short days, we:
-
-- Aligned on Firezone’s product direction
-- Made critical architecture decisions for the gateway and client apps
-- Made significant progress on a few key features
-- Bonded over great food, conversation, and Mario Kart
-
-We could have accomplished some of these over a few long Zoom calls and chat threads, but not as quickly. There’s something about mind melding over a few days of intense work that’s hard to replicate.
-
-So, will we have another off-site? Definitely!
-
-Until next time!
-
-:::info 👋 thanks for reading
-Firezone secures remote access to private resources. This post doesn't have much to do about security, networking, or a fancy new feature. But hey, our product improves the remote work experience - organizing a great off-site helps too.
-
-If you want to try it out, our [Docker install script](/docs/deploy) gets Firezone running in just a few minutes.
-:::
diff --git a/www/blog/_2022-10-21-3000-stars/index.mdx b/www/blog/_2022-10-21-3000-stars/index.mdx
deleted file mode 100644
index a6025a879..000000000
--- a/www/blog/_2022-10-21-3000-stars/index.mdx
+++ /dev/null
@@ -1,8 +0,0 @@
----
-slug: 3000-stars
-title: 3,000 GitHub Stars
-authors: [jamil]
-tags: [open-source, github]
----
-
-## 3,000 GitHub Stars
diff --git a/www/blog/_2022-12-23-yc-as-oss-company/index.mdx b/www/blog/_2022-12-23-yc-as-oss-company/index.mdx
deleted file mode 100644
index ae9e546bb..000000000
--- a/www/blog/_2022-12-23-yc-as-oss-company/index.mdx
+++ /dev/null
@@ -1,181 +0,0 @@
----
-slug: yc-oss-experience
-title: Going through YC as an open source company
-authors: [jason]
-tags: [open-source, ycombinator, company]
----
-
-# Going through YC as an open source company
-
-During YC's three-month bootcamp, your goal is simple. Make meaningful progress.
-
-In our batch, we met a company that made powdered breast milk. Multiple hospital networks as customers and $150k+ of MRR. Their problems were scaling production and FDA approval.
-
-Firezone, our company, had launched a few weeks prior on HN. We had no revenue and only a small handful of users.
-
-YC's challenge is to give advice that helps these two companies and everything in between.
-
-Open-source security is a relatively new category for YC investments. About half of the 240 open-source YC investments made by YC since S05 (17 years ago) were made in the past 2 years. Only 7 are security companies.
-
-During the batch, we had come up with our own interpretation of advice meant for traditional enterprise Saas or B2B freemium software companies. This post is my attempt at sharing what we did and learned in our journey.
-
-## How it all started
-
-As a business guy, I have long felt the business pains of a slow, clunky VPN.
-
-Slow VPN speeds are an eroding pain. One that makes every task 10% slower. Like loading my Kibana dashboard, and having to wait an extra few seconds, so I go check my email or my phone. A 2 second wait that triggers a few minutes of lost productivity. A hiccup of 1 minute at the start of every zoom call that throws off all the prep I had coming into it. “How does my mic sound?”.
-
-Big pains come from blockers. Halting the onboarding of a new contractor because our internal resources have not been segmented for least privilege. The contractor needs to build a website, but would get access to customer data and network access to production servers. There was no way we'd adopt a new tool for just this problem. In a past company we spent weeks installing a firewall appliance
-
-When I met my co-founder Jamil last summer, he showed me a solution to these problems. A new faster VPN protocol called WireGuard (read more about that here) and a modern UX built for end users. One that's easy to self-serve for IT admins, SREs, and DevOps engineers.
-
-The latter may seem like a silly differentiator, but it isn't. In the past software was sold top-down to large companies. The buyer was often not the user, so products with a laundry list of features won. They checked all the boxes.
-
-In fact, for many of Firezone's users, a VPN was a checkbox. A feature that came with their legacy firewall that's cumbersome to deploy and configure. Not to mention that firewall is now sitting in an empty office as employees move to remote work.
-
-This wasn't apparent to us at the beginning, but after we posted our project to HN, we quickly realized technical IT staff needed a product like Firezone.
-
-## Why open-source?
-
-Firezone is core IT infrastructure. It deals with network security and cryptography, and runs in pretty sensitive environments. On your employee's laptops and behind firewalls on your servers. Private data about your company and customers flow through our gateways and apps. And with remote work, almost every employee relies on it to get work done.
-
-We don't expect many organization to run such critical software without knowing what's in it.
-
-We also don't expect all organizations to leave control of their network to a third party. One that can experience outages, be targeted by hackers, or even snoop on your data themselves.
-
-So we leave it all open for you to see and make it easy to host yourself.
-
-Of course, there are other benefits of building in the open. We hired world class engineers, but with such a complex product mistakes can happen. More eyes on our code means vulnerabilities are spotted and resolved faster. As we've grown, we are even getting contributions from the community.
-
-## Why Y Combinator?
-
-After our ShowHN, a long list of feature requests appeared in our GitHub repo. A list we couldn't close alone. At least not within a reasonable amount of time.
-
-For a new product with no revenue (yet), VC funding seemed to fit. It would allow us to create something for the community and in parallel investigate the right model to build a sustainable business. As first time founders, YC seemed like a good fit. After all, they helped GitLab and Mattermost get off the ground.
-
-A brief summary for those that don't know. For a stake in your company, YC offers 3 things: capital, advice, and community.
-
-When we accepted the invitation, YC's investment was $125k for 7% of our company. A few weeks into the batch we were offered an additional $375k as an uncapped MFN safe. Lucky us! You can read more about it here.
-
-Advice comes in the form of interactive workshops and long-form posts. They are invaluable resources and often come with snappy titles, like “how not to fail”.
-
-Community is YC's magic. Thousands of past founders who can make introductions to investors, give advice, and even become users of your product. They can help you understand what “how not to fail” should mean to an open-source security company. Same with general advice on setting metrics, talking to users, and pricing.
-
-Here's some of our learnings.
-
-## Should I collect telemetry?
-
-As a VC backed-startup, probably yes.
-
-Even with a crystal ball on what users want, metrics can still help identify reliability issues and add insight to reported bugs.
-
-From a business point of view, they tell you who and how many people like your product and which features are getting used.
-
-It's a great way to focus the team on what matters.
-
-Best of all when the data-points start lining up like a hockey stick, it can get you the funding you need to build a great product.
-
-YC's advice is to set a primary metric that accurately captures the value you're delivering to users. This primary metric should be paired with secondary metrics that drive the primary metric and you can actionably move and iterate on.
-
-In case you're curious, we've set users in production as our primary metric. Our secondary metrics help add context to the growth.
-
-For example, here are 3 different graphs of our progress near demo day. Our star count, number of live instances, and number of devices. Each graph tells a slightly different story. Star count shows growing awareness in the open-source community. Instances show steady growth in actual adoption. Number of users tell us more about the deployments of Firezone. Since it outpaced the growth of instances, we knew larger teams were adopting Firezone over time and existing deployments were growing inside organizations.
-
-
-
-So, how do you measure usage? Not as simple as you think.
-
-For most software products, telemetry is a small script in the header of your website and an annoying cookie banner. Sometimes it's also a few lines of code sprinkled through the backend. Most users expect to be tracked by the hosted services they use. They may not like it, but they generally won't fuss about it.
-
-Open-source is different.
-
-Though it's getting more common, not everyone expects a self-hosted open-source project to report their usage. We had to be careful what we tracked, how we anonymized it, and how we communicate it to users.
-
-We spoke to a few other open source companies we respected. Here's the advice we received.
-
-- Explain why you do it: Document what you track, how it's stored, and what you use it for. We took heavy inspiration from companies like Mattermost and made our own page in our documentation.
-- Make it clear and easy to opt-out: To make it simple for users, we created a deployment script that streamlines the install process. In the script we explicitly ask for permission and make it easy to switch off later directly in the UI.
-- Don't unnecessarily expose user data to third parties: Those annoying cookie banners on websites you visit generally mean one thing. You're being tracked, and your information is being sent to third party tools like CRMs and ad platforms. If you've signed up for an account and checked the box for terms and conditions, you're agreeing to that as well. With Firezone, we try to use open-source and self-hosted products whenever possible. This includes our telemetry platform as well.
-
-So, now we know about users in aggregate.
-
-But, our product is early and legacy VPNs are painful in many ways. We need more information to prioritize what to build first. The best way to do that is by talking to users.
-
-## We don't know who our users are
-
-“Write code and talk to users” is consistently echoed during YC.
-
-A great summary why is in “do things that don't scale”. I recommend reading the article, but it boils down to this:
-
-You often build the initial product for yourself. The MVP is usually not good enough - it's never quite right. You should get it in front of users as soon as it provides utility so you can get feedback to iterate and improve.
-
-The average user of Firezone is technical. Usually a system admin, IT manager, or DevOps engineer. They're fully capable of setting up Firezone and reading our docs to figure out what the product can do.
-
-We get frequent GitHub issues and Discourse posts pointing at issues or desired features. Sometimes they'll even fix it for us!
-
-However, Firezone does not require a valid email to sign up. It's hosted entirely on your infrastructure. It would be weird to lock anything behind a signup.
-
-I would be equally distasteful to hijack discussions with requests for a user interview.
-
-So, to generate more conversations, we increased the surface area of how users can reach us. It's important to note who you're getting feedback from as well. Often for developer facing products, the person that's deploying the product is not the person who decides what to use, what the budget is, or even the only one benefiting from it.
-
-Firezone ties into security playbooks, compliance requirements, hiring plans for contractors globally, and risk planning from risk departments.
-
-Here's how we're currently reaching them:
-Source Types of conversations Who we speak with
-Install script email (opt-in) Deployment issues ICs, IT Managers
-Slack Group and Discourse threads Deployment and configuration issues ICs, IT Managers
-GitHub issues Feature requests ICs, IT Managers, IT Leaders
-Inbound sales leads Required functionality, pricing discussions CTO, CISO, IT Leaders
-Outbound leads Problem discovery, product roadmap planning CTO, CISO, IT Leaders
-
-One example of why it's important to dig deeper involves a request to “load a custom logo”. When we got on a Zoom call, we would uncover a group of re-sellers who want to white-label our product with their clients. Turns out they have other requirements they'd be happy to pay for if we had them.
-
-These conversations helped make the product better and form our view on our business model.
-
-This leads into the final piece of advice from YC, pricing.
-
-## Paying user feedback > free users
-
-Figuring out your pricing model and generating meaningful revenue is the great filter between early MVPs and successful companies.
-
-The main question however is when.
-
-With limited resources, generating revenue is almost always a tradeoff. Less growth, slower development of features, and the potential to ruin a perfectly good story for investors. Queue Silicon Valley:
-
-
-
-So, when to figure out revenue?
-
-For B2B software, the answer should probably be “right now”.
-
-Steering early user conversations toward pricing tells you if the product is viable and solves a big enough pain. YC echoes this advice.
-
-A startup I previously worked at, Kite, failed partly because we punted the question of “will people pay?” too many times. It was an AI powered co-pilot, an early iteration of GitHub Copilot.
-
-When we finally tried, it was clear the product needed to evolve to generate meaningful revenue. By the time we realized that, it was too late. Adam, the founder of Kite and an investor in Firezone, recently open-sourced the codebase and wrote a great post-mortem:
-
-https://www.kite.com/blog/product/kite-is-saying-farewell/
-
-For self-hosted open-source software the answer is not as clear.
-
-[As a self-hosted security product, layering feature gating logic into the core product is problematic. Feature flags are complex to write, and even harder to maintain as our product evolves. Being critical infrastructure for remote work, we also don't want your company to come to a halt when your credit card expires. There's more to say here, but I'll leave this to a future deep-dive from my co-founder, Jamil.]
-
-So, similar to other successful open-source projects, our early goal was to grow the community. During YC we focused on building out the core parts of our platform, driving adoption, and optimizing for learning from our users. One of things we wanted to learn was how to build a business around Firezone.
-
-As usage grew, a pattern emerged when talking to users. Our largest deployments all started with an individual spinning Firezone up without ever speaking to us.
-
-As usage grew, they reached out to inquire about additional features and services.
-
-As we continue to develop our pricing model, we want to ensure the following:
-- Individuals and hobbyists can use Firezone for free
-- Small teams can use Firezone for free (if they support it themselves)
-- Large organizations can run a PoC without any calls with sales
-
-If this sounds familiar, it's similar to how GitLab thinks about their pricing. We're obviously big fans.
-
-## Paying it forward (still writing this part...)
-
-[not sure how to end this]
-
-- https://a16z.com/2019/10/04/open-source-from-community-to-commercialization/
diff --git a/www/blog/_2023-02-13-ebpf-firewall/index.mdx b/www/blog/_2023-02-13-ebpf-firewall/index.mdx
deleted file mode 100644
index 37b255358..000000000
--- a/www/blog/_2023-02-13-ebpf-firewall/index.mdx
+++ /dev/null
@@ -1,544 +0,0 @@
----
-slug: ebpf-firewall
-title: How We Built an eBPF-based General Purpose Packet Filter
-authors: [conectado]
-tags: [ebpf, firewall, rust, aya]
----
-
-## Introduction
-
-As part of our migration to multi-site in Firezone the VPN and Firewall were rewritten in Rust. As part of that rewrite we decided to improve how we were handling the firewall.
-
-In the past we were using [nftables](https://netfilter.org/projects/nftables/), the way we did this was shelling-out to the console and use the nft cli.
-
-This has a number of problems, for one shelling out can be prone to error, inefficient and hard to unit-test, also there's no Rust lib to call into nftables and even the existing libraries in C can be too complicated to use. Furthermore, we were limited to nft's data structure which meant doing a lot of work to not mess up the rules, this in turn made doing improvements really slow.
-
-So after a lot of consideration we decided that creating our own firewall using [ebpf](https://ebpf.io/).
-
-## eBPF
-
-We will briefly go into what eBPF is, however If you want a more detailed introduction you can take a look at [the official introduction](https://ebpf.io/what-is-ebpf).
-
-### What is eBPF
-
-eBPF stands for extended Berkeley Packet Filter, which is an upgrade from BPF(Berkely Packet Filter), while eBPF brings a lot of improvements over BPF the gist is the same, run user-defined packet-filtering code inside of the kernel as part of the packet processing pipeline.
-
-This is an oversimplification because eBPF programs can be hooked into multiple different events in the kernel but for our intent and purposes, we just want to hook into the packet-classifier pipeline.
-
-
-### How the kernel safely run user-defined code
-
-eBPF has its own ISA and there is a runtime for said ISA in the kernel (JIT'd), the instructions allows calling into parts of the kernel that we might need and gives us the necessary context to process a given packet.
-
-Furthermore, to prevent crashes in the kernel and hogging out resources before an eBPF program gets loaded into the kernel it goes through a verification process, a verificator program sets a bunch of limitations to the program to prevent situations like infinite loops and crashes:
-
-* It sets an upper-bound for the number of times a loop within the code can run (or strictly prohibits them in older kernel versions).
-* An upper-bound in the number of instructions the program can execute in total.
-* Keeps tracks of read/writes to know that you are using valid memory locations.
-
-To know the specifics of how it works, you should take a look at the [kernel's doc](https://www.kernel.org/doc/Documentation/networking/filter.txt) and even more in details you can take a look at [cillium's docs](https://docs.cilium.io/en/stable/bpf/#bpf-guide).
-
-### Packet pipeline
-
-Without getting into the specific an eBPF program can be hooked into different hooks on the packet processing pipeline for the linux kernel. eBPF allows hooking into [XDP](https://www.iovisor.org/technology/xdp) which runs just after the packet reached the NIC. However, [XDP doesn't support Wireguard](https://lore.kernel.org/netdev/20200813195816.67222-1-Jason@zx2c4.com/T/) since wireguard doesn't have L2 headers, for more info on this see [this fly.io blogpost](https://fly.io/blog/bpf-xdp-packet-filters-and-udp/#xdp).
-
-Fret not, for eBPF can also hook into the network's [TC Ingress](https://man7.org/linux/man-pages/man8/tc-bpf.8.html) that doesn't make any assumption about the packet's header.
-
-### Maps
-
-Maps are the kernel structures that enables us to share data between the eBPF kernel program and a user-space program. Maps, as their name suggest allow us to store relations as `Key -> Value` the types of maps offered by eBPF is limited however there are a lot of them. For our use case we just need to concern us with [trie](https://github.com/torvalds/linux/blob/master/kernel/bpf/lpm_trie.c) and hash maps.
-
-Again I reffer to [cillium's documentation](https://docs.cilium.io/en/v1.12/bpf/#maps) for more information.
-
-### TL;DR
-
-eBPF is an ISA and its corresponding implementation for user-defined programs that run in the kernel that we used for filtering packets, however, the programs we can run have some severe limitations so that they don't crash the kernel.
-
-## Firewall
-
-With this in mind we wanted to write a Firewall that can allow/deny traffic based on the following:
-
-- Destination CIDR
-- Possibly multiple sender IPs
-- Possibly a port-range along associated with UDP, TCP or both
-
-We took an additional simplification to make the implementation easier(we will see why further along), you can configure the firewall to allow all or deny all, then when a packet match a rule it'd invert that behavior:
-> A firewall that denies all traffic with a rule for destination `10.20.30.40`, would deny all traffic from all sources to all destinations except for traffic for `10.20.30.40` from any destination.
-
-### Aya
-
-When implementing the firewall in Rust two possible libraries:
-
-- [aya](https://github.com/aya-rs/aya)
-- [redbpf](https://github.com/foniod/redbpf)
-
-`redbpf` relies on bindings to `libbpf` while `aya` only relies on `libc`, also, aya's tooling seems to be easier to use and it uses cargo's target for ebpf instead of relying on `cargo bpf` which is easier when writing the Firewall as a library.
-
-So taking that into account we went with `aya`.
-
-Normally, the way an aya program is structured: we have a user-space crate that loads the eBPF program and is a proxy between it and the user and a crate that targets eBPF which has more limitations(such as being `no-std`).
-
-Aya normally expects to be run as a binary and not as a library or as a separate userspace/bpf library, so we needed to do some tuning for the template to be able to run it as we wanted, a single library crate that you include.
-
-More about how we did this in a separate blogpost.
-
-### Architecture
-
-** TODO: ** Add diagrams
-
-So, with this information, we can plan an architecture.
-
-Thinking about the steps how ideally, the firewall would work:
-
-1. A packet arrives
-2. The source is classified into a `user_id` if any
-3. Check existing rules if match
-4. Decide REJECT/ACCEPT action based on previous step
-
-Let's go over how we can achieve this.
-
-### The anatomy of a rule
-
-As we said before a rule has 3 components
-
-- Associated `user_id`
-- Destination CIDR
-- Destination Port Ranges
-
-The `user_id` is an arbitrary name, the idea is that a single rule can associate multiple source ips, so we can associate a rule with an `id` and then we can update the `id` association with multiple ips during runtime.
-
-Rules need to be stored in eBPF's maps, that way we can update the maps during run-time from userspace to be able to update the rules.
-
-And we need to be able to lookup those maps using information from the incoming packets.
-
-The way we did this is having the following maps:
-
-- `SOURCE_MAP`: A hashmap mapping source ips to `id`s
-- `RULE_MAP`: A trie mapping CIDR to port ranges
-
-** Note: ** There is actually an ipv6 and ipv4 version for both of those maps, so we have 4 maps in total.
-
-### `SOURCE_MAP`
-
-The `SOURCE_MAP` is really simple, we store the mapping IP -> ID, so we can associate let's say IP `10.10.10.3` and `10.10.10.4` with id `4` and `10.1.1.5` with id `7`. Now when a packet comes from `10.10.10.4` we lookup the map and get `4` and for `10.1.1.5` we get `7`.
-
-### `RULE_MAP`
-
-[Tries](https://en.wikipedia.org/wiki/Trie) are prefix-matching trees, they let us efficiently store and lookup ranges grouped by prefix. For ips this is exactly how [CIDR](https://en.wikipedia.org/wiki/Classless_Inter-Domain_Routing) works.
-
-The nodes in the trie tree correspond to a an ip and a prefix, so `10.5.8.0/24` corresponds to to the bits of `10.5.8.0` and 24 bits so that node would match with `10.5.8.0` to `10.5.8.255` but if you store `10.5.8.128/25` that'd match with `10.5.8.128` to `10.5.8.255`.
-
-Both nodes, `10.5.8.0/24 and `10.5.8.128/25`, could be stored but the `lookup` method in the `trie` only allows us to find the node with the most specific match. so `10.5.8.110` would match with `10.5.8.0/24` and `10.5.8.170` would match with `10.5.8.128/25` but we would never learn that it also match with `10.5.8.0/24`.
-
-So a trie would give us a way to associate CIDR with... something? The question is what's this "something".
-
-Well, we don't need an action, since we know the action is just inverting the default one. What we still lack to know if the rule matches is a port-range(With its protocol) and the associated `id`.
-
-However, if we store multiple rules, all associated with the same destination IP we would need to lookup all the rules for each packet and this is incredibly inefficient. But there's a solution, we can easily store the ID and protocol in the key!
-
-So instead of storing as the key `10.5.8.0/24` and when we do lookup we get all the other data we store as the key `6.TCP.10.5.8.0` and the prefix instead of 24 is 33, 4 extra bytes for the id, 1 for the protocol(We use the protocol number).
-
-If this is still unclear we will see more when we discuss the specific of the code, just know that we store the id and protocol as part of the key, so we can compose the number `id.protocol.ip` with the prefix and look that up.
-
-The result value will be the port range, which we have to map to the port of the incoming packet, we will talk more about how we do this below.
-
-For sources with no id we use `0` as the id. For non-TCP/UDP packets, we store the rule in both the TCP and UDP key and look up TCP(arbitrarily) but only match for port 0 (which we use to encode all ports), for rules with both protocols, we store the rule twice once for TCP and once for UDP.
-
-### Another look at the ip matching
-
-Let's look again at the steps when a packet arrives:
-
-1. Packet arrives
-2. Lookup destination IP get an ID or use 0
-3. Create the lookup key (ID.PROTOCOL.DESTINATION_IP)
-4. Use the lookup key to get the port ranges
-5. Lookup the port in the port ranges
-6. REJECT/ACCEPT based on that
-
-Basically, this is a high-level on how the ebpf side works. Now, let's take a look at the userspace-side.
-
-### Userspace
-
-Now that we know how we access the rules let's see how we need to store them from userspace.
-
-Remember, that the Trie map provided by the kernel, for search, only have its lookup method that let us know the longest prefix. So let's think about this scenario:
-
-We store these rules:
-
-```
-10.0.0.0/24 port 80 Allowed
-10.0.0.1/32 port 23 Allowed
-```
-
-now a packet comes from 10.0.0.1 with port 80, and we use the Trie lookup method to see if it's allowed, the lookup method returns all the ports from the longest prefix, meaning port 23 is allowed but the packet has port 80 so it's denied.
-
-This is of course, erroneous because IP `10.0.0.1` is part of range `10.0.0.0/24` which has port 80 is allowed. So what do we do about this? Changing the trie API is impossible without modifying the kernel and even if we submit the PR for that the new API would only be included in the latest kernels.
-
-We could lookup manually each range before deciding an action, so when packet with `10.0.0.1` comes we check `10.0.0.1/32` then `10.0.0.0/31` the `10.0.0.0/30` so on and so on before taking a decision. The performance of this is bad, specially if we are going to do that about each packet.
-
-What we can do, is from userspace present an API that when adding rules, it propagates them to all pertinent ips, so:
-
-If you have:
-
-```
-10.0.0.1/32 port 23 Allowed
-```
-
-and you want to add `10.0.0.0/24 port 80`, the API would automatically propagate it to:
-
-```
-10.0.0.1/32 port 23, 80 Allowed
-10.0.0.0/24 port 80 Allowed
-```
-
-and if you have:
-
-```
-10.0.0.0/24 port 80 Allowed
-```
-
-then you add `10.0.0.1/32 port 23` the api actually updates the rules like:
-
-```
-10.0.0.1/32 port 23, 80 Allowed
-10.0.0.0/24 port 80 allowed
-```
-
-So you see, how the api automatically propagates rules to have a consistent table.
-
-### Port Ranges
-
-## At last, CODE!
-
-With the previous section you should have a clear picture at the architecture of what we built and why but from now on we will **need** to see code.
-
-Will not go over how Aya's API or eBPF code works, hopefully it will be self-evident with the explanations until now enough to understand the gist of it.
-
-### Code structure
-
-We have 3 crates in our repo:
-* Userspace
-* Common (This contains the codebase shared by both)
-* eBPF
-
-From userspace we have the `Firewall` which is the entrypoint for everything. You first initialize and load a firewall by calling `Firewall::new` for a given interface.
-
-The most interesting part is the `RuleTracker` this is an internal struct (which is almost directly exposed by `Firewall` using pass-through methods), this is where the magic happens, userspace `Rule`s are converted into valid eBPF `Rule`, we keep track of them to propagate them and obviously add them to the maps in eBPF.
-
-So let's see how that happens.
-
-### A rule
-
-#### eBPF
-
-So, how does a rule looks in reality:
-
-```rs
-#[repr(C)]
-pub struct RuleStore {
- // Sorted non-overlapping ranges
- // bit 0-15: port-start
- // bit 16-31: port-end
- rules: [u32; MAX_RULES],
- rules_len: u32,
-}
-```
-
-Structs in eBPF need to be `repr(C)`, which just means it uses C's ABI, eBPF structs need to be simple array of bytes (with no padding to convince the eBPF verifier that we never read uninitialized memory).
-
-So, let's analyze this struct, this is the value that we are going to store in the map. This only need to be the port-ranges (remember that the key already stores the `id`, `destination`, `protocol`).
-
-So we store the rules as an array of port-ranges. With a range being the inclusive intervals of the port covered by the rule. we use the first 2 bytes for the starting port and the last 2 bytes for the ending port.
-
-Then in `rules_len` we just have the number of rules stored (the rest is padded with 0).
-
-#### Useraspace
-
-From userspace we have many different structs that represent a rule at different stage of processing, these are not complex but we have different parts of the code that require different information for what to do with the rule.
-
-But for user-facing API a rule looks like:
-
-```rs
-pub enum Rule {
- V4(RuleImpl),
- V6(RuleImpl),
-}
-```
-
-Alright, not very interesting without knowing how `RuleImpl` looks:
-
-```rs
-pub struct RuleImpl {
- pub(crate) id: Option,
- pub(crate) dest: T,
- pub(crate) port_range: Option,
-}
-```
-
-So we see that a rule in userspace contains all the information for a rule but the important part is:
-
-```rs
-pub(crate) struct PortRange {
- pub(crate) ports: RangeInclusive,
- pub(crate) proto: Protocol,
-}
-```
-
-Cool! Use rust's `RangeInclusive` to represent ports with `u16` as a port and a `Protocol` (which is just an enum to indicate the kind of rule)
-
-So when we do `Firewall::add_rule(rule)` we need to make it arrive to eBPF with the struct we previously saw.
-
-We also need to propagate correctly like we saw in the previous userspace architecture, so let's walk through how does that work!
-
-#### Translation
-
-So at some point we want to add the `rule` to the eBPF map. For that, we first need to determine the key that we are going to use.
-
-That's easy:
-
-```rs
-// Convert the id to big endian bytes
-let key_id = id.to_be_bytes();
-
-// Convert the ip to bytes
-let key_cidr = ip.normalize().as_octets();
-let mut key_data = [0u8; N];
-
-// Store in a new `key_data`: protocol.id.ip
-let (left_key_data, cidr) = key_data.split_at_mut(5);
-let (id, prot) = left_key_data.split_at_mut(4);
-prot[0] = proto;
-id.copy_from_slice(&key_id);
-cidr.copy_from_slice(key_cidr.as_ref());
-
-// Calculate the prefix and return the eBPF key
-Key::new(
- u32::from(ip.prefix()) + (left_key_data.len() * 8) as u32,
- key_data,
-)
-```
-
-Cool, this is the key that we are going to insert to the eBPF map
-
-Now we need to calculate the value that we are going to insert.
-
-Remember that the `rule` field in the ebpf `RuleStore` looked like this:
-
-```rs
- rules: [u32; MAX_RULES],
-```
-
-So we have a maximum number of rules, one reason for this, is that we need to store an array, we can't store a vector (we can't share heap allocations). But this number is also limited by the lookup algorithm.
-
-Remember, that the verifier imposes a limit on the number of times a loop can run, so if we linearly search all ranges we were getting capped at around 1000 intervals we would reach the upper limit on loops, this is okay, this would be enough but we can do better.
-
-If we can somehow sort the port ranges we could do binary search, this means less loop iterations and faster lookup in general. But how to sort it exactly?
-
-This is actually the reason each rule, doesn't have an Accept/Reject instead it only inverts the default behavior, also why we store all UDP rules together and TCP rules together.
-
-To sort, we just need to merge intervals. Merging intervals is a well studied problem that can be done in `O(N)` and since it's from userspace we could afford worse performance.
-
-Mergining intervals just means that from the existing intervals we create a series of new non-overlapping intervals that cover the same area and we sort them.
-
-So `[10-20, 15-30, 6-9]` would become `[6-9, 10-30]`. Then we can do binary search on this interval. We will see below the specific of that but this is the code to get the intervals from a series of port ranges:
-
-
-```rs
-fn resolve_overlap(port_ranges: &mut [&PortRange]) -> Vec<(u16, u16)>
-{
- let mut res = Vec::new();
-
- // Sort the ranges by the starting potr
- port_ranges.sort_by_key(|p| p.ports.ports.start());
-
- Get the first prot into the result
- if let Some(range) = port_ranges.first() {
- res.push((*range.ports.ports.start(), *range.ports.ports.end()));
- } else {
- return res;
- }
-
- // Go through each range
- for range in &port_ranges[1..] {
- let last_res = res
- .last_mut()
- .expect("should contain at least the first element of port_ranges");
-
- // If the new range fall within the last one extend it
- if last_res.1 >= *range.ports.ports.start() {
- *last_res = (last_res.0, last_res.1.max(*range.ports.ports.end()));
- // Otherwise, add a new range
- } else {
- res.push((*range.ports.ports.start(), *range.ports.ports.end()));
- }
- }
-
- res
-}
-```
-
-As you see doing this is really easy. We still need to do some small work to get it from `Vec<(u16, u16)>` to `[u32; RULE_MAX]` but you can imagine it's pretty trivial.
-
-### Propagating Rules
-
-Then the last interesting part from userspace is how to propagate the rules.
-
-So when you insert a new rule, you need to keep track of all the rules that would include it, since when a lookup happen it would return the new rule because it's more specific. So basically the gist is traverse all rules and include all the port ranges from those "above" in the new rule.
-
-```rs
-(The code here requires a lot of context on the specifics of how we did this but it's nothing interesting, check if you can rewrite it in a "context-free" way)
-```
-
-And then there could be more specific rules that are included in the new rule, you need to propagate the new rule (the port-range) to those.
-
-```rs
-(The code here requires a lot of context on the specifics of how we did this but it's nothing interesting, check if you can rewrite it in a "context-free" way)
-```
-
-### eBPF Rule lookup
-
-
-When a packet arrives we first extract the network headers (source, destination, protocol and port).
-
-```rs
- let (source, dest, proto) = load_ntw_headers(&ctx, version)?;
- let port = get_port(&ctx, version, proto)?;
- let class = source_class(source_map, source);
- let action = get_action(class, dest, rule_map, port, proto);
-```
-
-Then, we get the source id:
-
-```rs
-unsafe fn source_class(
- source_map: &HashMap<[u8; N], u32>,
- address: [u8; N],
-) -> Option<[u8; 4]> {
- source_map.get(&address).map(|x| u32::to_be_bytes(*x))
-}
-```
-Then we try to calculate what action we should take:
-
-```rs
-fn get_action(
- group: Option<[u8; 4]>,
- address: [u8; N],
- rule_map: &LpmTrie<[u8; M], RuleStore>,
- port: u16,
- proto: u8,
-) -> i32 {
- let proto = if port == 0 { TCP } else { proto };
- let default_action = get_default_action();
-
- let rule_store = rule_map.get(&Key::new((M * 8) as u32, get_key(group, proto, address)));
- if is_stored(&rule_store, port) {
- return invert_action(default_action);
- }
-
- if group.is_some() {
- let rule_store = rule_map.get(&Key::new((M * 8) as u32, get_key(None, proto, address)));
- if is_stored(&rule_store, port) {
- return invert_action(default_action);
- }
- }
-
- default_action
-}
-```
-
-Here we try to extract the action from the existing map, we get the `RuleStore` by constructing the key corresponding to that packet:
-
-```rs
-fn get_key(
- group: Option<[u8; 4]>,
- proto: u8,
- address: [u8; N],
-) -> [u8; M] {
- let group = group.unwrap_or_default();
- let mut res = [0; M];
- let (res_left, res_address) = res.split_at_mut(5);
- let (res_group, res_proto) = res_left.split_at_mut(4);
- res_group.copy_from_slice(&group);
- res_proto[0] = proto;
- res_address.copy_from_slice(&address);
- res
-}
-```
-And most importantly we lookup in the rulestore if the `port` that arrived exists.
-
-```rs
- pub fn lookup(&self, val: u16) -> bool {
- // 0 means all ports
- if self.rules_len > 0 {
- // SAFETY: We know that rules_len < MAX_RULES
- if start(*unsafe { self.rules.get_unchecked(0) }) == 0 {
- return true;
- }
- }
-
- // We test for 0 in all non tcp/udp packets
- // it's worth returning early for those cases.
- if val == 0 {
- return false;
- }
-
- // Reimplementation of partition_point to satisfy verifier
- let mut size = self.rules_len as usize;
- // appeasing the verifier
- if size >= MAX_RULES {
- return false;
- }
- let mut left = 0;
- let mut right = size;
- #[cfg(not(feature = "user"))]
- let mut i = 0;
- while left < right {
- let mid = left + size / 2;
-
- // This can never happen but we need the verifier to believe us
- let r = if mid < MAX_RULES {
- // SAFETY: We are already bound checking
- *unsafe { self.rules.get_unchecked(mid) }
- } else {
- return false;
- };
- let cmp = start(r) <= val;
- if cmp {
- left = mid + 1;
- } else {
- right = mid;
- }
- size = right - left;
-
- #[cfg(not(feature = "user"))]
- {
- i += 1;
- // This should never happen, here just to satisfy verifier
- if i >= MAX_ITER {
- return false;
- }
- }
- }
-
- if left == 0 {
- false
- } else {
- let indx = left - 1;
- if indx >= MAX_RULES {
- return false;
- }
- // SAFETY: Again, we are already bound checking
- end(*unsafe { self.rules.get_unchecked(indx) }) >= val
- }
- }
-```
-
-If 0 is included we consider it to be "all ports".
-
-Otherwise we basically do binary search on the starting port to see the maximum starting port that is less than the port we are checking for and then we check for the ending port to see if it's more than the port we are checking.
-
-Binary search for the maximum that keeps a predicate as true is an algorithm that already exists in Rust called partition point, we needed to reimplement it to make it compatible with eBPF due to the verifier limitations.
-
-## Conclusion
-
-ebpf is awesome but complicated! (something along those lines) and future for firezone rearchitecture and check it out!
diff --git a/www/blog/authors.yml b/www/blog/authors.yml
deleted file mode 100644
index 189b7469c..000000000
--- a/www/blog/authors.yml
+++ /dev/null
@@ -1,16 +0,0 @@
-jamil:
- name: Jamil Bou Kheir
- title: Co-founder
- url: https://github.com/jamilbk
- image_url: https://www.gravatar.com/avatar/3c8434814eec26026718e992322648c8
-
-jason:
- name: Jason Gong
- title: Co-founder
- url: https://github.com/gongjason
- image_url: https://www.gravatar.com/avatar/d688e2280a36287f61c4426334dce065
-
-conectado:
- name: Gabriel Steinberg
- title: Senior Rust Engineer
- url: https://github.com/conectado
diff --git a/www/docs/README.mdx b/www/docs/README.mdx
deleted file mode 100644
index a7ccb391c..000000000
--- a/www/docs/README.mdx
+++ /dev/null
@@ -1,49 +0,0 @@
----
-title: Overview
-sidebar_position: 1
----
-
-[Firezone](/) is an open-source secure remote access
-platform that can be deployed on your own infrastructure in minutes.
-Use it to **quickly and easily** secure access to
-your private network and internal applications from an intuitive web UI.
-
-
-
-These docs explain how to deploy, configure, and use Firezone.
-
-## Quick start
-
-1. [Deploy](deploy): A step-by-step walk-through setting up Firezone.
- Start here if you are new.
-1. [Authenticate](authenticate): Set up authentication using local
- email/password, OpenID Connect, or SAML 2.0 and optionally enable
- TOTP-based MFA.
-1. [Administer](administer): Day to day administration of the Firezone
- server.
-1. [User Guides](user-guides): Useful guides to help you learn how to use
- Firezone and troubleshoot common issues. Consult this section
- after you successfully deploy the Firezone server.
-
-## Common configuration guides
-
-1. [Split Tunneling](./user-guides/use-cases/split-tunnel):
- Only route traffic to certain IP ranges through the VPN.
-1. [Setting up a NAT Gateway with a Static IP](./user-guides/use-cases/nat-gateway):
- Configure Firezone with a static IP address to provide
- a single egress IP for your team's traffic.
-1. [Reverse Tunnels](./user-guides/use-cases/reverse-tunnel):
- Establish tunnels between multiple peers.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
-
-## Contribute to firezone
-
-We deeply appreciate any and all contributions to the project and do our best to
-ensure your contribution is included. To get started, see [CONTRIBUTING.md
-](https://github.com/firezone/firezone/blob/master/CONTRIBUTING.md).
-
-
-
-
diff --git a/www/docs/administer/README.mdx b/www/docs/administer/README.mdx
deleted file mode 100644
index a7830cb43..000000000
--- a/www/docs/administer/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Administer
-sidebar_position: 4
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/administer/backup.mdx b/www/docs/administer/backup.mdx
deleted file mode 100644
index cf5aaa934..000000000
--- a/www/docs/administer/backup.mdx
+++ /dev/null
@@ -1,101 +0,0 @@
----
-title: Backup and Restore
-sidebar_position: 4
----
-
-Firezone can be safely backed up and restored in a couple of minutes under
-most circumstances.
-
-:::info
-This guide is written for Firezone deployments using **Docker Engine** on **Linux** only.
-:::
-
-Unless your hosting provider supports taking live VM snapshots, you'll
-need to stop Firezone before backing it up. This ensures the Postgres data
-directory is in a consistent state when the backup is performed. Backing up a
-running Firezone instance will **most likely** result in data loss when restored;
-you have been warned.
-
-After stopping Firezone, backing up Firezone is mostly a matter of copying the relevant
-[files and directories](/docs/reference/file-and-directory-locations/) to a location of your
-choosing.
-
-See the steps below for specific examples for Docker and Omnibus.
-
-
-
-
-### Backup
-
-For Docker-based deployments, this will consist of backing up the `$HOME/.firezone`
-directory along with the Postgres data directory, typically located at
-`/var/lib/docker/volumes/firezone_postgres-data` on Linux if you're using the default
-Docker compose template.
-
-1. Stop Firezone (warning: this **will** disconnect any users connected to the VPN):
-
-```
-docker compose -f $HOME/.firezone/docker-compose.yml down
-```
-
-2. Copy relevant files and folders. If your made any customizations to `/etc/docker/daemon.json`
- (for example, for IPv6 support), be sure to include that in the backup as well.
-
-```
-tar -zcvfp $HOME/firezone-back-$(date +'%F-%H-%M').tgz $HOME/.firezone /var/lib/docker/volumes/firezone_postgres-data
-```
-
-A backup file named `firezone-back-TIMESTAMP.tgz` will then be stored in `$HOME/`.
-
-### Restore
-
-1. Copy the files back to their original location:
-
-```
-tar -zxvfp /path/to/firezone-back.tgz -C / --numeric-owner
-```
-
-2. Optionally, enable Docker to boot on startup:
-
-```
-systemctl enable docker
-```
-
-
-
-
-### Backup
-
-1. Stop Firezone (warning: this **will** disconnect any users connected to the VPN):
-
-```
-firezone-ctl stop
-```
-
-2. Copy relevant files and folders:
-
-```
-tar -zcvfp $HOME/firezone-back-$(date +'%F-%H-%M').tgz /var/opt/firezone /opt/firezone /usr/bin/firezone-ctl /etc/systemd/system/firezone-runsvdir-start.service /etc/firezone
-```
-
-A backup file named `firezone-back-TIMESTAMP.tgz` will then be stored in `$HOME/`.
-
-### Restore
-
-1. Copy the files back to their original location:
-
-```
-tar -zxvfp /path/to/firezone-back.tgz -C / --numeric-owner
-```
-
-2. Reconfigure Firezone to ensure configuration is applied to the host system:
-
-```
-firezone-ctl reconfigure
-```
-
-
-
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/administer/debug-logs.mdx b/www/docs/administer/debug-logs.mdx
deleted file mode 100644
index 834d875c6..000000000
--- a/www/docs/administer/debug-logs.mdx
+++ /dev/null
@@ -1,54 +0,0 @@
----
-title: Debug Logs
-sidebar_position: 8
-description:
- Docker deployments of Firezone generate and store debug logs to a JSON
- file on the host machine.
----
-
-:::note
-This article is written for Docker based deployments of Firezone.
-:::
-
-Docker deployments of Firezone consist of 3 running containers:
-
-| Container | Function | Example logs |
-| --------- | ------------- | --------------------------------------------- |
-| firezone | Web portal | HTTP requests received and responses provided |
-| postgres | Database | |
-| caddy | Reverse proxy | |
-
-Each container generates and stores logs to a JSON file on the host
-machine. These files can be found at
-`var/lib/docker/containers/{CONTAINER_ID}/{CONTAINER_ID}-json.log`.
-
-Run the `docker compose logs` command to view the log output from all running
-containers. Note, `docker compose` commands need to be run in the Firezone
-root directory. This is `$HOME/.firezone` by default.
-
-See additional options of the `docker compose logs` command
-[here](https://docs.docker.com/engine/reference/commandline/compose_logs/).
-
-## Managing and configuring Docker logs
-
-By default, Firezone uses the `json-file` logging driver without
-[additional configuration](https://docs.docker.com/config/containers/logging/json-file/).
-This means logs from each container are individually stored in a file format
-designed to be exclusively accessed by the Docker daemon. Log rotation is not
-enabled, so logs on the host can build up and consume excess storage space.
-
-For production deployments of Firezone you may want to configure how logs are
-collected and stored. Docker provides
-[multiple mechanisms](https://docs.docker.com/config/containers/logging/configure/)
-to collect information from running containers and services.
-
-Examples of popular plugins, configurations, and use cases are:
-
-- Export container logs to your SIEM or observability platform (i.e.
- [Splunk](https://docs.docker.com/config/containers/logging/splunk/)
- or
- [Google Cloud Logging](https://docs.docker.com/config/containers/logging/gcplogs/)
- )
-- Enable log rotation and max file size.
-- [Customize log driver output](https://docs.docker.com/config/containers/logging/log_tags/)
- with tags.
diff --git a/www/docs/administer/migrate.mdx b/www/docs/administer/migrate.mdx
deleted file mode 100644
index b9bb0d9a6..000000000
--- a/www/docs/administer/migrate.mdx
+++ /dev/null
@@ -1,74 +0,0 @@
----
-title: Migrate to Docker
-sidebar_position: 2
----
-
-# Migrate from Omnibus to Docker
-
-Chef Infra Client, the configuration system Chef Omnibus relies on, has been
-[scheduled for End-of-Life in 2024](https://docs.chef.io/versions/).
-Firezone 0.7 will be the last version to offer Omnibus-based deployments.
-Users are encouraged to migrate to a Docker-based deployment of Firezone using
-this guide.
-
-Existing Omnibus-based deployments of Firezone will continue to function as-is,
-but no officially supported RedHat or Debian packages will be published for
-Firezone 0.8 and above.
-
-See this [GitHub issue tracking discussion
-](https://github.com/firezone/firezone/issues/1304) for more details.
-
-Follow this guide to migrate from an Omnibus-based deployment to a Docker-based
-deployment. In most cases this can be done with minimal downtime and without
-requiring you to regenerate WireGuard configurations for each device.
-
-Heavily customized deployments (such as those using an external database or
-custom reverse proxy) will likely need extra troubleshooting and manual
-steps taken to perform a successful migration.
-
-Take a look at the [migration script source
-](https://github.com/firezone/firezone/blob/master/scripts/docker_migrate.sh)
-to get a detailed idea of the steps involved.
-
-Estimated time to complete: **2 hours**.
-
-## Steps to migrate
-
-1. **Back up** your server. This ensures you have a working state to roll back to
- in case anything goes terribly wrong. At a _bare minimum_ you'll want to back up the
- [file and directories Firezone uses
- ](/docs/reference/file-and-directory-locations/), but we recommend taking a full
- snapshot of your VPS if possible.
-1. Ensure you're running the latest version of Firezone. See our [upgrade guide
- ](/docs/administer/upgrade/) if not.
-1. Install the latest version of [**Docker**
- ](https://docs.docker.com/engine/install/) and [Docker Compose
- ](https://docs.docker.com/compose/install/linux/#install-compose)
- for your OS. **Docker Compose version 2 or higher is required**.
- We recommend using Docker Server for Linux. Docker Desktop will work too, but is not
- preferred for production use cases at this time because it rewrites packets under
- some conditions and may cause unexpected issues with Firezone.
-1. Download and run the migration script:
-
-```bash
-bash <(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/docker_migrate.sh)
-```
-
-This will ask you a few questions, then attempt to migrate your installation to
-Docker. If all goes well, your Firezone instance should be running with Docker, data intact.
-
-## Rolling back
-
-If anything goes wrong, you can abort the migration by simply bringing the Docker
-services down and the Omnibus ones back up:
-
-```bash
-docker-compose down
-sudo firezone-ctl start
-```
-
-If you've found a bug, please [open a GitHub issue](https://github.com/firezone/firezone/issues) with the error output and
-any steps needed to reproduce.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/administer/regen-keys.mdx b/www/docs/administer/regen-keys.mdx
deleted file mode 100644
index c9abd1250..000000000
--- a/www/docs/administer/regen-keys.mdx
+++ /dev/null
@@ -1,67 +0,0 @@
----
-title: Regenerate Secret Keys
-sidebar_position: 7
----
-
-When you install Firezone, secrets are generated for encrypting database
-fields, securing WireGuard tunnels, securing cookie sessions, and more.
-
-If you're looking to regenerate one or more of these secrets, it's possible
-to do so using the same bootstrap scripts that were used when installing
-Firezone.
-
-## Regenerate secrets
-
-:::warning
-Replacing the `DATABASE_ENCRYPTION_KEY` will render all encrypted data in the
-database useless. This **will** break your Firezone install unless you are
-starting with an empty database. You have been warned.
-:::
-
-:::caution
-Replacing `GUARDIAN_SECRET_KEY`, `SECRET_KEY_BASE`, `LIVE_VIEW_SIGNING_SALT`,
-`COOKIE_SIGNING_SALT`, and `COOKIE_ENCRYPTION_SALT` will reset all browser
-sessions and REST API tokens.
-:::
-
-Use the procedure below to regenerate secrets:
-
-
-
-
-Navigate to the Firezone installation directory, then:
-
-```bash
-mv .env .env.bak
-docker run firezone/firezone bin/gen-env > .env
-```
-
-Now, move desired env vars from `.env.bak` back to `.env`, keeping
-the new secrets intact.
-
-
-
-
-## Regenerate WireGuard private key
-
-:::warning
-Replacing the WireGuard private key will render all existing device configs
-invalid. Only do so if you're prepared to also regenerate device configs
-after regenerating the WireGuard private key.
-:::
-
-To regenerate WireGuard private key, simply move or rename the private key file.
-Firezone will generate a new one on next start.
-
-
-
-
-```bash
-cd $HOME/.firezone
-docker-compose stop firezone
-sudo mv firezone/private_key firezone/private_key.bak
-docker-compose start firezone
-```
-
-
-
diff --git a/www/docs/administer/troubleshoot.mdx b/www/docs/administer/troubleshoot.mdx
deleted file mode 100644
index 01e722646..000000000
--- a/www/docs/administer/troubleshoot.mdx
+++ /dev/null
@@ -1,153 +0,0 @@
----
-title: Troubleshoot
-sidebar_position: 6
-description: Troubleshoot common connectivity and configuration issues with Firezone's WireGuard®-based secure access platform.
----
-
-This guide documents common configuration and connectivity issues. For
-any problems that arise, a good first bet is to check the Firezone logs.
-
-
-
-
-Each container stores logs as a JSON file on the host machine. These can be shown with the
-`docker logs {CONTAINER}` command. Log files are found at
-`var/lib/docker/containers/{CONTAINER_ID}/{CONTAINER_ID}-json.log` by default.
-
-See [debug logs](../debug-logs) for additional details.
-
-
-
-
-## Application crash loop preventing config changes
-
-In cases where the application is crash looping because of corrupt, inaccessible, or
-invalid OIDC or SAML configuration in the DB, you can try clearing the affected fields.
-
-For example, to clear OIDC configs:
-
-
-
-
-```text
-psql -d firezone -h 127.0.0.1 -U postgres -c "UPDATE configurations SET openid_connect_providers = '[]'"
-```
-
-Similarly, to clear SAML configs:
-
-```text
-psql -d firezone -h 127.0.0.1 -U postgres -c "UPDATE configurations SET saml_identity_providers = '[]'"
-```
-
-
-
-
-## Debugging WebSocket connectivity issues
-
-The Web UI requires a secure websocket connection to function.
-If a secure websocket connection can't be established, you'll see a red dot
-indicator in the upper-right portion of the Firezone web UI and a corresponding
-message when you hover over it:
-
-```text
-Secure websocket not connected! ...
-```
-
-If you're accessing Firezone using the same URL defined in your
-`EXTERNAL_URL` variable from above, the issue is likely to be in your reverse
-proxy configuration. Ensure your reverse proxy has WebSocket support enabled
-for Firezone. If you're using the default Caddy reverse proxy, WebSocket
-is enabled and configured automatically.
-
-In most cases, you'll find clues in one or more of the following locations:
-
-
-
-## Debugging WireGuard connectivity issues
-
-Most connectivity issues with Firezone are caused by other `iptables` or
-`nftables` rules which interfere with Firezone's operation. If you have rules
-active, you'll need to ensure these don't conflict with the Firezone rules.
-
-### Internet connectivity drops when tunnel is active
-
-If your Internet connectivity drops whenever you activate your WireGuard
-tunnel, you should make sure that the `FORWARD` chain allows packets
-from your WireGuard clients to the destinations you want to allow through
-Firezone.
-
-If you're using `ufw`, this can be done by making sure the default routing
-policy is `allow`:
-
-```text
-ubuntu@fz:~$ sudo ufw default allow routed
-Default routed policy changed to 'allow'
-(be sure to update your rules accordingly)
-```
-
-A `ufw` status for a typical Firezone server might look like this:
-
-```text
-ubuntu@fz:~$ sudo ufw status verbose
-Status: active
-Logging: on (low)
-Default: deny (incoming), allow (outgoing), allow (routed)
-New profiles: skip
-
-To Action From
--- ------ ----
-22/tcp ALLOW IN Anywhere
-80/tcp ALLOW IN Anywhere
-443/tcp ALLOW IN Anywhere
-51820/udp ALLOW IN Anywhere
-22/tcp (v6) ALLOW IN Anywhere (v6)
-80/tcp (v6) ALLOW IN Anywhere (v6)
-443/tcp (v6) ALLOW IN Anywhere (v6)
-51820/udp (v6) ALLOW IN Anywhere (v6)
-```
-
-## Admin login isn't working
-
-If the password for the account with email `DEFAULT_ADMIN_EMAIL` isn't working, you can
-reset it using the process below.
-
-
-
-
-First change directory to your Firezone installation directory
-(`$HOME/.firezone` by default), then run the `bin/create-or-reset-admin` script
-to reset the admin user's password. The password for the user specified by
-`DEFAULT_ADMIN_EMAIL`
-in `$HOME/.firezone/.env` will be reset to the `DEFAULT_ADMIN_PASSWORD` variable.
-
-```shell
-cd $HOME/.firezone
-docker compose exec firezone bin/create-or-reset-admin
-```
-
-**Note**: If local authentication is disabled, resetting the admin user's
-password will not re-enable it.
-
-
-
-
-## Re-enable local authentication via CLI
-
-If you've configured an [OIDC](/docs/authenticate/oidc/) or [SAML](/docs/authenticate/saml/)
-provider, you can consider disabling local authentication for additional security.
-
-If, however, issues arise with your identity provider integration, it's possible you
-could be locked out of the admin portal. To re-enable local authentication so
-you can log in and resolve the issue, you can temporarily re-enable local authentication
-via the [REST API](/docs/reference/rest-api/configurations).
-
-If that's not an option, you can re-enable local authentication by
-running the following commands on the host of your Firezone instance:
-
-```shell
-cd $HOME/.firezone
-docker compose exec postgres psql -U postgres -h 127.0.0.1 -d firezone -c "UPDATE configurations SET local_auth_enabled = 't'"
-```
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/administer/uninstall.mdx b/www/docs/administer/uninstall.mdx
deleted file mode 100644
index 7c4bd94fc..000000000
--- a/www/docs/administer/uninstall.mdx
+++ /dev/null
@@ -1,37 +0,0 @@
----
-title: Uninstall
-sidebar_position: 5
----
-
-Firezone can be uninstalled using the steps below.
-
-:::warning
-This will irreversibly destroy ALL Firezone data and can't be undone.
-:::
-
-
-
-
-For docker-based deployments, simply bring the firezone services down,
-then delete the working directory where you installed the Firezone docker
-files (`$HOME/.firezone` by default):
-
-```bash
-# default install dir
-installDir=$HOME/.firezone
-docker compose -f $installDir/docker-compose.yml down -v
-rm -rf $installDir
-```
-
-
-
-
-To completely remove Omnibus-based deployments of Firezone run the [uninstall.sh
-script](https://github.com/firezone/firezone/blob/master/scripts/omnibus-uninstall.sh):
-
-```bash
-sudo /bin/bash -c "$(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/omnibus-uninstall.sh)"
-```
-
-
-
diff --git a/www/docs/administer/upgrade.mdx b/www/docs/administer/upgrade.mdx
deleted file mode 100644
index ee2504b12..000000000
--- a/www/docs/administer/upgrade.mdx
+++ /dev/null
@@ -1,283 +0,0 @@
----
-title: Upgrade
-sidebar_position: 3
----
-
-Upgrading Firezone will pause all VPN sessions and temporarily bring
-down the web UI.
-
-:::info
-Automatic rollbacks are still under development. We recommend backing up
-relevant [files and folders](/docs/reference/file-and-directory-locations/)
-before upgrading in case anything goes wrong.
-:::
-
-Follow the steps below to upgrade Firezone:
-
-
-
-
-1. Change to your Firezone installation directory, by default `$HOME/.firezone`:
-
-```
-cd $HOME/.firezone
-```
-
-1. If your `.env` file has a `VERSION` variable, update it to the desired version.
- By default `latest` is assumed if not set. This variable is read in newer versions
- of the docker-compose.yml template to populate the `image:` key for the `firezone`
- service.
-1. Update service images:
-
-```
-docker compose pull
-```
-
-1. Re-up the services (**warning: this will restart updated services**):
-
-```
-docker compose up -d
-```
-
-
-
-
-1. If not setup already, install our package repository based on your distro's
- package format:
-
-- [deb packages](https://cloudsmith.io/~firezone/repos/firezone/setup/#formats-deb)
-- [rpm packages](https://cloudsmith.io/~firezone/repos/firezone/setup/#formats-rpm)
-
-1. Upgrade the `firezone` package using your distro's package manager.
-1. Run `firezone-ctl reconfigure` to pick up the new changes.
-1. Run `firezone-ctl restart` to restart services.
-
-
-
-
-If you hit any issues, please let us know by [filing an
-issue](https://github.com/firezone/firezone/issues/new/choose).
-
-## Upgrading to 0.7.x
-
-Firezone 0.7.0 introduces a new [REST API](/docs/reference/rest-api/) that allows administrators
-to automate much of the day to day configuration of Firezone.
-
-The REST API `/v0/configuration` endpoint supersedes some of the previous environment
-variables used for WireGuard server configuration.
-
-If you're running Firezone < 0.6, we recommend updating to the latest
-0.6.x release **before** upgrading to 0.7. This will ensure any environment variables
-are properly parsed and migrated into the DB as runtime `configurations`.
-
-**Note**: Omnibus deployments are deprecated in 0.7.x and will be removed in Firezone
-0.8 and above. We recommend [migrating your installation](/docs/administer/migrate/) to
-Docker if you haven't done so already.
-
-## Upgrading to >= 0.6.12
-
-### WIREGUARD\_\* env vars
-
-Firezone 0.6.12 moves the `WIREGUARD_ALLOWED_IPS`, `WIREGUARD_PERSISTENT_KEEPALIVE`,
-and `WIREGUARD_DNS` environment variables to the database to be configured in the
-UI at `/settings/client_defaults`. If the corresponding value at
-`/settings/client_defaults` was empty, the environment variable's value was used to
-populate the field.
-
-This is a small step in our quest to move more runtime configuration from environment
-variables to the DB.
-
-### `AUTH_OIDC_JSON` config
-
-Similar to the `WIREGUARD_*` env vars above, the `AUTH_OIDC_JSON` env var has similarly
-been moved to the database and can be configured at `/settings/site`. In Firezone 0.7 this
-is now configurable via the [REST API](/docs/reference/rest-api/configurations) as well.
-
-### Fix IPv6
-
-0.6.12 fixes IPv6 routing within Docker networks.
-To enable, add IPv6 addresses to your `$HOME/.firezone/docker-compose.yml` by setting the following fields:
-
-```yaml
-services:
- firezone:
- networks:
- firezone-network:
- ipv6_address: 2001:3990:3990::99
-
-# ...
-networks:
- firezone-network:
- ipam:
- config:
- - subnet: 2001:3990:3990::/64
- - gateway: 2001:3990:3990::1
-```
-
-You also need to update the Docker daemon to enable IPv6. See our [IPv6 guide](/docs/deploy/docker/#step-4-enable-ipv6-optional) for more info.
-
-## Upgrading from 0.5.x to 0.6.x
-
-Firezone 0.6 introduces **Docker support**, SAML 2.0 authentication,
-more granular user provisioning options, and a slew of minor improvements and bugfixes.
-
-### Migrate to Docker
-
-Docker is now the preferred way to deploy and manage Firezone. See the [migration
-guide](/docs/administer/migrate/) to migrate today. In most cases this can be done in a few minutes
-using our automatic migration script.
-
-### Update Configuration
-
-Some configuration variables have recently moved to the DB in order to be configurable
-at runtime. Check the [configure guide](/docs/deploy/configure/) for more information.
-
-## Upgrading from < 0.5.0 to >= 0.5.0
-
-0.5.0 introduces a few breaking changes and configuration updates that will need
-to be addressed. Read more below.
-
-### Bundled Nginx non_ssl_port (HTTP) requests removed
-
-0.5.0 and above removes the `force_ssl` and `non_ssl_port` settings for
-Nginx. SSL is required for Firezone to function; if you're using (or would like
-to use) your own reverse proxy, we recommend disabling the bundle Nginx service
-by setting `default['firezone']['nginx']['enabled'] = false` and pointing your
-reverse proxy directly to the Phoenix app on port 13000 (by default).
-
-Read more about setting up a custom reverse proxy
-[here](/docs/deploy/advanced/reverse-proxy/).
-
-### ACME protocol support
-
-0.5.0 introduces ACME protocol support for automatically renewing SSL
-certificates with the bundled Nginx service. To enable,
-
-- Make sure `default['firezone']['external_url']` contains a valid FQDN that
- resolves to your server's public IP address.
-
-- Ensure port `80/tcp` is reachable
-
-- Enable ACME protocol support with
- `default['firezone']['ssl']['acme']['enabled'] = true` in your config file.
-
-### Overlapping egress rule destinations
-
-Firezone 0.5.0 removes the ability to add rules with overlapping destinations.
-When upgrading to 0.5.0, our migration script will automatically detect these
-cases and **keep only the rules whose destination encompasses the other rule**.
-If this is OK, **there is nothing you need to do**.
-
-Otherwise, we recommend modifying your ruleset to eliminate these cases before
-upgrading.
-
-### Preconfigured Okta and Google SSO
-
-Firezone 0.5.0 removes support for the old-style Okta and Google SSO
-configuration in favor of the new, more flexible OIDC-based configuration.
-If you have any configuration under the
-`default['firezone']['authentication']['okta']` or
-`default['firezone']['authentication']['google']` keys, **you need to migrate
-these to our OIDC-based configuration using the guide below.**
-
-#### Existing Google OAuth configuration
-
-Remove these lines containing the old Google OAuth configs from your configuration
-file located at `/etc/firezone/firezone.rb`
-
-```rb
-default['firezone']['authentication']['google']['enabled']
-default['firezone']['authentication']['google']['client_id']
-default['firezone']['authentication']['google']['client_secret']
-default['firezone']['authentication']['google']['redirect_uri']
-```
-
-Then, follow the instructions [here](/docs/authenticate/oidc/google/) to configure Google
-as an OIDC provider.
-
-#### Existing Okta OAuth configuration
-
-Remove these lines containing the old Okta OAuth configs from your configuration
-file located at `/etc/firezone/firezone.rb`
-
-```rb
-default['firezone']['authentication']['okta']['enabled']
-default['firezone']['authentication']['okta']['client_id']
-default['firezone']['authentication']['okta']['client_secret']
-default['firezone']['authentication']['okta']['site']
-```
-
-Then, follow the instructions [here](/docs/authenticate/oidc/okta/) to configure Okta as
-an OIDC provider.
-
-## Upgrading from 0.3.x to >= 0.3.16
-
-Follow the instructions below based on your current version and setup:
-
-### I have an existing OIDC integration
-
-Upgrading to >= 0.3.16 requires the `offline_access` scope for some OIDC providers
-to obtain a refresh token.
-This ensures Firezone syncs with the identity provider and VPN access is terminated
-once the user is removed. Previous versions of Firezone do not have this capability.
-Users who are removed from your identity provider will still have active VPN sessions
-in some cases.
-
-For OIDC providers that support the `offline_access` scope, you will need to add
-`offline_access` to the `scope` parameter of your OIDC config. The
-Firezone configuration file can be found at `/etc/firezone/firezone.rb` and requires
-running `firezone-ctl reconfigure` to pick up the changes.
-
-If Firezone is able to successfully retrieve the refresh token, you will see
-the **OIDC Connections** heading in the user details page of the web UI for
-users authenticated through your OIDC provider.
-
-
-
-If this does not work, you will need to delete your existing OAuth app
-and repeat the OIDC setup steps to
-[create a new app integration](/docs/authenticate/oidc/) .
-
-### I have an existing OAuth integration
-
-Prior to 0.3.11, Firezone used pre-configured OAuth2 providers. Follow the
-instructions [here](/docs/authenticate/oidc/) to migrate to OIDC.
-
-### I have not integrated an identity provider
-
-No action needed. You can follow the instructions
-[here](/docs/authenticate/oidc)
-to enable SSO through an OIDC provider.
-
-## Upgrading from 0.3.1 to >= 0.3.2
-
-The configuration option `default['firezone']['fqdn']` has been removed in favor
-of `default['firezone']['external_url']`. Please set this to the
-publicly-accessible URL of your Firezone web portal. If left unspecified it will
-default to `https://` + the FQDN of your server.
-
-Reminder, the configuration file can be found at `/etc/firezone/firezone.rb`.
-For an exhaustive list of configuration variables and their descriptions, see the
-[configuration file reference](/docs/reference/configuration-file).
-
-## Upgrading from 0.2.x to 0.3.x
-
-Starting with version 0.3.0, Firezone no longer stores device private
-keys on the Firezone server. Any existing devices should continue to function
-as-is, but you will not be able to re-download or view these configurations in
-the Firezone Web UI.
-
-## Upgrading from 0.1.x to 0.2.x
-
-Firezone 0.2.x contains some configuration file changes that will need to be
-handled manually if you're upgrading from 0.1.x. Run the commands below as root
-to perform the needed changes to your `/etc/firezone/firezone.rb` file.
-
-```bash
-cp /etc/firezone/firezone.rb /etc/firezone/firezone.rb.bak
-sed -i "s/\['enable'\]/\['enabled'\]/" /etc/firezone/firezone.rb
-echo "default['firezone']['connectivity_checks']['enabled'] = true" >> /etc/firezone/firezone.rb
-echo "default['firezone']['connectivity_checks']['interval'] = 3_600" >> /etc/firezone/firezone.rb
-firezone-ctl reconfigure
-firezone-ctl restart
-```
diff --git a/www/docs/authenticate/README.mdx b/www/docs/authenticate/README.mdx
deleted file mode 100644
index a989df386..000000000
--- a/www/docs/authenticate/README.mdx
+++ /dev/null
@@ -1,93 +0,0 @@
----
-title: Authenticate
-sidebar_position: 3
----
-
-Firezone supports the following authentication methods:
-
-1. [Local email/password (default)](local-auth)
-1. [SSO authentication via OpenID Connect](oidc)
-1. [SSO authentication via SAML 2.0](saml)
-
-:::note
-If your Identity Provider doesn't work with the methods listed above,
-[contact us](/contact/support) about a custom integration.
-:::
-
-## Integrate an SSO provider
-
-We've included instructions on how to set up Firezone with several popular
-identity providers using our Generic OIDC integration:
-
-- [Okta](oidc/okta)
-- [Azure Active Directory](oidc/azuread)
-- [Google](oidc/google)
-- [Onelogin](oidc/onelogin)
-- [JumpCloud](saml/jumpcloud)
-- [Keycloak](oidc/keycloak)
-- [Zitadel](oidc/zitadel)
-- [Auth0](oidc/auth0)
-
-If your identity provider is not listed above, but has a generic OIDC or SAML
-connector, please consult their documentation to find instructions on obtaining
-the configuration settings required. Instructions for setting up Firezone with any
-generic OIDC provider can be found [here](oidc).
-
-Open a [Github issue](https://github.com/firezone/firezone/issues)
-to request documentation or submit a pull request to add documentation for your
-provider.
-
-### The OIDC redirect URI
-
-For each OIDC provider a corresponding URL is created for redirecting to
-the configured provider's sign-in URL. The URL format is `https://firezone.example.com/auth/oidc/CONFIG_ID`
-where `CONFIG_ID` is the OIDC Config ID for that particular provider.
-
-For example, the OIDC config below:
-
-
-
-
-
-If you’re booking an Airbnb, check for planned maintenance and outages! We were notified three days before arrival the power would be out during two full workdays.
-
-Fortunately, we had a small power bank and mobile hotspot with unlimited data. Unfortunately, our lead Rust engineer’s beefy Linux machine only gets a single hour of battery life on a full charge.
-
-When his machine died, we migrated to our local coffee shop, where power and WiFi were surprisingly abundant. _Editor’s note: Coffee shops in Santa Rosa are much more accommodating as a makeshift office than most in San Francisco._
-
-When you’re building software, electricity and internet are vital -- splurge for that bigger battery bank and faster hotspot!
-
-### Lumbar support is underrated
-
-You’ll sacrifice some ergonomics when you work out of an Airbnb. Put a premium on large work surfaces, open common areas, and comfortable chairs. After a few days of working hunched over on a sofa, we learned the hard way.
-
-Even better, leave heads down work until after the off-site. Instead, prioritize architecture discussions, brainstorming sessions, and design sprints.
-
-### Stock the right fuel
-
-We got carried away at Costco. Our out-of-town guests had never witnessed the spectacle of an American snack aisle. Fortunately, our talented engineers can turn Funyuns into elegant lines of Rust code (shoutout [@Gabi](https://github.com/conectado)).
-
-All jokes aside, you’ll need the right fuel for your hackathons and deep product discussions. We recommend stocking up with plenty of coffee and healthy snacks.
-
-### Plan ahead: it’ll pay off
-
-As is often the case with startups, we planned the trip on short notice. This meant many last-minute restaurant bookings and trips to the store for basic supplies.
-
-So, make a shopping list, book a few restaurants in advance, and have a backup plan. If you’re looking for a template, take a look at this [guide](https://posthog.com/handbook/company/offsites#how-to-plan-an-offsite-in-8-weeks---a-checklist) from our friends at PostHog. A great checklist is hard to beat.
-
-## What’s next?
-
-In a few short days, we:
-
-- Aligned on Firezone’s product direction
-- Made critical architecture decisions for the gateway and client apps
-- Made significant progress on a few key features
-- Bonded over great food, conversation, and Mario Kart
-
-We could have accomplished some of these over a few long Zoom calls and chat threads, but not as quickly. There’s something about mind melding over a few days of intense work that’s hard to replicate.
-
-So, will we have another off-site? Definitely!
-
-Until next time!
-
-:::info 👋 thanks for reading
-Firezone secures remote access to private resources. This post doesn't have much to do about security, networking, or a fancy new feature. But hey, our product improves the remote work experience - organizing a great off-site helps too.
-
-If you want to try it out, our [Docker install script](/docs/deploy) gets Firezone running in just a few minutes.
-:::
diff --git a/www/blog/_2022-10-21-3000-stars/index.mdx b/www/blog/_2022-10-21-3000-stars/index.mdx
deleted file mode 100644
index a6025a879..000000000
--- a/www/blog/_2022-10-21-3000-stars/index.mdx
+++ /dev/null
@@ -1,8 +0,0 @@
----
-slug: 3000-stars
-title: 3,000 GitHub Stars
-authors: [jamil]
-tags: [open-source, github]
----
-
-## 3,000 GitHub Stars
diff --git a/www/blog/_2022-12-23-yc-as-oss-company/index.mdx b/www/blog/_2022-12-23-yc-as-oss-company/index.mdx
deleted file mode 100644
index ae9e546bb..000000000
--- a/www/blog/_2022-12-23-yc-as-oss-company/index.mdx
+++ /dev/null
@@ -1,181 +0,0 @@
----
-slug: yc-oss-experience
-title: Going through YC as an open source company
-authors: [jason]
-tags: [open-source, ycombinator, company]
----
-
-# Going through YC as an open source company
-
-During YC's three-month bootcamp, your goal is simple. Make meaningful progress.
-
-In our batch, we met a company that made powdered breast milk. Multiple hospital networks as customers and $150k+ of MRR. Their problems were scaling production and FDA approval.
-
-Firezone, our company, had launched a few weeks prior on HN. We had no revenue and only a small handful of users.
-
-YC's challenge is to give advice that helps these two companies and everything in between.
-
-Open-source security is a relatively new category for YC investments. About half of the 240 open-source YC investments made by YC since S05 (17 years ago) were made in the past 2 years. Only 7 are security companies.
-
-During the batch, we had come up with our own interpretation of advice meant for traditional enterprise Saas or B2B freemium software companies. This post is my attempt at sharing what we did and learned in our journey.
-
-## How it all started
-
-As a business guy, I have long felt the business pains of a slow, clunky VPN.
-
-Slow VPN speeds are an eroding pain. One that makes every task 10% slower. Like loading my Kibana dashboard, and having to wait an extra few seconds, so I go check my email or my phone. A 2 second wait that triggers a few minutes of lost productivity. A hiccup of 1 minute at the start of every zoom call that throws off all the prep I had coming into it. “How does my mic sound?”.
-
-Big pains come from blockers. Halting the onboarding of a new contractor because our internal resources have not been segmented for least privilege. The contractor needs to build a website, but would get access to customer data and network access to production servers. There was no way we'd adopt a new tool for just this problem. In a past company we spent weeks installing a firewall appliance
-
-When I met my co-founder Jamil last summer, he showed me a solution to these problems. A new faster VPN protocol called WireGuard (read more about that here) and a modern UX built for end users. One that's easy to self-serve for IT admins, SREs, and DevOps engineers.
-
-The latter may seem like a silly differentiator, but it isn't. In the past software was sold top-down to large companies. The buyer was often not the user, so products with a laundry list of features won. They checked all the boxes.
-
-In fact, for many of Firezone's users, a VPN was a checkbox. A feature that came with their legacy firewall that's cumbersome to deploy and configure. Not to mention that firewall is now sitting in an empty office as employees move to remote work.
-
-This wasn't apparent to us at the beginning, but after we posted our project to HN, we quickly realized technical IT staff needed a product like Firezone.
-
-## Why open-source?
-
-Firezone is core IT infrastructure. It deals with network security and cryptography, and runs in pretty sensitive environments. On your employee's laptops and behind firewalls on your servers. Private data about your company and customers flow through our gateways and apps. And with remote work, almost every employee relies on it to get work done.
-
-We don't expect many organization to run such critical software without knowing what's in it.
-
-We also don't expect all organizations to leave control of their network to a third party. One that can experience outages, be targeted by hackers, or even snoop on your data themselves.
-
-So we leave it all open for you to see and make it easy to host yourself.
-
-Of course, there are other benefits of building in the open. We hired world class engineers, but with such a complex product mistakes can happen. More eyes on our code means vulnerabilities are spotted and resolved faster. As we've grown, we are even getting contributions from the community.
-
-## Why Y Combinator?
-
-After our ShowHN, a long list of feature requests appeared in our GitHub repo. A list we couldn't close alone. At least not within a reasonable amount of time.
-
-For a new product with no revenue (yet), VC funding seemed to fit. It would allow us to create something for the community and in parallel investigate the right model to build a sustainable business. As first time founders, YC seemed like a good fit. After all, they helped GitLab and Mattermost get off the ground.
-
-A brief summary for those that don't know. For a stake in your company, YC offers 3 things: capital, advice, and community.
-
-When we accepted the invitation, YC's investment was $125k for 7% of our company. A few weeks into the batch we were offered an additional $375k as an uncapped MFN safe. Lucky us! You can read more about it here.
-
-Advice comes in the form of interactive workshops and long-form posts. They are invaluable resources and often come with snappy titles, like “how not to fail”.
-
-Community is YC's magic. Thousands of past founders who can make introductions to investors, give advice, and even become users of your product. They can help you understand what “how not to fail” should mean to an open-source security company. Same with general advice on setting metrics, talking to users, and pricing.
-
-Here's some of our learnings.
-
-## Should I collect telemetry?
-
-As a VC backed-startup, probably yes.
-
-Even with a crystal ball on what users want, metrics can still help identify reliability issues and add insight to reported bugs.
-
-From a business point of view, they tell you who and how many people like your product and which features are getting used.
-
-It's a great way to focus the team on what matters.
-
-Best of all when the data-points start lining up like a hockey stick, it can get you the funding you need to build a great product.
-
-YC's advice is to set a primary metric that accurately captures the value you're delivering to users. This primary metric should be paired with secondary metrics that drive the primary metric and you can actionably move and iterate on.
-
-In case you're curious, we've set users in production as our primary metric. Our secondary metrics help add context to the growth.
-
-For example, here are 3 different graphs of our progress near demo day. Our star count, number of live instances, and number of devices. Each graph tells a slightly different story. Star count shows growing awareness in the open-source community. Instances show steady growth in actual adoption. Number of users tell us more about the deployments of Firezone. Since it outpaced the growth of instances, we knew larger teams were adopting Firezone over time and existing deployments were growing inside organizations.
-
-
-
-So, how do you measure usage? Not as simple as you think.
-
-For most software products, telemetry is a small script in the header of your website and an annoying cookie banner. Sometimes it's also a few lines of code sprinkled through the backend. Most users expect to be tracked by the hosted services they use. They may not like it, but they generally won't fuss about it.
-
-Open-source is different.
-
-Though it's getting more common, not everyone expects a self-hosted open-source project to report their usage. We had to be careful what we tracked, how we anonymized it, and how we communicate it to users.
-
-We spoke to a few other open source companies we respected. Here's the advice we received.
-
-- Explain why you do it: Document what you track, how it's stored, and what you use it for. We took heavy inspiration from companies like Mattermost and made our own page in our documentation.
-- Make it clear and easy to opt-out: To make it simple for users, we created a deployment script that streamlines the install process. In the script we explicitly ask for permission and make it easy to switch off later directly in the UI.
-- Don't unnecessarily expose user data to third parties: Those annoying cookie banners on websites you visit generally mean one thing. You're being tracked, and your information is being sent to third party tools like CRMs and ad platforms. If you've signed up for an account and checked the box for terms and conditions, you're agreeing to that as well. With Firezone, we try to use open-source and self-hosted products whenever possible. This includes our telemetry platform as well.
-
-So, now we know about users in aggregate.
-
-But, our product is early and legacy VPNs are painful in many ways. We need more information to prioritize what to build first. The best way to do that is by talking to users.
-
-## We don't know who our users are
-
-“Write code and talk to users” is consistently echoed during YC.
-
-A great summary why is in “do things that don't scale”. I recommend reading the article, but it boils down to this:
-
-You often build the initial product for yourself. The MVP is usually not good enough - it's never quite right. You should get it in front of users as soon as it provides utility so you can get feedback to iterate and improve.
-
-The average user of Firezone is technical. Usually a system admin, IT manager, or DevOps engineer. They're fully capable of setting up Firezone and reading our docs to figure out what the product can do.
-
-We get frequent GitHub issues and Discourse posts pointing at issues or desired features. Sometimes they'll even fix it for us!
-
-However, Firezone does not require a valid email to sign up. It's hosted entirely on your infrastructure. It would be weird to lock anything behind a signup.
-
-I would be equally distasteful to hijack discussions with requests for a user interview.
-
-So, to generate more conversations, we increased the surface area of how users can reach us. It's important to note who you're getting feedback from as well. Often for developer facing products, the person that's deploying the product is not the person who decides what to use, what the budget is, or even the only one benefiting from it.
-
-Firezone ties into security playbooks, compliance requirements, hiring plans for contractors globally, and risk planning from risk departments.
-
-Here's how we're currently reaching them:
-Source Types of conversations Who we speak with
-Install script email (opt-in) Deployment issues ICs, IT Managers
-Slack Group and Discourse threads Deployment and configuration issues ICs, IT Managers
-GitHub issues Feature requests ICs, IT Managers, IT Leaders
-Inbound sales leads Required functionality, pricing discussions CTO, CISO, IT Leaders
-Outbound leads Problem discovery, product roadmap planning CTO, CISO, IT Leaders
-
-One example of why it's important to dig deeper involves a request to “load a custom logo”. When we got on a Zoom call, we would uncover a group of re-sellers who want to white-label our product with their clients. Turns out they have other requirements they'd be happy to pay for if we had them.
-
-These conversations helped make the product better and form our view on our business model.
-
-This leads into the final piece of advice from YC, pricing.
-
-## Paying user feedback > free users
-
-Figuring out your pricing model and generating meaningful revenue is the great filter between early MVPs and successful companies.
-
-The main question however is when.
-
-With limited resources, generating revenue is almost always a tradeoff. Less growth, slower development of features, and the potential to ruin a perfectly good story for investors. Queue Silicon Valley:
-
-
-
-So, when to figure out revenue?
-
-For B2B software, the answer should probably be “right now”.
-
-Steering early user conversations toward pricing tells you if the product is viable and solves a big enough pain. YC echoes this advice.
-
-A startup I previously worked at, Kite, failed partly because we punted the question of “will people pay?” too many times. It was an AI powered co-pilot, an early iteration of GitHub Copilot.
-
-When we finally tried, it was clear the product needed to evolve to generate meaningful revenue. By the time we realized that, it was too late. Adam, the founder of Kite and an investor in Firezone, recently open-sourced the codebase and wrote a great post-mortem:
-
-https://www.kite.com/blog/product/kite-is-saying-farewell/
-
-For self-hosted open-source software the answer is not as clear.
-
-[As a self-hosted security product, layering feature gating logic into the core product is problematic. Feature flags are complex to write, and even harder to maintain as our product evolves. Being critical infrastructure for remote work, we also don't want your company to come to a halt when your credit card expires. There's more to say here, but I'll leave this to a future deep-dive from my co-founder, Jamil.]
-
-So, similar to other successful open-source projects, our early goal was to grow the community. During YC we focused on building out the core parts of our platform, driving adoption, and optimizing for learning from our users. One of things we wanted to learn was how to build a business around Firezone.
-
-As usage grew, a pattern emerged when talking to users. Our largest deployments all started with an individual spinning Firezone up without ever speaking to us.
-
-As usage grew, they reached out to inquire about additional features and services.
-
-As we continue to develop our pricing model, we want to ensure the following:
-- Individuals and hobbyists can use Firezone for free
-- Small teams can use Firezone for free (if they support it themselves)
-- Large organizations can run a PoC without any calls with sales
-
-If this sounds familiar, it's similar to how GitLab thinks about their pricing. We're obviously big fans.
-
-## Paying it forward (still writing this part...)
-
-[not sure how to end this]
-
-- https://a16z.com/2019/10/04/open-source-from-community-to-commercialization/
diff --git a/www/blog/_2023-02-13-ebpf-firewall/index.mdx b/www/blog/_2023-02-13-ebpf-firewall/index.mdx
deleted file mode 100644
index 37b255358..000000000
--- a/www/blog/_2023-02-13-ebpf-firewall/index.mdx
+++ /dev/null
@@ -1,544 +0,0 @@
----
-slug: ebpf-firewall
-title: How We Built an eBPF-based General Purpose Packet Filter
-authors: [conectado]
-tags: [ebpf, firewall, rust, aya]
----
-
-## Introduction
-
-As part of our migration to multi-site in Firezone the VPN and Firewall were rewritten in Rust. As part of that rewrite we decided to improve how we were handling the firewall.
-
-In the past we were using [nftables](https://netfilter.org/projects/nftables/), the way we did this was shelling-out to the console and use the nft cli.
-
-This has a number of problems, for one shelling out can be prone to error, inefficient and hard to unit-test, also there's no Rust lib to call into nftables and even the existing libraries in C can be too complicated to use. Furthermore, we were limited to nft's data structure which meant doing a lot of work to not mess up the rules, this in turn made doing improvements really slow.
-
-So after a lot of consideration we decided that creating our own firewall using [ebpf](https://ebpf.io/).
-
-## eBPF
-
-We will briefly go into what eBPF is, however If you want a more detailed introduction you can take a look at [the official introduction](https://ebpf.io/what-is-ebpf).
-
-### What is eBPF
-
-eBPF stands for extended Berkeley Packet Filter, which is an upgrade from BPF(Berkely Packet Filter), while eBPF brings a lot of improvements over BPF the gist is the same, run user-defined packet-filtering code inside of the kernel as part of the packet processing pipeline.
-
-This is an oversimplification because eBPF programs can be hooked into multiple different events in the kernel but for our intent and purposes, we just want to hook into the packet-classifier pipeline.
-
-
-### How the kernel safely run user-defined code
-
-eBPF has its own ISA and there is a runtime for said ISA in the kernel (JIT'd), the instructions allows calling into parts of the kernel that we might need and gives us the necessary context to process a given packet.
-
-Furthermore, to prevent crashes in the kernel and hogging out resources before an eBPF program gets loaded into the kernel it goes through a verification process, a verificator program sets a bunch of limitations to the program to prevent situations like infinite loops and crashes:
-
-* It sets an upper-bound for the number of times a loop within the code can run (or strictly prohibits them in older kernel versions).
-* An upper-bound in the number of instructions the program can execute in total.
-* Keeps tracks of read/writes to know that you are using valid memory locations.
-
-To know the specifics of how it works, you should take a look at the [kernel's doc](https://www.kernel.org/doc/Documentation/networking/filter.txt) and even more in details you can take a look at [cillium's docs](https://docs.cilium.io/en/stable/bpf/#bpf-guide).
-
-### Packet pipeline
-
-Without getting into the specific an eBPF program can be hooked into different hooks on the packet processing pipeline for the linux kernel. eBPF allows hooking into [XDP](https://www.iovisor.org/technology/xdp) which runs just after the packet reached the NIC. However, [XDP doesn't support Wireguard](https://lore.kernel.org/netdev/20200813195816.67222-1-Jason@zx2c4.com/T/) since wireguard doesn't have L2 headers, for more info on this see [this fly.io blogpost](https://fly.io/blog/bpf-xdp-packet-filters-and-udp/#xdp).
-
-Fret not, for eBPF can also hook into the network's [TC Ingress](https://man7.org/linux/man-pages/man8/tc-bpf.8.html) that doesn't make any assumption about the packet's header.
-
-### Maps
-
-Maps are the kernel structures that enables us to share data between the eBPF kernel program and a user-space program. Maps, as their name suggest allow us to store relations as `Key -> Value` the types of maps offered by eBPF is limited however there are a lot of them. For our use case we just need to concern us with [trie](https://github.com/torvalds/linux/blob/master/kernel/bpf/lpm_trie.c) and hash maps.
-
-Again I reffer to [cillium's documentation](https://docs.cilium.io/en/v1.12/bpf/#maps) for more information.
-
-### TL;DR
-
-eBPF is an ISA and its corresponding implementation for user-defined programs that run in the kernel that we used for filtering packets, however, the programs we can run have some severe limitations so that they don't crash the kernel.
-
-## Firewall
-
-With this in mind we wanted to write a Firewall that can allow/deny traffic based on the following:
-
-- Destination CIDR
-- Possibly multiple sender IPs
-- Possibly a port-range along associated with UDP, TCP or both
-
-We took an additional simplification to make the implementation easier(we will see why further along), you can configure the firewall to allow all or deny all, then when a packet match a rule it'd invert that behavior:
-> A firewall that denies all traffic with a rule for destination `10.20.30.40`, would deny all traffic from all sources to all destinations except for traffic for `10.20.30.40` from any destination.
-
-### Aya
-
-When implementing the firewall in Rust two possible libraries:
-
-- [aya](https://github.com/aya-rs/aya)
-- [redbpf](https://github.com/foniod/redbpf)
-
-`redbpf` relies on bindings to `libbpf` while `aya` only relies on `libc`, also, aya's tooling seems to be easier to use and it uses cargo's target for ebpf instead of relying on `cargo bpf` which is easier when writing the Firewall as a library.
-
-So taking that into account we went with `aya`.
-
-Normally, the way an aya program is structured: we have a user-space crate that loads the eBPF program and is a proxy between it and the user and a crate that targets eBPF which has more limitations(such as being `no-std`).
-
-Aya normally expects to be run as a binary and not as a library or as a separate userspace/bpf library, so we needed to do some tuning for the template to be able to run it as we wanted, a single library crate that you include.
-
-More about how we did this in a separate blogpost.
-
-### Architecture
-
-** TODO: ** Add diagrams
-
-So, with this information, we can plan an architecture.
-
-Thinking about the steps how ideally, the firewall would work:
-
-1. A packet arrives
-2. The source is classified into a `user_id` if any
-3. Check existing rules if match
-4. Decide REJECT/ACCEPT action based on previous step
-
-Let's go over how we can achieve this.
-
-### The anatomy of a rule
-
-As we said before a rule has 3 components
-
-- Associated `user_id`
-- Destination CIDR
-- Destination Port Ranges
-
-The `user_id` is an arbitrary name, the idea is that a single rule can associate multiple source ips, so we can associate a rule with an `id` and then we can update the `id` association with multiple ips during runtime.
-
-Rules need to be stored in eBPF's maps, that way we can update the maps during run-time from userspace to be able to update the rules.
-
-And we need to be able to lookup those maps using information from the incoming packets.
-
-The way we did this is having the following maps:
-
-- `SOURCE_MAP`: A hashmap mapping source ips to `id`s
-- `RULE_MAP`: A trie mapping CIDR to port ranges
-
-** Note: ** There is actually an ipv6 and ipv4 version for both of those maps, so we have 4 maps in total.
-
-### `SOURCE_MAP`
-
-The `SOURCE_MAP` is really simple, we store the mapping IP -> ID, so we can associate let's say IP `10.10.10.3` and `10.10.10.4` with id `4` and `10.1.1.5` with id `7`. Now when a packet comes from `10.10.10.4` we lookup the map and get `4` and for `10.1.1.5` we get `7`.
-
-### `RULE_MAP`
-
-[Tries](https://en.wikipedia.org/wiki/Trie) are prefix-matching trees, they let us efficiently store and lookup ranges grouped by prefix. For ips this is exactly how [CIDR](https://en.wikipedia.org/wiki/Classless_Inter-Domain_Routing) works.
-
-The nodes in the trie tree correspond to a an ip and a prefix, so `10.5.8.0/24` corresponds to to the bits of `10.5.8.0` and 24 bits so that node would match with `10.5.8.0` to `10.5.8.255` but if you store `10.5.8.128/25` that'd match with `10.5.8.128` to `10.5.8.255`.
-
-Both nodes, `10.5.8.0/24 and `10.5.8.128/25`, could be stored but the `lookup` method in the `trie` only allows us to find the node with the most specific match. so `10.5.8.110` would match with `10.5.8.0/24` and `10.5.8.170` would match with `10.5.8.128/25` but we would never learn that it also match with `10.5.8.0/24`.
-
-So a trie would give us a way to associate CIDR with... something? The question is what's this "something".
-
-Well, we don't need an action, since we know the action is just inverting the default one. What we still lack to know if the rule matches is a port-range(With its protocol) and the associated `id`.
-
-However, if we store multiple rules, all associated with the same destination IP we would need to lookup all the rules for each packet and this is incredibly inefficient. But there's a solution, we can easily store the ID and protocol in the key!
-
-So instead of storing as the key `10.5.8.0/24` and when we do lookup we get all the other data we store as the key `6.TCP.10.5.8.0` and the prefix instead of 24 is 33, 4 extra bytes for the id, 1 for the protocol(We use the protocol number).
-
-If this is still unclear we will see more when we discuss the specific of the code, just know that we store the id and protocol as part of the key, so we can compose the number `id.protocol.ip` with the prefix and look that up.
-
-The result value will be the port range, which we have to map to the port of the incoming packet, we will talk more about how we do this below.
-
-For sources with no id we use `0` as the id. For non-TCP/UDP packets, we store the rule in both the TCP and UDP key and look up TCP(arbitrarily) but only match for port 0 (which we use to encode all ports), for rules with both protocols, we store the rule twice once for TCP and once for UDP.
-
-### Another look at the ip matching
-
-Let's look again at the steps when a packet arrives:
-
-1. Packet arrives
-2. Lookup destination IP get an ID or use 0
-3. Create the lookup key (ID.PROTOCOL.DESTINATION_IP)
-4. Use the lookup key to get the port ranges
-5. Lookup the port in the port ranges
-6. REJECT/ACCEPT based on that
-
-Basically, this is a high-level on how the ebpf side works. Now, let's take a look at the userspace-side.
-
-### Userspace
-
-Now that we know how we access the rules let's see how we need to store them from userspace.
-
-Remember, that the Trie map provided by the kernel, for search, only have its lookup method that let us know the longest prefix. So let's think about this scenario:
-
-We store these rules:
-
-```
-10.0.0.0/24 port 80 Allowed
-10.0.0.1/32 port 23 Allowed
-```
-
-now a packet comes from 10.0.0.1 with port 80, and we use the Trie lookup method to see if it's allowed, the lookup method returns all the ports from the longest prefix, meaning port 23 is allowed but the packet has port 80 so it's denied.
-
-This is of course, erroneous because IP `10.0.0.1` is part of range `10.0.0.0/24` which has port 80 is allowed. So what do we do about this? Changing the trie API is impossible without modifying the kernel and even if we submit the PR for that the new API would only be included in the latest kernels.
-
-We could lookup manually each range before deciding an action, so when packet with `10.0.0.1` comes we check `10.0.0.1/32` then `10.0.0.0/31` the `10.0.0.0/30` so on and so on before taking a decision. The performance of this is bad, specially if we are going to do that about each packet.
-
-What we can do, is from userspace present an API that when adding rules, it propagates them to all pertinent ips, so:
-
-If you have:
-
-```
-10.0.0.1/32 port 23 Allowed
-```
-
-and you want to add `10.0.0.0/24 port 80`, the API would automatically propagate it to:
-
-```
-10.0.0.1/32 port 23, 80 Allowed
-10.0.0.0/24 port 80 Allowed
-```
-
-and if you have:
-
-```
-10.0.0.0/24 port 80 Allowed
-```
-
-then you add `10.0.0.1/32 port 23` the api actually updates the rules like:
-
-```
-10.0.0.1/32 port 23, 80 Allowed
-10.0.0.0/24 port 80 allowed
-```
-
-So you see, how the api automatically propagates rules to have a consistent table.
-
-### Port Ranges
-
-## At last, CODE!
-
-With the previous section you should have a clear picture at the architecture of what we built and why but from now on we will **need** to see code.
-
-Will not go over how Aya's API or eBPF code works, hopefully it will be self-evident with the explanations until now enough to understand the gist of it.
-
-### Code structure
-
-We have 3 crates in our repo:
-* Userspace
-* Common (This contains the codebase shared by both)
-* eBPF
-
-From userspace we have the `Firewall` which is the entrypoint for everything. You first initialize and load a firewall by calling `Firewall::new` for a given interface.
-
-The most interesting part is the `RuleTracker` this is an internal struct (which is almost directly exposed by `Firewall` using pass-through methods), this is where the magic happens, userspace `Rule`s are converted into valid eBPF `Rule`, we keep track of them to propagate them and obviously add them to the maps in eBPF.
-
-So let's see how that happens.
-
-### A rule
-
-#### eBPF
-
-So, how does a rule looks in reality:
-
-```rs
-#[repr(C)]
-pub struct RuleStore {
- // Sorted non-overlapping ranges
- // bit 0-15: port-start
- // bit 16-31: port-end
- rules: [u32; MAX_RULES],
- rules_len: u32,
-}
-```
-
-Structs in eBPF need to be `repr(C)`, which just means it uses C's ABI, eBPF structs need to be simple array of bytes (with no padding to convince the eBPF verifier that we never read uninitialized memory).
-
-So, let's analyze this struct, this is the value that we are going to store in the map. This only need to be the port-ranges (remember that the key already stores the `id`, `destination`, `protocol`).
-
-So we store the rules as an array of port-ranges. With a range being the inclusive intervals of the port covered by the rule. we use the first 2 bytes for the starting port and the last 2 bytes for the ending port.
-
-Then in `rules_len` we just have the number of rules stored (the rest is padded with 0).
-
-#### Useraspace
-
-From userspace we have many different structs that represent a rule at different stage of processing, these are not complex but we have different parts of the code that require different information for what to do with the rule.
-
-But for user-facing API a rule looks like:
-
-```rs
-pub enum Rule {
- V4(RuleImpl),
- V6(RuleImpl),
-}
-```
-
-Alright, not very interesting without knowing how `RuleImpl` looks:
-
-```rs
-pub struct RuleImpl {
- pub(crate) id: Option,
- pub(crate) dest: T,
- pub(crate) port_range: Option,
-}
-```
-
-So we see that a rule in userspace contains all the information for a rule but the important part is:
-
-```rs
-pub(crate) struct PortRange {
- pub(crate) ports: RangeInclusive,
- pub(crate) proto: Protocol,
-}
-```
-
-Cool! Use rust's `RangeInclusive` to represent ports with `u16` as a port and a `Protocol` (which is just an enum to indicate the kind of rule)
-
-So when we do `Firewall::add_rule(rule)` we need to make it arrive to eBPF with the struct we previously saw.
-
-We also need to propagate correctly like we saw in the previous userspace architecture, so let's walk through how does that work!
-
-#### Translation
-
-So at some point we want to add the `rule` to the eBPF map. For that, we first need to determine the key that we are going to use.
-
-That's easy:
-
-```rs
-// Convert the id to big endian bytes
-let key_id = id.to_be_bytes();
-
-// Convert the ip to bytes
-let key_cidr = ip.normalize().as_octets();
-let mut key_data = [0u8; N];
-
-// Store in a new `key_data`: protocol.id.ip
-let (left_key_data, cidr) = key_data.split_at_mut(5);
-let (id, prot) = left_key_data.split_at_mut(4);
-prot[0] = proto;
-id.copy_from_slice(&key_id);
-cidr.copy_from_slice(key_cidr.as_ref());
-
-// Calculate the prefix and return the eBPF key
-Key::new(
- u32::from(ip.prefix()) + (left_key_data.len() * 8) as u32,
- key_data,
-)
-```
-
-Cool, this is the key that we are going to insert to the eBPF map
-
-Now we need to calculate the value that we are going to insert.
-
-Remember that the `rule` field in the ebpf `RuleStore` looked like this:
-
-```rs
- rules: [u32; MAX_RULES],
-```
-
-So we have a maximum number of rules, one reason for this, is that we need to store an array, we can't store a vector (we can't share heap allocations). But this number is also limited by the lookup algorithm.
-
-Remember, that the verifier imposes a limit on the number of times a loop can run, so if we linearly search all ranges we were getting capped at around 1000 intervals we would reach the upper limit on loops, this is okay, this would be enough but we can do better.
-
-If we can somehow sort the port ranges we could do binary search, this means less loop iterations and faster lookup in general. But how to sort it exactly?
-
-This is actually the reason each rule, doesn't have an Accept/Reject instead it only inverts the default behavior, also why we store all UDP rules together and TCP rules together.
-
-To sort, we just need to merge intervals. Merging intervals is a well studied problem that can be done in `O(N)` and since it's from userspace we could afford worse performance.
-
-Mergining intervals just means that from the existing intervals we create a series of new non-overlapping intervals that cover the same area and we sort them.
-
-So `[10-20, 15-30, 6-9]` would become `[6-9, 10-30]`. Then we can do binary search on this interval. We will see below the specific of that but this is the code to get the intervals from a series of port ranges:
-
-
-```rs
-fn resolve_overlap(port_ranges: &mut [&PortRange]) -> Vec<(u16, u16)>
-{
- let mut res = Vec::new();
-
- // Sort the ranges by the starting potr
- port_ranges.sort_by_key(|p| p.ports.ports.start());
-
- Get the first prot into the result
- if let Some(range) = port_ranges.first() {
- res.push((*range.ports.ports.start(), *range.ports.ports.end()));
- } else {
- return res;
- }
-
- // Go through each range
- for range in &port_ranges[1..] {
- let last_res = res
- .last_mut()
- .expect("should contain at least the first element of port_ranges");
-
- // If the new range fall within the last one extend it
- if last_res.1 >= *range.ports.ports.start() {
- *last_res = (last_res.0, last_res.1.max(*range.ports.ports.end()));
- // Otherwise, add a new range
- } else {
- res.push((*range.ports.ports.start(), *range.ports.ports.end()));
- }
- }
-
- res
-}
-```
-
-As you see doing this is really easy. We still need to do some small work to get it from `Vec<(u16, u16)>` to `[u32; RULE_MAX]` but you can imagine it's pretty trivial.
-
-### Propagating Rules
-
-Then the last interesting part from userspace is how to propagate the rules.
-
-So when you insert a new rule, you need to keep track of all the rules that would include it, since when a lookup happen it would return the new rule because it's more specific. So basically the gist is traverse all rules and include all the port ranges from those "above" in the new rule.
-
-```rs
-(The code here requires a lot of context on the specifics of how we did this but it's nothing interesting, check if you can rewrite it in a "context-free" way)
-```
-
-And then there could be more specific rules that are included in the new rule, you need to propagate the new rule (the port-range) to those.
-
-```rs
-(The code here requires a lot of context on the specifics of how we did this but it's nothing interesting, check if you can rewrite it in a "context-free" way)
-```
-
-### eBPF Rule lookup
-
-
-When a packet arrives we first extract the network headers (source, destination, protocol and port).
-
-```rs
- let (source, dest, proto) = load_ntw_headers(&ctx, version)?;
- let port = get_port(&ctx, version, proto)?;
- let class = source_class(source_map, source);
- let action = get_action(class, dest, rule_map, port, proto);
-```
-
-Then, we get the source id:
-
-```rs
-unsafe fn source_class(
- source_map: &HashMap<[u8; N], u32>,
- address: [u8; N],
-) -> Option<[u8; 4]> {
- source_map.get(&address).map(|x| u32::to_be_bytes(*x))
-}
-```
-Then we try to calculate what action we should take:
-
-```rs
-fn get_action(
- group: Option<[u8; 4]>,
- address: [u8; N],
- rule_map: &LpmTrie<[u8; M], RuleStore>,
- port: u16,
- proto: u8,
-) -> i32 {
- let proto = if port == 0 { TCP } else { proto };
- let default_action = get_default_action();
-
- let rule_store = rule_map.get(&Key::new((M * 8) as u32, get_key(group, proto, address)));
- if is_stored(&rule_store, port) {
- return invert_action(default_action);
- }
-
- if group.is_some() {
- let rule_store = rule_map.get(&Key::new((M * 8) as u32, get_key(None, proto, address)));
- if is_stored(&rule_store, port) {
- return invert_action(default_action);
- }
- }
-
- default_action
-}
-```
-
-Here we try to extract the action from the existing map, we get the `RuleStore` by constructing the key corresponding to that packet:
-
-```rs
-fn get_key(
- group: Option<[u8; 4]>,
- proto: u8,
- address: [u8; N],
-) -> [u8; M] {
- let group = group.unwrap_or_default();
- let mut res = [0; M];
- let (res_left, res_address) = res.split_at_mut(5);
- let (res_group, res_proto) = res_left.split_at_mut(4);
- res_group.copy_from_slice(&group);
- res_proto[0] = proto;
- res_address.copy_from_slice(&address);
- res
-}
-```
-And most importantly we lookup in the rulestore if the `port` that arrived exists.
-
-```rs
- pub fn lookup(&self, val: u16) -> bool {
- // 0 means all ports
- if self.rules_len > 0 {
- // SAFETY: We know that rules_len < MAX_RULES
- if start(*unsafe { self.rules.get_unchecked(0) }) == 0 {
- return true;
- }
- }
-
- // We test for 0 in all non tcp/udp packets
- // it's worth returning early for those cases.
- if val == 0 {
- return false;
- }
-
- // Reimplementation of partition_point to satisfy verifier
- let mut size = self.rules_len as usize;
- // appeasing the verifier
- if size >= MAX_RULES {
- return false;
- }
- let mut left = 0;
- let mut right = size;
- #[cfg(not(feature = "user"))]
- let mut i = 0;
- while left < right {
- let mid = left + size / 2;
-
- // This can never happen but we need the verifier to believe us
- let r = if mid < MAX_RULES {
- // SAFETY: We are already bound checking
- *unsafe { self.rules.get_unchecked(mid) }
- } else {
- return false;
- };
- let cmp = start(r) <= val;
- if cmp {
- left = mid + 1;
- } else {
- right = mid;
- }
- size = right - left;
-
- #[cfg(not(feature = "user"))]
- {
- i += 1;
- // This should never happen, here just to satisfy verifier
- if i >= MAX_ITER {
- return false;
- }
- }
- }
-
- if left == 0 {
- false
- } else {
- let indx = left - 1;
- if indx >= MAX_RULES {
- return false;
- }
- // SAFETY: Again, we are already bound checking
- end(*unsafe { self.rules.get_unchecked(indx) }) >= val
- }
- }
-```
-
-If 0 is included we consider it to be "all ports".
-
-Otherwise we basically do binary search on the starting port to see the maximum starting port that is less than the port we are checking for and then we check for the ending port to see if it's more than the port we are checking.
-
-Binary search for the maximum that keeps a predicate as true is an algorithm that already exists in Rust called partition point, we needed to reimplement it to make it compatible with eBPF due to the verifier limitations.
-
-## Conclusion
-
-ebpf is awesome but complicated! (something along those lines) and future for firezone rearchitecture and check it out!
diff --git a/www/blog/authors.yml b/www/blog/authors.yml
deleted file mode 100644
index 189b7469c..000000000
--- a/www/blog/authors.yml
+++ /dev/null
@@ -1,16 +0,0 @@
-jamil:
- name: Jamil Bou Kheir
- title: Co-founder
- url: https://github.com/jamilbk
- image_url: https://www.gravatar.com/avatar/3c8434814eec26026718e992322648c8
-
-jason:
- name: Jason Gong
- title: Co-founder
- url: https://github.com/gongjason
- image_url: https://www.gravatar.com/avatar/d688e2280a36287f61c4426334dce065
-
-conectado:
- name: Gabriel Steinberg
- title: Senior Rust Engineer
- url: https://github.com/conectado
diff --git a/www/docs/README.mdx b/www/docs/README.mdx
deleted file mode 100644
index a7ccb391c..000000000
--- a/www/docs/README.mdx
+++ /dev/null
@@ -1,49 +0,0 @@
----
-title: Overview
-sidebar_position: 1
----
-
-[Firezone](/) is an open-source secure remote access
-platform that can be deployed on your own infrastructure in minutes.
-Use it to **quickly and easily** secure access to
-your private network and internal applications from an intuitive web UI.
-
-
-
-These docs explain how to deploy, configure, and use Firezone.
-
-## Quick start
-
-1. [Deploy](deploy): A step-by-step walk-through setting up Firezone.
- Start here if you are new.
-1. [Authenticate](authenticate): Set up authentication using local
- email/password, OpenID Connect, or SAML 2.0 and optionally enable
- TOTP-based MFA.
-1. [Administer](administer): Day to day administration of the Firezone
- server.
-1. [User Guides](user-guides): Useful guides to help you learn how to use
- Firezone and troubleshoot common issues. Consult this section
- after you successfully deploy the Firezone server.
-
-## Common configuration guides
-
-1. [Split Tunneling](./user-guides/use-cases/split-tunnel):
- Only route traffic to certain IP ranges through the VPN.
-1. [Setting up a NAT Gateway with a Static IP](./user-guides/use-cases/nat-gateway):
- Configure Firezone with a static IP address to provide
- a single egress IP for your team's traffic.
-1. [Reverse Tunnels](./user-guides/use-cases/reverse-tunnel):
- Establish tunnels between multiple peers.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
-
-## Contribute to firezone
-
-We deeply appreciate any and all contributions to the project and do our best to
-ensure your contribution is included. To get started, see [CONTRIBUTING.md
-](https://github.com/firezone/firezone/blob/master/CONTRIBUTING.md).
-
-
-
-
diff --git a/www/docs/administer/README.mdx b/www/docs/administer/README.mdx
deleted file mode 100644
index a7830cb43..000000000
--- a/www/docs/administer/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Administer
-sidebar_position: 4
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/administer/backup.mdx b/www/docs/administer/backup.mdx
deleted file mode 100644
index cf5aaa934..000000000
--- a/www/docs/administer/backup.mdx
+++ /dev/null
@@ -1,101 +0,0 @@
----
-title: Backup and Restore
-sidebar_position: 4
----
-
-Firezone can be safely backed up and restored in a couple of minutes under
-most circumstances.
-
-:::info
-This guide is written for Firezone deployments using **Docker Engine** on **Linux** only.
-:::
-
-Unless your hosting provider supports taking live VM snapshots, you'll
-need to stop Firezone before backing it up. This ensures the Postgres data
-directory is in a consistent state when the backup is performed. Backing up a
-running Firezone instance will **most likely** result in data loss when restored;
-you have been warned.
-
-After stopping Firezone, backing up Firezone is mostly a matter of copying the relevant
-[files and directories](/docs/reference/file-and-directory-locations/) to a location of your
-choosing.
-
-See the steps below for specific examples for Docker and Omnibus.
-
-
-
-
-### Backup
-
-For Docker-based deployments, this will consist of backing up the `$HOME/.firezone`
-directory along with the Postgres data directory, typically located at
-`/var/lib/docker/volumes/firezone_postgres-data` on Linux if you're using the default
-Docker compose template.
-
-1. Stop Firezone (warning: this **will** disconnect any users connected to the VPN):
-
-```
-docker compose -f $HOME/.firezone/docker-compose.yml down
-```
-
-2. Copy relevant files and folders. If your made any customizations to `/etc/docker/daemon.json`
- (for example, for IPv6 support), be sure to include that in the backup as well.
-
-```
-tar -zcvfp $HOME/firezone-back-$(date +'%F-%H-%M').tgz $HOME/.firezone /var/lib/docker/volumes/firezone_postgres-data
-```
-
-A backup file named `firezone-back-TIMESTAMP.tgz` will then be stored in `$HOME/`.
-
-### Restore
-
-1. Copy the files back to their original location:
-
-```
-tar -zxvfp /path/to/firezone-back.tgz -C / --numeric-owner
-```
-
-2. Optionally, enable Docker to boot on startup:
-
-```
-systemctl enable docker
-```
-
-
-
-
-### Backup
-
-1. Stop Firezone (warning: this **will** disconnect any users connected to the VPN):
-
-```
-firezone-ctl stop
-```
-
-2. Copy relevant files and folders:
-
-```
-tar -zcvfp $HOME/firezone-back-$(date +'%F-%H-%M').tgz /var/opt/firezone /opt/firezone /usr/bin/firezone-ctl /etc/systemd/system/firezone-runsvdir-start.service /etc/firezone
-```
-
-A backup file named `firezone-back-TIMESTAMP.tgz` will then be stored in `$HOME/`.
-
-### Restore
-
-1. Copy the files back to their original location:
-
-```
-tar -zxvfp /path/to/firezone-back.tgz -C / --numeric-owner
-```
-
-2. Reconfigure Firezone to ensure configuration is applied to the host system:
-
-```
-firezone-ctl reconfigure
-```
-
-
-
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/administer/debug-logs.mdx b/www/docs/administer/debug-logs.mdx
deleted file mode 100644
index 834d875c6..000000000
--- a/www/docs/administer/debug-logs.mdx
+++ /dev/null
@@ -1,54 +0,0 @@
----
-title: Debug Logs
-sidebar_position: 8
-description:
- Docker deployments of Firezone generate and store debug logs to a JSON
- file on the host machine.
----
-
-:::note
-This article is written for Docker based deployments of Firezone.
-:::
-
-Docker deployments of Firezone consist of 3 running containers:
-
-| Container | Function | Example logs |
-| --------- | ------------- | --------------------------------------------- |
-| firezone | Web portal | HTTP requests received and responses provided |
-| postgres | Database | |
-| caddy | Reverse proxy | |
-
-Each container generates and stores logs to a JSON file on the host
-machine. These files can be found at
-`var/lib/docker/containers/{CONTAINER_ID}/{CONTAINER_ID}-json.log`.
-
-Run the `docker compose logs` command to view the log output from all running
-containers. Note, `docker compose` commands need to be run in the Firezone
-root directory. This is `$HOME/.firezone` by default.
-
-See additional options of the `docker compose logs` command
-[here](https://docs.docker.com/engine/reference/commandline/compose_logs/).
-
-## Managing and configuring Docker logs
-
-By default, Firezone uses the `json-file` logging driver without
-[additional configuration](https://docs.docker.com/config/containers/logging/json-file/).
-This means logs from each container are individually stored in a file format
-designed to be exclusively accessed by the Docker daemon. Log rotation is not
-enabled, so logs on the host can build up and consume excess storage space.
-
-For production deployments of Firezone you may want to configure how logs are
-collected and stored. Docker provides
-[multiple mechanisms](https://docs.docker.com/config/containers/logging/configure/)
-to collect information from running containers and services.
-
-Examples of popular plugins, configurations, and use cases are:
-
-- Export container logs to your SIEM or observability platform (i.e.
- [Splunk](https://docs.docker.com/config/containers/logging/splunk/)
- or
- [Google Cloud Logging](https://docs.docker.com/config/containers/logging/gcplogs/)
- )
-- Enable log rotation and max file size.
-- [Customize log driver output](https://docs.docker.com/config/containers/logging/log_tags/)
- with tags.
diff --git a/www/docs/administer/migrate.mdx b/www/docs/administer/migrate.mdx
deleted file mode 100644
index b9bb0d9a6..000000000
--- a/www/docs/administer/migrate.mdx
+++ /dev/null
@@ -1,74 +0,0 @@
----
-title: Migrate to Docker
-sidebar_position: 2
----
-
-# Migrate from Omnibus to Docker
-
-Chef Infra Client, the configuration system Chef Omnibus relies on, has been
-[scheduled for End-of-Life in 2024](https://docs.chef.io/versions/).
-Firezone 0.7 will be the last version to offer Omnibus-based deployments.
-Users are encouraged to migrate to a Docker-based deployment of Firezone using
-this guide.
-
-Existing Omnibus-based deployments of Firezone will continue to function as-is,
-but no officially supported RedHat or Debian packages will be published for
-Firezone 0.8 and above.
-
-See this [GitHub issue tracking discussion
-](https://github.com/firezone/firezone/issues/1304) for more details.
-
-Follow this guide to migrate from an Omnibus-based deployment to a Docker-based
-deployment. In most cases this can be done with minimal downtime and without
-requiring you to regenerate WireGuard configurations for each device.
-
-Heavily customized deployments (such as those using an external database or
-custom reverse proxy) will likely need extra troubleshooting and manual
-steps taken to perform a successful migration.
-
-Take a look at the [migration script source
-](https://github.com/firezone/firezone/blob/master/scripts/docker_migrate.sh)
-to get a detailed idea of the steps involved.
-
-Estimated time to complete: **2 hours**.
-
-## Steps to migrate
-
-1. **Back up** your server. This ensures you have a working state to roll back to
- in case anything goes terribly wrong. At a _bare minimum_ you'll want to back up the
- [file and directories Firezone uses
- ](/docs/reference/file-and-directory-locations/), but we recommend taking a full
- snapshot of your VPS if possible.
-1. Ensure you're running the latest version of Firezone. See our [upgrade guide
- ](/docs/administer/upgrade/) if not.
-1. Install the latest version of [**Docker**
- ](https://docs.docker.com/engine/install/) and [Docker Compose
- ](https://docs.docker.com/compose/install/linux/#install-compose)
- for your OS. **Docker Compose version 2 or higher is required**.
- We recommend using Docker Server for Linux. Docker Desktop will work too, but is not
- preferred for production use cases at this time because it rewrites packets under
- some conditions and may cause unexpected issues with Firezone.
-1. Download and run the migration script:
-
-```bash
-bash <(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/docker_migrate.sh)
-```
-
-This will ask you a few questions, then attempt to migrate your installation to
-Docker. If all goes well, your Firezone instance should be running with Docker, data intact.
-
-## Rolling back
-
-If anything goes wrong, you can abort the migration by simply bringing the Docker
-services down and the Omnibus ones back up:
-
-```bash
-docker-compose down
-sudo firezone-ctl start
-```
-
-If you've found a bug, please [open a GitHub issue](https://github.com/firezone/firezone/issues) with the error output and
-any steps needed to reproduce.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/administer/regen-keys.mdx b/www/docs/administer/regen-keys.mdx
deleted file mode 100644
index c9abd1250..000000000
--- a/www/docs/administer/regen-keys.mdx
+++ /dev/null
@@ -1,67 +0,0 @@
----
-title: Regenerate Secret Keys
-sidebar_position: 7
----
-
-When you install Firezone, secrets are generated for encrypting database
-fields, securing WireGuard tunnels, securing cookie sessions, and more.
-
-If you're looking to regenerate one or more of these secrets, it's possible
-to do so using the same bootstrap scripts that were used when installing
-Firezone.
-
-## Regenerate secrets
-
-:::warning
-Replacing the `DATABASE_ENCRYPTION_KEY` will render all encrypted data in the
-database useless. This **will** break your Firezone install unless you are
-starting with an empty database. You have been warned.
-:::
-
-:::caution
-Replacing `GUARDIAN_SECRET_KEY`, `SECRET_KEY_BASE`, `LIVE_VIEW_SIGNING_SALT`,
-`COOKIE_SIGNING_SALT`, and `COOKIE_ENCRYPTION_SALT` will reset all browser
-sessions and REST API tokens.
-:::
-
-Use the procedure below to regenerate secrets:
-
-
-
-
-Navigate to the Firezone installation directory, then:
-
-```bash
-mv .env .env.bak
-docker run firezone/firezone bin/gen-env > .env
-```
-
-Now, move desired env vars from `.env.bak` back to `.env`, keeping
-the new secrets intact.
-
-
-
-
-## Regenerate WireGuard private key
-
-:::warning
-Replacing the WireGuard private key will render all existing device configs
-invalid. Only do so if you're prepared to also regenerate device configs
-after regenerating the WireGuard private key.
-:::
-
-To regenerate WireGuard private key, simply move or rename the private key file.
-Firezone will generate a new one on next start.
-
-
-
-
-```bash
-cd $HOME/.firezone
-docker-compose stop firezone
-sudo mv firezone/private_key firezone/private_key.bak
-docker-compose start firezone
-```
-
-
-
diff --git a/www/docs/administer/troubleshoot.mdx b/www/docs/administer/troubleshoot.mdx
deleted file mode 100644
index 01e722646..000000000
--- a/www/docs/administer/troubleshoot.mdx
+++ /dev/null
@@ -1,153 +0,0 @@
----
-title: Troubleshoot
-sidebar_position: 6
-description: Troubleshoot common connectivity and configuration issues with Firezone's WireGuard®-based secure access platform.
----
-
-This guide documents common configuration and connectivity issues. For
-any problems that arise, a good first bet is to check the Firezone logs.
-
-
-
-
-Each container stores logs as a JSON file on the host machine. These can be shown with the
-`docker logs {CONTAINER}` command. Log files are found at
-`var/lib/docker/containers/{CONTAINER_ID}/{CONTAINER_ID}-json.log` by default.
-
-See [debug logs](../debug-logs) for additional details.
-
-
-
-
-## Application crash loop preventing config changes
-
-In cases where the application is crash looping because of corrupt, inaccessible, or
-invalid OIDC or SAML configuration in the DB, you can try clearing the affected fields.
-
-For example, to clear OIDC configs:
-
-
-
-
-```text
-psql -d firezone -h 127.0.0.1 -U postgres -c "UPDATE configurations SET openid_connect_providers = '[]'"
-```
-
-Similarly, to clear SAML configs:
-
-```text
-psql -d firezone -h 127.0.0.1 -U postgres -c "UPDATE configurations SET saml_identity_providers = '[]'"
-```
-
-
-
-
-## Debugging WebSocket connectivity issues
-
-The Web UI requires a secure websocket connection to function.
-If a secure websocket connection can't be established, you'll see a red dot
-indicator in the upper-right portion of the Firezone web UI and a corresponding
-message when you hover over it:
-
-```text
-Secure websocket not connected! ...
-```
-
-If you're accessing Firezone using the same URL defined in your
-`EXTERNAL_URL` variable from above, the issue is likely to be in your reverse
-proxy configuration. Ensure your reverse proxy has WebSocket support enabled
-for Firezone. If you're using the default Caddy reverse proxy, WebSocket
-is enabled and configured automatically.
-
-In most cases, you'll find clues in one or more of the following locations:
-
-
-
-## Debugging WireGuard connectivity issues
-
-Most connectivity issues with Firezone are caused by other `iptables` or
-`nftables` rules which interfere with Firezone's operation. If you have rules
-active, you'll need to ensure these don't conflict with the Firezone rules.
-
-### Internet connectivity drops when tunnel is active
-
-If your Internet connectivity drops whenever you activate your WireGuard
-tunnel, you should make sure that the `FORWARD` chain allows packets
-from your WireGuard clients to the destinations you want to allow through
-Firezone.
-
-If you're using `ufw`, this can be done by making sure the default routing
-policy is `allow`:
-
-```text
-ubuntu@fz:~$ sudo ufw default allow routed
-Default routed policy changed to 'allow'
-(be sure to update your rules accordingly)
-```
-
-A `ufw` status for a typical Firezone server might look like this:
-
-```text
-ubuntu@fz:~$ sudo ufw status verbose
-Status: active
-Logging: on (low)
-Default: deny (incoming), allow (outgoing), allow (routed)
-New profiles: skip
-
-To Action From
--- ------ ----
-22/tcp ALLOW IN Anywhere
-80/tcp ALLOW IN Anywhere
-443/tcp ALLOW IN Anywhere
-51820/udp ALLOW IN Anywhere
-22/tcp (v6) ALLOW IN Anywhere (v6)
-80/tcp (v6) ALLOW IN Anywhere (v6)
-443/tcp (v6) ALLOW IN Anywhere (v6)
-51820/udp (v6) ALLOW IN Anywhere (v6)
-```
-
-## Admin login isn't working
-
-If the password for the account with email `DEFAULT_ADMIN_EMAIL` isn't working, you can
-reset it using the process below.
-
-
-
-
-First change directory to your Firezone installation directory
-(`$HOME/.firezone` by default), then run the `bin/create-or-reset-admin` script
-to reset the admin user's password. The password for the user specified by
-`DEFAULT_ADMIN_EMAIL`
-in `$HOME/.firezone/.env` will be reset to the `DEFAULT_ADMIN_PASSWORD` variable.
-
-```shell
-cd $HOME/.firezone
-docker compose exec firezone bin/create-or-reset-admin
-```
-
-**Note**: If local authentication is disabled, resetting the admin user's
-password will not re-enable it.
-
-
-
-
-## Re-enable local authentication via CLI
-
-If you've configured an [OIDC](/docs/authenticate/oidc/) or [SAML](/docs/authenticate/saml/)
-provider, you can consider disabling local authentication for additional security.
-
-If, however, issues arise with your identity provider integration, it's possible you
-could be locked out of the admin portal. To re-enable local authentication so
-you can log in and resolve the issue, you can temporarily re-enable local authentication
-via the [REST API](/docs/reference/rest-api/configurations).
-
-If that's not an option, you can re-enable local authentication by
-running the following commands on the host of your Firezone instance:
-
-```shell
-cd $HOME/.firezone
-docker compose exec postgres psql -U postgres -h 127.0.0.1 -d firezone -c "UPDATE configurations SET local_auth_enabled = 't'"
-```
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/administer/uninstall.mdx b/www/docs/administer/uninstall.mdx
deleted file mode 100644
index 7c4bd94fc..000000000
--- a/www/docs/administer/uninstall.mdx
+++ /dev/null
@@ -1,37 +0,0 @@
----
-title: Uninstall
-sidebar_position: 5
----
-
-Firezone can be uninstalled using the steps below.
-
-:::warning
-This will irreversibly destroy ALL Firezone data and can't be undone.
-:::
-
-
-
-
-For docker-based deployments, simply bring the firezone services down,
-then delete the working directory where you installed the Firezone docker
-files (`$HOME/.firezone` by default):
-
-```bash
-# default install dir
-installDir=$HOME/.firezone
-docker compose -f $installDir/docker-compose.yml down -v
-rm -rf $installDir
-```
-
-
-
-
-To completely remove Omnibus-based deployments of Firezone run the [uninstall.sh
-script](https://github.com/firezone/firezone/blob/master/scripts/omnibus-uninstall.sh):
-
-```bash
-sudo /bin/bash -c "$(curl -fsSL https://github.com/firezone/firezone/raw/master/scripts/omnibus-uninstall.sh)"
-```
-
-
-
diff --git a/www/docs/administer/upgrade.mdx b/www/docs/administer/upgrade.mdx
deleted file mode 100644
index ee2504b12..000000000
--- a/www/docs/administer/upgrade.mdx
+++ /dev/null
@@ -1,283 +0,0 @@
----
-title: Upgrade
-sidebar_position: 3
----
-
-Upgrading Firezone will pause all VPN sessions and temporarily bring
-down the web UI.
-
-:::info
-Automatic rollbacks are still under development. We recommend backing up
-relevant [files and folders](/docs/reference/file-and-directory-locations/)
-before upgrading in case anything goes wrong.
-:::
-
-Follow the steps below to upgrade Firezone:
-
-
-
-
-1. Change to your Firezone installation directory, by default `$HOME/.firezone`:
-
-```
-cd $HOME/.firezone
-```
-
-1. If your `.env` file has a `VERSION` variable, update it to the desired version.
- By default `latest` is assumed if not set. This variable is read in newer versions
- of the docker-compose.yml template to populate the `image:` key for the `firezone`
- service.
-1. Update service images:
-
-```
-docker compose pull
-```
-
-1. Re-up the services (**warning: this will restart updated services**):
-
-```
-docker compose up -d
-```
-
-
-
-
-1. If not setup already, install our package repository based on your distro's
- package format:
-
-- [deb packages](https://cloudsmith.io/~firezone/repos/firezone/setup/#formats-deb)
-- [rpm packages](https://cloudsmith.io/~firezone/repos/firezone/setup/#formats-rpm)
-
-1. Upgrade the `firezone` package using your distro's package manager.
-1. Run `firezone-ctl reconfigure` to pick up the new changes.
-1. Run `firezone-ctl restart` to restart services.
-
-
-
-
-If you hit any issues, please let us know by [filing an
-issue](https://github.com/firezone/firezone/issues/new/choose).
-
-## Upgrading to 0.7.x
-
-Firezone 0.7.0 introduces a new [REST API](/docs/reference/rest-api/) that allows administrators
-to automate much of the day to day configuration of Firezone.
-
-The REST API `/v0/configuration` endpoint supersedes some of the previous environment
-variables used for WireGuard server configuration.
-
-If you're running Firezone < 0.6, we recommend updating to the latest
-0.6.x release **before** upgrading to 0.7. This will ensure any environment variables
-are properly parsed and migrated into the DB as runtime `configurations`.
-
-**Note**: Omnibus deployments are deprecated in 0.7.x and will be removed in Firezone
-0.8 and above. We recommend [migrating your installation](/docs/administer/migrate/) to
-Docker if you haven't done so already.
-
-## Upgrading to >= 0.6.12
-
-### WIREGUARD\_\* env vars
-
-Firezone 0.6.12 moves the `WIREGUARD_ALLOWED_IPS`, `WIREGUARD_PERSISTENT_KEEPALIVE`,
-and `WIREGUARD_DNS` environment variables to the database to be configured in the
-UI at `/settings/client_defaults`. If the corresponding value at
-`/settings/client_defaults` was empty, the environment variable's value was used to
-populate the field.
-
-This is a small step in our quest to move more runtime configuration from environment
-variables to the DB.
-
-### `AUTH_OIDC_JSON` config
-
-Similar to the `WIREGUARD_*` env vars above, the `AUTH_OIDC_JSON` env var has similarly
-been moved to the database and can be configured at `/settings/site`. In Firezone 0.7 this
-is now configurable via the [REST API](/docs/reference/rest-api/configurations) as well.
-
-### Fix IPv6
-
-0.6.12 fixes IPv6 routing within Docker networks.
-To enable, add IPv6 addresses to your `$HOME/.firezone/docker-compose.yml` by setting the following fields:
-
-```yaml
-services:
- firezone:
- networks:
- firezone-network:
- ipv6_address: 2001:3990:3990::99
-
-# ...
-networks:
- firezone-network:
- ipam:
- config:
- - subnet: 2001:3990:3990::/64
- - gateway: 2001:3990:3990::1
-```
-
-You also need to update the Docker daemon to enable IPv6. See our [IPv6 guide](/docs/deploy/docker/#step-4-enable-ipv6-optional) for more info.
-
-## Upgrading from 0.5.x to 0.6.x
-
-Firezone 0.6 introduces **Docker support**, SAML 2.0 authentication,
-more granular user provisioning options, and a slew of minor improvements and bugfixes.
-
-### Migrate to Docker
-
-Docker is now the preferred way to deploy and manage Firezone. See the [migration
-guide](/docs/administer/migrate/) to migrate today. In most cases this can be done in a few minutes
-using our automatic migration script.
-
-### Update Configuration
-
-Some configuration variables have recently moved to the DB in order to be configurable
-at runtime. Check the [configure guide](/docs/deploy/configure/) for more information.
-
-## Upgrading from < 0.5.0 to >= 0.5.0
-
-0.5.0 introduces a few breaking changes and configuration updates that will need
-to be addressed. Read more below.
-
-### Bundled Nginx non_ssl_port (HTTP) requests removed
-
-0.5.0 and above removes the `force_ssl` and `non_ssl_port` settings for
-Nginx. SSL is required for Firezone to function; if you're using (or would like
-to use) your own reverse proxy, we recommend disabling the bundle Nginx service
-by setting `default['firezone']['nginx']['enabled'] = false` and pointing your
-reverse proxy directly to the Phoenix app on port 13000 (by default).
-
-Read more about setting up a custom reverse proxy
-[here](/docs/deploy/advanced/reverse-proxy/).
-
-### ACME protocol support
-
-0.5.0 introduces ACME protocol support for automatically renewing SSL
-certificates with the bundled Nginx service. To enable,
-
-- Make sure `default['firezone']['external_url']` contains a valid FQDN that
- resolves to your server's public IP address.
-
-- Ensure port `80/tcp` is reachable
-
-- Enable ACME protocol support with
- `default['firezone']['ssl']['acme']['enabled'] = true` in your config file.
-
-### Overlapping egress rule destinations
-
-Firezone 0.5.0 removes the ability to add rules with overlapping destinations.
-When upgrading to 0.5.0, our migration script will automatically detect these
-cases and **keep only the rules whose destination encompasses the other rule**.
-If this is OK, **there is nothing you need to do**.
-
-Otherwise, we recommend modifying your ruleset to eliminate these cases before
-upgrading.
-
-### Preconfigured Okta and Google SSO
-
-Firezone 0.5.0 removes support for the old-style Okta and Google SSO
-configuration in favor of the new, more flexible OIDC-based configuration.
-If you have any configuration under the
-`default['firezone']['authentication']['okta']` or
-`default['firezone']['authentication']['google']` keys, **you need to migrate
-these to our OIDC-based configuration using the guide below.**
-
-#### Existing Google OAuth configuration
-
-Remove these lines containing the old Google OAuth configs from your configuration
-file located at `/etc/firezone/firezone.rb`
-
-```rb
-default['firezone']['authentication']['google']['enabled']
-default['firezone']['authentication']['google']['client_id']
-default['firezone']['authentication']['google']['client_secret']
-default['firezone']['authentication']['google']['redirect_uri']
-```
-
-Then, follow the instructions [here](/docs/authenticate/oidc/google/) to configure Google
-as an OIDC provider.
-
-#### Existing Okta OAuth configuration
-
-Remove these lines containing the old Okta OAuth configs from your configuration
-file located at `/etc/firezone/firezone.rb`
-
-```rb
-default['firezone']['authentication']['okta']['enabled']
-default['firezone']['authentication']['okta']['client_id']
-default['firezone']['authentication']['okta']['client_secret']
-default['firezone']['authentication']['okta']['site']
-```
-
-Then, follow the instructions [here](/docs/authenticate/oidc/okta/) to configure Okta as
-an OIDC provider.
-
-## Upgrading from 0.3.x to >= 0.3.16
-
-Follow the instructions below based on your current version and setup:
-
-### I have an existing OIDC integration
-
-Upgrading to >= 0.3.16 requires the `offline_access` scope for some OIDC providers
-to obtain a refresh token.
-This ensures Firezone syncs with the identity provider and VPN access is terminated
-once the user is removed. Previous versions of Firezone do not have this capability.
-Users who are removed from your identity provider will still have active VPN sessions
-in some cases.
-
-For OIDC providers that support the `offline_access` scope, you will need to add
-`offline_access` to the `scope` parameter of your OIDC config. The
-Firezone configuration file can be found at `/etc/firezone/firezone.rb` and requires
-running `firezone-ctl reconfigure` to pick up the changes.
-
-If Firezone is able to successfully retrieve the refresh token, you will see
-the **OIDC Connections** heading in the user details page of the web UI for
-users authenticated through your OIDC provider.
-
-
-
-If this does not work, you will need to delete your existing OAuth app
-and repeat the OIDC setup steps to
-[create a new app integration](/docs/authenticate/oidc/) .
-
-### I have an existing OAuth integration
-
-Prior to 0.3.11, Firezone used pre-configured OAuth2 providers. Follow the
-instructions [here](/docs/authenticate/oidc/) to migrate to OIDC.
-
-### I have not integrated an identity provider
-
-No action needed. You can follow the instructions
-[here](/docs/authenticate/oidc)
-to enable SSO through an OIDC provider.
-
-## Upgrading from 0.3.1 to >= 0.3.2
-
-The configuration option `default['firezone']['fqdn']` has been removed in favor
-of `default['firezone']['external_url']`. Please set this to the
-publicly-accessible URL of your Firezone web portal. If left unspecified it will
-default to `https://` + the FQDN of your server.
-
-Reminder, the configuration file can be found at `/etc/firezone/firezone.rb`.
-For an exhaustive list of configuration variables and their descriptions, see the
-[configuration file reference](/docs/reference/configuration-file).
-
-## Upgrading from 0.2.x to 0.3.x
-
-Starting with version 0.3.0, Firezone no longer stores device private
-keys on the Firezone server. Any existing devices should continue to function
-as-is, but you will not be able to re-download or view these configurations in
-the Firezone Web UI.
-
-## Upgrading from 0.1.x to 0.2.x
-
-Firezone 0.2.x contains some configuration file changes that will need to be
-handled manually if you're upgrading from 0.1.x. Run the commands below as root
-to perform the needed changes to your `/etc/firezone/firezone.rb` file.
-
-```bash
-cp /etc/firezone/firezone.rb /etc/firezone/firezone.rb.bak
-sed -i "s/\['enable'\]/\['enabled'\]/" /etc/firezone/firezone.rb
-echo "default['firezone']['connectivity_checks']['enabled'] = true" >> /etc/firezone/firezone.rb
-echo "default['firezone']['connectivity_checks']['interval'] = 3_600" >> /etc/firezone/firezone.rb
-firezone-ctl reconfigure
-firezone-ctl restart
-```
diff --git a/www/docs/authenticate/README.mdx b/www/docs/authenticate/README.mdx
deleted file mode 100644
index a989df386..000000000
--- a/www/docs/authenticate/README.mdx
+++ /dev/null
@@ -1,93 +0,0 @@
----
-title: Authenticate
-sidebar_position: 3
----
-
-Firezone supports the following authentication methods:
-
-1. [Local email/password (default)](local-auth)
-1. [SSO authentication via OpenID Connect](oidc)
-1. [SSO authentication via SAML 2.0](saml)
-
-:::note
-If your Identity Provider doesn't work with the methods listed above,
-[contact us](/contact/support) about a custom integration.
-:::
-
-## Integrate an SSO provider
-
-We've included instructions on how to set up Firezone with several popular
-identity providers using our Generic OIDC integration:
-
-- [Okta](oidc/okta)
-- [Azure Active Directory](oidc/azuread)
-- [Google](oidc/google)
-- [Onelogin](oidc/onelogin)
-- [JumpCloud](saml/jumpcloud)
-- [Keycloak](oidc/keycloak)
-- [Zitadel](oidc/zitadel)
-- [Auth0](oidc/auth0)
-
-If your identity provider is not listed above, but has a generic OIDC or SAML
-connector, please consult their documentation to find instructions on obtaining
-the configuration settings required. Instructions for setting up Firezone with any
-generic OIDC provider can be found [here](oidc).
-
-Open a [Github issue](https://github.com/firezone/firezone/issues)
-to request documentation or submit a pull request to add documentation for your
-provider.
-
-### The OIDC redirect URI
-
-For each OIDC provider a corresponding URL is created for redirecting to
-the configured provider's sign-in URL. The URL format is `https://firezone.example.com/auth/oidc/CONFIG_ID`
-where `CONFIG_ID` is the OIDC Config ID for that particular provider.
-
-For example, the OIDC config below:
-
-
-  -
-
-would generate the following OIDC login URL:
-
-- `https://firezone.example.com/auth/oidc/google`
-
-This URL could then be distributed to end users for direct navigation to
-the identity provider's login portal for authentication to Firezone.
-
-## Enforce periodic re-authentication
-
-Periodic re-authentication can be enforced by changing the setting in
-`settings/security`. This can be used to ensure a user must sign in to Firezone
-periodically in order to maintain their VPN session.
-
-You can set the session length to a minimum of **1 hour** and maximum of **90 days**.
-Setting this to Never disables this setting, allowing VPN sessions indefinitely.
-This is the default.
-
-### Re-authentication
-
-To re-authenticate an expired VPN session, a user will need to turn off their
-VPN session and sign in to the Firezone portal (URL specified during
-[deployment](../deploy#prepare-to-deploy)).
-
-See detailed Client Instructions on how to re-authenticate your session
-[here](../user-guides/client-instructions).
-
-#### VPN connection status
-
-A user's connection status is shown on the Users page under the table column
-`VPN Connection`. The connection statuses are:
-
-- ENABLED - The connection is enabled.
-- DISABLED - The connection is disabled by an administrator or OIDC refresh failure.
-- EXPIRED - The connection is disabled due to authentication expiration or a user
- has not signed in for the first time.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/authenticate/local-auth.mdx b/www/docs/authenticate/local-auth.mdx
deleted file mode 100644
index ce3c2c94e..000000000
--- a/www/docs/authenticate/local-auth.mdx
+++ /dev/null
@@ -1,30 +0,0 @@
----
-title: Local Authentication
-sidebar_position: 1
----
-
-# Local authentication (email & password)
-
-By default, Firezone will use local email / password for authenticating users to
-the Firezone portal. Administrators can add users and assign their passwords on
-the `/users` page. See [Add users](/docs/user-guides/add-users/) for more details.
-
-:::caution
-Although local authentication is quick and easy to get started with, you can
-limit attack surface by [disabling local authentication](#disabling-local-authentication)
-altogether. See our [OIDC](/docs/authenticate/oidc/) or [SAML](/docs/authenticate/saml/) guides
-for details. For production deployments it's usually a good idea to **disable
-local authentication** and enforce MFA through your identity provider.
-:::
-
-If you choose to keep Local authentication enabled, we recommend [enabling TOTP-based MFA
-](/docs/authenticate/multi-factor/) for any accounts that use the local authentication method.
-
-## Disabling local authentication
-
-Local authentication can be enabled or disabled from the `/settings/security` page
-or via the [REST API](/docs/reference/rest-api/configurations).
-If you've disabled local authentication and can no longer authenticate to the portal
-to re-enable it, see our [troubleshooting guide
-](/docs/administer/troubleshoot#re-enable-local-authentication-via-cli) for re-enabling
-local authentication from the CLI.
diff --git a/www/docs/authenticate/multi-factor.mdx b/www/docs/authenticate/multi-factor.mdx
deleted file mode 100644
index e206a48a7..000000000
--- a/www/docs/authenticate/multi-factor.mdx
+++ /dev/null
@@ -1,40 +0,0 @@
----
-title: Multi-Factor Authentication
-sidebar_position: 2
-description:
- Enforce multi-factor authentication with Firezone's WireGuard®-based
- secure access platform.
----
-
-# Multi-factor authentication (MFA)
-
-You have two options for activating MFA with Firezone:
-
-1. Enable a TOTP-based second factor for the local email/password
-authentication method.
-1. Configure Firezone to SSO via one of our [supported identity providers
-](../#integrate-an-sso-provider) and enable MFA through the identity provider.
-
-## MFA with Firezone
-
-Firezone currently supports using a time-based one time password
-(TOTP) as an additional factor. This is supported with the local authentication
-method only; for SSO authentication we recommend enabling your provider's MFA
-functionality [as described below](#mfa-with-identity-provider).
-
-Admins can visit `/settings/account/register_mfa` in the admin portal to
-generate a QR code to be scanned by your authenticator app.
-
-Unprivileged users can visit `/user_account/register_mfa` after logging into
-the user portal.
-
-## MFA with your identity provider
-
-Most identity providers support additional authentication factors in addition to
-email/password. Consult your provider's documentation to enforce an
-additional factor. We have included links to a few common providers below:
-
-* [Okta](https://help.okta.com/en-us/Content/Topics/Security/mfa/mfa-home.htm)
-* [Azure AD](https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-mfa-howitworks)
-* [Google](https://support.google.com/a/answer/175197)
-* [Onelogin](https://www.onelogin.com/getting-started/free-trial-plan/add-mfa)
diff --git a/www/docs/authenticate/oidc/README.mdx b/www/docs/authenticate/oidc/README.mdx
deleted file mode 100644
index 49771de7c..000000000
--- a/www/docs/authenticate/oidc/README.mdx
+++ /dev/null
@@ -1,66 +0,0 @@
----
-title: OpenID Connect
-sidebar_position: 10
-description: Setup single sign-on with your identity provider. Integrate
- providers like Okta, Google, Azure, and JumpCloud using Firezone's
- OpenID Connect (OIDC) connector.
----
-
-# Integrate your identity provider using OIDC
-
-Firezone supports Single Sign-On (SSO) via OpenID Connect (OIDC).
-
-## Supported identity providers
-
-In general, most identity providers that offer OIDC support work with Firezone. Some providers
-that only implement the OIDC partially or use uncommon configurations may have
-issues, however. If your identity provider falls into this category, [contact us
-](/contact/support) about a custom integration.
-
-The following OIDC providers are known to work well with Firezone:
-
-| Provider | Support Status | Notes |
-| ------------------------------------- | ------------------------------ | ------------------------------------------------------------------------------------------------------------------------------------------------------ |
-| [Azure Active Directory](azuread) | **Fully tested and supported** | Ensure the [`email` claim](https://learn.microsoft.com/en-us/azure/active-directory/develop/active-directory-optional-claims) is present in the token. |
-| [Okta](okta) | **Fully tested and supported** | |
-| [Onelogin](onelogin) | **Fully tested and supported** | |
-| [Keycloak](https://www.keycloak.org/) | **Fully tested and supported** | |
-| [Auth0](auth0) | **Fully tested and supported** | Auth0 does not provide an `end_session_uri` in its OIDC discovery document. Signing out of Auth0 from Firezone is not supported. |
-| [Google Workspace](google) | **Fully tested and supported** | Google does not provide an `end_session_uri` in its OIDC discovery document. Signing out of Google Workspace from Firezone is not supported. |
-| [Zitadel](zitadel) | Untested but known to work | |
-| [Authentik](https://goauthentik.io/) | Untested but known to work | |
-
-## General setup guide
-
-If you're using an OIDC provider not listed above, the following OIDC attributes
-are required for setting up an OIDC provider in Firezone:
-
-1. `discovery_document_uri`: The
- [OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
- which returns a JSON document used to construct subsequent requests to this
- OIDC provider. Some providers refer to this as the "well-known URL".
-1. `client_id`: The client ID of the application.
-1. `client_secret`: The client secret of the application.
-1. `redirect_uri`: Instructs OIDC provider where to redirect after authentication.
- This should be your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
- (e.g. `https://firezone.example.com/auth/oidc/google/callback/`).
-1. `response_type`: Set to `code`.
-1. `scope`: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
- to obtain from your OIDC provider. At a minimum, Firezone requires the `openid`
- and `email` scopes.
-1. `label`: The button label text displayed on the Firezone portal login page.
-
-### PKCE
-
-Firezone supports Proof Key for Code Exchange (PKCE) for increased login security.
-We recommend you enable PKCE in your IdP's settings whenever available. [Read more
-about PKCE here](https://oauth.net/2/pkce/).
-
-### OIDC logout URI
-
-The OpenID Connect standard [defines a mechanism](https://openid.net/specs/openid-connect-rpinitiated-1_0.html)
-for a Relying Party (RP) to request that an OpenID Provider log out the End-User.
-
-Unfortunately, not all IdPs support this (e.g. Google, Auth0). For the providers
-that do support this mechanism, Firezone automatically detects the `end_session_uri`
-found in the provider's discovery document and uses that to log out the End-User.
diff --git a/www/docs/authenticate/oidc/auth0.mdx b/www/docs/authenticate/oidc/auth0.mdx
deleted file mode 100644
index 7f77b990a..000000000
--- a/www/docs/authenticate/oidc/auth0.mdx
+++ /dev/null
@@ -1,69 +0,0 @@
----
-title: Auth0
-sidebar_position: 1
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Auth0
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Auth0 (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Auth0
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `auth0`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Auth0`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this OIDC
-provider.
-
-## Step 1: Obtain OIDC configuration parameters
-
-In the Auth0 dashboard, create an application.
-Select **Regular Web Application** as the application type.
-
-
-
-Next, visit the settings tab on the application details page. Take note and
-modify the following parameters:
-
-1. **Name**: `Firezone`
-1. **Domain**: The domain will be used to construct
-the url to retrieve the OIDC discovery document - `https:///.well-known/openid-configuration`
-1. **Icon**:
-[Firezone icon](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-(save link as).
-1. Set **Allowed Callback URLs** to `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/auth0/callback/`).
-
-
-
-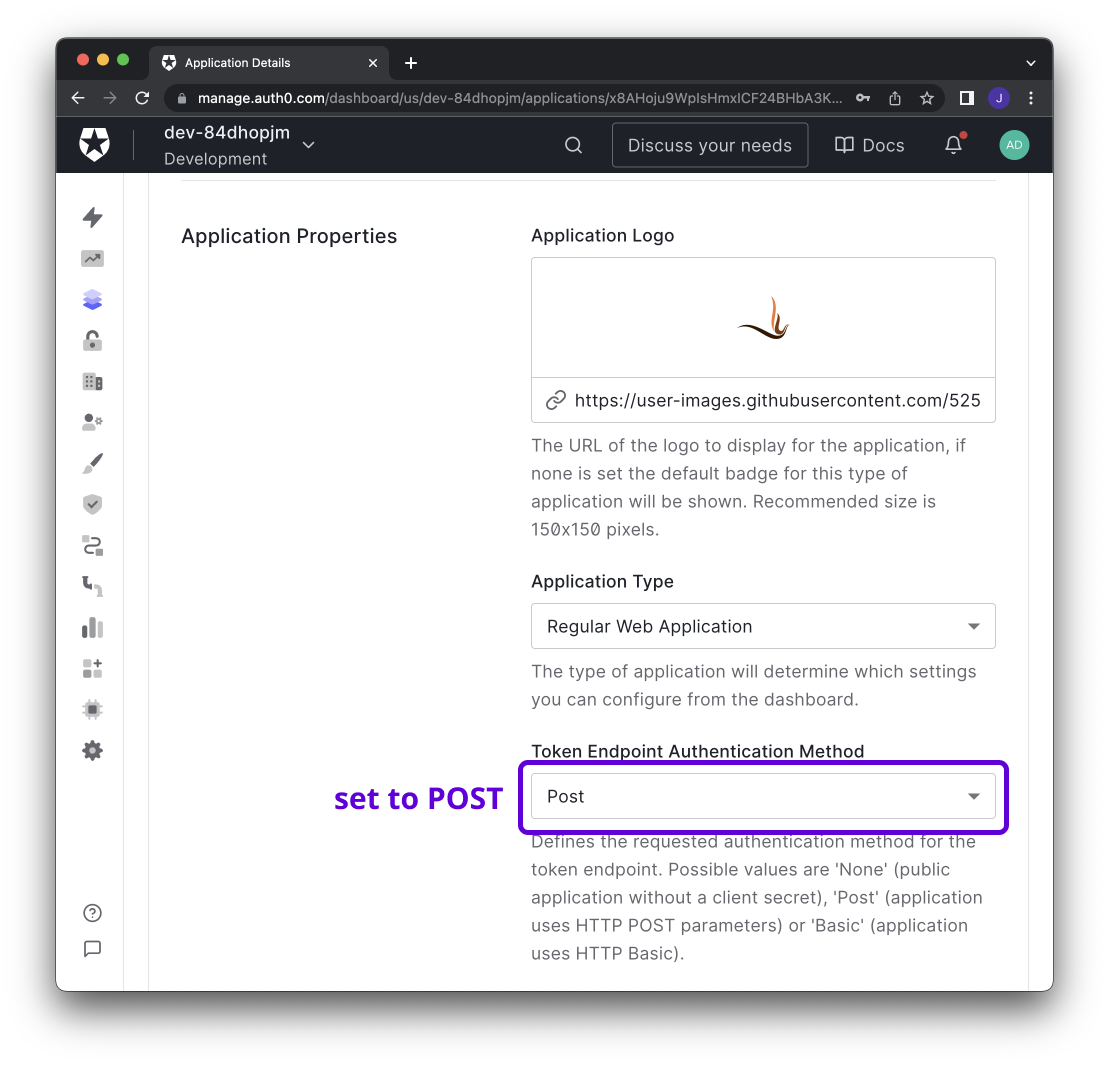
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Auth0` button on the sign in page.
-
-## Step 3 (optional): Restrict access to specific users
-
-Auth0 supports setting access policies to control which users
-can access the Firezone application. See Auth0's
-[Documentation](https://auth0.com/docs/manage-users/user-accounts/manage-user-access-to-applications)
-for details.
diff --git a/www/docs/authenticate/oidc/azuread.mdx b/www/docs/authenticate/oidc/azuread.mdx
deleted file mode 100644
index a30457f6f..000000000
--- a/www/docs/authenticate/oidc/azuread.mdx
+++ /dev/null
@@ -1,82 +0,0 @@
----
-title: Azure Active Directory
-sidebar_position: 2
-description: Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Azure AD
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Azure Active Directory (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Azure Active Directory through the generic
-generic OIDC connector. This guide will walk you through how to obtain the following
-config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `azure`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Azure`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
- to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
- to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
- [OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
- which returns a JSON document used to construct subsequent requests to this
- OIDC provider.
-
-
-
-## Step 1: Obtain configuration parameters
-
-_This guide is adapted from the [Azure Active Directory documentation](https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/auth-oidc)._
-
-Navigate to the Azure Active Directory page on the Azure portal.
-Select the App registrations link under the Manage menu, click
-`New Registration`, and register after entering the following:
-
-1. **Name**: `Firezone`
-1. **Supported account types**: `(Default Directory only - Single tenant)`
-1. **Redirect URI**: This should be your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
- (e.g. `https://firezone.example.com/auth/oidc/azure/callback/`). **Make sure you include the trailing slash both
- when saving the provider in Firezone and in Azure AD (`redirect_uri` field on the screenshot below).**
-
-
-
-After registering, open the details view of the application and copy the
-`Application (client) ID`. **This will be the `client_id` value**. Next, open
-the endpoints menu to retrieve the `OpenID Connect metadata document`.
-**This will be the `discovery_document_uri` value**.
-
-
-
-Next, select the Certificates & secrets link under the Manage menu and
-create a new client secret. Copy the client secret - **this will be the
-`client_secret` value**.
-
-
-
-Lastly, select the API permissions link under the Manage menu,
-click `Add a permission`, and select `Microsoft Graph`. Add `email`, `openid`,
-`offline_access` and `profile` to the required permissions.
-
-
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Azure` button on the sign in page.
-
-## Step 3 (optional): Restrict access to specific users
-
-Azure AD allows admins to restrict OAuth application access to a subset of users
-within your organization. See Microsoft's
-[documentation](https://docs.microsoft.com/en-us/azure/active-directory/develop/howto-restrict-your-app-to-a-set-of-users)
-for more information on how to do this.
diff --git a/www/docs/authenticate/oidc/google.mdx b/www/docs/authenticate/oidc/google.mdx
deleted file mode 100644
index a27e2ee03..000000000
--- a/www/docs/authenticate/oidc/google.mdx
+++ /dev/null
@@ -1,92 +0,0 @@
----
-title: Google Workspace
-sidebar_position: 3
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Google Workspace
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Google Workspace (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Google Workspace and Cloud Identity
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `google`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Google`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-
-
-## Step 1: Configure OAuth consent screen
-
-If this is the first time you are creating a new OAuth client ID, you will
-be asked to configure a consent screen.
-
-**IMPORTANT**: Select `Internal` for user type. This ensures only accounts
-belonging to users in your Google Workspace Organization can create device configs.
-DO NOT select `External` unless you want to enable anyone with a valid Google Account
-to create device configs.
-
-
-
-On the App information screen:
-
-1. **App name**: `Firezone`
-1. **App logo**: [Firezone logo](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-(save link as).
-1. **Application home page**: the URL of your Firezone instance.
-1. **Authorized domains**: the top level domain of your Firezone instance.
-
-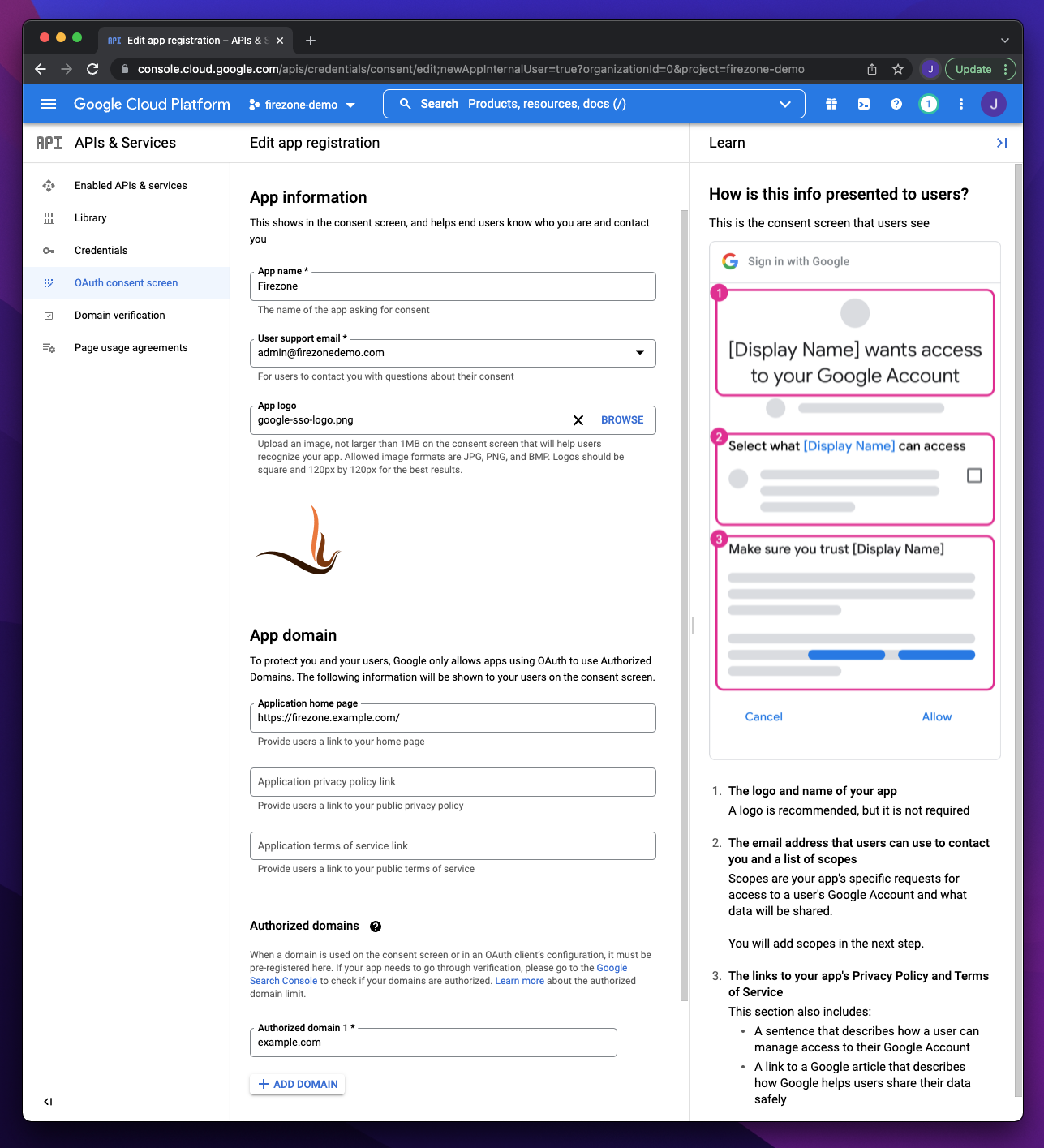
-
-On the next step add the following scopes:
-
-
-
-## Step 2: Create OAuth client
-
-_This section is based off Google's own documentation on
-[setting up OAuth 2.0](https://support.google.com/cloud/answer/6158849)._
-
-Visit the Google Cloud Console
-[Credentials page](https://console.cloud.google.com/apis/credentials)
-page, click `+ Create Credentials` and select `OAuth client ID`.
-
-
-
-On the OAuth client ID creation screen:
-
-1. Set `Application Type` to `Web application`
-1. Add your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/google/callback/`) as an entry to
-Authorized redirect URIs.
-
-
-
-After creating the OAuth client ID, you will be given a Client ID and Client Secret.
-These will be used together with the redirect URI in the next step.
-
-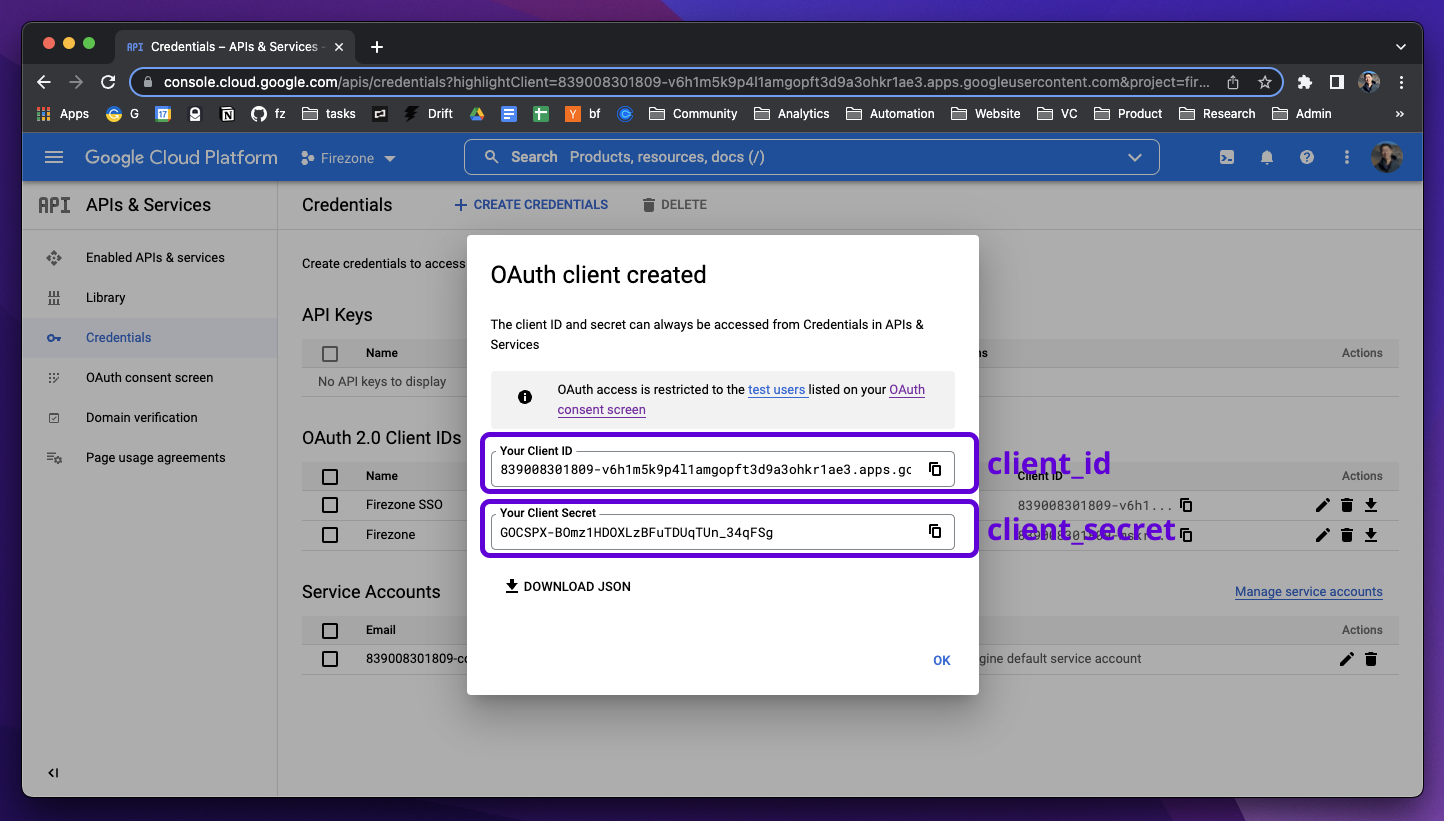
-
-## Step 3: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Google` button on the sign in page.
diff --git a/www/docs/authenticate/oidc/keycloak.mdx b/www/docs/authenticate/oidc/keycloak.mdx
deleted file mode 100644
index 529bfcc3a..000000000
--- a/www/docs/authenticate/oidc/keycloak.mdx
+++ /dev/null
@@ -1,80 +0,0 @@
----
-title: Keycloak
-sidebar_position: 4
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Keycloak
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Keycloak (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Keycloak
-through the generic OIDC provider. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `keycloak`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Keycloak`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-## Step 1: Obtain configuration parameters
-
-In the Keycloak Admin Console, make sure the realm you want to use with Firezone
-is selected.
-
-
-
-### Create Firezone OAuth client
-
-Create a new Client for Firezone by navigating to **Clients > Create Client** and
-configure the following:
-
-1. **Client type**: `OpenID Connect`
-1. **Client ID**: `firezone`
-1. **Name**: `Firezone`
-1. Click **Next**.
-
-
-
-1. Toggle **Client authentication** to `On` to generate the client secret.
-1. Click **Save**.
-
-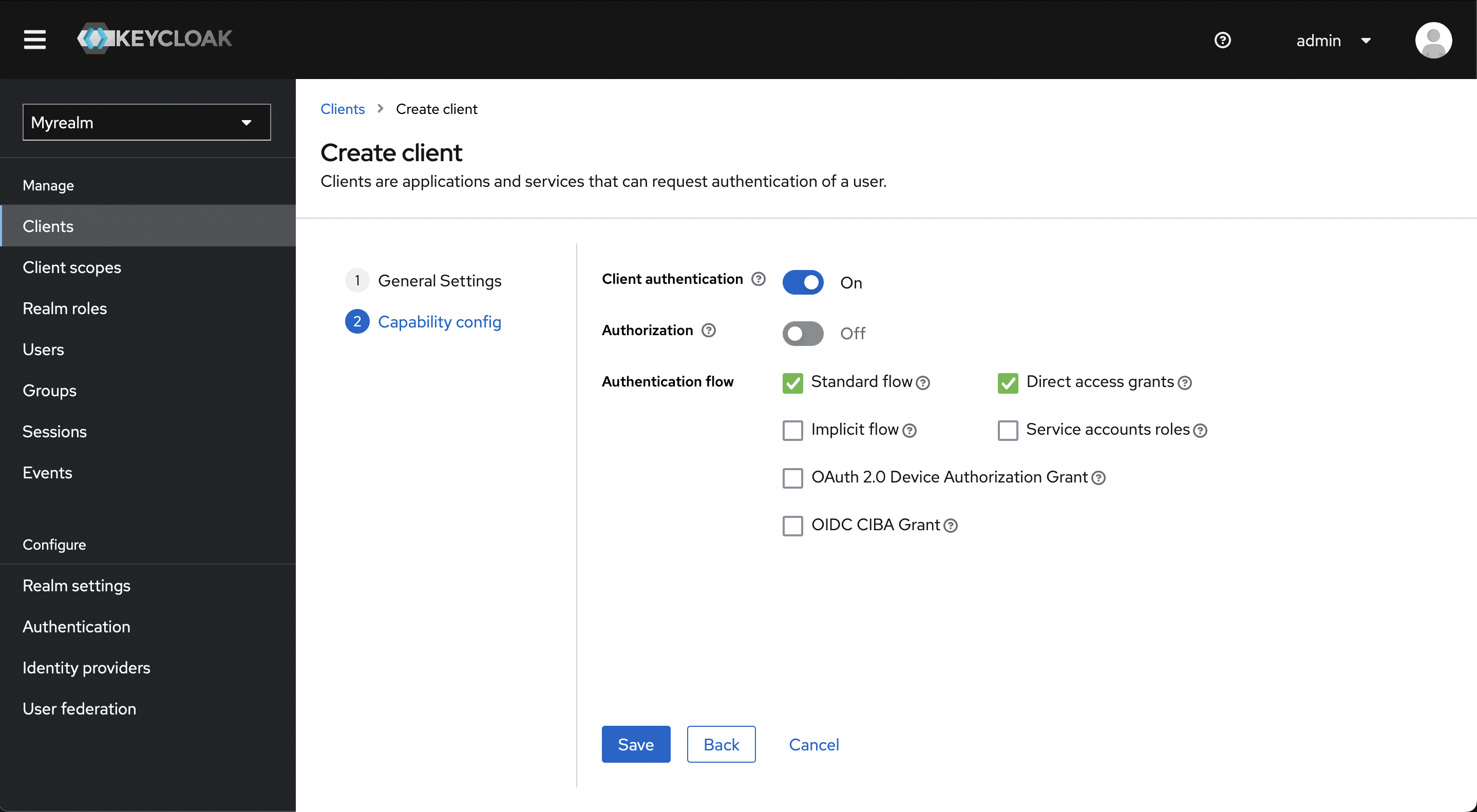
-
-Click **Access settings** to jump to that section and configure the valid redirect URI:
-
-1. **Valid Redirect URIs**: This should be your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/keycloak/callback/`).
-1. Click **Add valid redirect URIs**
-
-
-
-Click the **Credentials** tab and copy the client secret.
-
-
-
-Navigate to the **Realm Settings** page to get the **Discovery Document URI** by
-copying the **OpenID Endpoint Configuration** link at the bottom of the page.
-
-
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Keycloak` button on the sign in page.
diff --git a/www/docs/authenticate/oidc/okta.mdx b/www/docs/authenticate/oidc/okta.mdx
deleted file mode 100644
index 89a4da2e6..000000000
--- a/www/docs/authenticate/oidc/okta.mdx
+++ /dev/null
@@ -1,83 +0,0 @@
----
-title: Okta
-sidebar_position: 5
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Okta
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Okta (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Okta
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `okta`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Okta`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-
-
-## Step 1: Create Okta app integration
-
-_This section of the guide is based on
-[Okta's documentation](https://help.okta.com/en/prod/Content/Topics/Apps/Apps_App_Integration_Wizard_OIDC.htm)._
-
-In the Admin Console, go to **Applications > Applications** and click
-**Create App Integration**. Set **Sign-in method** to **OICD - OpenID Connect**
-and **Application type** to **Web application**.
-
-
-
-On the following screen, configure the following settings:
-
-1. **App Name**: `Firezone`
-1. **App logo**:
-[Firezone logo](https://user-images.githubusercontent.com/52545545/155907625-a4f6c8c2-3952-488d-b244-3c37400846cf.png)
-(save link as).
-1. **Proof Key for Code Exchange (PKCE)**: Check `Require PKCE as additional verification` if you're running Firezone
-0.6.8 or higher. [PKCE](https://oauth.net/2/pkce/) is recommended for increased security whenever possible.
-1. **Grant Type**: Check the **Refresh Token** box. This ensures Firezone syncs
-with the identity provider and VPN access is terminated once the user is removed.
-1. **Sign-in redirect URIs**: Add your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/okta/callback/`) as an entry to
-Authorized redirect URIs.
-1. **Assignments**:
-Limit to the groups you wish to provide access to your Firezone instance.
-
-
-
-Once settings are saved, you will be given a **Client ID**, **Client Secret**,
-and **Okta Domain**. These 3 values will be used in Step 2 to configure Firezone.
-
-
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Okta` button on the sign in page.
-
-## Step 3 (optional): Restrict Access to specific users
-
-Okta can limit the users with access to the Firezone app. To do this,
-go to the Assignments tab of the Firezone App Integration in your Okta
-Admin Console.
-
-
diff --git a/www/docs/authenticate/oidc/onelogin.mdx b/www/docs/authenticate/oidc/onelogin.mdx
deleted file mode 100644
index c043f75d0..000000000
--- a/www/docs/authenticate/oidc/onelogin.mdx
+++ /dev/null
@@ -1,65 +0,0 @@
----
-title: OneLogin
-sidebar_position: 6
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating OneLogin
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with OneLogin (OIDC)
-
-Firezone supports Single Sign-On (SSO) using OneLogin
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `onelogin`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `OneLogin`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-## Step 1: Create custom connector
-
-Create a new OIDC connector by visiting **Appliances > Custom Connectors**.
-
-1. **App name**: `Firezone`
-1. **Icon**: [Firezone logo](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-or
-[Firezone icon](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-(save link as).
-1. **Sign on method**: select **OpenID Connect**
-1. **Redirect URI**: Add your Firezone ` + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/onelogin/callback/`).
-
-
-
-## Step 2: Obtain configuration parameters
-
-Next, click **Add App to Connector** to create an OIDC application.
-Visit the **SSO** tab, then change the token endpoint authentication method
-to **POST**.
-
-You will find the values for the config settings required by Firezone
-on this page as well.
-
-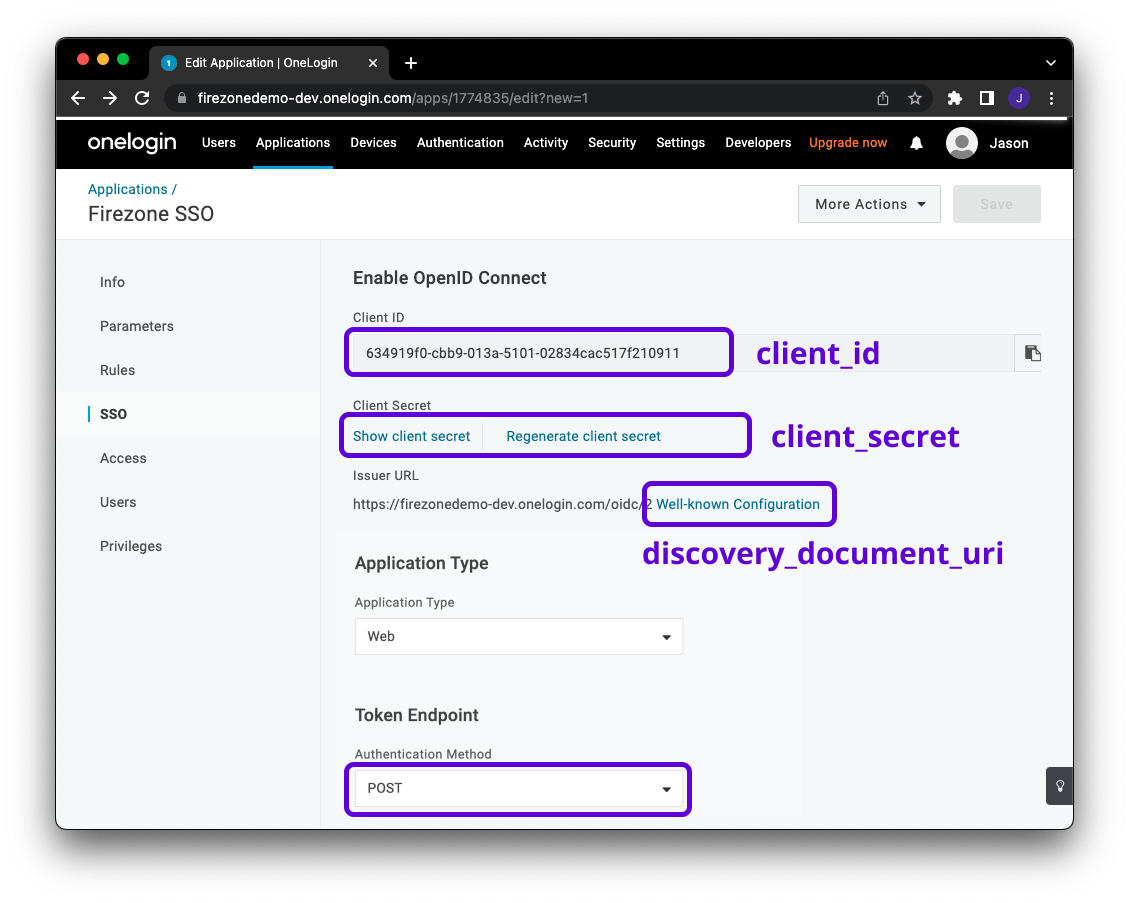
-
-## Step 3: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with OneLogin` button on the sign in page.
diff --git a/www/docs/authenticate/oidc/zitadel.mdx b/www/docs/authenticate/oidc/zitadel.mdx
deleted file mode 100644
index c44182311..000000000
--- a/www/docs/authenticate/oidc/zitadel.mdx
+++ /dev/null
@@ -1,103 +0,0 @@
----
-title: Zitadel
-sidebar_position: 7
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Zitadel
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Zitadel (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Zitadel
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `zitadel`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Zitadel`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-
-
-## Requirements
-
-* Setup your own [Zitadel Cloud](https://zitadel.cloud/) account.
-* Create your first Zitadel instance in the
- [Zitadel Customer portal](https://zitadel.cloud/admin/instances)
-* Login to your Zitadel instance and create a project (i.e. "Internal")
-
-More information about these steps can be found in
-[Zitadel's documentation](https://docs.zitadel.com/docs/guides/start/quickstart#try-out-zitadel-cloud).
-
-## Create Zitadel Application
-
-In the Instance Console, go to **Projects** and select the project you want,
-then click **New**.
-
-
-
-Give the application a name (e.g. "Firezone") and select **WEB**
-for the application type.
-
-
-
-Select **CODE** for the authentication method.
-
-
-
-Specify the redirect URI and post logout URI.
-
-1. **Redirect URIs**: `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://vpn.example.com/auth/oidc/zitadel/callback/`)
-1. **Post Logout URIs**: `EXTERNAL_URL` (e.g. `https://vpn.example.com`)
-
-
-
-Double-check the configuration, then click **Create**.
-
-
-
-Copy the **ClientId** and **ClientSecret** as it will be used for the Firezone
-configuration.
-
-
-
-In the application **Configuration** click **Refresh Token** and then on
-**Save**. The refresh token is optional for some features of Firezone.
-
-
-
-In the application **Token Settings** select **User roles inside ID Token** and
-**User Info inside ID Token**. Save it with a click on **Save**.
-
-
-
-## Integrate With Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Zitadel` button on the sign in page.
-
-## Step 3 (optional): Restrict access to specific users
-
-Zitadel can limit which users have access to Firezone. To do this,
-go to the project where your created your application. In **General** you can
-find **Check Authorization on Authentication** which allows only users with at
-least one role to login to Firezone.
-
-
diff --git a/www/docs/authenticate/saml/README.mdx b/www/docs/authenticate/saml/README.mdx
deleted file mode 100644
index 9c6c09f27..000000000
--- a/www/docs/authenticate/saml/README.mdx
+++ /dev/null
@@ -1,81 +0,0 @@
----
-title: SAML 2.0
-sidebar_position: 11
-description: Enforce single sign-on with your identity provider. Integrate
- providers like Okta, Google, OneLogin, and JumpCloud using Firezone's
- SAML 2.0 connector.
----
-
-# Integrate your identity provider using SAML 2.0
-
-Firezone supports Single Sign-On (SSO) via SAML 2.0.
-
-## Supported identity providers
-
-In general, most identity providers that support SAML 2.0 should work with
-Firezone.
-
-| Provider | Support Status | Notes |
-| -------------------------- | ------------------------ | ---------------------------------- |
-| [Okta](okta) | **Tested and supported** | |
-| [Google Workspace](google) | **Tested and supported** | Uncheck `Require signed envelopes` |
-| [OneLogin](onelogin) | **Tested and supported** | |
-| [JumpCloud](jumpcloud) | **Tested and supported** | Uncheck `Require signed envelopes` |
-
-Occasionally, providers that don't implement the full SAML 2.0 standard or use
-uncommon configurations may be problematic. If this is the case, [contact us](/contact/support)
-about a custom integration.
-
-## Custom SAML cert and keyfile
-
-SAML 2.0 requires a set of private and public keys using the RSA or
-DSA algorithms along with an X.509 certificate that contains the public key.
-
-Firezone automatically generates these for on both Docker and Omnibus-based
-deployments. If you'd like to use your own cert and key, however, you can generate
-them with `openssl`:
-
-```
-openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout saml.key -out saml.crt
-```
-
-Then use them with your Firezone installation:
-
-
-
-
-Set the `SAML_KEYFILE_PATH` and `SAML_CERTFILE_PATH` environment variables to
-the path containing your `saml.key` and `saml.crt` above. If using our [example
-docker compose file](https://github.com/firezone/firezone/blob/master/docker-compose.prod.yml),
-which includes a volume for mapping configuration,
-save these files to `$HOME/.firezone/firezone` on the Docker host and set the
-`SAML_KEYFILE_PATH=/var/firezone/saml.key` and
-`SAML_CERTFILE_PATH=/var/firezone/saml.crt` environment variables for the Firezone
-container.
-
-
-
-
-## General setup instructions
-
-Once you've configured Firezone with an X.509 certificate and corresponding
-private key as shown above, you'll need a few more things to set up a generic
-SAML integration.
-
-### IdP metadata document
-
-You'll need to get the SAML Metadata XML document from your identity provider. In most
-cases this can be downloaded from your IdP's SAML App configuration dashboard.
-
-### ACS URL
-
-Firezone constructs the ACS URL based on the Base URL and Configuration ID entered
-in the Firezone SAML configuration, defaulting to: `EXTERNAL_URL/auth/saml/sp/consume/:config_id`,
-e.g. `https://firezone.company.com/auth/saml/sp/consume/okta`.
-
-### Entity ID
-
-The Firezone Entity ID can be configured with the `SAML_ENTITY_ID` environment variable
-and defaults to `urn:firezone.dev:firezone-app` if not set.
-
-See the [environment variable reference](/docs/reference/env-vars) for more information.
diff --git a/www/docs/authenticate/saml/google.mdx b/www/docs/authenticate/saml/google.mdx
deleted file mode 100644
index c40e9d352..000000000
--- a/www/docs/authenticate/saml/google.mdx
+++ /dev/null
@@ -1,54 +0,0 @@
----
-title: Google Workspace
-sidebar_position: 2
-description:
- Enforce 2FA/MFA using Google Workspace for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Google Workspace
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with Google Workspace (SAML 2.0)
-
-Firezone supports Single Sign-On (SSO) using Google through the generic SAML 2.0
-connector. This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the Google Workspace admin portal, create a new SAML app under
-the Application > Web and mobile apps tab. Use the following config values during setup:
-
-| Setting | Value |
-| --------------- | ---------------------------------------------------------------------------------------------------------------------------------------- |
-| App name | Firezone |
-| App icon | [save link as](https://user-images.githubusercontent.com/52545545/202567638-513dba14-ea8c-4da8-8f75-341310f1e456.png) |
-| ACS URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/google`). |
-| Entity ID | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| Signed response | Unchecked. |
-| Name ID format | Unspecified |
-| Name ID | Basic Information > Primary email |
-
-
-
-Once complete, save the changes and download the SAML metadata document. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | --------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | google | Firezone uses this value to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | Google | Appears on the sign in button for authentication. |
-| Metadata | see note | Paste the contents of the SAML metadata document you downloaded in the previous step from Google. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | **Unchecked.** | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-
-
-After saving the SAML config, you should see a `Sign in with Google` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/authenticate/saml/jumpcloud.mdx b/www/docs/authenticate/saml/jumpcloud.mdx
deleted file mode 100644
index db61c4d38..000000000
--- a/www/docs/authenticate/saml/jumpcloud.mdx
+++ /dev/null
@@ -1,71 +0,0 @@
----
-title: JumpCloud
-sidebar_position: 4
-description:
- Enforce 2FA/MFA using JumpCloud for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating JumpCloud
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with JumpCloud (SAML 2.0)
-
-:::note
-This guide assumes you have completed the prerequisite steps
-(e.g. generate self-signed X.509 certificates) outlined [here](/docs/authenticate/saml#prerequisites).
-:::
-
-Firezone supports Single Sign-On (SSO) using JumpCloud through the generic SAML 2.0 connector.
-This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the JumpCloud admin portal, create a new App under
-the SSO tab. At the bottom of the popup window, click `Custom SAML App`.
-
-After entering your desired value for `Display Label`, click the `SSO` tab,
-then use the following configuration values:
-
-| Setting | Value |
-| ------------------------- | ------------------------------------------------------------------------------------------------------------------------------------------ |
-| IdP Entity ID | Any unique string will work, e.g. `firezone-jumpcloud`. |
-| SP Entity ID | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| ACS URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id`, e.g. `https://firezone.company.com/auth/saml/sp/consume/jumpcloud`. |
-| SAMLSubject NameID | `email` |
-| SAMLSubject NameID Format | Leave at the default. |
-| Signature Algorithm | `RSA-SHA256` |
-| Sign Assertion | **Checked**. |
-| Login URL | This is your Firezone `EXTERNAL_URL/auth/saml/auth/signin/:config_id`, e.g. `https://firezone.company.com/auth/saml/auth/signin/jumpcloud` |
-
-Leave the rest of the settings unchanged, then click the `activate` button at the bottom-right.
-
-Your JumpCloud configuration should now resemble the following:
-
-
-
-Now, download the IdP Metadata document by selecting the App you just created
-and then clicking the `export metadata` button in the upper-right. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | ---------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | `jumpcloud` | Firezone uses this value to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | `JumpCloud` | Appears on the sign in button for authentication. |
-| Base URL | Leave unchanged. | |
-| Metadata | see note | Copy-paste the contents of the SAML metadata document you downloaded in the previous step from JumpCloud. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | **Unchecked.** | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-Your Firezone configuration should now resemble the following:
-
-
-
-After saving the SAML config, you should see a `Sign in with JumpCloud` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/authenticate/saml/okta.mdx b/www/docs/authenticate/saml/okta.mdx
deleted file mode 100644
index f0b1ad8c8..000000000
--- a/www/docs/authenticate/saml/okta.mdx
+++ /dev/null
@@ -1,62 +0,0 @@
----
-title: Okta
-sidebar_position: 1
-description: Enforce 2FA/MFA using Okta for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Okta
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with Okta (SAML 2.0)
-
-:::note
-This guide assumes you have completed the prerequisite steps
-(e.g. generate self-signed X.509 certificates) outlined [here](/docs/authenticate/saml#prerequisites).
-:::
-
-Firezone supports Single Sign-On (SSO) using Okta through the generic SAML 2.0 connector. This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the Okta admin portal, create a new app integration under
-the Application tab. Select `SAML 2.0` as the authentication method.
-Use the following config values during setup:
-
-| Setting | Value |
-| ------------------------------ | -------------------------------------------------------------------------------------------------------------------------------------- |
-| App name | Firezone |
-| App logo | [save link as](https://user-images.githubusercontent.com/52545545/155907625-a4f6c8c2-3952-488d-b244-3c37400846cf.png) |
-| Single sign on URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/okta`). |
-| Audience (EntityID) | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| Name ID format | EmailAddress |
-| Application username | Email |
-| Update application username on | Create and update |
-
-[Okta's documentation](https://help.okta.com/oie/en-us/Content/Topics/Apps/Apps_App_Integration_Wizard_SAML.htm)
-contains additional details on the purpose of each configuration setting.
-
-
-
-After creating the SAML connector, visit the `View SAML setup instructions` link in
-the Sign On tab to download the metadata document. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | --------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | Okta | Used to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | Okta | Appears on the sign in button for authentication. |
-| Metadata | see note | Paste the contents of the SAML metadata document you downloaded in the previous step from Okta. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | Checked. | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-
-
-After saving the SAML config, you should see a `Sign in with Okta` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/authenticate/saml/onelogin.mdx b/www/docs/authenticate/saml/onelogin.mdx
deleted file mode 100644
index 73ac6372b..000000000
--- a/www/docs/authenticate/saml/onelogin.mdx
+++ /dev/null
@@ -1,67 +0,0 @@
----
-title: OneLogin
-sidebar_position: 3
-description:
- Enforce 2FA/MFA using Onelogin for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating OneLogin
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with OneLogin (SAML 2.0)
-
-:::note
-This guide assumes you have completed the prerequisite steps
-(e.g. generate self-signed X.509 certificates) outlined [here](/docs/authenticate/saml#prerequisites).
-:::
-
-Firezone supports Single Sign-On (SSO) using OneLogin through the generic SAML 2.0 connector.
-This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the OneLogin admin portal, add an app under the application tab.
-Select `SAML Custom Connector (Advanced)` and provide the appropriate
-configuration settings under the under the configuration tab.
-
-The following fields should be filled out on this page:
-
-| Setting | Value |
-| ---------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
-| Audience (EntityID) | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| Recipient | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/onelogin`). |
-| ACS URL Validator | This field is regex to ensure OneLogin posts the response to the correct URL. For the sample URL below, we can use `^https:\/\/firezone\.company\.com\/auth\/saml\/sp\/consume\/onelogin` |
-| ACS URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/onelogin`). |
-| Login URL | This is your Firezone `EXTERNAL_URL/auth/saml/auth/signin/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/onelogin`). |
-| SAML initiator | Service Provider |
-| SAML signature element | Both |
-| Encrypt Assertion | Checked. |
-
-[OneLogin's docs](https://onelogin.service-now.com/support?id=kb_article&sys_id=912bb23edbde7810fe39dde7489619de&kb_category=93e869b0db185340d5505eea4b961934)
-provide a good overview of each field's purpose.
-
-
-
-Once complete, save the changes and download the SAML metadata document
-found unde the `More Actions` dropdown. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | --------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | `onelogin` | Used to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | `OneLogin` | Appears on the sign in button for authentication. |
-| Metadata | see note | Paste the contents of the SAML metadata document you downloaded in the previous step from OneLogin. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | Checked. | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-
-
-After saving the SAML config, you should see a `Sign in with OneLogin` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/deploy/README.mdx b/www/docs/deploy/README.mdx
deleted file mode 100644
index 136409fe8..000000000
--- a/www/docs/deploy/README.mdx
+++ /dev/null
@@ -1,90 +0,0 @@
----
-title: Deploy
-sidebar_position: 2
-description:
- Install Firezone's WireGuard®-based secure access platform on a support
- host using our Docker (recommended) or Omnibus deployment methods.
----
-
-# Deploy Firezone
-
-Firezone can be deployed on most Docker-supported platforms in a couple of minutes.
-Read more below to get started.
-
-## Step 1: Prepare to deploy
-
-Regardless of which deployment method you choose, you'll need to follow the
-preparation steps below before deploying Firezone to production.
-
-1. [Create a DNS record](#create-a-dns-record)
-1. [Set up SSL](#set-up-ssl)
-1. [Open required firewall ports](#open-required-firewall-ports)
-
-### Create a DNS record
-
-Firezone requires a fully-qualified domain name (e.g. `firezone.company.com`)
-for production use. You'll need to create the appropriate DNS record at your
-registrar to achieve this. Typically this is either an A, CNAME, or AAAA record
-depending on your requirements.
-
-### Set up SSL
-
-You'll need a valid SSL certificate to use Firezone in a production capacity.
-Firezone supports ACME for automatic provisioning of SSL certificates for both
-Docker-based and Omnibus-based installations. This is recommended in most cases.
-
-
-
-
-#### Setting up ACME for Docker-based deployments
-
-For Docker-based deployments, the simplest way to provision an SSL
-certificate is to use our Caddy service example in docker-compose.yml.
-Caddy uses ACME to automatically provision SSL certificates as long as
-it's available on port 80/tcp and the DNS record for the server is valid.
-
-See the [Docker deployment guide](docker) for more info.
-
-
-
-
-### Open required firewall ports
-
-By default, Firezone requires ports `443/tcp` and `51820/udp` to be
-accessible for HTTPS and WireGuard traffic respectively.
-These ports can change based on what you've configured in the configuration file.
-See the
-[configuration file reference](../reference/configuration-file)
-for details.
-
-### Resource requirements
-
-We recommend **starting with 1 vCPU and 1 GB of RAM and scaling up** as the
-number of users and devices grows.
-
-For Omnibus-based deployments on servers with less than 1GB of memory, we
-recommend turning on swap to prevent the Linux kernel from killing
-Firezone processes unexpectedly. When this happens, it's often difficult to
-debug and results in strange, unpredictable failure modes.
-
-For the VPN tunnels themselves, Firezone uses in-kernel WireGuard, so its
-performance should be very good. 1 vCPU should be more than enough to saturate
-a 1 Gbps link.
-
-## Step 2: Deploy
-
-You have two options for deploying Firezone:
-
-1. [Docker](docker) (recommended)
-1. [Omnibus](omnibus)
-
-Docker is the easiest way to install, manage, and upgrade Firezone and is the
-preferred method of deployment.
-
-:::warning
-Chef Infra Client, the configuration system Chef Omnibus relies on, has been
-[scheduled for End-of-Life in 2024](https://docs.chef.io/versions/). As such,
-support for Omnibus-based deployments will be removed starting with Firezone 0.8.
-To transition to Docker from Omnibus today, follow our [migration guide
-](../administer/migrate).
-:::
diff --git a/www/docs/deploy/advanced/README.mdx b/www/docs/deploy/advanced/README.mdx
deleted file mode 100644
index fad3678d9..000000000
--- a/www/docs/deploy/advanced/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Advanced
-sidebar_position: 8
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/deploy/advanced/build-from-source.mdx b/www/docs/deploy/advanced/build-from-source.mdx
deleted file mode 100644
index be6b789d4..000000000
--- a/www/docs/deploy/advanced/build-from-source.mdx
+++ /dev/null
@@ -1,91 +0,0 @@
----
-title: Build From Source
-sidebar_position: 1
----
-
-Building from source allows you to bring Firezone to unsupported platforms.
-
-:::warning
-You're entering unsupported territory. This is not for the faint of heart and
-will require being able to figure out snags you may hit on your own.
-
-If you're very comfortable with your environment of choice, then read on to
-learn how to build Firezone from source.
-:::
-
-:::info
-You will need to setup your own service management for Firezone (eg. `runit`,
-`systemd`, shell scripts). You will also need to install and configure your
-own database (eg. `postgres`) and reverse proxy (eg. `caddy`, `nginx`).
-
-Info about database configuration is [here](../external-database/#configure-firezone-to-connect),
-and info about configuring a reverse proxy is [here](../reverse-proxy/#proxy-requirements).
-:::
-
-# Prerequisites
-
-:::info
-Check the `.tool-versions` file [here](https://github.com/firezone/firezone/blob/master/.tool-versions)
-for the versions we use for Erlang, Elixir, and Node. If your system supports it,
-you can install these using [asdf-vm](https://asdf-vm.com/guide/getting-started.html)
-using a similar `.tool-versions` of your own to match versions. Your system's package
-manager may have them as well.
-:::
-
-**These must be available in the user's path that runs Firezone.**
-
-- [Erlang/OTP](https://www.erlang.org)
-- [Elixir](https://elixir-lang.org)
-- [NodeJS](https://nodejs.org)
-
-# Steps
-
-From your terminal, run these steps to build Firezone:
-
-```bash
-git clone https://github.com/firezone/firezone
-cd firezone
-mix local.rebar --force
-mix local.hex --force
-MIX_ENV=prod mix deps.get
-MIX_ENV=prod mix release
-```
-
-After the release build finishes, you should have a shiny new Firezone release artifact in
-`/_build/dev/rel/firezone`. In the `bin` folder, the `firezone` binary
-can be used to start up Firezone. If you run it without any arguments you should see
-a list of available commands like this:
-
-```bash
-Usage: firezone COMMAND [ARGS]
-
-The known commands are:
-
- start Starts the system
- start_iex Starts the system with IEx attached
- daemon Starts the system as a daemon
- daemon_iex Starts the system as a daemon with IEx attached
- eval "EXPR" Executes the given expression on a new, non-booted system
- rpc "EXPR" Executes the given expression remotely on the running system
- remote Connects to the running system via a remote shell
- restart Restarts the running system via a remote command
- stop Stops the running system via a remote command
- pid Prints the operating system PID of the running system via a remote command
- version Prints the release name and version to be booted
-```
-
-Most deployment-related configuration is handled with environment variables.
-You'll probably want to at least set variables related to your reverse proxy
-and database. See the [ENV var reference](/docs/reference/env-vars/) for an exhaustive list.
-
-Now all you need are the database and reverse proxy that you've previously set up.
-Once that's done, you can use `firezone start` to start Firezone and run
-`create-or-reset-admin` (in the same `bin` dir) to create the admin user and use
-it to log into Firezone from a web browser to start setting up your brand new
-custom instance that you built by hand with a little bit of elbow grease :)
-
-:::info
-As mentioned at the top, it's recommended to use some sort of service management
-to start and stop Firezone easily without having to manually do it using the
-`firezone` binary directly. But the choice is yours, since you're in control!
-:::
diff --git a/www/docs/deploy/advanced/external-database.mdx b/www/docs/deploy/advanced/external-database.mdx
deleted file mode 100644
index 867fddcb4..000000000
--- a/www/docs/deploy/advanced/external-database.mdx
+++ /dev/null
@@ -1,58 +0,0 @@
----
-title: Custom External Database
-sidebar_position: 2
----
-
-Firezone uses [Postgresql DB](https://postgresql.org) as its primary data store.
-
-## Compatibility
-
-Firezone should work fine on Postgres versions 12 and above, but we recommend
-using the latest stable version whenever possible. If you find an issue with
-your particular version of Postgres, [please open a GitHub issue
-](https://github.com/firezone/firezone/issues).
-
-In general, Firezone should also work fine using external Postgres-based
-database services like Amazon RDS. See the [configuration
-](#configure-firezone-to-connect) section below for more information configuring
-Firezone with an external DB.
-
-:::warning
-Configuring Firezone to use an external database can be complicated and
-error-prone. We recommend using the bundled Postgres for Omnibus-based
-deployments or the official Postgres Docker image for Docker-based deployments
-if possible.
-:::
-
-## Configure Firezone to Connect
-
-
-
-
-The Firezone Docker image uses the following environment
-variables to connect to the DB (fields in bold required):
-
-| Name | Description | Format | Default |
-| ----------------------------- | --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | --------------------- | ------------------------------------ |
-| **`DATABASE_ENCRYPTION_KEY`** | The base64-encoded symmetric encryption key used to encrypt and decrypt sensitive fields. | base64-encoded String | None -- must be generated on install |
-| `DATABASE_HOST` | Database host | IP or hostname | `postgres` |
-| `DATABASE_PORT` | Database port | Integer | `5432` |
-| `DATABASE_NAME` | Name of database | String | `firezone` |
-| `DATABASE_USER` | User | String | `postgres` |
-| `DATABASE_PASSWORD` | Password | String | `postgres` |
-| `DATABASE_POOL` | Size of the Firezone connection pool | Integer | `10` |
-| `DATABASE_SSL` | Whether to connect to the database over SSL | Boolean | `false` |
-| `DATABASE_SSL_OPTS` | Map of options to send to the `:ssl_opts` option when connecting over SSL. See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options) | JSON-encoded String | `{}` |
-| `DATABASE_PARAMETERS` | Map of parameters to send to the `:parameters` option when connecting to the database. See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options). | JSON-encoded String | `{}` |
-
-For more information, see the [environment variable reference
-](/docs/reference/env-vars/).
-
-:::note
-The official `postgres` docker image can be configured by setting
-environment variables for the container. See the Postgres image
-[documentation](https://hub.docker.com/_/postgres) for more details.
-:::
-
-
-
diff --git a/www/docs/deploy/advanced/reverse-proxy.mdx b/www/docs/deploy/advanced/reverse-proxy.mdx
deleted file mode 100644
index 761a10d68..000000000
--- a/www/docs/deploy/advanced/reverse-proxy.mdx
+++ /dev/null
@@ -1,105 +0,0 @@
----
-title: Custom Reverse Proxy
-sidebar_position: 3
----
-
-:::warning
-Using a custom reverse proxy is an advanced configuration. The default bundled
-Nginx proxy (Omnibus-based deployments) and Caddy (Docker-based deployments) is
-suitable for the vast majority of use cases and is recommended for most users.
-There are important security risks if the reverse proxy is not set up correctly.
-:::
-
-## Introduction
-
-Firezone comes with bundled [Nginx](https://www.nginx.com/) (Omnibus-based
-deployments) or uses Caddy (Docker-based deployments) by default. However, in
-some cases you might want to deploy your own server such as when using
-your own load balancer.
-
-## Prerequisites
-
-Below you will find the requirements in order to setup Firezone with a custom
-reverse proxy.
-
-### Firezone configuration requirements
-
-- Disable the bundled Nginx by setting `default['firezone']['nginx']['enabled']`
- to `false` in the config file.
-- If you have any immediate proxies between your primary reverse proxy and the
- Firezone web app, add their IPs to
- `default['firezone']['phoenix']['external_trusted_proxies']`. Because of the
- way the [X-Forwarded-For header works](https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Forwarded-For),
- this is needed to parse the actual client's IP address to prevent
- IP spoofing.
-
-:::note
-The `external_trusted_proxies` list automatically implicitly includes the
-following private CIDR ranges, even if they're not specified in the
-configuration file:
-
-- `127.0.0.0/8`
-- `10.0.0.0/8`
-- `172.16.0.0/12`
-- `192.168.0.0/16`
-- `::1/128`
-- `fc00::/7`
-
-This means any web requests originating from these IPs are automatically ignored
-from the `X-Forwarded-For` headers. If you're accessing Firezone from any IPs in
-this range (as seen by the Firezone web app), be sure to add them to the
-`default['firezone']['phoenix']['clients']` configuration option instead.
-:::
-
-Read more about the configuration options
-[here](/docs/reference/configuration-file/).
-
-### Proxy requirements
-
-- All your proxies need to configure the `X-Forwarded-For` header as explained
- [here](https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Forwarded-For)
-- Your proxy should also set the `X-Forwarded-Proto` to `https`.
-- Your proxy (or another downstream proxy) **must** terminate SSL since we
- enforce [secure cookies](https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies#restrict_access_to_cookies).
-- Firezone requires the use of WebSockets to establish realtime connections. We
- recommend following your proxy's specific documentation for supporting
- WebSockets as each proxy varies. In general, your proxy needs to be able to
- proxy HTTP 1.1 connections, and the Firezone web app expects the following
- headers to be set:
- - `Connection: upgrade`
- - `Upgrade: websocket`
-
-## Security considerations
-
-In addition to the headers above, we recommend adding the following headers for
-security purposes:
-
-- `X-XSS-Protection: 1; mode=block`
-- `X-Content-Type-Options nosniff`
-- `Referrer-Policy no-referrer-when-downgrade`
-- `Content-Security-Policy: default-src 'self' ws: wss: http: https: data: blob:
-'unsafe-inline'; frame-ancestors 'self';`
-- `Permissions-Policy: interest-cohort=()`
-
-Since the upstream Firezone web app expects plain HTTP traffic, any requests the
-proxy forwards is sent over HTTP and thus is **not encrypted**. In most cases,
-the reverse proxy is installed in a trusted network, and this is not an issue.
-But the connection between your trusted proxy and the Firezone web app spans
-an untrusted network (such as the Internet), you may want to leave the bundled
-`nginx` proxy enabled for SSL termination, and set up your custom
-reverse proxy to proxy to that instead.
-
-## Example configurations
-
-- [Apache](/docs/reference/reverse-proxy-templates/apache/)
-- [Traefik](/docs/reference/reverse-proxy-templates/traefik/)
-- [HAProxy](/docs/reference/reverse-proxy-templates/haproxy/)
-
-These configurations are written to be as simple as possible. They're designed
-to function as a simple template which you can customize further to suit your
-needs.
-
-If you have a working configuration for a different reverse proxy or a different
-version of an existing one we appreciate any
-[contribution](https://github.com/firezone/firezone/) to expand the examples for
-the community.
diff --git a/www/docs/deploy/configure.mdx b/www/docs/deploy/configure.mdx
deleted file mode 100644
index 1788ebd35..000000000
--- a/www/docs/deploy/configure.mdx
+++ /dev/null
@@ -1,45 +0,0 @@
----
-title: Configure
-sidebar_position: 5
----
-
-# Configure Firezone
-
-There are two types of configuration in Firezone:
-
-- [Runtime configuration](#runtime-configuration): Application configuration
- related to day-to-day operation of Firezone.
-- [Deployment configuration](#deployment-configuration): Deployment or
- infrastructure-related configuration relevant to running Firezone on-prem.
-
-## Runtime configuration
-
-Most day-to-day configuration of Firezone can be done via the Web UI or
-[REST API](/docs/reference/rest-api/configurations).
-This type of configuration can be expected to be changed **with no downtime**
-in a production deployment.
-
-We're actively working to move more configuration variables to
-this type of configuration, so expect more ENV vars to transition to runtime
-configuration in the future.
-
-## Deployment configuration
-
-Deployment-related and infrastructure configuration require restarting Firezone
-services after change.
-
-
-
-
-Docker-based deployments are configured through environment
-variables passed to the `firezone` container. These can be
-specified either in a `.env` file in the current directory,
-the `docker-compose.yml` file, or passed to the `docker run`
-call directly. See the [env var reference](../../reference/env-vars)
-for a complete listing.
-
-See [Docker's documentation
-](https://docs.docker.com/compose/envvars-precedence/) for more information.
-
-
-
diff --git a/www/docs/deploy/docker/README.mdx b/www/docs/deploy/docker/README.mdx
deleted file mode 100644
index 322c76f2f..000000000
--- a/www/docs/deploy/docker/README.mdx
+++ /dev/null
@@ -1,180 +0,0 @@
----
-title: Docker
-sidebar_position: 2
-description: Install Firezone via Docker to manage secure remote
- access to private networks and resources.
----
-
-# Install Firezone with Docker
-
-As of 0.6.0, Docker is now the **preferred method** for
-deploying Firezone. Docker offers a number of benefits over the old
-[Omnibus method](../omnibus):
-
-- **Simpler, more robust upgrades**: In most cases, simply pull the latest `firezone/firezone`
- image and restart the container.
-- **Simpler configuration**: Most day-to-day configuration of Firezone can now
- be done in the web UI instead of the `/etc/firezone/firezone.rb` configuration
- file. All other configuration variables can be specified as ENV vars to the
- Firezone container.
-- **Smaller footprint**: The Firezone image weighs in at a couple dozen
- megabytes versus hundreds of megabytes for the Omnibus package.
-- **Portability**: Firezone now runs on any platform that supports Docker.
-- **Security**: Containerization providers better security isolation than
- simply running as an unprivileged local user.
-
-## Step 1: Prerequisites
-
-- Ensure you're on a [supported platform](supported-platforms) with [
- docker-compose](https://docs.docker.com/compose/install/) **version 2
- or higher** installed.
-- Ensure port forwarding is enabled on your firewall.
- The default Firezone configuration requires the following ports to be open:
- - `80/tcp` (optional): For automatically issuing SSL certificates.
- - `443/tcp`: To access the web UI.
- - `51820/udp`: VPN traffic listen port.
-
-:::caution
-Before deploying Firezone in **production**, you'll need a valid DNS record
-pointing to this instance. See [Prepare to Deploy](../#prepare-to-deploy)
-if you haven't done this already.
-:::
-
-## Step 2: Install server
-
-After prerequisites are satisfied, you're ready to install the Firezone Server.
-
-### Option 1: Automatic install
-
-The easiest way to deploy Firezone with Docker is the automatic install script:
-
-
-
-This will ask you a few questions regarding initial configuration, then proceed
-to download a sample docker-compose.yml file, configure it with your responses,
-and then print instructions for accessing the Web UI.
-
-Firezone files will be installed in `$HOME/.firezone` by default.
-
-### Option 2: Manual install
-
-If the automatic install fails, or you'd just like more control over the
-installation process, follow the steps below to install manually.
-
-1. Download the docker compose template to a local working directory:
- **For Linux**:
-
-```
-curl -fsSL https://raw.githubusercontent.com/firezone/firezone/master/docker-compose.prod.yml -o docker-compose.yml
-```
-
-**For macOS, Windows (non-production only)**:
-
-```
-curl -fsSL https://raw.githubusercontent.com/firezone/firezone/master/docker-compose.desktop.yml -o docker-compose.yml
-```
-
-1. Generate required secrets:
-
-```
-docker run --rm firezone/firezone bin/gen-env > .env
-```
-
-1. At a minimum, change the `DEFAULT_ADMIN_EMAIL` and `EXTERNAL_URL` variables.
- Optionally modify other secrets as needed.
-1. Migrate the database:
-
-```
-docker compose run --rm firezone bin/migrate
-```
-
-1. Create the first admin:
-
-```
-docker compose run --rm firezone bin/create-or-reset-admin
-```
-
-1. Bring the services up: `docker compose up -d`
-
-You should now be able to access the Firezone web portal at the `EXTERNAL_URL`
-variable you defined above.
-
-## Step 3 (optional): Enable on boot
-
-If you'd like Firezone to start automatically on boot, first ensure Docker is enabled at startup:
-
-```
-sudo systemctl enable docker
-```
-
-Then, make sure your Firezone services have the `restart: always` or `restart: unless-stopped` option
-specified in the `docker-compose.yml` file. This is the default used in the docker-compose.prod.yml
-production template file.
-
-## Step 4 (optional): Enable IPv6
-
-By default, Firezone ships with IPv6 connectivity enabled inside the tunnel but not routable
-to the public internet. To enable IPv6 support in Docker-deployed Firezone, follow the steps below.
-
-1. Enable IPv6 support within Docker by adding the following to `/etc/docker/daemon.json`:
-
-```json
-{
- "ipv6": true,
- "ip6tables": true,
- "experimental": true,
- "fixed-cidr-v6": "2001:db8:1::/64"
-}
-```
-
-This enables IPv6 NAT and configures IPv6 forwarding for Docker containers.
-
-1. Enable router advertisements on boot for your default egress interface:
-
-```
-egress=`ip route show default 0.0.0.0/0 | grep -oP '(?<=dev ).*' | cut -f1 -d' ' | tr -d '\n'`
-sudo bash -c "echo net.ipv6.conf.${egress}.accept_ra=2 >> /etc/sysctl.conf"
-```
-
-1. Reboot
-
-You should now be able to ping google from within a docker container:
-
-```
-docker run --rm -t busybox ping6 -c 4 google.com
-```
-
-You shouldn't need to manually add any `iptables` rules to enable IPv6 SNAT/masquerading for
-tunneled traffic; Firezone handles this for you by default on start.
-
-## Step 5: Install client apps
-
-:::note
-Firezone currently uses WireGuard's
-[open-source client apps](https://www.wireguard.com/install/).
-:::
-
-Once successfully deployed, users and devices can be added to
-connect to the VPN server:
-
-- [Add Users](../../user-guides/add-users):
- Add users to grant them access to your network.
-- [Client Instructions](../../user-guides/client-instructions):
- Instructions to establish a VPN session.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
-
-## Post Setup
-
-Congrats! You have completed the setup, but there's a lot more you can do with
-Firezone:
-
-- [Integrate your identity provider](../../authenticate/)
- for authenticating clients
-- Using Firezone as a NAT gateway to
- [establish a static IP for your team](../../user-guides/use-cases/nat-gateway)
-- Create tunnels between multiple peers with
- [reverse tunnels](../../user-guides/use-cases/reverse-tunnel)
-- Only route certain traffic through Firezone with
- [split tunneling](../../user-guides/use-cases/split-tunnel)
diff --git a/www/docs/deploy/docker/supported-platforms.mdx b/www/docs/deploy/docker/supported-platforms.mdx
deleted file mode 100644
index 5bcd05049..000000000
--- a/www/docs/deploy/docker/supported-platforms.mdx
+++ /dev/null
@@ -1,33 +0,0 @@
----
-title: Supported Platforms
-sidebar_position: 1
----
-
-Firezone currently supports the following platforms for Docker-based
-deployments.
-
-| OS | Architecture(s) | Runtime | Status | Notes |
-| --- | --- | --- | --- | --- |
-| Linux | `amd64` `arm64` | Docker Server | **Fully-supported** | `wireguard` kernel module needed for kernels < `5.6`. |
-| Linux | `amd64` `arm64` | Docker Desktop | Works, but unsupported. | Not recommended for production deployments. See [caveats](#docker-desktop-caveats). |
-| macOS | `amd64` `arm64` | Docker Desktop | Works. but unsupported. | Not recommended for production deployments. See [caveats](#non-linux-platform-caveats). |
-| Windows | `amd64` `arm64` | Docker Desktop | **Untested** | Not recommended for production deployments. See [caveats](#non-linux-platform-caveats). |
-
-## Docker Desktop caveats
-
-Docker Desktop [rewrites the source address
-](https://www.docker.com/blog/how-docker-desktop-networking-works-under-the-hood/)
-for packets flowing out of container networks under some conditions. This can
-cause routing loops and other hard to debug connectivity issues with Firezone.
-We recommend **only** using Docker Server for Linux for production deployments.
-
-## Non-Linux platform caveats
-
-Only Docker for Linux supports the host networking mode, so macOS and Windows
-platforms will be able unable to properly attribute client source address
-for HTTP requests. This means any IP-based throttling or logging in your
-chosen proxy (`caddy` by default) will be ineffective, since the source
-IP will always be the Docker-side host IP (typically `172.X.0.1`).
-
-Egress rules operate on the tunneled client IP address and aren't affected
-by this limitation.
diff --git a/www/docs/deploy/security-considerations.mdx b/www/docs/deploy/security-considerations.mdx
deleted file mode 100644
index 60d974a32..000000000
--- a/www/docs/deploy/security-considerations.mdx
+++ /dev/null
@@ -1,57 +0,0 @@
----
-title: Security Considerations
-sidebar_position: 6
----
-
-# Security considerations
-
-**Disclaimer**: Firezone is still beta software. The codebase has not yet
-received a formal security audit. For highly sensitive and mission-critical
-production deployments, we recommend disabling local authentication as
-detailed [below](#production-deployments).
-
-## List of services and ports
-
-Shown below is a table of default ports used by Firezone services.
-
-
-
-
-| Service | Port | Listen address | Description |
-| ---------- | ----------- | -------------- | ----------------------------------------------------------------------------- |
-| Caddy | `443/tcp` | `all` | Public HTTPS port for administering Firezone and facilitating authentication. |
-| Caddy | `80/tcp` | `all` | Public HTTP port used for ACME. Disabled when ACME is disabled. |
-| WireGuard | `51820/udp` | `all` | Public WireGuard port used for VPN sessions. |
-| Postgresql | `5432/tcp` | `-` | Containerized port used for bundled Postgresql server. |
-| Phoenix | `13000/tcp` | `-` | Containerized port used by upstream elixir app server. |
-
-
-
-
-| Service | Port | Listen address | Description |
-| ---------- | ----------- | -------------- | ----------------------------------------------------------------------------- |
-| Nginx | `443/tcp` | `all` | Public HTTPS port for administering Firezone and facilitating authentication. |
-| Nginx | `80/tcp` | `all` | Public HTTP port used for ACME. Disabled when ACME is disabled. |
-| WireGuard | `51820/udp` | `all` | Public WireGuard port used for VPN sessions. |
-| Postgresql | `15432/tcp` | `127.0.0.1` | Local-only port used for bundled Postgresql server. |
-| Phoenix | `13000/tcp` | `127.0.0.1` | Local-only port used by upstream elixir app server. |
-
-
-
-
-## Production deployments
-
-For production deployments of Firezone, we recommend you disable local authentication
-altogether by setting `default['firezone']['authentication']['local']['enabled'] = false`
-(Omnibus-based deployments) or `LOCAL_AUTH_ENABLED=false` (Docker-based deployments).
-Local authentication can also be disabled on the `/settings/security` page.
-
-:::caution
-Ensure you've set up a working [OIDC](/docs/authenticate/oidc/) or [SAML](/docs/authenticate/saml/)-based
-authentication provider before disabling the local authentication method.
-:::
-
-## Reporting security issues
-
-To report any security-related bugs, see [our security bug reporting policy
-](https://github.com/firezone/firezone/blob/master/SECURITY.md).
diff --git a/www/docs/reference/README.mdx b/www/docs/reference/README.mdx
deleted file mode 100644
index 170fb3136..000000000
--- a/www/docs/reference/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Reference
-sidebar_position: 6
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/reference/_audit-logs.mdx b/www/docs/reference/_audit-logs.mdx
deleted file mode 100644
index 0c5785ab2..000000000
--- a/www/docs/reference/_audit-logs.mdx
+++ /dev/null
@@ -1,17 +0,0 @@
----
-title: Audit Logs
-sidebar_position: 2
----
-
-# Audit logs
-
-Firezone maintains two types of logs tied to user identity: configuration logs
-and network activity logs.
-
-Configuration logs track events related to the configuration of Firezone
-itself, either by admins or users. Network activity logs track connections to
-protected resources made by users of your network.
-
-Logged events are recorded as JSON objects and stored in the database. These
-are accessible via a REST API or the Firezone portal, and exportable to CSV
-format.
diff --git a/www/docs/reference/configuration-file.mdx b/www/docs/reference/configuration-file.mdx
deleted file mode 100644
index 9f8c9ec8f..000000000
--- a/www/docs/reference/configuration-file.mdx
+++ /dev/null
@@ -1,186 +0,0 @@
----
-title: Configuration File
-sidebar_position: 2
----
-
-# Omnibus configuration options
-
-:::warning
-This reference is written for Omnibus-based deployments of Firezone. For
-Docker-based deployments visit the [Environment Variables](../env-vars) page.
-:::
-
-To configure Omnibus-based deployments of Firezone:
-
-1. Edit `/etc/firezone/firezone.rb` with your changes.
-1. Run `sudo firezone-ctl reconfigure` to process the changes and restart affected services.
-
-Read more about configuring Firezone in the [configure guide](/docs/deploy/configure).
-
-## Configuration file reference
-
-Shown below is a complete listing of the configuration options available in
-`/etc/firezone/firezone.rb`.
-
-
-
-
-| Option | Description | Default Value |
-| -------------------------------------------------------------------- | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ |
-| `default['firezone']['external_url']` | URL used to access the web portal of this Firezone instance. |
-
-
-would generate the following OIDC login URL:
-
-- `https://firezone.example.com/auth/oidc/google`
-
-This URL could then be distributed to end users for direct navigation to
-the identity provider's login portal for authentication to Firezone.
-
-## Enforce periodic re-authentication
-
-Periodic re-authentication can be enforced by changing the setting in
-`settings/security`. This can be used to ensure a user must sign in to Firezone
-periodically in order to maintain their VPN session.
-
-You can set the session length to a minimum of **1 hour** and maximum of **90 days**.
-Setting this to Never disables this setting, allowing VPN sessions indefinitely.
-This is the default.
-
-### Re-authentication
-
-To re-authenticate an expired VPN session, a user will need to turn off their
-VPN session and sign in to the Firezone portal (URL specified during
-[deployment](../deploy#prepare-to-deploy)).
-
-See detailed Client Instructions on how to re-authenticate your session
-[here](../user-guides/client-instructions).
-
-#### VPN connection status
-
-A user's connection status is shown on the Users page under the table column
-`VPN Connection`. The connection statuses are:
-
-- ENABLED - The connection is enabled.
-- DISABLED - The connection is disabled by an administrator or OIDC refresh failure.
-- EXPIRED - The connection is disabled due to authentication expiration or a user
- has not signed in for the first time.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
diff --git a/www/docs/authenticate/local-auth.mdx b/www/docs/authenticate/local-auth.mdx
deleted file mode 100644
index ce3c2c94e..000000000
--- a/www/docs/authenticate/local-auth.mdx
+++ /dev/null
@@ -1,30 +0,0 @@
----
-title: Local Authentication
-sidebar_position: 1
----
-
-# Local authentication (email & password)
-
-By default, Firezone will use local email / password for authenticating users to
-the Firezone portal. Administrators can add users and assign their passwords on
-the `/users` page. See [Add users](/docs/user-guides/add-users/) for more details.
-
-:::caution
-Although local authentication is quick and easy to get started with, you can
-limit attack surface by [disabling local authentication](#disabling-local-authentication)
-altogether. See our [OIDC](/docs/authenticate/oidc/) or [SAML](/docs/authenticate/saml/) guides
-for details. For production deployments it's usually a good idea to **disable
-local authentication** and enforce MFA through your identity provider.
-:::
-
-If you choose to keep Local authentication enabled, we recommend [enabling TOTP-based MFA
-](/docs/authenticate/multi-factor/) for any accounts that use the local authentication method.
-
-## Disabling local authentication
-
-Local authentication can be enabled or disabled from the `/settings/security` page
-or via the [REST API](/docs/reference/rest-api/configurations).
-If you've disabled local authentication and can no longer authenticate to the portal
-to re-enable it, see our [troubleshooting guide
-](/docs/administer/troubleshoot#re-enable-local-authentication-via-cli) for re-enabling
-local authentication from the CLI.
diff --git a/www/docs/authenticate/multi-factor.mdx b/www/docs/authenticate/multi-factor.mdx
deleted file mode 100644
index e206a48a7..000000000
--- a/www/docs/authenticate/multi-factor.mdx
+++ /dev/null
@@ -1,40 +0,0 @@
----
-title: Multi-Factor Authentication
-sidebar_position: 2
-description:
- Enforce multi-factor authentication with Firezone's WireGuard®-based
- secure access platform.
----
-
-# Multi-factor authentication (MFA)
-
-You have two options for activating MFA with Firezone:
-
-1. Enable a TOTP-based second factor for the local email/password
-authentication method.
-1. Configure Firezone to SSO via one of our [supported identity providers
-](../#integrate-an-sso-provider) and enable MFA through the identity provider.
-
-## MFA with Firezone
-
-Firezone currently supports using a time-based one time password
-(TOTP) as an additional factor. This is supported with the local authentication
-method only; for SSO authentication we recommend enabling your provider's MFA
-functionality [as described below](#mfa-with-identity-provider).
-
-Admins can visit `/settings/account/register_mfa` in the admin portal to
-generate a QR code to be scanned by your authenticator app.
-
-Unprivileged users can visit `/user_account/register_mfa` after logging into
-the user portal.
-
-## MFA with your identity provider
-
-Most identity providers support additional authentication factors in addition to
-email/password. Consult your provider's documentation to enforce an
-additional factor. We have included links to a few common providers below:
-
-* [Okta](https://help.okta.com/en-us/Content/Topics/Security/mfa/mfa-home.htm)
-* [Azure AD](https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-mfa-howitworks)
-* [Google](https://support.google.com/a/answer/175197)
-* [Onelogin](https://www.onelogin.com/getting-started/free-trial-plan/add-mfa)
diff --git a/www/docs/authenticate/oidc/README.mdx b/www/docs/authenticate/oidc/README.mdx
deleted file mode 100644
index 49771de7c..000000000
--- a/www/docs/authenticate/oidc/README.mdx
+++ /dev/null
@@ -1,66 +0,0 @@
----
-title: OpenID Connect
-sidebar_position: 10
-description: Setup single sign-on with your identity provider. Integrate
- providers like Okta, Google, Azure, and JumpCloud using Firezone's
- OpenID Connect (OIDC) connector.
----
-
-# Integrate your identity provider using OIDC
-
-Firezone supports Single Sign-On (SSO) via OpenID Connect (OIDC).
-
-## Supported identity providers
-
-In general, most identity providers that offer OIDC support work with Firezone. Some providers
-that only implement the OIDC partially or use uncommon configurations may have
-issues, however. If your identity provider falls into this category, [contact us
-](/contact/support) about a custom integration.
-
-The following OIDC providers are known to work well with Firezone:
-
-| Provider | Support Status | Notes |
-| ------------------------------------- | ------------------------------ | ------------------------------------------------------------------------------------------------------------------------------------------------------ |
-| [Azure Active Directory](azuread) | **Fully tested and supported** | Ensure the [`email` claim](https://learn.microsoft.com/en-us/azure/active-directory/develop/active-directory-optional-claims) is present in the token. |
-| [Okta](okta) | **Fully tested and supported** | |
-| [Onelogin](onelogin) | **Fully tested and supported** | |
-| [Keycloak](https://www.keycloak.org/) | **Fully tested and supported** | |
-| [Auth0](auth0) | **Fully tested and supported** | Auth0 does not provide an `end_session_uri` in its OIDC discovery document. Signing out of Auth0 from Firezone is not supported. |
-| [Google Workspace](google) | **Fully tested and supported** | Google does not provide an `end_session_uri` in its OIDC discovery document. Signing out of Google Workspace from Firezone is not supported. |
-| [Zitadel](zitadel) | Untested but known to work | |
-| [Authentik](https://goauthentik.io/) | Untested but known to work | |
-
-## General setup guide
-
-If you're using an OIDC provider not listed above, the following OIDC attributes
-are required for setting up an OIDC provider in Firezone:
-
-1. `discovery_document_uri`: The
- [OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
- which returns a JSON document used to construct subsequent requests to this
- OIDC provider. Some providers refer to this as the "well-known URL".
-1. `client_id`: The client ID of the application.
-1. `client_secret`: The client secret of the application.
-1. `redirect_uri`: Instructs OIDC provider where to redirect after authentication.
- This should be your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
- (e.g. `https://firezone.example.com/auth/oidc/google/callback/`).
-1. `response_type`: Set to `code`.
-1. `scope`: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
- to obtain from your OIDC provider. At a minimum, Firezone requires the `openid`
- and `email` scopes.
-1. `label`: The button label text displayed on the Firezone portal login page.
-
-### PKCE
-
-Firezone supports Proof Key for Code Exchange (PKCE) for increased login security.
-We recommend you enable PKCE in your IdP's settings whenever available. [Read more
-about PKCE here](https://oauth.net/2/pkce/).
-
-### OIDC logout URI
-
-The OpenID Connect standard [defines a mechanism](https://openid.net/specs/openid-connect-rpinitiated-1_0.html)
-for a Relying Party (RP) to request that an OpenID Provider log out the End-User.
-
-Unfortunately, not all IdPs support this (e.g. Google, Auth0). For the providers
-that do support this mechanism, Firezone automatically detects the `end_session_uri`
-found in the provider's discovery document and uses that to log out the End-User.
diff --git a/www/docs/authenticate/oidc/auth0.mdx b/www/docs/authenticate/oidc/auth0.mdx
deleted file mode 100644
index 7f77b990a..000000000
--- a/www/docs/authenticate/oidc/auth0.mdx
+++ /dev/null
@@ -1,69 +0,0 @@
----
-title: Auth0
-sidebar_position: 1
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Auth0
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Auth0 (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Auth0
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `auth0`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Auth0`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this OIDC
-provider.
-
-## Step 1: Obtain OIDC configuration parameters
-
-In the Auth0 dashboard, create an application.
-Select **Regular Web Application** as the application type.
-
-
-
-Next, visit the settings tab on the application details page. Take note and
-modify the following parameters:
-
-1. **Name**: `Firezone`
-1. **Domain**: The domain will be used to construct
-the url to retrieve the OIDC discovery document - `https:///.well-known/openid-configuration`
-1. **Icon**:
-[Firezone icon](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-(save link as).
-1. Set **Allowed Callback URLs** to `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/auth0/callback/`).
-
-
-
-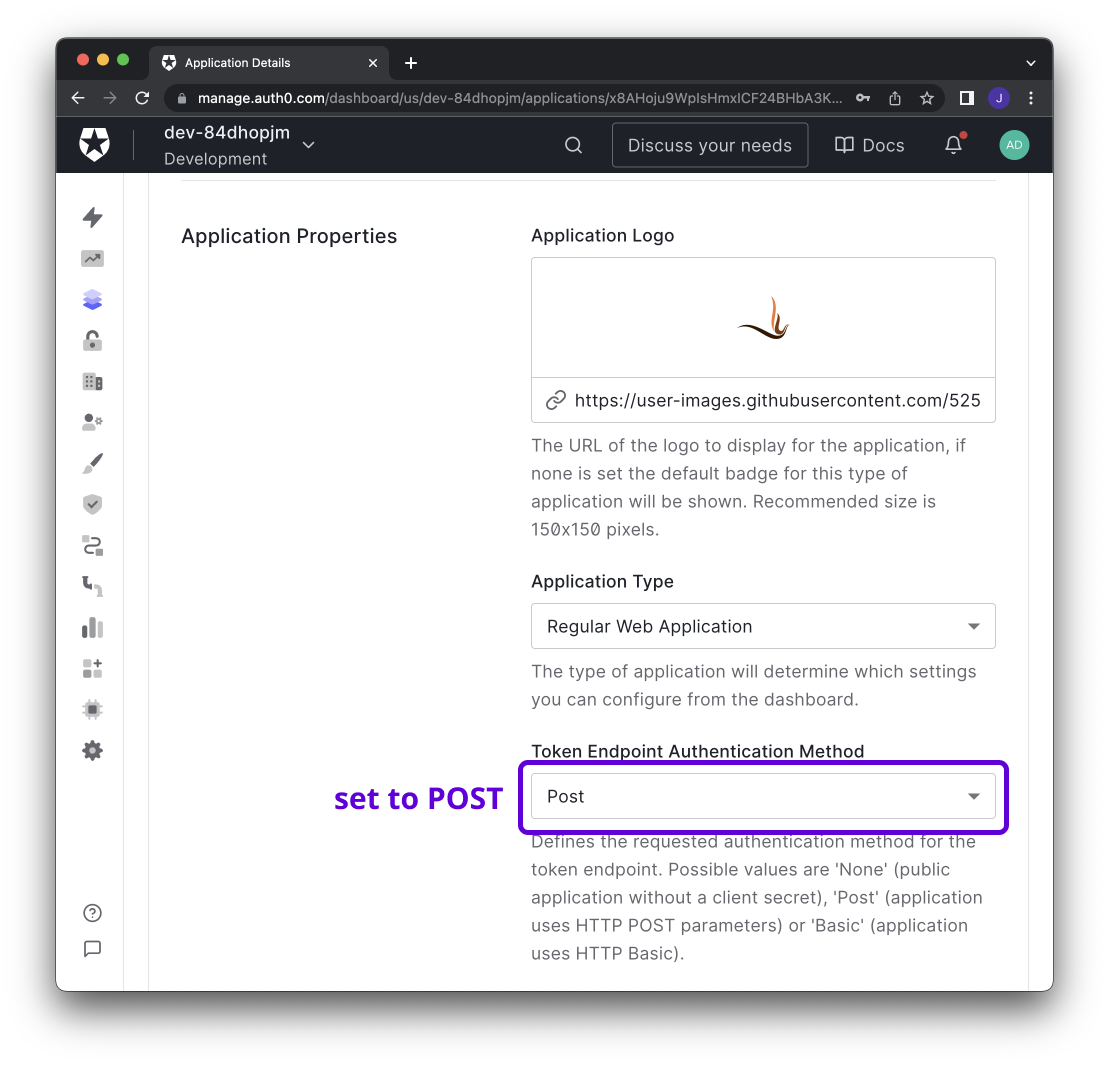
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Auth0` button on the sign in page.
-
-## Step 3 (optional): Restrict access to specific users
-
-Auth0 supports setting access policies to control which users
-can access the Firezone application. See Auth0's
-[Documentation](https://auth0.com/docs/manage-users/user-accounts/manage-user-access-to-applications)
-for details.
diff --git a/www/docs/authenticate/oidc/azuread.mdx b/www/docs/authenticate/oidc/azuread.mdx
deleted file mode 100644
index a30457f6f..000000000
--- a/www/docs/authenticate/oidc/azuread.mdx
+++ /dev/null
@@ -1,82 +0,0 @@
----
-title: Azure Active Directory
-sidebar_position: 2
-description: Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Azure AD
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Azure Active Directory (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Azure Active Directory through the generic
-generic OIDC connector. This guide will walk you through how to obtain the following
-config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `azure`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Azure`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
- to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
- to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
- [OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
- which returns a JSON document used to construct subsequent requests to this
- OIDC provider.
-
-
-
-## Step 1: Obtain configuration parameters
-
-_This guide is adapted from the [Azure Active Directory documentation](https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/auth-oidc)._
-
-Navigate to the Azure Active Directory page on the Azure portal.
-Select the App registrations link under the Manage menu, click
-`New Registration`, and register after entering the following:
-
-1. **Name**: `Firezone`
-1. **Supported account types**: `(Default Directory only - Single tenant)`
-1. **Redirect URI**: This should be your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
- (e.g. `https://firezone.example.com/auth/oidc/azure/callback/`). **Make sure you include the trailing slash both
- when saving the provider in Firezone and in Azure AD (`redirect_uri` field on the screenshot below).**
-
-
-
-After registering, open the details view of the application and copy the
-`Application (client) ID`. **This will be the `client_id` value**. Next, open
-the endpoints menu to retrieve the `OpenID Connect metadata document`.
-**This will be the `discovery_document_uri` value**.
-
-
-
-Next, select the Certificates & secrets link under the Manage menu and
-create a new client secret. Copy the client secret - **this will be the
-`client_secret` value**.
-
-
-
-Lastly, select the API permissions link under the Manage menu,
-click `Add a permission`, and select `Microsoft Graph`. Add `email`, `openid`,
-`offline_access` and `profile` to the required permissions.
-
-
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Azure` button on the sign in page.
-
-## Step 3 (optional): Restrict access to specific users
-
-Azure AD allows admins to restrict OAuth application access to a subset of users
-within your organization. See Microsoft's
-[documentation](https://docs.microsoft.com/en-us/azure/active-directory/develop/howto-restrict-your-app-to-a-set-of-users)
-for more information on how to do this.
diff --git a/www/docs/authenticate/oidc/google.mdx b/www/docs/authenticate/oidc/google.mdx
deleted file mode 100644
index a27e2ee03..000000000
--- a/www/docs/authenticate/oidc/google.mdx
+++ /dev/null
@@ -1,92 +0,0 @@
----
-title: Google Workspace
-sidebar_position: 3
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Google Workspace
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Google Workspace (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Google Workspace and Cloud Identity
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `google`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Google`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-
-
-## Step 1: Configure OAuth consent screen
-
-If this is the first time you are creating a new OAuth client ID, you will
-be asked to configure a consent screen.
-
-**IMPORTANT**: Select `Internal` for user type. This ensures only accounts
-belonging to users in your Google Workspace Organization can create device configs.
-DO NOT select `External` unless you want to enable anyone with a valid Google Account
-to create device configs.
-
-
-
-On the App information screen:
-
-1. **App name**: `Firezone`
-1. **App logo**: [Firezone logo](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-(save link as).
-1. **Application home page**: the URL of your Firezone instance.
-1. **Authorized domains**: the top level domain of your Firezone instance.
-
-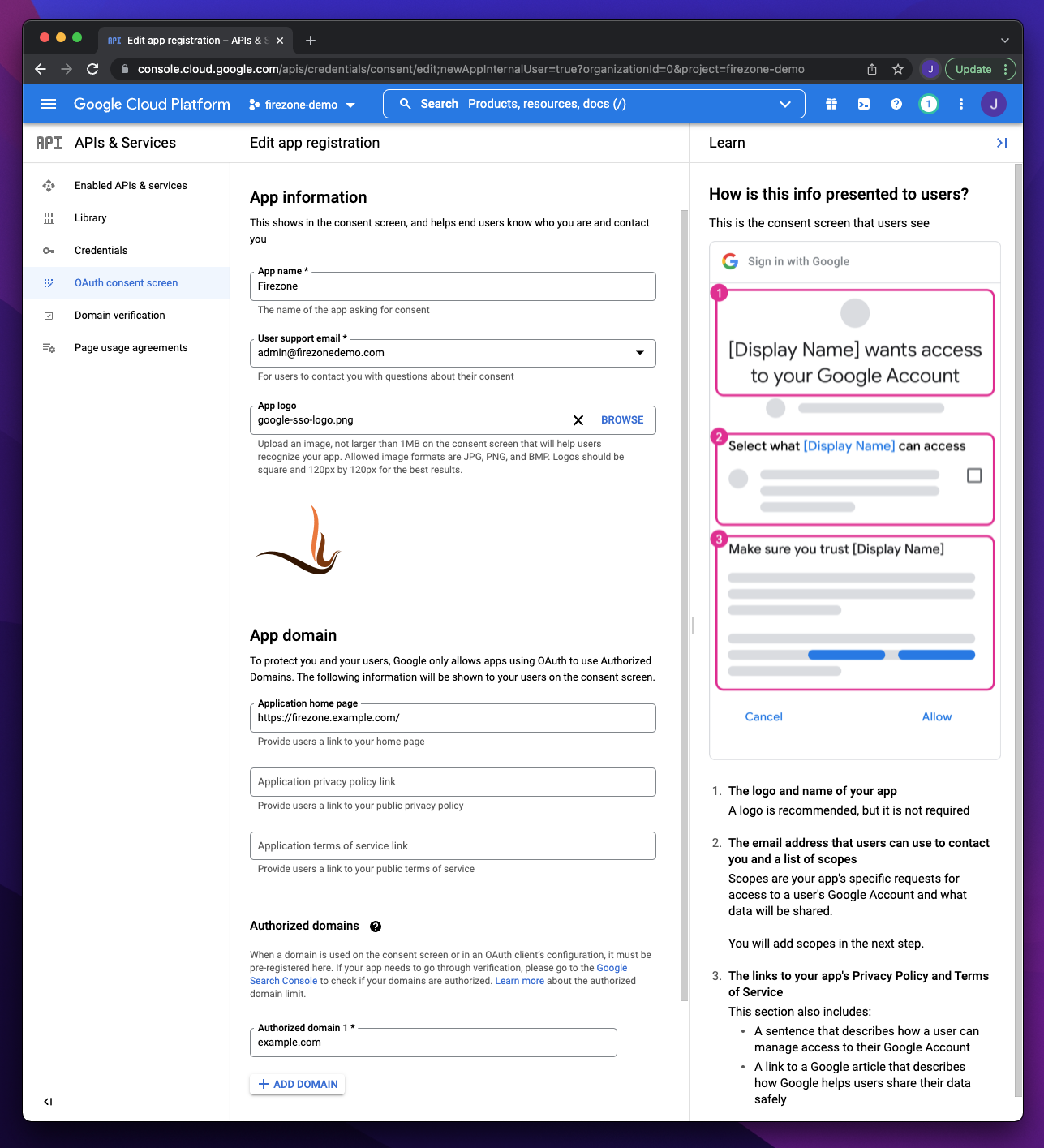
-
-On the next step add the following scopes:
-
-
-
-## Step 2: Create OAuth client
-
-_This section is based off Google's own documentation on
-[setting up OAuth 2.0](https://support.google.com/cloud/answer/6158849)._
-
-Visit the Google Cloud Console
-[Credentials page](https://console.cloud.google.com/apis/credentials)
-page, click `+ Create Credentials` and select `OAuth client ID`.
-
-
-
-On the OAuth client ID creation screen:
-
-1. Set `Application Type` to `Web application`
-1. Add your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/google/callback/`) as an entry to
-Authorized redirect URIs.
-
-
-
-After creating the OAuth client ID, you will be given a Client ID and Client Secret.
-These will be used together with the redirect URI in the next step.
-
-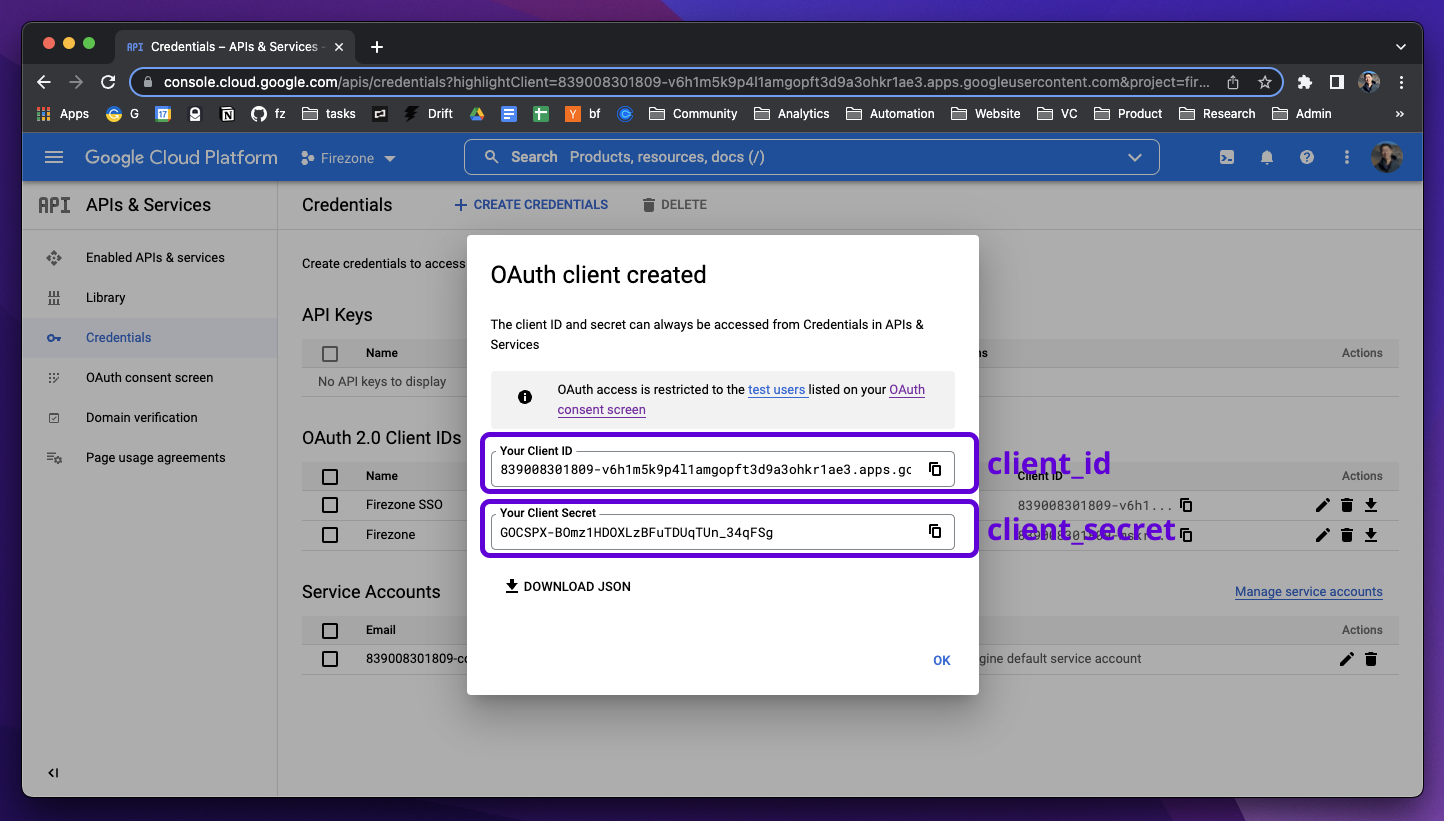
-
-## Step 3: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Google` button on the sign in page.
diff --git a/www/docs/authenticate/oidc/keycloak.mdx b/www/docs/authenticate/oidc/keycloak.mdx
deleted file mode 100644
index 529bfcc3a..000000000
--- a/www/docs/authenticate/oidc/keycloak.mdx
+++ /dev/null
@@ -1,80 +0,0 @@
----
-title: Keycloak
-sidebar_position: 4
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Keycloak
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Keycloak (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Keycloak
-through the generic OIDC provider. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `keycloak`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Keycloak`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-## Step 1: Obtain configuration parameters
-
-In the Keycloak Admin Console, make sure the realm you want to use with Firezone
-is selected.
-
-
-
-### Create Firezone OAuth client
-
-Create a new Client for Firezone by navigating to **Clients > Create Client** and
-configure the following:
-
-1. **Client type**: `OpenID Connect`
-1. **Client ID**: `firezone`
-1. **Name**: `Firezone`
-1. Click **Next**.
-
-
-
-1. Toggle **Client authentication** to `On` to generate the client secret.
-1. Click **Save**.
-
-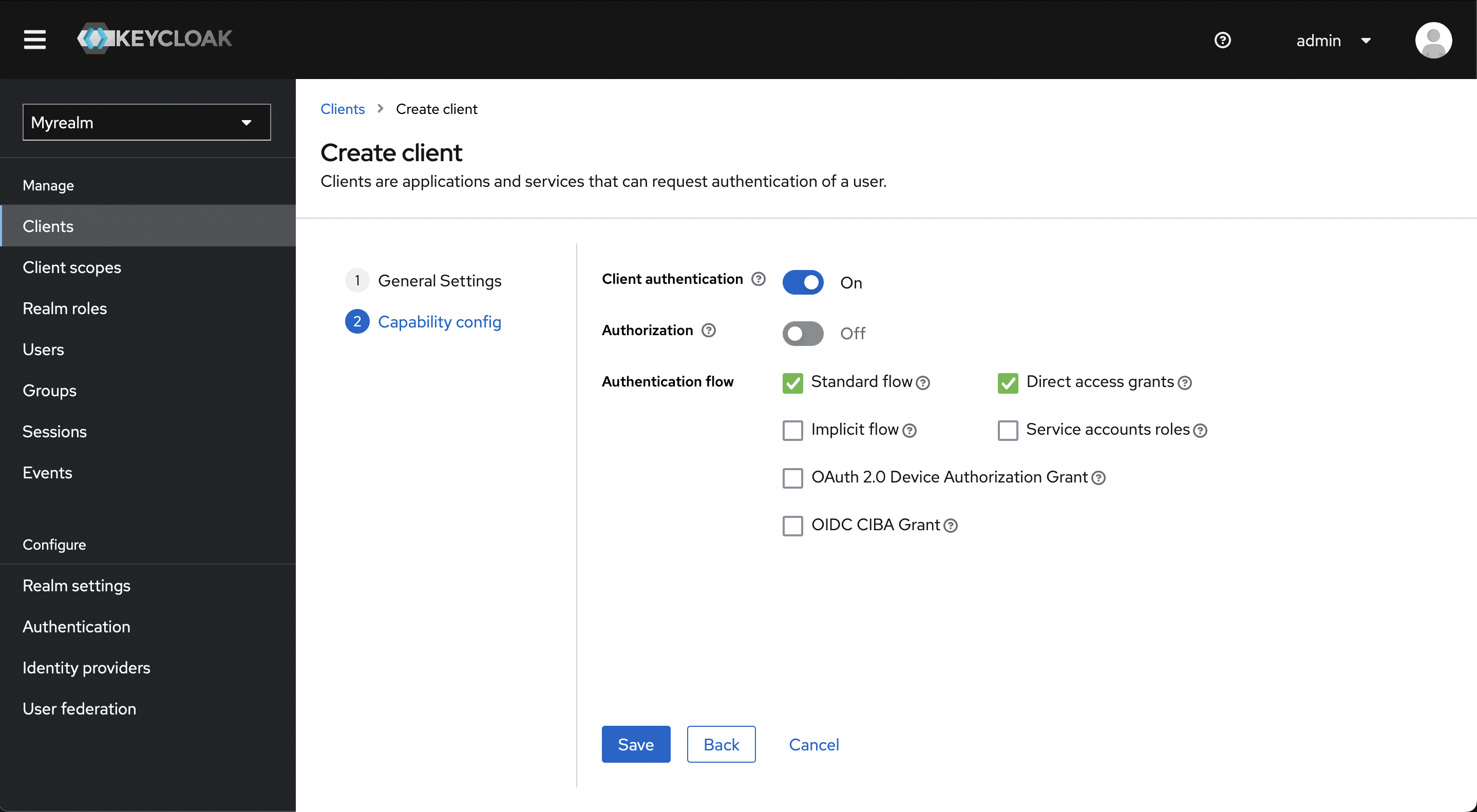
-
-Click **Access settings** to jump to that section and configure the valid redirect URI:
-
-1. **Valid Redirect URIs**: This should be your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/keycloak/callback/`).
-1. Click **Add valid redirect URIs**
-
-
-
-Click the **Credentials** tab and copy the client secret.
-
-
-
-Navigate to the **Realm Settings** page to get the **Discovery Document URI** by
-copying the **OpenID Endpoint Configuration** link at the bottom of the page.
-
-
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Keycloak` button on the sign in page.
diff --git a/www/docs/authenticate/oidc/okta.mdx b/www/docs/authenticate/oidc/okta.mdx
deleted file mode 100644
index 89a4da2e6..000000000
--- a/www/docs/authenticate/oidc/okta.mdx
+++ /dev/null
@@ -1,83 +0,0 @@
----
-title: Okta
-sidebar_position: 5
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Okta
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Okta (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Okta
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `okta`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Okta`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-
-
-## Step 1: Create Okta app integration
-
-_This section of the guide is based on
-[Okta's documentation](https://help.okta.com/en/prod/Content/Topics/Apps/Apps_App_Integration_Wizard_OIDC.htm)._
-
-In the Admin Console, go to **Applications > Applications** and click
-**Create App Integration**. Set **Sign-in method** to **OICD - OpenID Connect**
-and **Application type** to **Web application**.
-
-
-
-On the following screen, configure the following settings:
-
-1. **App Name**: `Firezone`
-1. **App logo**:
-[Firezone logo](https://user-images.githubusercontent.com/52545545/155907625-a4f6c8c2-3952-488d-b244-3c37400846cf.png)
-(save link as).
-1. **Proof Key for Code Exchange (PKCE)**: Check `Require PKCE as additional verification` if you're running Firezone
-0.6.8 or higher. [PKCE](https://oauth.net/2/pkce/) is recommended for increased security whenever possible.
-1. **Grant Type**: Check the **Refresh Token** box. This ensures Firezone syncs
-with the identity provider and VPN access is terminated once the user is removed.
-1. **Sign-in redirect URIs**: Add your Firezone `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/okta/callback/`) as an entry to
-Authorized redirect URIs.
-1. **Assignments**:
-Limit to the groups you wish to provide access to your Firezone instance.
-
-
-
-Once settings are saved, you will be given a **Client ID**, **Client Secret**,
-and **Okta Domain**. These 3 values will be used in Step 2 to configure Firezone.
-
-
-
-## Step 2: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Okta` button on the sign in page.
-
-## Step 3 (optional): Restrict Access to specific users
-
-Okta can limit the users with access to the Firezone app. To do this,
-go to the Assignments tab of the Firezone App Integration in your Okta
-Admin Console.
-
-
diff --git a/www/docs/authenticate/oidc/onelogin.mdx b/www/docs/authenticate/oidc/onelogin.mdx
deleted file mode 100644
index c043f75d0..000000000
--- a/www/docs/authenticate/oidc/onelogin.mdx
+++ /dev/null
@@ -1,65 +0,0 @@
----
-title: OneLogin
-sidebar_position: 6
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating OneLogin
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with OneLogin (OIDC)
-
-Firezone supports Single Sign-On (SSO) using OneLogin
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `onelogin`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `OneLogin`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-## Step 1: Create custom connector
-
-Create a new OIDC connector by visiting **Appliances > Custom Connectors**.
-
-1. **App name**: `Firezone`
-1. **Icon**: [Firezone logo](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-or
-[Firezone icon](https://user-images.githubusercontent.com/52545545/156854754-da66a9e1-33d5-47f5-877f-eff8b330ab2b.png)
-(save link as).
-1. **Sign on method**: select **OpenID Connect**
-1. **Redirect URI**: Add your Firezone ` + /auth/oidc//callback/`
-(e.g. `https://firezone.example.com/auth/oidc/onelogin/callback/`).
-
-
-
-## Step 2: Obtain configuration parameters
-
-Next, click **Add App to Connector** to create an OIDC application.
-Visit the **SSO** tab, then change the token endpoint authentication method
-to **POST**.
-
-You will find the values for the config settings required by Firezone
-on this page as well.
-
-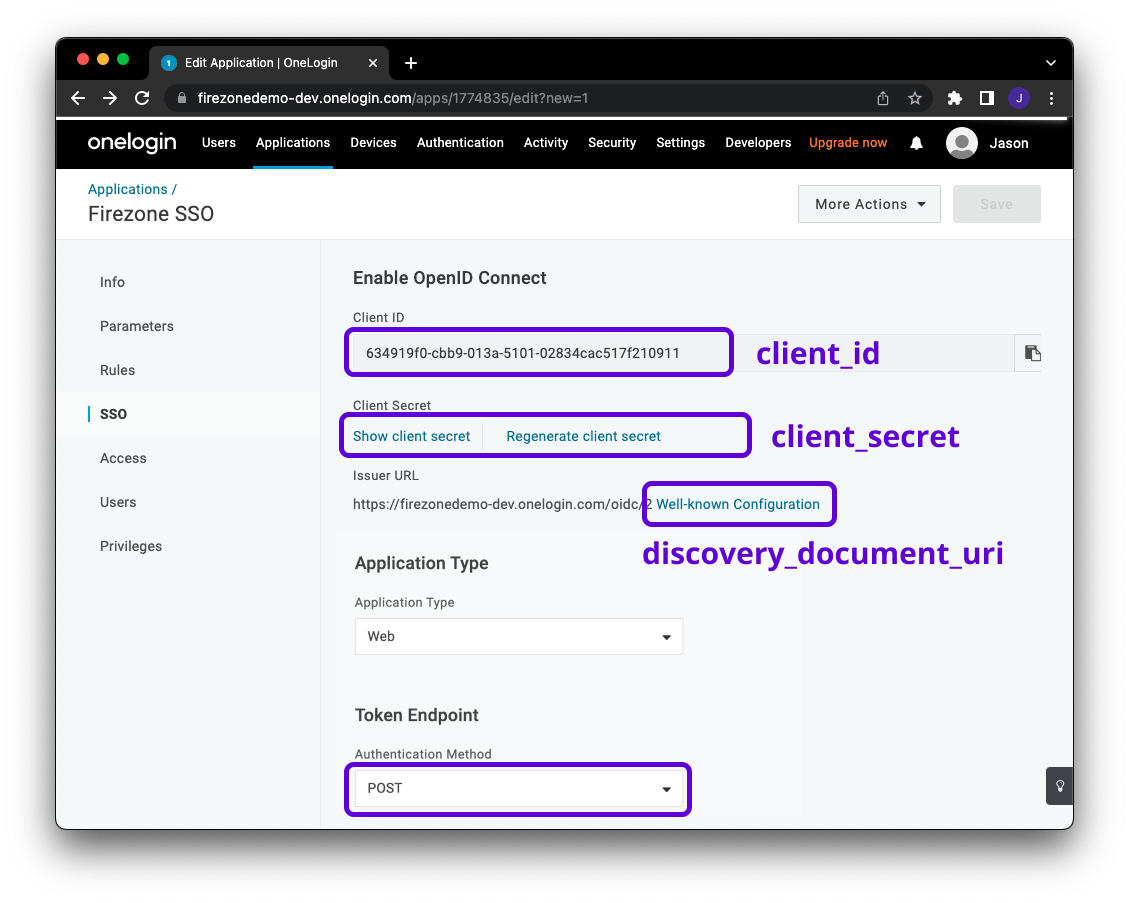
-
-## Step 3: Integrate with Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with OneLogin` button on the sign in page.
diff --git a/www/docs/authenticate/oidc/zitadel.mdx b/www/docs/authenticate/oidc/zitadel.mdx
deleted file mode 100644
index c44182311..000000000
--- a/www/docs/authenticate/oidc/zitadel.mdx
+++ /dev/null
@@ -1,103 +0,0 @@
----
-title: Zitadel
-sidebar_position: 7
-description:
- Enforce 2FA/MFA for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Zitadel
- for single sign-on using OpenID Connect (OIDC).
----
-
-# Enable SSO with Zitadel (OIDC)
-
-Firezone supports Single Sign-On (SSO) using Zitadel
-through the generic OIDC connector. This guide will walk you through how to
-obtain the following config settings required for the integration:
-
-1. **Config ID**: The provider's config ID. (e.g. `zitadel`)
-1. **Label**: The button label text that shows up on your Firezone login screen. (e.g. `Zitadel`)
-1. **Scope**: [OIDC scopes](https://openid.net/specs/openid-connect-basic-1_0.html#Scopes)
-to obtain from your OIDC provider. This should be set to `openid email profile offline_access`
-to provide Firezone with the user's email in the returned claims.
-1. **Response type**: Set to `code`.
-1. **Client ID**: The client ID of the application.
-1. **Client secret**: The client secret of the application.
-1. **Discovery Document URI**: The
-[OpenID Connect provider configuration URI](https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfig)
-which returns a JSON document used to construct subsequent requests to this
-OIDC provider.
-
-
-
-## Requirements
-
-* Setup your own [Zitadel Cloud](https://zitadel.cloud/) account.
-* Create your first Zitadel instance in the
- [Zitadel Customer portal](https://zitadel.cloud/admin/instances)
-* Login to your Zitadel instance and create a project (i.e. "Internal")
-
-More information about these steps can be found in
-[Zitadel's documentation](https://docs.zitadel.com/docs/guides/start/quickstart#try-out-zitadel-cloud).
-
-## Create Zitadel Application
-
-In the Instance Console, go to **Projects** and select the project you want,
-then click **New**.
-
-
-
-Give the application a name (e.g. "Firezone") and select **WEB**
-for the application type.
-
-
-
-Select **CODE** for the authentication method.
-
-
-
-Specify the redirect URI and post logout URI.
-
-1. **Redirect URIs**: `EXTERNAL_URL + /auth/oidc//callback/`
-(e.g. `https://vpn.example.com/auth/oidc/zitadel/callback/`)
-1. **Post Logout URIs**: `EXTERNAL_URL` (e.g. `https://vpn.example.com`)
-
-
-
-Double-check the configuration, then click **Create**.
-
-
-
-Copy the **ClientId** and **ClientSecret** as it will be used for the Firezone
-configuration.
-
-
-
-In the application **Configuration** click **Refresh Token** and then on
-**Save**. The refresh token is optional for some features of Firezone.
-
-
-
-In the application **Token Settings** select **User roles inside ID Token** and
-**User Info inside ID Token**. Save it with a click on **Save**.
-
-
-
-## Integrate With Firezone
-
-Navigate to the `/settings/security` page in the admin portal, click
-"Add OpenID Connect Provider" and enter the details you obtained in the steps
-above.
-
-Enable or disable the **Auto create users** option to automatically create
-an unprivileged user when signing in via this authentication mechanism.
-
-And that's it! The configuration should be updated immediately.
-You should now see a `Sign in with Zitadel` button on the sign in page.
-
-## Step 3 (optional): Restrict access to specific users
-
-Zitadel can limit which users have access to Firezone. To do this,
-go to the project where your created your application. In **General** you can
-find **Check Authorization on Authentication** which allows only users with at
-least one role to login to Firezone.
-
-
diff --git a/www/docs/authenticate/saml/README.mdx b/www/docs/authenticate/saml/README.mdx
deleted file mode 100644
index 9c6c09f27..000000000
--- a/www/docs/authenticate/saml/README.mdx
+++ /dev/null
@@ -1,81 +0,0 @@
----
-title: SAML 2.0
-sidebar_position: 11
-description: Enforce single sign-on with your identity provider. Integrate
- providers like Okta, Google, OneLogin, and JumpCloud using Firezone's
- SAML 2.0 connector.
----
-
-# Integrate your identity provider using SAML 2.0
-
-Firezone supports Single Sign-On (SSO) via SAML 2.0.
-
-## Supported identity providers
-
-In general, most identity providers that support SAML 2.0 should work with
-Firezone.
-
-| Provider | Support Status | Notes |
-| -------------------------- | ------------------------ | ---------------------------------- |
-| [Okta](okta) | **Tested and supported** | |
-| [Google Workspace](google) | **Tested and supported** | Uncheck `Require signed envelopes` |
-| [OneLogin](onelogin) | **Tested and supported** | |
-| [JumpCloud](jumpcloud) | **Tested and supported** | Uncheck `Require signed envelopes` |
-
-Occasionally, providers that don't implement the full SAML 2.0 standard or use
-uncommon configurations may be problematic. If this is the case, [contact us](/contact/support)
-about a custom integration.
-
-## Custom SAML cert and keyfile
-
-SAML 2.0 requires a set of private and public keys using the RSA or
-DSA algorithms along with an X.509 certificate that contains the public key.
-
-Firezone automatically generates these for on both Docker and Omnibus-based
-deployments. If you'd like to use your own cert and key, however, you can generate
-them with `openssl`:
-
-```
-openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout saml.key -out saml.crt
-```
-
-Then use them with your Firezone installation:
-
-
-
-
-Set the `SAML_KEYFILE_PATH` and `SAML_CERTFILE_PATH` environment variables to
-the path containing your `saml.key` and `saml.crt` above. If using our [example
-docker compose file](https://github.com/firezone/firezone/blob/master/docker-compose.prod.yml),
-which includes a volume for mapping configuration,
-save these files to `$HOME/.firezone/firezone` on the Docker host and set the
-`SAML_KEYFILE_PATH=/var/firezone/saml.key` and
-`SAML_CERTFILE_PATH=/var/firezone/saml.crt` environment variables for the Firezone
-container.
-
-
-
-
-## General setup instructions
-
-Once you've configured Firezone with an X.509 certificate and corresponding
-private key as shown above, you'll need a few more things to set up a generic
-SAML integration.
-
-### IdP metadata document
-
-You'll need to get the SAML Metadata XML document from your identity provider. In most
-cases this can be downloaded from your IdP's SAML App configuration dashboard.
-
-### ACS URL
-
-Firezone constructs the ACS URL based on the Base URL and Configuration ID entered
-in the Firezone SAML configuration, defaulting to: `EXTERNAL_URL/auth/saml/sp/consume/:config_id`,
-e.g. `https://firezone.company.com/auth/saml/sp/consume/okta`.
-
-### Entity ID
-
-The Firezone Entity ID can be configured with the `SAML_ENTITY_ID` environment variable
-and defaults to `urn:firezone.dev:firezone-app` if not set.
-
-See the [environment variable reference](/docs/reference/env-vars) for more information.
diff --git a/www/docs/authenticate/saml/google.mdx b/www/docs/authenticate/saml/google.mdx
deleted file mode 100644
index c40e9d352..000000000
--- a/www/docs/authenticate/saml/google.mdx
+++ /dev/null
@@ -1,54 +0,0 @@
----
-title: Google Workspace
-sidebar_position: 2
-description:
- Enforce 2FA/MFA using Google Workspace for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Google Workspace
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with Google Workspace (SAML 2.0)
-
-Firezone supports Single Sign-On (SSO) using Google through the generic SAML 2.0
-connector. This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the Google Workspace admin portal, create a new SAML app under
-the Application > Web and mobile apps tab. Use the following config values during setup:
-
-| Setting | Value |
-| --------------- | ---------------------------------------------------------------------------------------------------------------------------------------- |
-| App name | Firezone |
-| App icon | [save link as](https://user-images.githubusercontent.com/52545545/202567638-513dba14-ea8c-4da8-8f75-341310f1e456.png) |
-| ACS URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/google`). |
-| Entity ID | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| Signed response | Unchecked. |
-| Name ID format | Unspecified |
-| Name ID | Basic Information > Primary email |
-
-
-
-Once complete, save the changes and download the SAML metadata document. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | --------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | google | Firezone uses this value to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | Google | Appears on the sign in button for authentication. |
-| Metadata | see note | Paste the contents of the SAML metadata document you downloaded in the previous step from Google. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | **Unchecked.** | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-
-
-After saving the SAML config, you should see a `Sign in with Google` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/authenticate/saml/jumpcloud.mdx b/www/docs/authenticate/saml/jumpcloud.mdx
deleted file mode 100644
index db61c4d38..000000000
--- a/www/docs/authenticate/saml/jumpcloud.mdx
+++ /dev/null
@@ -1,71 +0,0 @@
----
-title: JumpCloud
-sidebar_position: 4
-description:
- Enforce 2FA/MFA using JumpCloud for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating JumpCloud
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with JumpCloud (SAML 2.0)
-
-:::note
-This guide assumes you have completed the prerequisite steps
-(e.g. generate self-signed X.509 certificates) outlined [here](/docs/authenticate/saml#prerequisites).
-:::
-
-Firezone supports Single Sign-On (SSO) using JumpCloud through the generic SAML 2.0 connector.
-This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the JumpCloud admin portal, create a new App under
-the SSO tab. At the bottom of the popup window, click `Custom SAML App`.
-
-After entering your desired value for `Display Label`, click the `SSO` tab,
-then use the following configuration values:
-
-| Setting | Value |
-| ------------------------- | ------------------------------------------------------------------------------------------------------------------------------------------ |
-| IdP Entity ID | Any unique string will work, e.g. `firezone-jumpcloud`. |
-| SP Entity ID | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| ACS URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id`, e.g. `https://firezone.company.com/auth/saml/sp/consume/jumpcloud`. |
-| SAMLSubject NameID | `email` |
-| SAMLSubject NameID Format | Leave at the default. |
-| Signature Algorithm | `RSA-SHA256` |
-| Sign Assertion | **Checked**. |
-| Login URL | This is your Firezone `EXTERNAL_URL/auth/saml/auth/signin/:config_id`, e.g. `https://firezone.company.com/auth/saml/auth/signin/jumpcloud` |
-
-Leave the rest of the settings unchanged, then click the `activate` button at the bottom-right.
-
-Your JumpCloud configuration should now resemble the following:
-
-
-
-Now, download the IdP Metadata document by selecting the App you just created
-and then clicking the `export metadata` button in the upper-right. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | ---------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | `jumpcloud` | Firezone uses this value to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | `JumpCloud` | Appears on the sign in button for authentication. |
-| Base URL | Leave unchanged. | |
-| Metadata | see note | Copy-paste the contents of the SAML metadata document you downloaded in the previous step from JumpCloud. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | **Unchecked.** | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-Your Firezone configuration should now resemble the following:
-
-
-
-After saving the SAML config, you should see a `Sign in with JumpCloud` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/authenticate/saml/okta.mdx b/www/docs/authenticate/saml/okta.mdx
deleted file mode 100644
index f0b1ad8c8..000000000
--- a/www/docs/authenticate/saml/okta.mdx
+++ /dev/null
@@ -1,62 +0,0 @@
----
-title: Okta
-sidebar_position: 1
-description: Enforce 2FA/MFA using Okta for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating Okta
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with Okta (SAML 2.0)
-
-:::note
-This guide assumes you have completed the prerequisite steps
-(e.g. generate self-signed X.509 certificates) outlined [here](/docs/authenticate/saml#prerequisites).
-:::
-
-Firezone supports Single Sign-On (SSO) using Okta through the generic SAML 2.0 connector. This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the Okta admin portal, create a new app integration under
-the Application tab. Select `SAML 2.0` as the authentication method.
-Use the following config values during setup:
-
-| Setting | Value |
-| ------------------------------ | -------------------------------------------------------------------------------------------------------------------------------------- |
-| App name | Firezone |
-| App logo | [save link as](https://user-images.githubusercontent.com/52545545/155907625-a4f6c8c2-3952-488d-b244-3c37400846cf.png) |
-| Single sign on URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/okta`). |
-| Audience (EntityID) | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| Name ID format | EmailAddress |
-| Application username | Email |
-| Update application username on | Create and update |
-
-[Okta's documentation](https://help.okta.com/oie/en-us/Content/Topics/Apps/Apps_App_Integration_Wizard_SAML.htm)
-contains additional details on the purpose of each configuration setting.
-
-
-
-After creating the SAML connector, visit the `View SAML setup instructions` link in
-the Sign On tab to download the metadata document. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | --------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | Okta | Used to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | Okta | Appears on the sign in button for authentication. |
-| Metadata | see note | Paste the contents of the SAML metadata document you downloaded in the previous step from Okta. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | Checked. | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-
-
-After saving the SAML config, you should see a `Sign in with Okta` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/authenticate/saml/onelogin.mdx b/www/docs/authenticate/saml/onelogin.mdx
deleted file mode 100644
index 73ac6372b..000000000
--- a/www/docs/authenticate/saml/onelogin.mdx
+++ /dev/null
@@ -1,67 +0,0 @@
----
-title: OneLogin
-sidebar_position: 3
-description:
- Enforce 2FA/MFA using Onelogin for users of Firezone's WireGuard®-based
- secure access platform. This guide walks through integrating OneLogin
- for single sign-on using the SAML 2.0 connector.
----
-
-# Enable SSO with OneLogin (SAML 2.0)
-
-:::note
-This guide assumes you have completed the prerequisite steps
-(e.g. generate self-signed X.509 certificates) outlined [here](/docs/authenticate/saml#prerequisites).
-:::
-
-Firezone supports Single Sign-On (SSO) using OneLogin through the generic SAML 2.0 connector.
-This guide will walk you through how to configure the integration.
-
-## Step 1: Create a SAML connector
-
-In the OneLogin admin portal, add an app under the application tab.
-Select `SAML Custom Connector (Advanced)` and provide the appropriate
-configuration settings under the under the configuration tab.
-
-The following fields should be filled out on this page:
-
-| Setting | Value |
-| ---------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- |
-| Audience (EntityID) | This should be the same as your Firezone `SAML_ENTITY_ID`, defaults to `urn:firezone.dev:firezone-app`. |
-| Recipient | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/onelogin`). |
-| ACS URL Validator | This field is regex to ensure OneLogin posts the response to the correct URL. For the sample URL below, we can use `^https:\/\/firezone\.company\.com\/auth\/saml\/sp\/consume\/onelogin` |
-| ACS URL | This is your Firezone `EXTERNAL_URL/auth/saml/sp/consume/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/onelogin`). |
-| Login URL | This is your Firezone `EXTERNAL_URL/auth/saml/auth/signin/:config_id` (e.g., `https://firezone.company.com/auth/saml/sp/consume/onelogin`). |
-| SAML initiator | Service Provider |
-| SAML signature element | Both |
-| Encrypt Assertion | Checked. |
-
-[OneLogin's docs](https://onelogin.service-now.com/support?id=kb_article&sys_id=912bb23edbde7810fe39dde7489619de&kb_category=93e869b0db185340d5505eea4b961934)
-provide a good overview of each field's purpose.
-
-
-
-Once complete, save the changes and download the SAML metadata document
-found unde the `More Actions` dropdown. You'll need
-to copy-paste the contents of this document into the Firezone portal in the next step.
-
-## Step 2: Add SAML identity provider to Firezone
-
-In the Firezone portal, add a SAML identity provider under the Security tab
-by filling out the following information:
-
-| Setting | Value | Notes |
-| ------------------------- | --------------- | ------------------------------------------------------------------------------------------------------------------------------------------- |
-| Config ID | `onelogin` | Used to construct endpoints required in the SAML authentication flow (e.g., receiving assertions, login requests). |
-| Label | `OneLogin` | Appears on the sign in button for authentication. |
-| Metadata | see note | Paste the contents of the SAML metadata document you downloaded in the previous step from OneLogin. |
-| Sign assertions | Checked. | |
-| Sign metadata | Checked. | |
-| Require signed assertions | Checked. | |
-| Require signed envelopes | Checked. | |
-| Auto create users | Default `false` | Enable this setting to automatically create users when signing in with this connector for the first time. Disable to manually create users. |
-
-
-
-After saving the SAML config, you should see a `Sign in with OneLogin` button
-on your Firezone portal sign-in page.
diff --git a/www/docs/deploy/README.mdx b/www/docs/deploy/README.mdx
deleted file mode 100644
index 136409fe8..000000000
--- a/www/docs/deploy/README.mdx
+++ /dev/null
@@ -1,90 +0,0 @@
----
-title: Deploy
-sidebar_position: 2
-description:
- Install Firezone's WireGuard®-based secure access platform on a support
- host using our Docker (recommended) or Omnibus deployment methods.
----
-
-# Deploy Firezone
-
-Firezone can be deployed on most Docker-supported platforms in a couple of minutes.
-Read more below to get started.
-
-## Step 1: Prepare to deploy
-
-Regardless of which deployment method you choose, you'll need to follow the
-preparation steps below before deploying Firezone to production.
-
-1. [Create a DNS record](#create-a-dns-record)
-1. [Set up SSL](#set-up-ssl)
-1. [Open required firewall ports](#open-required-firewall-ports)
-
-### Create a DNS record
-
-Firezone requires a fully-qualified domain name (e.g. `firezone.company.com`)
-for production use. You'll need to create the appropriate DNS record at your
-registrar to achieve this. Typically this is either an A, CNAME, or AAAA record
-depending on your requirements.
-
-### Set up SSL
-
-You'll need a valid SSL certificate to use Firezone in a production capacity.
-Firezone supports ACME for automatic provisioning of SSL certificates for both
-Docker-based and Omnibus-based installations. This is recommended in most cases.
-
-
-
-
-#### Setting up ACME for Docker-based deployments
-
-For Docker-based deployments, the simplest way to provision an SSL
-certificate is to use our Caddy service example in docker-compose.yml.
-Caddy uses ACME to automatically provision SSL certificates as long as
-it's available on port 80/tcp and the DNS record for the server is valid.
-
-See the [Docker deployment guide](docker) for more info.
-
-
-
-
-### Open required firewall ports
-
-By default, Firezone requires ports `443/tcp` and `51820/udp` to be
-accessible for HTTPS and WireGuard traffic respectively.
-These ports can change based on what you've configured in the configuration file.
-See the
-[configuration file reference](../reference/configuration-file)
-for details.
-
-### Resource requirements
-
-We recommend **starting with 1 vCPU and 1 GB of RAM and scaling up** as the
-number of users and devices grows.
-
-For Omnibus-based deployments on servers with less than 1GB of memory, we
-recommend turning on swap to prevent the Linux kernel from killing
-Firezone processes unexpectedly. When this happens, it's often difficult to
-debug and results in strange, unpredictable failure modes.
-
-For the VPN tunnels themselves, Firezone uses in-kernel WireGuard, so its
-performance should be very good. 1 vCPU should be more than enough to saturate
-a 1 Gbps link.
-
-## Step 2: Deploy
-
-You have two options for deploying Firezone:
-
-1. [Docker](docker) (recommended)
-1. [Omnibus](omnibus)
-
-Docker is the easiest way to install, manage, and upgrade Firezone and is the
-preferred method of deployment.
-
-:::warning
-Chef Infra Client, the configuration system Chef Omnibus relies on, has been
-[scheduled for End-of-Life in 2024](https://docs.chef.io/versions/). As such,
-support for Omnibus-based deployments will be removed starting with Firezone 0.8.
-To transition to Docker from Omnibus today, follow our [migration guide
-](../administer/migrate).
-:::
diff --git a/www/docs/deploy/advanced/README.mdx b/www/docs/deploy/advanced/README.mdx
deleted file mode 100644
index fad3678d9..000000000
--- a/www/docs/deploy/advanced/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Advanced
-sidebar_position: 8
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/deploy/advanced/build-from-source.mdx b/www/docs/deploy/advanced/build-from-source.mdx
deleted file mode 100644
index be6b789d4..000000000
--- a/www/docs/deploy/advanced/build-from-source.mdx
+++ /dev/null
@@ -1,91 +0,0 @@
----
-title: Build From Source
-sidebar_position: 1
----
-
-Building from source allows you to bring Firezone to unsupported platforms.
-
-:::warning
-You're entering unsupported territory. This is not for the faint of heart and
-will require being able to figure out snags you may hit on your own.
-
-If you're very comfortable with your environment of choice, then read on to
-learn how to build Firezone from source.
-:::
-
-:::info
-You will need to setup your own service management for Firezone (eg. `runit`,
-`systemd`, shell scripts). You will also need to install and configure your
-own database (eg. `postgres`) and reverse proxy (eg. `caddy`, `nginx`).
-
-Info about database configuration is [here](../external-database/#configure-firezone-to-connect),
-and info about configuring a reverse proxy is [here](../reverse-proxy/#proxy-requirements).
-:::
-
-# Prerequisites
-
-:::info
-Check the `.tool-versions` file [here](https://github.com/firezone/firezone/blob/master/.tool-versions)
-for the versions we use for Erlang, Elixir, and Node. If your system supports it,
-you can install these using [asdf-vm](https://asdf-vm.com/guide/getting-started.html)
-using a similar `.tool-versions` of your own to match versions. Your system's package
-manager may have them as well.
-:::
-
-**These must be available in the user's path that runs Firezone.**
-
-- [Erlang/OTP](https://www.erlang.org)
-- [Elixir](https://elixir-lang.org)
-- [NodeJS](https://nodejs.org)
-
-# Steps
-
-From your terminal, run these steps to build Firezone:
-
-```bash
-git clone https://github.com/firezone/firezone
-cd firezone
-mix local.rebar --force
-mix local.hex --force
-MIX_ENV=prod mix deps.get
-MIX_ENV=prod mix release
-```
-
-After the release build finishes, you should have a shiny new Firezone release artifact in
-`/_build/dev/rel/firezone`. In the `bin` folder, the `firezone` binary
-can be used to start up Firezone. If you run it without any arguments you should see
-a list of available commands like this:
-
-```bash
-Usage: firezone COMMAND [ARGS]
-
-The known commands are:
-
- start Starts the system
- start_iex Starts the system with IEx attached
- daemon Starts the system as a daemon
- daemon_iex Starts the system as a daemon with IEx attached
- eval "EXPR" Executes the given expression on a new, non-booted system
- rpc "EXPR" Executes the given expression remotely on the running system
- remote Connects to the running system via a remote shell
- restart Restarts the running system via a remote command
- stop Stops the running system via a remote command
- pid Prints the operating system PID of the running system via a remote command
- version Prints the release name and version to be booted
-```
-
-Most deployment-related configuration is handled with environment variables.
-You'll probably want to at least set variables related to your reverse proxy
-and database. See the [ENV var reference](/docs/reference/env-vars/) for an exhaustive list.
-
-Now all you need are the database and reverse proxy that you've previously set up.
-Once that's done, you can use `firezone start` to start Firezone and run
-`create-or-reset-admin` (in the same `bin` dir) to create the admin user and use
-it to log into Firezone from a web browser to start setting up your brand new
-custom instance that you built by hand with a little bit of elbow grease :)
-
-:::info
-As mentioned at the top, it's recommended to use some sort of service management
-to start and stop Firezone easily without having to manually do it using the
-`firezone` binary directly. But the choice is yours, since you're in control!
-:::
diff --git a/www/docs/deploy/advanced/external-database.mdx b/www/docs/deploy/advanced/external-database.mdx
deleted file mode 100644
index 867fddcb4..000000000
--- a/www/docs/deploy/advanced/external-database.mdx
+++ /dev/null
@@ -1,58 +0,0 @@
----
-title: Custom External Database
-sidebar_position: 2
----
-
-Firezone uses [Postgresql DB](https://postgresql.org) as its primary data store.
-
-## Compatibility
-
-Firezone should work fine on Postgres versions 12 and above, but we recommend
-using the latest stable version whenever possible. If you find an issue with
-your particular version of Postgres, [please open a GitHub issue
-](https://github.com/firezone/firezone/issues).
-
-In general, Firezone should also work fine using external Postgres-based
-database services like Amazon RDS. See the [configuration
-](#configure-firezone-to-connect) section below for more information configuring
-Firezone with an external DB.
-
-:::warning
-Configuring Firezone to use an external database can be complicated and
-error-prone. We recommend using the bundled Postgres for Omnibus-based
-deployments or the official Postgres Docker image for Docker-based deployments
-if possible.
-:::
-
-## Configure Firezone to Connect
-
-
-
-
-The Firezone Docker image uses the following environment
-variables to connect to the DB (fields in bold required):
-
-| Name | Description | Format | Default |
-| ----------------------------- | --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | --------------------- | ------------------------------------ |
-| **`DATABASE_ENCRYPTION_KEY`** | The base64-encoded symmetric encryption key used to encrypt and decrypt sensitive fields. | base64-encoded String | None -- must be generated on install |
-| `DATABASE_HOST` | Database host | IP or hostname | `postgres` |
-| `DATABASE_PORT` | Database port | Integer | `5432` |
-| `DATABASE_NAME` | Name of database | String | `firezone` |
-| `DATABASE_USER` | User | String | `postgres` |
-| `DATABASE_PASSWORD` | Password | String | `postgres` |
-| `DATABASE_POOL` | Size of the Firezone connection pool | Integer | `10` |
-| `DATABASE_SSL` | Whether to connect to the database over SSL | Boolean | `false` |
-| `DATABASE_SSL_OPTS` | Map of options to send to the `:ssl_opts` option when connecting over SSL. See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options) | JSON-encoded String | `{}` |
-| `DATABASE_PARAMETERS` | Map of parameters to send to the `:parameters` option when connecting to the database. See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options). | JSON-encoded String | `{}` |
-
-For more information, see the [environment variable reference
-](/docs/reference/env-vars/).
-
-:::note
-The official `postgres` docker image can be configured by setting
-environment variables for the container. See the Postgres image
-[documentation](https://hub.docker.com/_/postgres) for more details.
-:::
-
-
-
diff --git a/www/docs/deploy/advanced/reverse-proxy.mdx b/www/docs/deploy/advanced/reverse-proxy.mdx
deleted file mode 100644
index 761a10d68..000000000
--- a/www/docs/deploy/advanced/reverse-proxy.mdx
+++ /dev/null
@@ -1,105 +0,0 @@
----
-title: Custom Reverse Proxy
-sidebar_position: 3
----
-
-:::warning
-Using a custom reverse proxy is an advanced configuration. The default bundled
-Nginx proxy (Omnibus-based deployments) and Caddy (Docker-based deployments) is
-suitable for the vast majority of use cases and is recommended for most users.
-There are important security risks if the reverse proxy is not set up correctly.
-:::
-
-## Introduction
-
-Firezone comes with bundled [Nginx](https://www.nginx.com/) (Omnibus-based
-deployments) or uses Caddy (Docker-based deployments) by default. However, in
-some cases you might want to deploy your own server such as when using
-your own load balancer.
-
-## Prerequisites
-
-Below you will find the requirements in order to setup Firezone with a custom
-reverse proxy.
-
-### Firezone configuration requirements
-
-- Disable the bundled Nginx by setting `default['firezone']['nginx']['enabled']`
- to `false` in the config file.
-- If you have any immediate proxies between your primary reverse proxy and the
- Firezone web app, add their IPs to
- `default['firezone']['phoenix']['external_trusted_proxies']`. Because of the
- way the [X-Forwarded-For header works](https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Forwarded-For),
- this is needed to parse the actual client's IP address to prevent
- IP spoofing.
-
-:::note
-The `external_trusted_proxies` list automatically implicitly includes the
-following private CIDR ranges, even if they're not specified in the
-configuration file:
-
-- `127.0.0.0/8`
-- `10.0.0.0/8`
-- `172.16.0.0/12`
-- `192.168.0.0/16`
-- `::1/128`
-- `fc00::/7`
-
-This means any web requests originating from these IPs are automatically ignored
-from the `X-Forwarded-For` headers. If you're accessing Firezone from any IPs in
-this range (as seen by the Firezone web app), be sure to add them to the
-`default['firezone']['phoenix']['clients']` configuration option instead.
-:::
-
-Read more about the configuration options
-[here](/docs/reference/configuration-file/).
-
-### Proxy requirements
-
-- All your proxies need to configure the `X-Forwarded-For` header as explained
- [here](https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Forwarded-For)
-- Your proxy should also set the `X-Forwarded-Proto` to `https`.
-- Your proxy (or another downstream proxy) **must** terminate SSL since we
- enforce [secure cookies](https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies#restrict_access_to_cookies).
-- Firezone requires the use of WebSockets to establish realtime connections. We
- recommend following your proxy's specific documentation for supporting
- WebSockets as each proxy varies. In general, your proxy needs to be able to
- proxy HTTP 1.1 connections, and the Firezone web app expects the following
- headers to be set:
- - `Connection: upgrade`
- - `Upgrade: websocket`
-
-## Security considerations
-
-In addition to the headers above, we recommend adding the following headers for
-security purposes:
-
-- `X-XSS-Protection: 1; mode=block`
-- `X-Content-Type-Options nosniff`
-- `Referrer-Policy no-referrer-when-downgrade`
-- `Content-Security-Policy: default-src 'self' ws: wss: http: https: data: blob:
-'unsafe-inline'; frame-ancestors 'self';`
-- `Permissions-Policy: interest-cohort=()`
-
-Since the upstream Firezone web app expects plain HTTP traffic, any requests the
-proxy forwards is sent over HTTP and thus is **not encrypted**. In most cases,
-the reverse proxy is installed in a trusted network, and this is not an issue.
-But the connection between your trusted proxy and the Firezone web app spans
-an untrusted network (such as the Internet), you may want to leave the bundled
-`nginx` proxy enabled for SSL termination, and set up your custom
-reverse proxy to proxy to that instead.
-
-## Example configurations
-
-- [Apache](/docs/reference/reverse-proxy-templates/apache/)
-- [Traefik](/docs/reference/reverse-proxy-templates/traefik/)
-- [HAProxy](/docs/reference/reverse-proxy-templates/haproxy/)
-
-These configurations are written to be as simple as possible. They're designed
-to function as a simple template which you can customize further to suit your
-needs.
-
-If you have a working configuration for a different reverse proxy or a different
-version of an existing one we appreciate any
-[contribution](https://github.com/firezone/firezone/) to expand the examples for
-the community.
diff --git a/www/docs/deploy/configure.mdx b/www/docs/deploy/configure.mdx
deleted file mode 100644
index 1788ebd35..000000000
--- a/www/docs/deploy/configure.mdx
+++ /dev/null
@@ -1,45 +0,0 @@
----
-title: Configure
-sidebar_position: 5
----
-
-# Configure Firezone
-
-There are two types of configuration in Firezone:
-
-- [Runtime configuration](#runtime-configuration): Application configuration
- related to day-to-day operation of Firezone.
-- [Deployment configuration](#deployment-configuration): Deployment or
- infrastructure-related configuration relevant to running Firezone on-prem.
-
-## Runtime configuration
-
-Most day-to-day configuration of Firezone can be done via the Web UI or
-[REST API](/docs/reference/rest-api/configurations).
-This type of configuration can be expected to be changed **with no downtime**
-in a production deployment.
-
-We're actively working to move more configuration variables to
-this type of configuration, so expect more ENV vars to transition to runtime
-configuration in the future.
-
-## Deployment configuration
-
-Deployment-related and infrastructure configuration require restarting Firezone
-services after change.
-
-
-
-
-Docker-based deployments are configured through environment
-variables passed to the `firezone` container. These can be
-specified either in a `.env` file in the current directory,
-the `docker-compose.yml` file, or passed to the `docker run`
-call directly. See the [env var reference](../../reference/env-vars)
-for a complete listing.
-
-See [Docker's documentation
-](https://docs.docker.com/compose/envvars-precedence/) for more information.
-
-
-
diff --git a/www/docs/deploy/docker/README.mdx b/www/docs/deploy/docker/README.mdx
deleted file mode 100644
index 322c76f2f..000000000
--- a/www/docs/deploy/docker/README.mdx
+++ /dev/null
@@ -1,180 +0,0 @@
----
-title: Docker
-sidebar_position: 2
-description: Install Firezone via Docker to manage secure remote
- access to private networks and resources.
----
-
-# Install Firezone with Docker
-
-As of 0.6.0, Docker is now the **preferred method** for
-deploying Firezone. Docker offers a number of benefits over the old
-[Omnibus method](../omnibus):
-
-- **Simpler, more robust upgrades**: In most cases, simply pull the latest `firezone/firezone`
- image and restart the container.
-- **Simpler configuration**: Most day-to-day configuration of Firezone can now
- be done in the web UI instead of the `/etc/firezone/firezone.rb` configuration
- file. All other configuration variables can be specified as ENV vars to the
- Firezone container.
-- **Smaller footprint**: The Firezone image weighs in at a couple dozen
- megabytes versus hundreds of megabytes for the Omnibus package.
-- **Portability**: Firezone now runs on any platform that supports Docker.
-- **Security**: Containerization providers better security isolation than
- simply running as an unprivileged local user.
-
-## Step 1: Prerequisites
-
-- Ensure you're on a [supported platform](supported-platforms) with [
- docker-compose](https://docs.docker.com/compose/install/) **version 2
- or higher** installed.
-- Ensure port forwarding is enabled on your firewall.
- The default Firezone configuration requires the following ports to be open:
- - `80/tcp` (optional): For automatically issuing SSL certificates.
- - `443/tcp`: To access the web UI.
- - `51820/udp`: VPN traffic listen port.
-
-:::caution
-Before deploying Firezone in **production**, you'll need a valid DNS record
-pointing to this instance. See [Prepare to Deploy](../#prepare-to-deploy)
-if you haven't done this already.
-:::
-
-## Step 2: Install server
-
-After prerequisites are satisfied, you're ready to install the Firezone Server.
-
-### Option 1: Automatic install
-
-The easiest way to deploy Firezone with Docker is the automatic install script:
-
-
-
-This will ask you a few questions regarding initial configuration, then proceed
-to download a sample docker-compose.yml file, configure it with your responses,
-and then print instructions for accessing the Web UI.
-
-Firezone files will be installed in `$HOME/.firezone` by default.
-
-### Option 2: Manual install
-
-If the automatic install fails, or you'd just like more control over the
-installation process, follow the steps below to install manually.
-
-1. Download the docker compose template to a local working directory:
- **For Linux**:
-
-```
-curl -fsSL https://raw.githubusercontent.com/firezone/firezone/master/docker-compose.prod.yml -o docker-compose.yml
-```
-
-**For macOS, Windows (non-production only)**:
-
-```
-curl -fsSL https://raw.githubusercontent.com/firezone/firezone/master/docker-compose.desktop.yml -o docker-compose.yml
-```
-
-1. Generate required secrets:
-
-```
-docker run --rm firezone/firezone bin/gen-env > .env
-```
-
-1. At a minimum, change the `DEFAULT_ADMIN_EMAIL` and `EXTERNAL_URL` variables.
- Optionally modify other secrets as needed.
-1. Migrate the database:
-
-```
-docker compose run --rm firezone bin/migrate
-```
-
-1. Create the first admin:
-
-```
-docker compose run --rm firezone bin/create-or-reset-admin
-```
-
-1. Bring the services up: `docker compose up -d`
-
-You should now be able to access the Firezone web portal at the `EXTERNAL_URL`
-variable you defined above.
-
-## Step 3 (optional): Enable on boot
-
-If you'd like Firezone to start automatically on boot, first ensure Docker is enabled at startup:
-
-```
-sudo systemctl enable docker
-```
-
-Then, make sure your Firezone services have the `restart: always` or `restart: unless-stopped` option
-specified in the `docker-compose.yml` file. This is the default used in the docker-compose.prod.yml
-production template file.
-
-## Step 4 (optional): Enable IPv6
-
-By default, Firezone ships with IPv6 connectivity enabled inside the tunnel but not routable
-to the public internet. To enable IPv6 support in Docker-deployed Firezone, follow the steps below.
-
-1. Enable IPv6 support within Docker by adding the following to `/etc/docker/daemon.json`:
-
-```json
-{
- "ipv6": true,
- "ip6tables": true,
- "experimental": true,
- "fixed-cidr-v6": "2001:db8:1::/64"
-}
-```
-
-This enables IPv6 NAT and configures IPv6 forwarding for Docker containers.
-
-1. Enable router advertisements on boot for your default egress interface:
-
-```
-egress=`ip route show default 0.0.0.0/0 | grep -oP '(?<=dev ).*' | cut -f1 -d' ' | tr -d '\n'`
-sudo bash -c "echo net.ipv6.conf.${egress}.accept_ra=2 >> /etc/sysctl.conf"
-```
-
-1. Reboot
-
-You should now be able to ping google from within a docker container:
-
-```
-docker run --rm -t busybox ping6 -c 4 google.com
-```
-
-You shouldn't need to manually add any `iptables` rules to enable IPv6 SNAT/masquerading for
-tunneled traffic; Firezone handles this for you by default on start.
-
-## Step 5: Install client apps
-
-:::note
-Firezone currently uses WireGuard's
-[open-source client apps](https://www.wireguard.com/install/).
-:::
-
-Once successfully deployed, users and devices can be added to
-connect to the VPN server:
-
-- [Add Users](../../user-guides/add-users):
- Add users to grant them access to your network.
-- [Client Instructions](../../user-guides/client-instructions):
- Instructions to establish a VPN session.
-
-import SupportOptions from "@site/src/partials/_support_options.mdx";
-;
-
-## Post Setup
-
-Congrats! You have completed the setup, but there's a lot more you can do with
-Firezone:
-
-- [Integrate your identity provider](../../authenticate/)
- for authenticating clients
-- Using Firezone as a NAT gateway to
- [establish a static IP for your team](../../user-guides/use-cases/nat-gateway)
-- Create tunnels between multiple peers with
- [reverse tunnels](../../user-guides/use-cases/reverse-tunnel)
-- Only route certain traffic through Firezone with
- [split tunneling](../../user-guides/use-cases/split-tunnel)
diff --git a/www/docs/deploy/docker/supported-platforms.mdx b/www/docs/deploy/docker/supported-platforms.mdx
deleted file mode 100644
index 5bcd05049..000000000
--- a/www/docs/deploy/docker/supported-platforms.mdx
+++ /dev/null
@@ -1,33 +0,0 @@
----
-title: Supported Platforms
-sidebar_position: 1
----
-
-Firezone currently supports the following platforms for Docker-based
-deployments.
-
-| OS | Architecture(s) | Runtime | Status | Notes |
-| --- | --- | --- | --- | --- |
-| Linux | `amd64` `arm64` | Docker Server | **Fully-supported** | `wireguard` kernel module needed for kernels < `5.6`. |
-| Linux | `amd64` `arm64` | Docker Desktop | Works, but unsupported. | Not recommended for production deployments. See [caveats](#docker-desktop-caveats). |
-| macOS | `amd64` `arm64` | Docker Desktop | Works. but unsupported. | Not recommended for production deployments. See [caveats](#non-linux-platform-caveats). |
-| Windows | `amd64` `arm64` | Docker Desktop | **Untested** | Not recommended for production deployments. See [caveats](#non-linux-platform-caveats). |
-
-## Docker Desktop caveats
-
-Docker Desktop [rewrites the source address
-](https://www.docker.com/blog/how-docker-desktop-networking-works-under-the-hood/)
-for packets flowing out of container networks under some conditions. This can
-cause routing loops and other hard to debug connectivity issues with Firezone.
-We recommend **only** using Docker Server for Linux for production deployments.
-
-## Non-Linux platform caveats
-
-Only Docker for Linux supports the host networking mode, so macOS and Windows
-platforms will be able unable to properly attribute client source address
-for HTTP requests. This means any IP-based throttling or logging in your
-chosen proxy (`caddy` by default) will be ineffective, since the source
-IP will always be the Docker-side host IP (typically `172.X.0.1`).
-
-Egress rules operate on the tunneled client IP address and aren't affected
-by this limitation.
diff --git a/www/docs/deploy/security-considerations.mdx b/www/docs/deploy/security-considerations.mdx
deleted file mode 100644
index 60d974a32..000000000
--- a/www/docs/deploy/security-considerations.mdx
+++ /dev/null
@@ -1,57 +0,0 @@
----
-title: Security Considerations
-sidebar_position: 6
----
-
-# Security considerations
-
-**Disclaimer**: Firezone is still beta software. The codebase has not yet
-received a formal security audit. For highly sensitive and mission-critical
-production deployments, we recommend disabling local authentication as
-detailed [below](#production-deployments).
-
-## List of services and ports
-
-Shown below is a table of default ports used by Firezone services.
-
-
-
-
-| Service | Port | Listen address | Description |
-| ---------- | ----------- | -------------- | ----------------------------------------------------------------------------- |
-| Caddy | `443/tcp` | `all` | Public HTTPS port for administering Firezone and facilitating authentication. |
-| Caddy | `80/tcp` | `all` | Public HTTP port used for ACME. Disabled when ACME is disabled. |
-| WireGuard | `51820/udp` | `all` | Public WireGuard port used for VPN sessions. |
-| Postgresql | `5432/tcp` | `-` | Containerized port used for bundled Postgresql server. |
-| Phoenix | `13000/tcp` | `-` | Containerized port used by upstream elixir app server. |
-
-
-
-
-| Service | Port | Listen address | Description |
-| ---------- | ----------- | -------------- | ----------------------------------------------------------------------------- |
-| Nginx | `443/tcp` | `all` | Public HTTPS port for administering Firezone and facilitating authentication. |
-| Nginx | `80/tcp` | `all` | Public HTTP port used for ACME. Disabled when ACME is disabled. |
-| WireGuard | `51820/udp` | `all` | Public WireGuard port used for VPN sessions. |
-| Postgresql | `15432/tcp` | `127.0.0.1` | Local-only port used for bundled Postgresql server. |
-| Phoenix | `13000/tcp` | `127.0.0.1` | Local-only port used by upstream elixir app server. |
-
-
-
-
-## Production deployments
-
-For production deployments of Firezone, we recommend you disable local authentication
-altogether by setting `default['firezone']['authentication']['local']['enabled'] = false`
-(Omnibus-based deployments) or `LOCAL_AUTH_ENABLED=false` (Docker-based deployments).
-Local authentication can also be disabled on the `/settings/security` page.
-
-:::caution
-Ensure you've set up a working [OIDC](/docs/authenticate/oidc/) or [SAML](/docs/authenticate/saml/)-based
-authentication provider before disabling the local authentication method.
-:::
-
-## Reporting security issues
-
-To report any security-related bugs, see [our security bug reporting policy
-](https://github.com/firezone/firezone/blob/master/SECURITY.md).
diff --git a/www/docs/reference/README.mdx b/www/docs/reference/README.mdx
deleted file mode 100644
index 170fb3136..000000000
--- a/www/docs/reference/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Reference
-sidebar_position: 6
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/reference/_audit-logs.mdx b/www/docs/reference/_audit-logs.mdx
deleted file mode 100644
index 0c5785ab2..000000000
--- a/www/docs/reference/_audit-logs.mdx
+++ /dev/null
@@ -1,17 +0,0 @@
----
-title: Audit Logs
-sidebar_position: 2
----
-
-# Audit logs
-
-Firezone maintains two types of logs tied to user identity: configuration logs
-and network activity logs.
-
-Configuration logs track events related to the configuration of Firezone
-itself, either by admins or users. Network activity logs track connections to
-protected resources made by users of your network.
-
-Logged events are recorded as JSON objects and stored in the database. These
-are accessible via a REST API or the Firezone portal, and exportable to CSV
-format.
diff --git a/www/docs/reference/configuration-file.mdx b/www/docs/reference/configuration-file.mdx
deleted file mode 100644
index 9f8c9ec8f..000000000
--- a/www/docs/reference/configuration-file.mdx
+++ /dev/null
@@ -1,186 +0,0 @@
----
-title: Configuration File
-sidebar_position: 2
----
-
-# Omnibus configuration options
-
-:::warning
-This reference is written for Omnibus-based deployments of Firezone. For
-Docker-based deployments visit the [Environment Variables](../env-vars) page.
-:::
-
-To configure Omnibus-based deployments of Firezone:
-
-1. Edit `/etc/firezone/firezone.rb` with your changes.
-1. Run `sudo firezone-ctl reconfigure` to process the changes and restart affected services.
-
-Read more about configuring Firezone in the [configure guide](/docs/deploy/configure).
-
-## Configuration file reference
-
-Shown below is a complete listing of the configuration options available in
-`/etc/firezone/firezone.rb`.
-
-
-
-
-| Option | Description | Default Value |
-| -------------------------------------------------------------------- | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------ |
-| `default['firezone']['external_url']` | URL used to access the web portal of this Firezone instance. | "https://#{node['fqdn'] || node['hostname']}" |
-| `default['firezone']['config_directory']` | Top-level directory for Firezone configuration. | `'/etc/firezone'` |
-| `default['firezone']['install_directory']` | Top-level directory to install Firezone to. | `'/opt/firezone'` |
-| `default['firezone']['app_directory']` | Top-level directory to install the Firezone web application. | `"#{node['firezone']['install_directory']}/embedded/service/firezone"` |
-| `default['firezone']['log_directory']` | Top-level directory for Firezone logs. | `'/var/log/firezone'` |
-| `default['firezone']['var_directory']` | Top-level directory for Firezone runtime files. | `'/var/opt/firezone'` |
-| `default['firezone']['user']` | Name of unprivileged Linux user most services and files will belong to. | `'firezone'` |
-| `default['firezone']['group']` | Name of Linux group most services and files will belong to. | `'firezone'` |
-| `default['firezone']['admin_email']` | Email address for initial Firezone user. | `"firezone@localhost"` |
-| `default['firezone']['max_devices_per_user']` | Maximum number of devices a user can have. | `10` |
-| `default['firezone']['allow_unprivileged_device_management']` | Allows non-admin users to create and delete devices. | `true` |
-| `default['firezone']['allow_unprivileged_device_configuration']` | Allows non-admin users to modify device configurations. When disabled, prevents unprivileged users from changing all device fields except for `name` and `description`. | `true` |
-| `default['firezone']['egress_interface']` | Interface name where tunneled traffic will exit. If nil, the default route interface will be used. | `nil` |
-| `default['firezone']['fips_enabled']` | Enable or disable OpenSSL FIPs mode. | `nil` |
-| `default['firezone']['logging']['enabled']` | Enable or disable logging across Firezone. Set to `false` to disable logging entirely. | `true` |
-| `default['enterprise']['name']` | Name used by the Chef 'enterprise' cookbook. | `'firezone'` |
-| `default['firezone']['install_path']` | Install path used by Chef 'enterprise' cookbook. Should be set to the same as the `install_directory` above. | `node['firezone']['install_directory']` |
-| `default['firezone']['sysvinit_id']` | An identifier used in `/etc/inittab`. Must be a unique sequence of 1-4 characters. | `'SUP'` |
-| `default['firezone']['authentication']['local']['enabled']` | Enable or disable local email/password authentication. | `true` |
-| `default['firezone']['authentication']['disable_vpn_on_oidc_error']` | Disable a user's VPN if an error is detected trying to refresh their OIDC token. | `false` |
-| `default['firezone']['authentication']['oidc']` | OpenID Connect config, in the format of `{"provider" => [config...]}` - See [OpenIDConnect documentation](https://hexdocs.pm/openid_connect/readme.html) for config examples. | `{}` |
-| `default['firezone']['nginx']['enabled']` | Enable or disable the bundled nginx server. | `true` |
-| `default['firezone']['nginx']['ssl_port']` | HTTPS listen port. | `443` |
-| `default['firezone']['nginx']['directory']` | Directory to store Firezone-related nginx virtual host configuration. | `"#{node['firezone']['var_directory']}/nginx/etc"` |
-| `default['firezone']['nginx']['log_directory']` | Directory to store Firezone-related nginx log files. | `"#{node['firezone']['log_directory']}/nginx"` |
-| `default['firezone']['nginx']['log_rotation']['file_maxbytes']` | File size at which to rotate Nginx log files. | `104857600` |
-| `default['firezone']['nginx']['log_rotation']['num_to_keep']` | Number of Firezone nginx log files to keep before discarding. | `10` |
-| `default['firezone']['nginx']['log_x_forwarded_for']` | Whether to log Firezone nginx `x-forwarded-for` header. | `true` |
-| `default['firezone']['nginx']['hsts_header']['enabled']` | Enable or disable [HSTS](https://www.nginx.com/blog/http-strict-transport-security-hsts-and-nginx/). | `true` |
-| `default['firezone']['nginx']['hsts_header']['include_subdomains']` | Enable or disable `includeSubDomains` for the HSTS header. | `true` |
-| `default['firezone']['nginx']['hsts_header']['max_age']` | Max age for the HSTS header. | `31536000` |
-| `default['firezone']['nginx']['redirect_to_canonical']` | Whether to redirect URLs to the canonical FQDN specified above | `false` |
-| `default['firezone']['nginx']['cache']['enabled']` | Enable or disable the Firezone nginx cache. | `false` |
-| `default['firezone']['nginx']['cache']['directory']` | Directory for Firezone nginx cache. | `"#{node['firezone']['var_directory']}/nginx/cache"` |
-| `default['firezone']['nginx']['user']` | Firezone nginx user. | `node['firezone']['user']` |
-| `default['firezone']['nginx']['group']` | Firezone nginx group. | `node['firezone']['group']` |
-| `default['firezone']['nginx']['dir']` | Top-level nginx configuration directory. | `node['firezone']['nginx']['directory']` |
-| `default['firezone']['nginx']['log_dir']` | Top-level nginx log directory. | `node['firezone']['nginx']['log_directory']` |
-| `default['firezone']['nginx']['pid']` | Location for nginx pid file. | `"#{node['firezone']['nginx']['directory']}/nginx.pid"` |
-| `default['firezone']['nginx']['daemon_disable']` | Disable nginx daemon mode so we can monitor it instead. | `true` |
-| `default['firezone']['nginx']['gzip']` | Turn nginx gzip compression on or off. | `'on'` |
-| `default['firezone']['nginx']['gzip_static']` | Turn nginx gzip compression on or off for static files. | `'off'` |
-| `default['firezone']['nginx']['gzip_http_version']` | HTTP version to use for serving static files. | `'1.0'` |
-| `default['firezone']['nginx']['gzip_comp_level']` | nginx gzip compression level. | `'2'` |
-| `default['firezone']['nginx']['gzip_proxied']` | Enables or disables gzipping of responses for proxied requests depending on the request and response. | `'any'` |
-| `default['firezone']['nginx']['gzip_vary']` | Enables or disables inserting the “Vary: Accept-Encoding” response header. | `'off'` |
-| `default['firezone']['nginx']['gzip_buffers']` | Sets the number and size of buffers used to compress a response. If `nil`, nginx default is used. | `nil` |
-| `default['firezone']['nginx']['gzip_types']` | MIME types to enable gzip compression for. | `['text/plain', 'text/css','application/x-javascript', 'text/xml', 'application/xml', 'application/rss+xml', 'application/atom+xml', 'text/javascript', 'application/javascript', 'application/json']` |
-| `default['firezone']['nginx']['gzip_min_length']` | Minimum file length to enable file gzip compression for. | `1000` |
-| `default['firezone']['nginx']['gzip_disable']` | User-agent matcher to disable gzip compression for. | `'MSIE [1-6]\.'` |
-| `default['firezone']['nginx']['keepalive']` | Activates cache for connection to upstream servers. | `'on'` |
-| `default['firezone']['nginx']['keepalive_timeout']` | Timeout in seconds for keepalive connection to upstream servers. | `65` |
-| `default['firezone']['nginx']['worker_processes']` | Number of nginx worker processes. | `node['cpu'] && node['cpu']['total'] ? node['cpu']['total'] : 1` |
-| `default['firezone']['nginx']['worker_connections']` | Max number of simultaneous connections that can be opened by a worker process. | `1024` |
-| `default['firezone']['nginx']['worker_rlimit_nofile']` | Changes the limit on the maximum number of open files for worker processes. Uses nginx default if nil. | `nil` |
-| `default['firezone']['nginx']['multi_accept']` | Whether workers should accept one connection at a time or multiple. | `true` |
-| `default['firezone']['nginx']['event']` | Specifies the connection processing method to use inside nginx events context. | `'epoll'` |
-| `default['firezone']['nginx']['server_tokens']` | Enables or disables emitting nginx version on error pages and in the “Server” response header field. | `nil` |
-| `default['firezone']['nginx']['server_names_hash_bucket_size']` | Sets the bucket size for the server names hash tables. | `64` |
-| `default['firezone']['nginx']['sendfile']` | Enables or disables the use of nginx's `sendfile()`. | `'on'` |
-| `default['firezone']['nginx']['access_log_options']` | Sets nginx access log options. | `nil` |
-| `default['firezone']['nginx']['error_log_options']` | Sets nginx error log options. | `nil` |
-| `default['firezone']['nginx']['disable_access_log']` | Disables nginx access log. | `false` |
-| `default['firezone']['nginx']['types_hash_max_size']` | nginx types hash max size. | `2048` |
-| `default['firezone']['nginx']['types_hash_bucket_size']` | nginx types hash bucket size. | `64` |
-| `default['firezone']['nginx']['proxy_read_timeout']` | nginx proxy read timeout. Set to `nil` to use nginx default. | `nil` |
-| `default['firezone']['nginx']['client_body_buffer_size']` | nginx client body buffer size. Set to `nil` to use nginx default. | `nil` |
-| `default['firezone']['nginx']['client_max_body_size']` | nginx client max body size. | `'250m'` |
-| `default['firezone']['nginx']['default']['modules']` | Specify additional nginx modules. | `[]` |
-| `default['firezone']['nginx']['enable_rate_limiting']` | Enable or disable nginx rate limiting. | `true` |
-| `default['firezone']['nginx']['rate_limiting_zone_name']` | Nginx rate limiting zone name. | `'firezone'` |
-| `default['firezone']['nginx']['rate_limiting_backoff']` | Nginx rate limiting backoff. | `'10m'` |
-| `default['firezone']['nginx']['rate_limit']` | Nginx rate limit. | `'10r/s'` |
-| `default['firezone']['nginx']['ipv6']` | Allow nginx to listen for HTTP requests for IPv6 in addition to IPv4. | `true` |
-| `default['firezone']['postgresql']['enabled']` | Enable or disable bundled Postgresql. Set to `false` and fill in the `database` options below to use your own Postgresql instance. | `true` |
-| `default['firezone']['postgresql']['username']` | Username for Postgresql. | `node['firezone']['user']` |
-| `default['firezone']['postgresql']['data_directory']` | Postgresql data directory. | `"#{node['firezone']['var_directory']}/postgresql/13.3/data"` |
-| `default['firezone']['postgresql']['log_directory']` | Postgresql log directory. | `"#{node['firezone']['log_directory']}/postgresql"` |
-| `default['firezone']['postgresql']['log_rotation']['file_maxbytes']` | Postgresql log file maximum size before it's rotated. | `104857600` |
-| `default['firezone']['postgresql']['log_rotation']['num_to_keep']` | Number of Postgresql log files to keep. | `10` |
-| `default['firezone']['postgresql']['checkpoint_completion_target']` | Postgresql checkpoint completion target. | `0.5` |
-| `default['firezone']['postgresql']['checkpoint_segments']` | Number of Postgresql checkpoint segments. | `3` |
-| `default['firezone']['postgresql']['checkpoint_timeout']` | Postgresql checkpoint timeout. | `'5min'` |
-| `default['firezone']['postgresql']['checkpoint_warning']` | Postgresql checkpoint warning time in seconds. | `'30s'` |
-| `default['firezone']['postgresql']['effective_cache_size']` | Postgresql effective cache size. | `'128MB'` |
-| `default['firezone']['postgresql']['listen_address']` | Postgresql listen address. | `'127.0.0.1'` |
-| `default['firezone']['postgresql']['max_connections']` | Postgresql max connections. | `350` |
-| `default['firezone']['postgresql']['md5_auth_cidr_addresses']` | Postgresql CIDRs to allow for md5 auth. | `['127.0.0.1/32', '::1/128']` |
-| `default['firezone']['postgresql']['port']` | Postgresql listen port. | `15432` |
-| `default['firezone']['postgresql']['shared_buffers']` | Postgresql shared buffers size. | `"#{(node['memory']['total'].to_i / 4) / 1024}MB"` |
-| `default['firezone']['postgresql']['shmmax']` | Postgresql shmmax in bytes. | `17179869184` |
-| `default['firezone']['postgresql']['shmall']` | Postgresql shmall in bytes. | `4194304` |
-| `default['firezone']['postgresql']['work_mem']` | Postgresql working memory size. | `'8MB'` |
-| `default['firezone']['database']['user']` | Specifies the username Firezone will use to connect to the DB. | `node['firezone']['postgresql']['username']` |
-| `default['firezone']['database']['password']` | If using an external DB, specifies the password Firezone will use to connect to the DB. | `'change_me'` |
-| `default['firezone']['database']['name']` | Database that Firezone will use. Will be created if it doesn't exist. | `'firezone'` |
-| `default['firezone']['database']['host']` | Database host that Firezone will connect to. | `node['firezone']['postgresql']['listen_address']` |
-| `default['firezone']['database']['port']` | Database port that Firezone will connect to. | `node['firezone']['postgresql']['port']` |
-| `default['firezone']['database']['pool']` | Database pool size Firezone will use. | `[10, Etc.nprocessors].max` |
-| `default['firezone']['database']['ssl']` | Whether to connect to the database over SSL. | `false` |
-| `default['firezone']['database']['ssl_opts']` | Hash of options to send to the `:ssl_opts` option when connecting over SSL. See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options). | `{}` |
-| `default['firezone']['database']['parameters']` | Hash of parameters to send to the `:parameters` option when connecting to the database. See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options). | `{}` |
-| `default['firezone']['database']['extensions']` | Database extensions to enable. | `{ 'plpgsql' => true, 'pg_trgm' => true }` |
-| `default['firezone']['phoenix']['enabled']` | Enable or disable the Firezone web application. | `true` |
-| `default['firezone']['phoenix']['listen_address']` | Firezone web application listen address. This will be the upstream listen address that nginx proxies. | `'127.0.0.1'` |
-| `default['firezone']['phoenix']['port']` | Firezone web application listen port. This will be the upstream port that nginx proxies. | `13000` |
-| `default['firezone']['phoenix']['log_directory']` | Firezone web application log directory. | `"#{node['firezone']['log_directory']}/phoenix"` |
-| `default['firezone']['phoenix']['log_rotation']['file_maxbytes']` | Firezone web application log file size. | `104857600` |
-| `default['firezone']['phoenix']['log_rotation']['num_to_keep']` | Number of Firezone web application log files to keep. | `10` |
-| `default['firezone']['phoenix']['crash_detection']['enabled']` | Enable or disable bringing down the Firezone web application when a crash is detected. | `true` |
-| `default['firezone']['phoenix']['external_trusted_proxies']` | List of trusted reverse proxies formatted as an Array of IPs and/or CIDRs. | `[]` |
-| `default['firezone']['phoenix']['private_clients']` | List of private network HTTP clients, formatted an Array of IPs and/or CIDRs. | `[]` |
-| `default['firezone']['wireguard']['enabled']` | Enable or disable bundled WireGuard management. | `true` |
-| `default['firezone']['wireguard']['log_directory']` | Log directory for bundled WireGuard management. | `"#{node['firezone']['log_directory']}/wireguard"` |
-| `default['firezone']['wireguard']['log_rotation']['file_maxbytes']` | WireGuard log file max size. | `104857600` |
-| `default['firezone']['wireguard']['log_rotation']['num_to_keep']` | Number of WireGuard log files to keep. | `10` |
-| `default['firezone']['wireguard']['interface_name']` | WireGuard interface name. **Changing this parameter may cause a temporary loss in VPN connectivity**. | `'wg-firezone'` |
-| `default['firezone']['wireguard']['port']` | WireGuard listen port. | `51820` |
-| `default['firezone']['wireguard']['persistent_keepalive']` | Default PersistentKeepalive setting for generated device configurations. A value of 0 disables. | `0` |
-| `default['firezone']['wireguard']['ipv4']['enabled']` | Enable or disable IPv4 for WireGuard network. | `true` |
-| `default['firezone']['wireguard']['ipv4']['masquerade']` | Enable or disable masquerade for packets leaving the IPv4 tunnel. | `true` |
-| `default['firezone']['wireguard']['ipv4']['network']` | WireGuard network IPv4 address pool. | `'10.3.2.0/24'` |
-| `default['firezone']['wireguard']['ipv4']['address']` | WireGuard interface IPv4 address. Must be within WireGuard address pool. | `'10.3.2.1'` |
-| `default['firezone']['wireguard']['ipv6']['enabled']` | Enable or disable IPv6 for WireGuard network. | `true` |
-| `default['firezone']['wireguard']['ipv6']['masquerade']` | Enable or disable masquerade for packets leaving the IPv6 tunnel. | `true` |
-| `default['firezone']['wireguard']['ipv6']['network']` | WireGuard network IPv6 address pool. | `'fd00::3:2:0/120'` |
-| `default['firezone']['wireguard']['ipv6']['address']` | WireGuard interface IPv6 address. Must be within IPv6 address pool. | `'fd00::3:2:1'` |
-| `default['firezone']['runit']['svlogd_bin']` | Runit svlogd bin location. | `"#{node['firezone']['install_directory']}/embedded/bin/svlogd"` |
-| `default['firezone']['ssl']['directory']` | SSL directory for storing generated certs. | `'/var/opt/firezone/ssl'` |
-| `default['firezone']['ssl']['email_address']` | Email address to use for self-signed certs and ACME protocol renewal notices. | `'you@example.com'` |
-| `default['firezone']['ssl']['acme']['enabled']` | Enable ACME for automatic SSL cert provisioning. | `false` |
-| `default['firezone']['ssl']['acme']['server']` | ACME server to use for certificate issuance/renewal. Can be any [valid acme.sh server](https://github.com/acmesh-official/acme.sh/wiki/Server) | `letsencrypt` |
-| `default['firezone']['ssl']['acme']['keylength']` | Specify the key type and length for SSL certificates. See [here](https://github.com/acmesh-official/acme.sh#10-issue-ecc-certificates) | `ec-256` |
-| `default['firezone']['ssl']['certificate']` | Path to the certificate file for your FQDN. Overrides ACME setting above if specified. If both ACME and this are `nil` a self-signed cert will be generated. | `nil` |
-| `default['firezone']['ssl']['certificate_key']` | Path to the certificate file. | `nil` |
-| `default['firezone']['ssl']['ssl_dhparam']` | nginx ssl dh_param. | `nil` |
-| `default['firezone']['ssl']['country_name']` | Country name for self-signed cert. | `'US'` |
-| `default['firezone']['ssl']['state_name']` | State name for self-signed cert. | `'CA'` |
-| `default['firezone']['ssl']['locality_name']` | Locality name for self-signed cert. | `'San Francisco'` |
-| `default['firezone']['ssl']['company_name']` | Company name self-signed cert. | `'My Company'` |
-| `default['firezone']['ssl']['organizational_unit_name']` | Organizational unit name for self-signed cert. | `'Operations'` |
-| `default['firezone']['ssl']['ciphers']` | SSL ciphers for nginx to use. | `'ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA:AES256-SHA:AES:CAMELLIA:DES-CBC3-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!aECDH:!EDH-DSS-DES-CBC3-SHA:!EDH-RSA-DES-CBC3-SHA:!KRB5-DES-CBC3-SHA'` |
-| `default['firezone']['ssl']['fips_ciphers']` | SSL ciphers for FIPs mode. | `'FIPS@STRENGTH:!aNULL:!eNULL'` |
-| `default['firezone']['ssl']['protocols']` | TLS protocols to use. | `'TLSv1 TLSv1.1 TLSv1.2'` |
-| `default['firezone']['ssl']['session_cache']` | SSL session cache. | `'shared:SSL:4m'` |
-| `default['firezone']['ssl']['session_timeout']` | SSL session timeout. | `'5m'` |
-| `default['firezone']['robots_allow']` | nginx robots allow. | `'/'` |
-| `default['firezone']['robots_disallow']` | nginx robots disallow. | `nil` |
-| `default['firezone']['outbound_email']['from']` | Outbound email from address. | `nil` |
-| `default['firezone']['outbound_email']['provider']` | Outbound email service provider. | `nil` |
-| `default['firezone']['outbound_email']['configs']` | Outbound email provider configs. | see `omnibus/cookbooks/firezone/attributes/default.rb` |
-| `default['firezone']['telemetry']['enabled']` | Enable or disable anonymized product telemetry. | `true` |
-| `default['firezone']['connectivity_checks']['enabled']` | Enable or disable the Firezone connectivity checks service. | `true` |
-| `default['firezone']['connectivity_checks']['interval']` | Interval between connectivity checks in seconds. | `3_600` |
-
-
-
diff --git a/www/docs/reference/env-vars.mdx b/www/docs/reference/env-vars.mdx
deleted file mode 100644
index 981e0debb..000000000
--- a/www/docs/reference/env-vars.mdx
+++ /dev/null
@@ -1,147 +0,0 @@
----
-title: Environment Variables
-sidebar_position: 1
----
-
-Most day-to-day config of Firezone can be done via the Firezone Web UI,
-but for zero-touch deployments we allow to override most of configuration options
-using environment variables.
-
-Read more about configuring Firezone in our [configure guide](/docs/deploy/configure).
-
-## Errors
-
-Firezone will not boot if the configuration is invalid, providing a detailed error message
-and a link to the documentation for the configuration key with samples how to set it.
-
-## Naming
-
-If environment variables are used, the configuration key must be in uppercase.
-The database variables are the same as the configuration keys.
-
-## Precedence
-
-The configuration precedence is as follows:
-
-1. Environment variables
-2. Database values
-3. Default values
-
-It means that if environment variable is set, it will be used, regardless of the database value,
-and UI to edit database value will be disabled.
-
-## Environment Variable Listing
-
-We recommend setting these in your Docker ENV file (`$HOME/.firezone/.env` by
-default). Required fields in **bold**.
-
-### WebServer
-
-| Env Key | Description | Format | Default |
-| -------------------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ----------------- | ------- |
-| **EXTERNAL_URL** | The external URL the web UI will be accessible at.
Must be a valid and public FQDN for ACME SSL issuance to function.
You can add a path suffix if you want to serve firezone from a non-root path, eg: `https://firezone.mycorp.com/vpn/`. | string | |
-| PHOENIX_SECURE_COOKIES | Enable or disable requiring secure cookies. Required for HTTPS. | boolean | true |
-| PHOENIX_HTTP_PORT | Internal port to listen on for the Phoenix web server. | integer | 13000 |
-| PHOENIX_HTTP_PROTOCOL_OPTIONS | Allows to override Cowboy HTTP server options.
Keep in mind though changing those limits can pose a security risk. Other times, browsers and proxies along the way may have equally strict limits, which means the request will still fail or the URL will be pruned.
You can see all supported options at https://ninenines.eu/docs/en/cowboy/2.5/manual/cowboy_http/. | JSON-encoded map | `{}` |
-| PHOENIX_EXTERNAL_TRUSTED_PROXIES | List of trusted reverse proxies.
This is used to determine the correct IP address of the client when the application is behind a reverse proxy by skipping a trusted proxy IP from a list of possible source IPs. | JSON-encoded list | `"[]"` |
-| PHOENIX_PRIVATE_CLIENTS | List of trusted clients.
This is used to determine the correct IP address of the client when the application is behind a reverse proxy by picking a trusted client IP from a list of possible source IPs. | JSON-encoded list | `"[]"` |
-
-### Database
-
-| Env Key | Description | Format | Default |
-| -------------------- | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ---------------- | --------- |
-| DATABASE_HOST | PostgreSQL host. | string | postgres |
-| DATABASE_PORT | PostgreSQL port. | integer | 5432 |
-| DATABASE_NAME | Name of the PostgreSQL database. | string | firezone |
-| DATABASE_USER | User that will be used to access the PostgreSQL database. | string | postgres |
-| DATABASE_PASSWORD | Password that will be used to access the PostgreSQL database. | string | |
-| DATABASE_POOL_SIZE | Size of the connection pool to the PostgreSQL database. | integer | generated |
-| DATABASE_SSL_ENABLED | Whether to connect to the database over SSL.
If this field is set to `true`, the `database_ssl_opts` config must be set too with at least `cacertfile` option present. | boolean | false |
-| DATABASE_SSL_OPTS | SSL options for connecting to the PostgreSQL database.
Typically, to enabled SSL you want following options:
- `cacertfile` - path to the CA certificate file;
- `verify` - set to `verify_peer` to verify the server certificate;
- `fail_if_no_peer_cert` - set to `true` to require the server to present a certificate;
- `server_name_indication` - specify the hostname to be used in TLS Server Name Indication extension.
See [Ecto.Adapters.Postgres documentation](https://hexdocs.pm/ecto_sql/Ecto.Adapters.Postgres.html#module-connection-options). For list of all supported options, see the [`ssl`](http://erlang.org/doc/man/ssl.html#type-tls_client_option) module documentation. | JSON-encoded map | `{}` |
-
-### Admin Setup
-
-Options responsible for initial admin provisioning and resetting the admin password.
-
-For more details see [troubleshooting guide](/docs/administer/troubleshoot/#admin-login-isnt-working).
-
-| Env Key | Description | Format | Default |
-| ---------------------- | --------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ------- | ------- |
-| RESET_ADMIN_ON_BOOT | Set this variable to `true` to create or reset the admin password every time Firezone starts. By default, the admin password is only set when Firezone is installed.
Note: This **will not** change the status of local authentication. | boolean | false |
-| DEFAULT_ADMIN_EMAIL | Primary administrator email. | string | |
-| DEFAULT_ADMIN_PASSWORD | Default password that will be used for creating or resetting the primary administrator account. | string | |
-
-### Secrets and Encryption
-
-Your secrets should be generated during installation automatically and persisted to `.env` file.
-
-All secrets should be a **base64-encoded string**.
-
-| Env Key | Description | Format | Default |
-| --------------------------- | ------------------------------------------------------------------ | ------ | ------- |
-| **GUARDIAN_SECRET_KEY** | Secret key used for signing JWTs. | string | |
-| **DATABASE_ENCRYPTION_KEY** | Secret key used for encrypting sensitive data in the database. | string | |
-| **SECRET_KEY_BASE** | Primary secret key base for the Phoenix application. | string | |
-| **LIVE_VIEW_SIGNING_SALT** | Signing salt for Phoenix LiveView connection tokens. | string | |
-| **COOKIE_SIGNING_SALT** | Signing salt for cookies issued by the Phoenix web application. | string | |
-| **COOKIE_ENCRYPTION_SALT** | Encryption salt for cookies issued by the Phoenix web application. | string | |
-
-### Devices
-
-| Env Key | Description | Format | Default |
-| --------------------------------------- | -------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | --------------------------------------------------------------------------------------- | ----------------- |
-| ALLOW_UNPRIVILEGED_DEVICE_MANAGEMENT | Enable or disable management of devices on unprivileged accounts. | boolean | true |
-| ALLOW_UNPRIVILEGED_DEVICE_CONFIGURATION | Enable or disable configuration of device network settings for unprivileged users. | boolean | true |
-| VPN_SESSION_DURATION | Optionally require users to periodically authenticate to the Firezone web UI in order to keep their VPN sessions active. | integer | 0 |
-| DEFAULT_CLIENT_PERSISTENT_KEEPALIVE | Interval for WireGuard [persistent keepalive](https://www.wireguard.com/quickstart/#nat-and-firewall-traversal-persistence).
If you experience NAT or firewall traversal problems, you can enable this to send a keepalive packet every 25 seconds. Otherwise, keep it disabled with a 0 default value. | integer | 25 |
-| DEFAULT_CLIENT_MTU | WireGuard interface MTU for devices. 1280 is a safe bet for most networks. Leave this blank to omit this field from generated configs. | integer | 1280 |
-| DEFAULT_CLIENT_ENDPOINT | IPv4, IPv6 address, or FQDN that devices will be configured to connect to. Defaults to this server's FQDN. | one of `IP with port`, `string` | generated |
-| DEFAULT_CLIENT_DNS | Comma-separated list of DNS servers to use for devices.
It can be either an IP address or a FQDN if you intend to use a DNS-over-TLS server.
Leave this blank to omit the `DNS` section from generated configs. | {:array, ",", {:one_of, [Domain.Types.IP, :string]}, [validate_unique: true]} | `[]` |
-| DEFAULT_CLIENT_ALLOWED_IPS | Configures the default AllowedIPs setting for devices.
AllowedIPs determines which destination IPs get routed through Firezone.
Specify a comma-separated list of IPs or CIDRs here to achieve split tunneling, or use `0.0.0.0/0, ::/0` to route all device traffic through this Firezone server. | {:array, ",", {:one_of, [Domain.Types.CIDR, Domain.Types.IP]}, [validate_unique: true]} | `0.0.0.0/0, ::/0` |
-
-### Authorization
-
-| Env Key | Description | Format | Default |
-| ------------------------- | ---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ----------------- | ----------------------------- |
-| LOCAL_AUTH_ENABLED | Enable or disable the local authentication method for all users. | boolean | true |
-| DISABLE_VPN_ON_OIDC_ERROR | Enable or disable auto disabling VPN connection on OIDC refresh error. | boolean | false |
-| SAML_ENTITY_ID | Entity ID for SAML authentication. | string | urn:firezone.dev:firezone-app |
-| SAML_KEYFILE_PATH | Path to the SAML keyfile inside the container. Should be either a PEM or DER-encoded private key, with file extension `.pem` or `.key`. | string | /var/firezone/saml.key |
-| SAML_CERTFILE_PATH | Path to the SAML certificate file inside the container. Should be either a PEM or DER-encoded certificate, with file extension `.crt` or `.pem`. | string | /var/firezone/saml.crt |
-| OPENID_CONNECT_PROVIDERS | List of OpenID Connect identity providers configurations.
For example:
`[ { "auto_create_users": false, "id": "google", "label": "google", "client_id": "test-id", "client_secret": "test-secret", "discovery_document_uri": "https://accounts.google.com/.well-known/openid-configuration", "redirect_uri": "https://invalid", "response_type": "response-type", "scope": "oauth email profile" } ]`
For more details see https://docs.firezone.dev/authenticate/oidc/. | JSON-encoded list | `"[]"` |
-| SAML_IDENTITY_PROVIDERS | List of SAML identity providers configurations.
For example:
`[ { "auto_create_users": false, "base_url": "https://saml", "id": "okta", "label": "okta", "metadata": "...", "sign_metadata": false, "sign_requests": false, "signed_assertion_in_resp": false, "signed_envelopes_in_resp": false } ]`
For more details see https://docs.firezone.dev/authenticate/saml/. | JSON-encoded list | `"[]"` |
-
-### WireGuard
-
-| Env Key | Description | Format | Default |
-| ---------------------- | --------------------------------------------------------------- | ------- | ------- |
-| WIREGUARD_PORT | A port on which WireGuard will listen for incoming connections. | integer | 51820 |
-| WIREGUARD_IPV4_ENABLED | Enable or disable IPv4 support for WireGuard. | boolean | true |
-| WIREGUARD_IPV6_ENABLED | Enable or disable IPv6 support for WireGuard. | boolean | true |
-
-### Outbound Emails
-
-| Env Key | Description | Format | Default |
-| --------------------------- | ------------------------------------------------------------------------------------------------------------ | ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- | ------------------------------- |
-| OUTBOUND_EMAIL_FROM | From address to use for sending outbound emails. If not set, sending email will be disabled (default). | string | generated |
-| OUTBOUND_EMAIL_ADAPTER | Method to use for sending outbound email. | One of `Elixir.Swoosh.Adapters.AmazonSES`, `Elixir.Swoosh.Adapters.CustomerIO`, `Elixir.Swoosh.Adapters.Dyn`, `Elixir.Swoosh.Adapters.ExAwsAmazonSES`, `Elixir.Swoosh.Adapters.Gmail`, `Elixir.Swoosh.Adapters.MailPace`, `Elixir.Swoosh.Adapters.Mailgun`, `Elixir.Swoosh.Adapters.Mailjet`, `Elixir.Swoosh.Adapters.Mandrill`, `Elixir.Swoosh.Adapters.Postmark`, `Elixir.Swoosh.Adapters.ProtonBridge`, `Elixir.Swoosh.Adapters.SMTP`, `Elixir.Swoosh.Adapters.SMTP2GO`, `Elixir.Swoosh.Adapters.Sendgrid`, `Elixir.Swoosh.Adapters.Sendinblue`, `Elixir.Swoosh.Adapters.Sendmail`, `Elixir.Swoosh.Adapters.SocketLabs`, `Elixir.Swoosh.Adapters.SparkPost`, `Elixir.Web.Mailer.NoopAdapter` | `Elixir.Web.Mailer.NoopAdapter` |
-| OUTBOUND_EMAIL_ADAPTER_OPTS | Adapter configuration, for list of options see [Swoosh Adapters](https://github.com/swoosh/swoosh#adapters). | JSON-encoded map | `{}` |
-
-### Connectivity Checks
-
-| Env Key | Description | Format | Default |
-| ---------------------------- | ------------------------------------------------------------------------------------------------------------------------------ | ------- | ------- |
-| CONNECTIVITY_CHECKS_ENABLED | Enable / disable periodic checking for egress connectivity. Determines the instance's public IP to populate `Endpoint` fields. | boolean | true |
-| CONNECTIVITY_CHECKS_INTERVAL | Periodicity in seconds to check for egress connectivity. | integer | 43200 |
-
-### Telemetry
-
-| Env Key | Description | Format | Default |
-| ----------------- | ------------------------------------------------------------------------------------------------------------------------------------- | ------- | ------- |
-| TELEMETRY_ENABLED | Enable or disable the Firezone telemetry collection.
For more details see https://docs.firezone.dev/reference/telemetry/. | boolean | true |
-
-### Other
-
-| Env Key | Description | Format | Default |
-| ------- | --------------------------------------------------------------- | ---------------------------- | ------- |
-| LOGO | The path to a logo image file to replace default Firezone logo. | {:embed, Domain.Config.Logo} | `` |
diff --git a/www/docs/reference/file-and-directory-locations.mdx b/www/docs/reference/file-and-directory-locations.mdx
deleted file mode 100644
index f830a4f19..000000000
--- a/www/docs/reference/file-and-directory-locations.mdx
+++ /dev/null
@@ -1,37 +0,0 @@
----
-title: File and Directory Locations
-sidebar_position: 3
----
-
-Here you'll find a listing of files and directories related to a typical
-Firezone installation. These can change depending on how you've configured
-your installation.
-
-
-
-
-| Default path | Description |
-| ----------------------------------------------------------------------------------------------------------- | ------------------------------------------------------------------------------------------------------------------------- |
-| `$HOME/.firezone/.env` | Firezone secrets used for encryption, cookies, and sessions. **Losing this file will result in irrecoverable data loss**. |
-| `$HOME/.firezone/docker-compose.yml` | Docker Compose file used to manage Firezone services. |
-| `$HOME/.firezone/firezone` | Top-level directory containing Firezone-related persisted data |
-| `$HOME/.firezone/caddy` | Caddy persisted files. |
-| Default Docker named volume location, typically `/var/lib/docker/volumes/firezone_postgres-data` for Linux. | Postgres DB files. |
-
-
-
-
-| Path | Description |
-| ----------------------------------------------------- | ---------------------------------------------------------------------------------------------- |
-| `/var/opt/firezone` | Top-level directory containing data and generated configuration for Firezone bundled services. |
-| `/opt/firezone` | Top-level directory containing built libraries, binaries and runtime files needed by Firezone. |
-| `/usr/bin/firezone-ctl` | `firezone-ctl` utility for managing your Firezone installation. |
-| `/etc/systemd/system/firezone-runsvdir-start.service` | systemd unit file for starting the Firezone runsvdir supervisor process. |
-| `/etc/firezone` | Firezone configuration files. |
-
-
-
-
-## Backup and restore
-
-See our [backup guide](/docs/administer/backup).
diff --git a/www/docs/reference/firewall-templates/README.mdx b/www/docs/reference/firewall-templates/README.mdx
deleted file mode 100644
index aa9612fff..000000000
--- a/www/docs/reference/firewall-templates/README.mdx
+++ /dev/null
@@ -1,15 +0,0 @@
----
-title: Firewall Templates
-sidebar_position: 9
----
-
-Firewall templates to secure the Firezone server itself are available from here.
-If the server is not running any services other than Firezone, the firewall
-template should work as-is.
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/reference/firewall-templates/nftables.mdx b/www/docs/reference/firewall-templates/nftables.mdx
deleted file mode 100644
index 7cf17dc57..000000000
--- a/www/docs/reference/firewall-templates/nftables.mdx
+++ /dev/null
@@ -1,339 +0,0 @@
----
-title: nftables Firewall Template
-sidebar_position: 1
----
-
-The following nftables firewall template can be used to secure the server
-running Firezone. The template does make some assumptions; you may need to
-adjust the rules to suit your use case:
-
-* The WireGuard interface is named `wg-firezone`. If this is not correct,
-change the `DEV_WIREGUARD` variable to match the
-`default['firezone']['wireguard']['interface_name']` configuration option.
-* The port WireGuard is listening on is `51820`. If you are not using the
-default port change the `WIREGUARD_PORT` variable.
-* Only the following inbound traffic will be allowed to the server:
- * SSH (TCP dport 22)
- * HTTP (TCP dport 80)
- * HTTPS (TCP dport 443)
- * WireGuard (UDP dport `WIREGUARD_PORT`)
- * UDP traceroute (UDP dport 33434-33524, rate limited to 500/second)
- * ICMP and ICMPv6 (ping/ping responses rate limited to 2000/second)
-* Only the following outbound traffic will be allowed from the server:
- * DNS (UDP and TCP dport 53)
- * HTTP (TCP dport 80)
- * NTP (UDP port 123)
- * HTTPS (TCP dport 443)
- * SMTP submission (TCP dport 587)
- * UDP traceroute (UDP dport 33434-33524, rate limited to 500/second)
-* Unmatched traffic will be logged. The rules used for logging are separated
-from the rules to drop traffic and are rate limited. Removing the relevant
-logging rules will not affect traffic.
-
-## Firezone-managed rules
-
-Firezone configures its own nftables rules to permit/reject traffic to destinations
-configured in the web interface and to handle outbound NAT for client traffic.
-
-Applying the below firewall template on an already running server (not at boot time)
-will result in the Firezone rules being cleared. This may have security implications.
-
-To work around this restart the `phoenix` service:
-
-```shell
-firezone-ctl restart phoenix
-```
-
-## Base firewall template
-
-```shell
-#!/usr/sbin/nft -f
-
-## Clear/flush all existing rules
-flush ruleset
-
-################################ VARIABLES ################################
-## Internet/WAN interface name
-define DEV_WAN = eth0
-
-## WireGuard interface name
-define DEV_WIREGUARD = wg-firezone
-
-## WireGuard listen port
-define WIREGUARD_PORT = 51820
-############################## VARIABLES END ##############################
-
-# Main inet family filtering table
-table inet filter {
-
- # Rules for forwarded traffic
- # This chain is processed before the Firezone forward chain
- chain forward {
- type filter hook forward priority filter - 5; policy accept
- }
-
- # Rules for input traffic
- chain input {
- type filter hook input priority filter; policy drop
-
- ## Permit inbound traffic to loopback interface
- iif lo \
- accept \
- comment "Permit all traffic in from loopback interface"
-
- ## Permit established and related connections
- ct state established,related \
- accept \
- comment "Permit established/related connections"
-
- ## Permit inbound WireGuard traffic
- iif $DEV_WAN udp dport $WIREGUARD_PORT \
- counter \
- accept \
- comment "Permit inbound WireGuard traffic"
-
- ## Log and drop new TCP non-SYN packets
- tcp flags != syn ct state new \
- limit rate 100/minute burst 150 packets \
- log prefix "IN - New !SYN: " \
- comment "Rate limit logging for new connections that do not have the SYN TCP flag set"
- tcp flags != syn ct state new \
- counter \
- drop \
- comment "Drop new connections that do not have the SYN TCP flag set"
-
- ## Log and drop TCP packets with invalid fin/syn flag set
- tcp flags & (fin|syn) == (fin|syn) \
- limit rate 100/minute burst 150 packets \
- log prefix "IN - TCP FIN|SIN: " \
- comment "Rate limit logging for TCP packets with invalid fin/syn flag set"
- tcp flags & (fin|syn) == (fin|syn) \
- counter \
- drop \
- comment "Drop TCP packets with invalid fin/syn flag set"
-
- ## Log and drop TCP packets with invalid syn/rst flag set
- tcp flags & (syn|rst) == (syn|rst) \
- limit rate 100/minute burst 150 packets \
- log prefix "IN - TCP SYN|RST: " \
- comment "Rate limit logging for TCP packets with invalid syn/rst flag set"
- tcp flags & (syn|rst) == (syn|rst) \
- counter \
- drop \
- comment "Drop TCP packets with invalid syn/rst flag set"
-
- ## Log and drop invalid TCP flags
- tcp flags & (fin|syn|rst|psh|ack|urg) < (fin) \
- limit rate 100/minute burst 150 packets \
- log prefix "IN - FIN:" \
- comment "Rate limit logging for invalid TCP flags (fin|syn|rst|psh|ack|urg) < (fin)"
- tcp flags & (fin|syn|rst|psh|ack|urg) < (fin) \
- counter \
- drop \
- comment "Drop TCP packets with flags (fin|syn|rst|psh|ack|urg) < (fin)"
-
- ## Log and drop invalid TCP flags
- tcp flags & (fin|syn|rst|psh|ack|urg) == (fin|psh|urg) \
- limit rate 100/minute burst 150 packets \
- log prefix "IN - FIN|PSH|URG:" \
- comment "Rate limit logging for invalid TCP flags (fin|syn|rst|psh|ack|urg) == (fin|psh|urg)"
- tcp flags & (fin|syn|rst|psh|ack|urg) == (fin|psh|urg) \
- counter \
- drop \
- comment "Drop TCP packets with flags (fin|syn|rst|psh|ack|urg) == (fin|psh|urg)"
-
- ## Drop traffic with invalid connection state
- ct state invalid \
- limit rate 100/minute burst 150 packets \
- log flags all prefix "IN - Invalid: " \
- comment "Rate limit logging for traffic with invalid connection state"
- ct state invalid \
- counter \
- drop \
- comment "Drop traffic with invalid connection state"
-
- ## Permit IPv4 ping/ping responses but rate limit to 2000 PPS
- ip protocol icmp icmp type { echo-reply, echo-request } \
- limit rate 2000/second \
- counter \
- accept \
- comment "Permit inbound IPv4 echo (ping) limited to 2000 PPS"
-
- ## Permit all other inbound IPv4 ICMP
- ip protocol icmp \
- counter \
- accept \
- comment "Permit all other IPv4 ICMP"
-
- ## Permit IPv6 ping/ping responses but rate limit to 2000 PPS
- icmpv6 type { echo-reply, echo-request } \
- limit rate 2000/second \
- counter \
- accept \
- comment "Permit inbound IPv6 echo (ping) limited to 2000 PPS"
-
- ## Permit all other inbound IPv6 ICMP
- meta l4proto { icmpv6 } \
- counter \
- accept \
- comment "Permit all other IPv6 ICMP"
-
- ## Permit inbound traceroute UDP ports but limit to 500 PPS
- udp dport 33434-33524 \
- limit rate 500/second \
- counter \
- accept \
- comment "Permit inbound UDP traceroute limited to 500 PPS"
-
- ## Permit inbound SSH
- tcp dport ssh ct state new \
- counter \
- accept \
- comment "Permit inbound SSH connections"
-
- ## Permit inbound HTTP and HTTPS
- tcp dport { http, https } ct state new \
- counter \
- accept \
- comment "Permit inbound HTTP and HTTPS connections"
-
- ## Log any unmatched traffic but rate limit logging to a maximum of 60 messages/minute
- ## The default policy will be applied to unmatched traffic
- limit rate 60/minute burst 100 packets \
- log prefix "IN - Drop: " \
- comment "Log any unmatched traffic"
-
- ## Count the unmatched traffic
- counter \
- comment "Count any unmatched traffic"
- }
-
- # Rules for output traffic
- chain output {
- type filter hook output priority filter; policy drop
-
- ## Permit outbound traffic to loopback interface
- oif lo \
- accept \
- comment "Permit all traffic out to loopback interface"
-
- ## Permit established and related connections
- ct state established,related \
- counter \
- accept \
- comment "Permit established/related connections"
-
- ## Permit outbound WireGuard traffic before dropping connections with bad state
- oif $DEV_WAN udp sport $WIREGUARD_PORT \
- counter \
- accept \
- comment "Permit WireGuard outbound traffic"
-
- ## Drop traffic with invalid connection state
- ct state invalid \
- limit rate 100/minute burst 150 packets \
- log flags all prefix "OUT - Invalid: " \
- comment "Rate limit logging for traffic with invalid connection state"
- ct state invalid \
- counter \
- drop \
- comment "Drop traffic with invalid connection state"
-
- ## Permit all other outbound IPv4 ICMP
- ip protocol icmp \
- counter \
- accept \
- comment "Permit all IPv4 ICMP types"
-
- ## Permit all other outbound IPv6 ICMP
- meta l4proto { icmpv6 } \
- counter \
- accept \
- comment "Permit all IPv6 ICMP types"
-
- ## Permit outbound traceroute UDP ports but limit to 500 PPS
- udp dport 33434-33524 \
- limit rate 500/second \
- counter \
- accept \
- comment "Permit outbound UDP traceroute limited to 500 PPS"
-
- ## Permit outbound HTTP and HTTPS connections
- tcp dport { http, https } ct state new \
- counter \
- accept \
- comment "Permit outbound HTTP and HTTPS connections"
-
- ## Permit outbound SMTP submission
- tcp dport submission ct state new \
- counter \
- accept \
- comment "Permit outbound SMTP submission"
-
- ## Permit outbound DNS requests
- udp dport 53 \
- counter \
- accept \
- comment "Permit outbound UDP DNS requests"
- tcp dport 53 \
- counter \
- accept \
- comment "Permit outbound TCP DNS requests"
-
- ## Permit outbound NTP requests
- udp dport 123 \
- counter \
- accept \
- comment "Permit outbound NTP requests"
-
- ## Log any unmatched traffic but rate limit logging to a maximum of 60 messages/minute
- ## The default policy will be applied to unmatched traffic
- limit rate 60/minute burst 100 packets \
- log prefix "OUT - Drop: " \
- comment "Log any unmatched traffic"
-
- ## Count the unmatched traffic
- counter \
- comment "Count any unmatched traffic"
- }
-
-}
-
-# Main NAT filtering table
-table inet nat {
-
- # Rules for NAT traffic pre-routing
- chain prerouting {
- type nat hook prerouting priority dstnat; policy accept
- }
-
- # Rules for NAT traffic post-routing
- # This table is processed before the Firezone post-routing chain
- chain postrouting {
- type nat hook postrouting priority srcnat - 5; policy accept
- }
-
-}
-```
-
-## Usage
-
-The firewall should be stored in the relevant location for the Linux distribution
-that is running. For Debian/Ubuntu this is `/etc/nftables.conf` and for RHEL this
-is `/etc/sysconfig/nftables.conf`.
-
-`nftables.service` will need to be configured to start on boot (if not already) set:
-
-```shell
-systemctl enable nftables.service
-```
-
-If making any changes to the firewall template the syntax can be validated by running
-the check command:
-
-```shell
-nft -f /path/to/nftables.conf -c
-```
-
-Be sure to validate the firewall works as expected as certain nftables features may
-not be available depending on the release running on the server.
diff --git a/www/docs/reference/rest-api/README.mdx b/www/docs/reference/rest-api/README.mdx
deleted file mode 100644
index 5a2cd8ce5..000000000
--- a/www/docs/reference/rest-api/README.mdx
+++ /dev/null
@@ -1,35 +0,0 @@
----
-title: REST API
-sidebar_position: 10
----
-
-Welcome to Firezone's REST API v0 documentation.
-
-## Getting started
-
-To get started with the REST API, you'll first need an API token.
-This can be generated in the UI at `/settings/account` or via the CLI
-with:
-
-```shell
-docker compose -f $HOME/.firezone/docker-compose.yml exec firezone bin/create-api-token
-```
-
-**Note**: The token is written to `STDOUT` by default. You may wish to redirect its output
-to a file instead:
-
-```shell
-docker compose -f $HOME/.firezone/docker-compose.yml exec firezone bin/create-api-token > fz_token
-```
-
-:::caution
-API tokens generated from the CLI are owned by the primary administrator specified by
-the `DEFAULT_ADMIN_EMAIL` environment variable.
-:::
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/reference/rest-api/configurations.mdx b/www/docs/reference/rest-api/configurations.mdx
deleted file mode 100644
index 20d7eae87..000000000
--- a/www/docs/reference/rest-api/configurations.mdx
+++ /dev/null
@@ -1,163 +0,0 @@
----
-title: Configurations
-group: Configuration
----
-
-
-This endpoint allows an administrator to manage Configurations.
-
-Updates here can be applied at runtime with little to no downtime of affected services.
-
-## API Documentation
-### GET /v0/configuration
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/configuration" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "allow_unprivileged_device_configuration": true,
- "allow_unprivileged_device_management": true,
- "default_client_allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "default_client_dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "default_client_endpoint": "localhost:51820",
- "default_client_mtu": 1280,
- "default_client_persistent_keepalive": 25,
- "disable_vpn_on_oidc_error": false,
- "id": "c4582e2b-cba3-4a4e-9f05-0f37666c41fe",
- "inserted_at": "2023-03-29T15:10:03.142320Z",
- "local_auth_enabled": true,
- "logo": {},
- "openid_connect_providers": [],
- "saml_identity_providers": [],
- "updated_at": "2023-03-29T15:10:03.142320Z",
- "vpn_session_duration": 0
- }
-}
-```
-### PATCH /v0/configuration
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X PUT "https://{firezone_host}/v0/configuration" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "configuration": {
- "allow_unprivileged_device_configuration": false,
- "allow_unprivileged_device_management": false,
- "default_client_allowed_ips": [
- "1.1.1.1",
- "2.2.2.2"
- ],
- "default_client_dns": [
- "1.1.1.1"
- ],
- "default_client_endpoint": "new-endpoint",
- "default_client_mtu": 1100,
- "default_client_persistent_keepalive": 1,
- "disable_vpn_on_oidc_error": true,
- "local_auth_enabled": false,
- "openid_connect_providers": [
- {
- "auto_create_users": false,
- "client_id": "test-id",
- "client_secret": "test-secret",
- "discovery_document_uri": "https://accounts.google.com/.well-known/openid-configuration",
- "id": "google",
- "label": "google",
- "redirect_uri": "https://invalid",
- "response_type": "code",
- "scope": "email openid"
- }
- ],
- "saml_identity_providers": [
- {
- "auto_create_users": false,
- "base_url": "https://saml",
- "id": "okta",
- "label": "okta",
- "metadata": "\n\n \n \n \n \n MIIDqDCCApCgAwIBAgIGAYMaIfiKMA0GCSqGSIb3DQEBCwUAMIGUMQswCQYDVQQGEwJVUzETMBEG\nA1UECAwKQ2FsaWZvcm5pYTEWMBQGA1UEBwwNU2FuIEZyYW5jaXNjbzENMAsGA1UECgwET2t0YTEU\nMBIGA1UECwwLU1NPUHJvdmlkZXIxFTATBgNVBAMMDGRldi04Mzg1OTk1NTEcMBoGCSqGSIb3DQEJ\nARYNaW5mb0Bva3RhLmNvbTAeFw0yMjA5MDcyMjQ1MTdaFw0zMjA5MDcyMjQ2MTdaMIGUMQswCQYD\nVQQGEwJVUzETMBEGA1UECAwKQ2FsaWZvcm5pYTEWMBQGA1UEBwwNU2FuIEZyYW5jaXNjbzENMAsG\nA1UECgwET2t0YTEUMBIGA1UECwwLU1NPUHJvdmlkZXIxFTATBgNVBAMMDGRldi04Mzg1OTk1NTEc\nMBoGCSqGSIb3DQEJARYNaW5mb0Bva3RhLmNvbTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoC\nggEBAOmj276L3kHm57hNGYTocT6NS4mffPbcvsA2UuKIWfmpV8HLTcmS+NahLtuN841OnRnTn+2p\nfjlwa1mwJhCODbF3dcVYOkGTPUC4y2nvf1Xas6M7+0O2WIfrzdX/OOUs/ROMnB/O/MpBwMR2SQh6\nQ3V+9v8g3K9yfMvcifDbl6g9fTliDzqV7I9xF5eJykl+iCAKNaQgp3cO6TaIa5u2ZKtRAdzwnuJC\nBXMyzaoNs/vfnwzuFtzWP1PSS1Roan+8AMwkYA6BCr1YRIqZ0GSkr/qexFCTZdq0UnSN78fY6CCM\nRFw5wU0WM9nEpbWzkBBWsYHeTLo5JqR/mZukfjlPDlcCAwEAATANBgkqhkiG9w0BAQsFAAOCAQEA\nlUhwzCSnuqt4wlHxJONN4kxUBG8bPnjHxob6jBKK+onFDuSVWZ+7LZw67blz6xdxvlOLaQLi1fK2\nFifehbc7KbRLckcgNgg7Y8qfUKdP0/nS0JlyAvlnICQqaHTHwhIzQqTHtTZeeIJHtpWOX/OPRI0S\nbkygh2qjF8bYn3sX8bGNUQL8iiMxFnvwGrXaErPqlRqFJbWQDBXD+nYDIBw7WN3Jyb0Ydin2zrlh\ngp3Qooi0TnAir3ncw/UF/+sivCgd+6nX7HkbZtipkMbg7ZByyD9xrOQG2JXrP6PyzGCPwnGMt9pL\niiVMepeLNqKZ3UvhrR1uRN0KWu7lduIRhxldLA==\n \n \n \n urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified\n urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress\n \n \n \n\n",
- "sign_metadata": false,
- "sign_requests": false,
- "signed_assertion_in_resp": false,
- "signed_envelopes_in_resp": false
- }
- ],
- "vpn_session_duration": 100
- }
-}'
-EOF
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "allow_unprivileged_device_configuration": false,
- "allow_unprivileged_device_management": false,
- "default_client_allowed_ips": [
- "1.1.1.1",
- "2.2.2.2"
- ],
- "default_client_dns": [
- "1.1.1.1"
- ],
- "default_client_endpoint": "new-endpoint",
- "default_client_mtu": 1100,
- "default_client_persistent_keepalive": 1,
- "disable_vpn_on_oidc_error": true,
- "id": "c4582e2b-cba3-4a4e-9f05-0f37666c41fe",
- "inserted_at": "2023-03-29T15:10:03.142320Z",
- "local_auth_enabled": false,
- "logo": {},
- "openid_connect_providers": [
- {
- "auto_create_users": false,
- "client_id": "test-id",
- "client_secret": "test-secret",
- "discovery_document_uri": "https://accounts.google.com/.well-known/openid-configuration",
- "id": "google",
- "label": "google",
- "redirect_uri": "https://invalid",
- "response_type": "code",
- "scope": "email openid"
- }
- ],
- "saml_identity_providers": [
- {
- "auto_create_users": false,
- "base_url": "https://saml",
- "id": "okta",
- "label": "okta",
- "metadata": "\n\n \n \n \n \n MIIDqDCCApCgAwIBAgIGAYMaIfiKMA0GCSqGSIb3DQEBCwUAMIGUMQswCQYDVQQGEwJVUzETMBEG\nA1UECAwKQ2FsaWZvcm5pYTEWMBQGA1UEBwwNU2FuIEZyYW5jaXNjbzENMAsGA1UECgwET2t0YTEU\nMBIGA1UECwwLU1NPUHJvdmlkZXIxFTATBgNVBAMMDGRldi04Mzg1OTk1NTEcMBoGCSqGSIb3DQEJ\nARYNaW5mb0Bva3RhLmNvbTAeFw0yMjA5MDcyMjQ1MTdaFw0zMjA5MDcyMjQ2MTdaMIGUMQswCQYD\nVQQGEwJVUzETMBEGA1UECAwKQ2FsaWZvcm5pYTEWMBQGA1UEBwwNU2FuIEZyYW5jaXNjbzENMAsG\nA1UECgwET2t0YTEUMBIGA1UECwwLU1NPUHJvdmlkZXIxFTATBgNVBAMMDGRldi04Mzg1OTk1NTEc\nMBoGCSqGSIb3DQEJARYNaW5mb0Bva3RhLmNvbTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoC\nggEBAOmj276L3kHm57hNGYTocT6NS4mffPbcvsA2UuKIWfmpV8HLTcmS+NahLtuN841OnRnTn+2p\nfjlwa1mwJhCODbF3dcVYOkGTPUC4y2nvf1Xas6M7+0O2WIfrzdX/OOUs/ROMnB/O/MpBwMR2SQh6\nQ3V+9v8g3K9yfMvcifDbl6g9fTliDzqV7I9xF5eJykl+iCAKNaQgp3cO6TaIa5u2ZKtRAdzwnuJC\nBXMyzaoNs/vfnwzuFtzWP1PSS1Roan+8AMwkYA6BCr1YRIqZ0GSkr/qexFCTZdq0UnSN78fY6CCM\nRFw5wU0WM9nEpbWzkBBWsYHeTLo5JqR/mZukfjlPDlcCAwEAATANBgkqhkiG9w0BAQsFAAOCAQEA\nlUhwzCSnuqt4wlHxJONN4kxUBG8bPnjHxob6jBKK+onFDuSVWZ+7LZw67blz6xdxvlOLaQLi1fK2\nFifehbc7KbRLckcgNgg7Y8qfUKdP0/nS0JlyAvlnICQqaHTHwhIzQqTHtTZeeIJHtpWOX/OPRI0S\nbkygh2qjF8bYn3sX8bGNUQL8iiMxFnvwGrXaErPqlRqFJbWQDBXD+nYDIBw7WN3Jyb0Ydin2zrlh\ngp3Qooi0TnAir3ncw/UF/+sivCgd+6nX7HkbZtipkMbg7ZByyD9xrOQG2JXrP6PyzGCPwnGMt9pL\niiVMepeLNqKZ3UvhrR1uRN0KWu7lduIRhxldLA==\n \n \n \n urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified\n urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress\n \n \n \n\n",
- "sign_metadata": false,
- "sign_requests": false,
- "signed_assertion_in_resp": false,
- "signed_envelopes_in_resp": false
- }
- ],
- "updated_at": "2023-03-29T15:11:47.879874Z",
- "vpn_session_duration": 100
- }
-}
-```
diff --git a/www/docs/reference/rest-api/devices.mdx b/www/docs/reference/rest-api/devices.mdx
deleted file mode 100644
index 4fdcdf3ac..000000000
--- a/www/docs/reference/rest-api/devices.mdx
+++ /dev/null
@@ -1,423 +0,0 @@
----
-title: Devices
-group: Devices
----
-
-
-This endpoint allows an administrator to manage Devices.
-
-## API Documentation
-### GET /v0/devices
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/devices" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": [
- {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "description": "factory description",
- "dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "endpoint": "localhost:51820",
- "id": "61d5930b-2b35-44b3-87a9-904e81806728",
- "inserted_at": "2023-03-29T15:11:47.450107Z",
- "ipv4": "100.72.98.240",
- "ipv6": "fd00::39:bf15",
- "latest_handshake": null,
- "mtu": 1280,
- "name": "factory 4421",
- "persistent_keepalive": 25,
- "preshared_key": "32vztut9u6QJG2spTUMnvcb+twugGlT1ikM6AyiPDv8=",
- "public_key": "cGEIZje2ITjFDn96F3bItc5BCl8G1r4SWHH/6QUF4ek=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.450107Z",
- "use_default_allowed_ips": true,
- "use_default_dns": true,
- "use_default_endpoint": true,
- "use_default_mtu": true,
- "use_default_persistent_keepalive": true,
- "user_id": "56062619-2fe2-49de-898c-492d8da794c7"
- },
- {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "description": "factory description",
- "dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "endpoint": "localhost:51820",
- "id": "05db5d62-218e-4139-92f5-0510903ce4f8",
- "inserted_at": "2023-03-29T15:11:47.455712Z",
- "ipv4": "100.111.252.39",
- "ipv6": "fd00::2:456a",
- "latest_handshake": null,
- "mtu": 1280,
- "name": "factory 5411",
- "persistent_keepalive": 25,
- "preshared_key": "78O12m5lG+je3eAqlgJ9pd6d/+VeLjsswsljJFV0jU0=",
- "public_key": "ADOmUjeMl08RgKNhpRaaaHV3YmI9GOVh81zLVLOPk84=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.455712Z",
- "use_default_allowed_ips": true,
- "use_default_dns": true,
- "use_default_endpoint": true,
- "use_default_mtu": true,
- "use_default_persistent_keepalive": true,
- "user_id": "9d3e2da3-bce1-4a03-95cc-d8d0a9797a17"
- },
- {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "description": "factory description",
- "dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "endpoint": "localhost:51820",
- "id": "c865c545-36bd-473e-9c20-9b76766582b2",
- "inserted_at": "2023-03-29T15:11:47.461266Z",
- "ipv4": "100.116.252.229",
- "ipv6": "fd00::7:f039",
- "latest_handshake": null,
- "mtu": 1280,
- "name": "factory 5766",
- "persistent_keepalive": 25,
- "preshared_key": "Dlefj06JAOOCtKxoSlLmvmNXq2zql30FvwDFlEpEISQ=",
- "public_key": "hH9ifN5kI1RtnG54eUXGLEL7Pue9qgGvJ3Gvef7irzU=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.461266Z",
- "use_default_allowed_ips": true,
- "use_default_dns": true,
- "use_default_endpoint": true,
- "use_default_mtu": true,
- "use_default_persistent_keepalive": true,
- "user_id": "47a8eda4-433a-4ce3-a119-720b5d62ddac"
- },
- {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "description": "factory description",
- "dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "endpoint": "localhost:51820",
- "id": "93da8405-217e-40b3-a91b-45d8cd28c2d4",
- "inserted_at": "2023-03-29T15:11:47.467794Z",
- "ipv4": "100.70.183.42",
- "ipv6": "fd00::9:a393",
- "latest_handshake": null,
- "mtu": 1280,
- "name": "factory 1417",
- "persistent_keepalive": 25,
- "preshared_key": "3ipinU20+iTgqCZxSskRPRTBargqtoG73seKz8wZqiE=",
- "public_key": "gzAOiYTnq+rFRBDUbRuJhKXCbe+ULB9xjpCy9l0mBCA=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.467794Z",
- "use_default_allowed_ips": true,
- "use_default_dns": true,
- "use_default_endpoint": true,
- "use_default_mtu": true,
- "use_default_persistent_keepalive": true,
- "user_id": "d8c001ca-ee0f-457f-80a6-802592a7d4ca"
- },
- {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "description": "factory description",
- "dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "endpoint": "localhost:51820",
- "id": "16b319c1-4d8a-478a-88d2-f17056bf1b66",
- "inserted_at": "2023-03-29T15:11:47.473062Z",
- "ipv4": "100.101.38.171",
- "ipv6": "fd00::39:35af",
- "latest_handshake": null,
- "mtu": 1280,
- "name": "factory 4485",
- "persistent_keepalive": 25,
- "preshared_key": "WzNqj8NEQBvYCYjWv4qhuL8sT3n0LVIH52x1xx5U6EE=",
- "public_key": "eD1iqgs712xDZsplZHd7LrNs+WXYshMH99WFkJ0So8o=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.473062Z",
- "use_default_allowed_ips": true,
- "use_default_dns": true,
- "use_default_endpoint": true,
- "use_default_mtu": true,
- "use_default_persistent_keepalive": true,
- "user_id": "605c4532-d516-4b59-a7df-b0479d493cce"
- }
- ]
-}
-```
-### POST /v0/devices
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X POST "https://{firezone_host}/v0/devices" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "device": {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0",
- "1.1.1.1"
- ],
- "description": "create-description",
- "dns": [
- "9.9.9.8"
- ],
- "endpoint": "9.9.9.9",
- "ipv4": "100.64.0.2",
- "ipv6": "fd00::2",
- "mtu": 999,
- "name": "create-name",
- "persistent_keepalive": 9,
- "preshared_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "public_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "use_default_allowed_ips": false,
- "use_default_dns": false,
- "use_default_endpoint": false,
- "use_default_mtu": false,
- "use_default_persistent_keepalive": false,
- "user_id": "95138a8e-c89f-41b4-b62c-a5b8c23a0b8c"
- }
-}'
-EOF
-
-HTTP/1.1 201
-Content-Type: application/json; charset=utf-8
-Location: /v0/devices/3aefe1b8-d98b-4725-bed3-cad021a13480
-
-{
- "data": {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0",
- "1.1.1.1"
- ],
- "description": "create-description",
- "dns": [
- "9.9.9.8"
- ],
- "endpoint": "9.9.9.9",
- "id": "3aefe1b8-d98b-4725-bed3-cad021a13480",
- "inserted_at": "2023-03-29T15:11:47.190722Z",
- "ipv4": "100.64.0.2",
- "ipv6": "fd00::2",
- "latest_handshake": null,
- "mtu": 999,
- "name": "create-name",
- "persistent_keepalive": 9,
- "preshared_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "public_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.190722Z",
- "use_default_allowed_ips": false,
- "use_default_dns": false,
- "use_default_endpoint": false,
- "use_default_mtu": false,
- "use_default_persistent_keepalive": false,
- "user_id": "95138a8e-c89f-41b4-b62c-a5b8c23a0b8c"
- }
-}
-```
-### GET /v0/devices/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `f85310b7-87b5-4c89-b391-d985f7789007`
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/devices/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0"
- ],
- "description": "factory description",
- "dns": [
- "1.1.1.1",
- "1.0.0.1"
- ],
- "endpoint": "localhost:51820",
- "id": "f85310b7-87b5-4c89-b391-d985f7789007",
- "inserted_at": "2023-03-29T15:11:47.299345Z",
- "ipv4": "100.99.173.193",
- "ipv6": "fd00::17:d1a9",
- "latest_handshake": null,
- "mtu": 1280,
- "name": "factory 713",
- "persistent_keepalive": 25,
- "preshared_key": "qrcrAnUh7ryP69SwfseKdBNElOSjOC9/Wv7Z+EBxs50=",
- "public_key": "mLN9py6whsGt+Lg9jP4lX+Cqqlf02plODqWg2UqOmPI=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.299345Z",
- "use_default_allowed_ips": true,
- "use_default_dns": true,
- "use_default_endpoint": true,
- "use_default_mtu": true,
- "use_default_persistent_keepalive": true,
- "user_id": "5f5b582d-9153-46ac-99e5-37a6bc93ce13"
- }
-}
-```
-### PATCH /v0/devices/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `01272ce2-df59-4816-9d82-44830427d757`
-```bash
-$ curl -i \
- -X PUT "https://{firezone_host}/v0/devices/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "device": {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0",
- "1.1.1.1"
- ],
- "description": "create-description",
- "dns": [
- "9.9.9.8"
- ],
- "endpoint": "9.9.9.9",
- "ipv4": "100.64.0.2",
- "ipv6": "fd00::2",
- "mtu": 999,
- "name": "create-name",
- "persistent_keepalive": 9,
- "preshared_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "public_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "use_default_allowed_ips": false,
- "use_default_dns": false,
- "use_default_endpoint": false,
- "use_default_mtu": false,
- "use_default_persistent_keepalive": false
- }
-}'
-EOF
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "allowed_ips": [
- "0.0.0.0/0",
- "::/0",
- "1.1.1.1"
- ],
- "description": "create-description",
- "dns": [
- "9.9.9.8"
- ],
- "endpoint": "9.9.9.9",
- "id": "01272ce2-df59-4816-9d82-44830427d757",
- "inserted_at": "2023-03-29T15:11:47.264313Z",
- "ipv4": "100.64.0.2",
- "ipv6": "fd00::2",
- "latest_handshake": null,
- "mtu": 999,
- "name": "create-name",
- "persistent_keepalive": 9,
- "preshared_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "public_key": "CHqFuS+iL3FTog5F4Ceumqlk0CU4Cl/dyUP/9F9NDnI=",
- "remote_ip": null,
- "rx_bytes": null,
- "server_public_key": "is+0ov0/SZ9I+qyDD+adVoH9LreWHa85QQgpt6RUtA4=",
- "tx_bytes": null,
- "updated_at": "2023-03-29T15:11:47.276849Z",
- "use_default_allowed_ips": false,
- "use_default_dns": false,
- "use_default_endpoint": false,
- "use_default_mtu": false,
- "use_default_persistent_keepalive": false,
- "user_id": "3f7c9d0f-fa89-4619-9237-f0215db34e58"
- }
-}
-```
-### DELETE /v0/devices/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `29f86ac9-82e8-4691-aa44-ea396d3af476`
-```bash
-$ curl -i \
- -X DELETE "https://{firezone_host}/v0/devices/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 204
-```
diff --git a/www/docs/reference/rest-api/rules.mdx b/www/docs/reference/rest-api/rules.mdx
deleted file mode 100644
index a2ce1ad28..000000000
--- a/www/docs/reference/rest-api/rules.mdx
+++ /dev/null
@@ -1,203 +0,0 @@
----
-title: Rules
-group: Rules
----
-
-
-This endpoint allows an adminisrator to manage Rules.
-
-## API Documentation
-### GET /v0/rules
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/rules" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": [
- {
- "action": "drop",
- "destination": "10.3.2.1",
- "id": "2a136a17-4d29-4d8b-a6d4-f35ee3051105",
- "inserted_at": "2023-03-29T15:11:47.482818Z",
- "port_range": null,
- "port_type": null,
- "updated_at": "2023-03-29T15:11:47.482818Z",
- "user_id": null
- },
- {
- "action": "drop",
- "destination": "10.3.2.2",
- "id": "7a4961bf-6b2b-4217-b87b-ffd1deb448ac",
- "inserted_at": "2023-03-29T15:11:47.483506Z",
- "port_range": null,
- "port_type": null,
- "updated_at": "2023-03-29T15:11:47.483506Z",
- "user_id": null
- },
- {
- "action": "drop",
- "destination": "10.3.2.3",
- "id": "6dffbc74-ec58-43ca-8700-d0c572baa198",
- "inserted_at": "2023-03-29T15:11:47.484107Z",
- "port_range": null,
- "port_type": null,
- "updated_at": "2023-03-29T15:11:47.484107Z",
- "user_id": null
- },
- {
- "action": "drop",
- "destination": "10.3.2.4",
- "id": "9bba129d-cdad-4efe-8296-b78ba50f3ef4",
- "inserted_at": "2023-03-29T15:11:47.484759Z",
- "port_range": null,
- "port_type": null,
- "updated_at": "2023-03-29T15:11:47.484759Z",
- "user_id": null
- },
- {
- "action": "drop",
- "destination": "10.3.2.5",
- "id": "df142fde-922c-4a6d-a8e4-0b145a875624",
- "inserted_at": "2023-03-29T15:11:47.485540Z",
- "port_range": null,
- "port_type": null,
- "updated_at": "2023-03-29T15:11:47.485540Z",
- "user_id": null
- }
- ]
-}
-```
-### POST /v0/rules
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X POST "https://{firezone_host}/v0/rules" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "rule": {
- "action": "accept",
- "destination": "1.1.1.1/24",
- "port_range": "1 - 2",
- "port_type": "udp",
- "user_id": "def4dacc-6367-4320-a0fb-4675b9b571cf"
- }
-}'
-EOF
-
-HTTP/1.1 201
-Content-Type: application/json; charset=utf-8
-Location: /v0/rules/c52efbe6-5ed0-4514-97df-93f6013dd52b
-
-{
- "data": {
- "action": "accept",
- "destination": "1.1.1.1/24",
- "id": "c52efbe6-5ed0-4514-97df-93f6013dd52b",
- "inserted_at": "2023-03-29T15:11:47.185000Z",
- "port_range": "1 - 2",
- "port_type": "udp",
- "updated_at": "2023-03-29T15:11:47.185000Z",
- "user_id": "def4dacc-6367-4320-a0fb-4675b9b571cf"
- }
-}
-```
-### GET /v0/rules/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `dd39b339-2ac4-4c83-96e5-9b29516dd85e`
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/rules/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "action": "drop",
- "destination": "10.10.10.0/24",
- "id": "dd39b339-2ac4-4c83-96e5-9b29516dd85e",
- "inserted_at": "2023-03-29T15:11:47.447659Z",
- "port_range": null,
- "port_type": null,
- "updated_at": "2023-03-29T15:11:47.447659Z",
- "user_id": null
- }
-}
-```
-### PATCH /v0/rules/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `720fdab6-32af-4487-bce5-e72fa76be829`
-```bash
-$ curl -i \
- -X PUT "https://{firezone_host}/v0/rules/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "rule": {
- "action": "accept",
- "destination": "1.1.1.1/24",
- "port_range": "1 - 2",
- "port_type": "udp"
- }
-}'
-EOF
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "action": "accept",
- "destination": "1.1.1.1/24",
- "id": "720fdab6-32af-4487-bce5-e72fa76be829",
- "inserted_at": "2023-03-29T15:11:47.243306Z",
- "port_range": "1 - 2",
- "port_type": "udp",
- "updated_at": "2023-03-29T15:11:47.251589Z",
- "user_id": null
- }
-}
-```
-### DELETE /v0/rules/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `f5f10a6e-cfdd-47ea-ae23-264195b3503c`
-```bash
-$ curl -i \
- -X DELETE "https://{firezone_host}/v0/rules/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 204
-```
diff --git a/www/docs/reference/rest-api/users.mdx b/www/docs/reference/rest-api/users.mdx
deleted file mode 100644
index 80ecaee9d..000000000
--- a/www/docs/reference/rest-api/users.mdx
+++ /dev/null
@@ -1,363 +0,0 @@
----
-title: Users
-sidebar_position: 2
-toc_max_heading_level: 4
----
-
-
-This endpoint allows an administrator to manage Users.
-
-## Auto-Create Users from OpenID or SAML providers
-
-You can set Configuration option `auto_create_users` to `true` to automatically create users
-from OpenID or SAML providers. Use it with care as anyone with access to the provider will be
-able to log-in to Firezone.
-
-If `auto_create_users` is `false`, then you need to provision users with `password` attribute,
-otherwise they will have no means to log in.
-
-## Disabling users
-
-Even though API returns `disabled_at` attribute, currently, it's not possible to disable users via API,
-since this field is only for internal use by automatic user disabling mechanism on OIDC/SAML errors.
-
-## API Documentation
-### List all Users [`GET /v0/users`]
-
-
-
-#### Example
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/users" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": [
- {
- "disabled_at": null,
- "email": "test-5094@test",
- "id": "4963a5f0-dbb5-424a-8859-8032209eeaef",
- "inserted_at": "2023-03-29T15:11:47.363517Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "admin",
- "updated_at": "2023-03-29T15:11:47.363517Z"
- },
- {
- "disabled_at": null,
- "email": "test-5634@test",
- "id": "e904d9ae-c358-4ab4-9bfd-44b4bf942a15",
- "inserted_at": "2023-03-29T15:11:47.364938Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "admin",
- "updated_at": "2023-03-29T15:11:47.364938Z"
- },
- {
- "disabled_at": null,
- "email": "test-5666@test",
- "id": "e7decf88-4abb-45df-9dd0-35e3587dfb59",
- "inserted_at": "2023-03-29T15:11:47.366068Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "admin",
- "updated_at": "2023-03-29T15:11:47.366068Z"
- },
- {
- "disabled_at": null,
- "email": "test-5190@test",
- "id": "457aeee0-13aa-44b3-9057-181cc206edcb",
- "inserted_at": "2023-03-29T15:11:47.367568Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "admin",
- "updated_at": "2023-03-29T15:11:47.367568Z"
- }
- ]
-}
-```
-### Create a User [`POST /v0/users`]
-
-
-Create a new User.
-
-This endpoint is useful in two cases:
-
- 1. When [Local Authentication](/docs/authenticate/local-auth/) is enabled (discouraged in
- production deployments), it allows an administrator to provision users with their passwords;
- 2. When `auto_create_users` in the associated OpenID or SAML configuration is disabled,
- it allows an administrator to provision users with their emails beforehand, effectively
- whitelisting specific users for authentication.
-
-If `auto_create_users` is `true` in the associated OpenID or SAML configuration, there is no need
-to provision users; they will be created automatically when they log in for the first time using
-the associated OpenID or SAML provider.
-
-#### User Attributes
-
-| Attribute | Type | Required | Description |
-| --------- | ---- | -------- | ----------- |
-| `role` | `admin` or `unprivileged` (default) | No | User role. |
-| `email` | `string` | Yes | Email which will be used to identify the user. |
-| `password` | `string` | No | A password that can be used for login-password authentication. |
-| `password_confirmation` | `string` | -> | Is required when the `password` is set. |
-
-#### Example
-```bash
-$ curl -i \
- -X POST "https://{firezone_host}/v0/users" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "user": {
- "email": "new-user@test",
- "password": "test1234test",
- "password_confirmation": "test1234test",
- "role": "unprivileged"
- }
-}'
-EOF
-
-HTTP/1.1 201
-Content-Type: application/json; charset=utf-8
-Location: /v0/users/2b7128fb-4a30-472d-9f45-d2a5063ba5db
-
-{
- "data": {
- "disabled_at": null,
- "email": "new-user@test",
- "id": "2b7128fb-4a30-472d-9f45-d2a5063ba5db",
- "inserted_at": "2023-03-29T15:11:47.178709Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "unprivileged",
- "updated_at": "2023-03-29T15:11:47.178709Z"
- }
-}
-```
-#### Provision an unprivileged OpenID User
-```bash
-$ curl -i \
- -X POST "https://{firezone_host}/v0/users" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "user": {
- "email": "new-user@test",
- "role": "unprivileged"
- }
-}'
-EOF
-
-HTTP/1.1 201
-Content-Type: application/json; charset=utf-8
-Location: /v0/users/e4796108-f4d8-4a11-9860-d07b92b08d93
-
-{
- "data": {
- "disabled_at": null,
- "email": "new-user@test",
- "id": "e4796108-f4d8-4a11-9860-d07b92b08d93",
- "inserted_at": "2023-03-29T15:11:47.192265Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "unprivileged",
- "updated_at": "2023-03-29T15:11:47.192265Z"
- }
-}
-```
-#### Provision an admin OpenID User
-```bash
-$ curl -i \
- -X POST "https://{firezone_host}/v0/users" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "user": {
- "email": "new-user@test",
- "role": "admin"
- }
-}'
-EOF
-
-HTTP/1.1 201
-Content-Type: application/json; charset=utf-8
-Location: /v0/users/479ed1cb-1657-4c82-bc32-2200f6cc82e9
-
-{
- "data": {
- "disabled_at": null,
- "email": "new-user@test",
- "id": "479ed1cb-1657-4c82-bc32-2200f6cc82e9",
- "inserted_at": "2023-03-29T15:11:47.460359Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "admin",
- "updated_at": "2023-03-29T15:11:47.460359Z"
- }
-}
-```
-#### Error due to invalid parameters
-```bash
-$ curl -i \
- -X POST "https://{firezone_host}/v0/users" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "user": {
- "email": "test@test.com",
- "password": "test1234"
- }
-}'
-EOF
-
-HTTP/1.1 422
-Content-Type: application/json; charset=utf-8
-
-{
- "errors": {
- "password": [
- "should be at least 12 character(s)"
- ],
- "password_confirmation": [
- "can't be blank"
- ]
- }
-}
-```
-### GET /v0/users/{id}
-
-
-
-#### An email can be used instead of ID.
-**URI Parameters:**
-
- - `id`: `test-905@test`
-```bash
-$ curl -i \
- -X GET "https://{firezone_host}/v0/users/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "disabled_at": null,
- "email": "test-905@test",
- "id": "d43dae29-0687-456c-a3a4-a461eb744cf5",
- "inserted_at": "2023-03-29T15:11:47.340583Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "admin",
- "updated_at": "2023-03-29T15:11:47.340583Z"
- }
-}
-```
-### Update a User [`PATCH /v0/users/{id}`]
-
-
-For details please see [Create a User](#create-a-user-post-v0users) section.
-
-#### Update by email
-**URI Parameters:**
-
- - `id`: `test-1960@test`
-```bash
-$ curl -i \
- -X PUT "https://{firezone_host}/v0/users/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "user": {}
-}'
-EOF
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "disabled_at": null,
- "email": "test-1960@test",
- "id": "8830b359-2368-4f55-9879-1cb04ee0cbbf",
- "inserted_at": "2023-03-29T15:11:47.391921Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "unprivileged",
- "updated_at": "2023-03-29T15:11:47.391921Z"
- }
-}
-```
-#### Update by ID
-**URI Parameters:**
-
- - `id`: `d542e1bc-25b2-453d-ae14-41f8f81605ee`
-```bash
-$ curl -i \
- -X PUT "https://{firezone_host}/v0/users/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
- --data-binary @- << EOF
-{
- "user": {}
-}'
-EOF
-
-HTTP/1.1 200
-Content-Type: application/json; charset=utf-8
-
-{
- "data": {
- "disabled_at": null,
- "email": "test-1513@test",
- "id": "d542e1bc-25b2-453d-ae14-41f8f81605ee",
- "inserted_at": "2023-03-29T15:11:47.475440Z",
- "last_signed_in_at": null,
- "last_signed_in_method": null,
- "role": "unprivileged",
- "updated_at": "2023-03-29T15:11:47.475440Z"
- }
-}
-```
-### DELETE /v0/users/{id}
-
-
-
-#### Example
-**URI Parameters:**
-
- - `id`: `31156bf6-73de-4d9b-aa1e-2e419a45dd25`
-```bash
-$ curl -i \
- -X DELETE "https://{firezone_host}/v0/users/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 204
-Content-Type: application/json; charset=utf-8
-```
-#### An email can be used instead of ID.
-**URI Parameters:**
-
- - `id`: `test-4996@test`
-```bash
-$ curl -i \
- -X DELETE "https://{firezone_host}/v0/users/{id}" \
- -H 'Content-Type: application/json' \
- -H 'Authorization: Bearer {api_token}' \
-
-HTTP/1.1 204
-Content-Type: application/json; charset=utf-8
-```
diff --git a/www/docs/reference/reverse-proxy-templates/README.mdx b/www/docs/reference/reverse-proxy-templates/README.mdx
deleted file mode 100644
index 84d6c6262..000000000
--- a/www/docs/reference/reverse-proxy-templates/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Reverse Proxy Templates
-sidebar_position: 8
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/reference/reverse-proxy-templates/apache.mdx b/www/docs/reference/reverse-proxy-templates/apache.mdx
deleted file mode 100644
index af680037a..000000000
--- a/www/docs/reference/reverse-proxy-templates/apache.mdx
+++ /dev/null
@@ -1,66 +0,0 @@
----
-title: Apache
-sidebar_position: 1
----
-
-The following are example [apache](https://httpd.apache.org/) configurations
-with and without SSL termination.
-
-These expect the apache to be running on the same host as Firezone and
-`default['firezone']['phoenix']['port']` to be `13000`.
-
-## Without SSL termination
-
-Since Firezone requires HTTPS for the web portal, please bear in mind a
-downstream proxy will need to terminate SSL connections in this scenario.
-
-`` needs to be replaced with your domain name.
-
-This configuration needs to be placed in
-`/etc/sites-available/.conf`
-
-and activated with `a2ensite `
-
-```conf
-LoadModule rewrite_module /usr/lib/apache2/modules/mod_rewrite.so
-LoadModule proxy_module /usr/lib/apache2/modules/mod_proxy.so
-LoadModule proxy_http_module /usr/lib/apache2/modules/mod_proxy_http.so
-LoadModule proxy_wstunnel_module /usr/lib/apache2/modules/mod_proxy_wstunnel.so
-
- ServerName
- ProxyPassReverse "/" "http://127.0.0.1:13000/"
- ProxyPass "/" "http://127.0.0.1:13000/"
- RewriteEngine on
- RewriteCond %{HTTP:Upgrade} websocket [NC]
- RewriteCond %{HTTP:Connection} upgrade [NC]
- RewriteRule ^/?(.*) "ws://127.0.0.1:13000/$1" [P,L]
-
-```
-
-## With SSL termination
-
-This configuration builds on the one above and uses Firezone's auto-generated
-self-signed certificates.
-
-```conf
-LoadModule rewrite_module /usr/lib/apache2/modules/mod_rewrite.so
-LoadModule proxy_module /usr/lib/apache2/modules/mod_proxy.so
-LoadModule proxy_http_module /usr/lib/apache2/modules/mod_proxy_http.so
-LoadModule proxy_wstunnel_module /usr/lib/apache2/modules/mod_proxy_wstunnel.so
-LoadModule ssl_module /usr/lib/apache2/modules/mod_ssl.so
-LoadModule headers_module /usr/lib/apache2/modules/mod_headers.so
-Listen 443
-
- ServerName
- RequestHeader set X-Forwarded-Proto "https"
- ProxyPassReverse "/" "http://127.0.0.1:13000/"
- ProxyPass "/" "http://127.0.0.1:13000/"
- RewriteEngine on
- RewriteCond %{HTTP:Upgrade} websocket [NC]
- RewriteCond %{HTTP:Connection} upgrade [NC]
- RewriteRule ^/?(.*) "ws://127.0.0.1:13000/$1" [P,L]
- SSLEngine On
- SSLCertificateFile "/var/opt/firezone/ssl/ca/acme-test.firez.one.crt"
- SSLCertificateKeyFile "/var/opt/firezone/ssl/ca/acme-test.firez.one.key"
-
-```
diff --git a/www/docs/reference/reverse-proxy-templates/haproxy.mdx b/www/docs/reference/reverse-proxy-templates/haproxy.mdx
deleted file mode 100644
index 6307b6d66..000000000
--- a/www/docs/reference/reverse-proxy-templates/haproxy.mdx
+++ /dev/null
@@ -1,32 +0,0 @@
----
-title: HAProxy
-sidebar_position: 3
----
-
-The following is an example reverse proxy configuration for [HAProxy](
-https://www.haproxy.org/) proxy. We assume
-`default['firezone']['phoenix']['port']` to be `13000` and the proxy running on
-the same host as the Firezone app.
-
-Since Firezone requires HTTPS for the web portal, please bear in mind a
-downstream proxy will need to terminate SSL connections in this scenario.
-
-You can also configure HAProxy to handle the SSL termination as explained
-[here](https://www.haproxy.com/blog/haproxy-ssl-termination/) but take into
-account that the `pem` file expected by `ssl crt` option needs to contain
-both the `crt` and `key` file.
-
-`/etc/haproxy/haproxy.cfg`:
-
-```conf
-defaults
- mode http
-
-frontend app1
- bind *:80
- option forwardfor
- default_backend backend_app1
-
-backend backend_app1
- server mybackendserver 127.0.0.1:13000
-```
diff --git a/www/docs/reference/reverse-proxy-templates/traefik.mdx b/www/docs/reference/reverse-proxy-templates/traefik.mdx
deleted file mode 100644
index d38c7a9a7..000000000
--- a/www/docs/reference/reverse-proxy-templates/traefik.mdx
+++ /dev/null
@@ -1,275 +0,0 @@
----
-title: Traefik
-sidebar_position: 2
----
-
-The following are examples for configuring the [Traefik](https://traefik.io/)
-proxy as a reverse proxy for Firezone.
-
-In these examples, we assume Traefik is deployed using Docker on the same host
-as Firezone. For this to work, you'll need to make sure
-`PHOENIX_EXTERNAL_TRUSTED_PROXIES` is set to include the Docker address of the
-Traefik service.
-
-## Without SSL termination
-
-Since Firezone requires HTTPS for the web portal, please bear in mind a
-downstream proxy will need to terminate SSL connections in this scenario.
-
-Use the following `docker-compose.yml` and `rules.yml` files as a starting point
-for your own Firezone config:
-
-### `docker-compose.yml`
-
-```yaml
-version: '3'
-
-x-deploy: &default-deploy
- restart_policy:
- condition: on-failure
- delay: 5s
- max_attempts: 3
- window: 120s
- update_config:
- order: start-first
-
-networks:
- firezone-network:
- enable_ipv6: true
- ipam:
- config:
- - subnet: 172.25.0.0/16
- - subnet: 2001:3990:3990::/64
-
-services:
- traefik:
- deploy:
- <<: *default-deploy
- # The official v2 Traefik docker image
- image: traefik:v2.8
- # Enables the web UI and tells Traefik to listen to docker
- command:
- - "--providers.docker"
- - "--providers.file.filename=rules.yml"
- - "--entrypoints.web.address=:80"
- - "--entrypoints.web.forwardedHeaders.insecure"
- - "--log.level=DEBUG"
- extra_hosts:
- - "host.docker.internal:host-gateway"
- ports:
- # The HTTP port
- - "80:80"
- volumes:
- # So that Traefik can listen to the Docker events
- - /var/run/docker.sock:/var/run/docker.sock
- - ./rules.yml:/rules.yml
- # make the IP of this service deterministic
- networks:
- firezone-network:
- ipv4_address: 172.25.0.99
- ipv6_address: 2001:3990:3990::99
-
- firezone:
- image: firezone/firezone
- ports:
- - 51820:51820/udp
- env_file:
- # This should contain a list of env vars for configuring Firezone.
- # See https://www.firezone.dev/docs/reference/env-vars for more info.
- - ${FZ_INSTALL_DIR:-.}/.env
- volumes:
- # IMPORTANT: Persists WireGuard private key and other data. If
- # /var/firezone/private_key exists when Firezone starts, it is
- # used as the WireGuard private. Otherwise, one is generated.
- - ${FZ_INSTALL_DIR:-.}/firezone:/var/firezone
- cap_add:
- # Needed for WireGuard and firewall support.
- - NET_ADMIN
- - SYS_MODULE
- sysctls:
- # Needed for masquerading and NAT.
- - net.ipv6.conf.all.disable_ipv6=0
- - net.ipv4.ip_forward=1
- - net.ipv6.conf.all.forwarding=1
- depends_on:
- - postgres
- networks:
- firezone-network:
- ipv4_address: 172.25.0.100
- deploy:
- <<: *default-deploy
-
- postgres:
- image: postgres:15
- volumes:
- - postgres-data:/var/lib/postgresql/data
- environment:
- POSTGRES_DB: ${DATABASE_NAME:-firezone}
- POSTGRES_USER: ${DATABASE_USER:-postgres}
- POSTGRES_PASSWORD: ${DATABASE_PASSWORD:?err}
- networks:
- - firezone-network
- deploy:
- <<: *default-deploy
- update_config:
- order: stop-first
-
-# Postgres needs a named volume to prevent perms issues on non-linux platforms
-volumes:
- postgres-data:
-
-networks:
- firezone-network:
- driver: bridge
- ipam:
- config:
- - subnet: 172.25.0.0/16
-```
-
-### `rules.yml`
-
-```yaml
-http:
- routers:
- test:
- entryPoints:
- - "web"
- service: test
- rule: "Host(`44.200.42.78`)"
- services:
- test:
- loadBalancer:
- servers:
- - url: "http://firezone:13000"
-```
-
-Now you should be able to start the Traefik proxy with `docker compose up`.
-
-## With SSL termination
-
-This configuration uses Firezone's auto-generated self-signed certificates.
-
-### SSL `docker-compose.yml`
-
-```yaml
-version: "3"
-
-x-deploy: &default-deploy
- restart_policy:
- condition: on-failure
- delay: 5s
- max_attempts: 3
- window: 120s
- update_config:
- order: start-first
-
-networks:
- app:
- enable_ipv6: true
- ipam:
- config:
- - subnet: 172.28.0.0/16
- - subnet: 2001:3990:3990::/64
-
-services:
- firezone:
- image: firezone/firezone
- ports:
- - 51820:51820/udp
- volumes:
- # IMPORTANT: Persists WireGuard private key and other data. If
- # /var/firezone/private_key exists when Firezone starts, it is
- # used as the WireGuard private. Otherwise, one is generated.
- - ${HOME}/.firezone/firezone:/var/firezone
- environment:
- EXTERNAL_URL: ${EXTERNAL_URL:?err}
- DEFAULT_ADMIN_EMAIL: ${DEFAULT_ADMIN_EMAIL:?err}
- DEFAULT_ADMIN_PASSWORD: ${DEFAULT_ADMIN_PASSWORD:?err}
- GUARDIAN_SECRET_KEY: ${GUARDIAN_SECRET_KEY:?err}
- SECRET_KEY_BASE: ${SECRET_KEY_BASE:?err}
- LIVE_VIEW_SIGNING_SALT: ${LIVE_VIEW_SIGNING_SALT:?err}
- COOKIE_SIGNING_SALT: ${COOKIE_SIGNING_SALT:?err}
- COOKIE_ENCRYPTION_SALT: ${COOKIE_ENCRYPTION_SALT:?err}
- DATABASE_ENCRYPTION_KEY: ${DATABASE_ENCRYPTION_KEY:?err}
-
- # Ensure this includes the traefik service IP.
- PHOENIX_EXTERNAL_TRUSTED_PROXIES: [""]
- networks:
- - app
- cap_add:
- - NET_ADMIN
- - SYS_MODULE
- sysctls:
- - net.ipv6.conf.all.disable_ipv6=0
- - net.ipv4.ip_forward=1
- - net.ipv6.conf.all.forwarding=1
- depends_on:
- - postgres
- traefik:
- deploy:
- <<: *default-deploy
- # The official v2 Traefik docker image
- image: traefik:v2.8
- # Enables the web UI and tells Traefik to listen to docker
- command:
- - "--providers.docker"
- - "--providers.file.filename=rules.yml"
- - "--entrypoints.web.address=:443"
- - "--entrypoints.web.forwardedHeaders.insecure"
- - "--log.level=DEBUG"
- extra_hosts:
- - "host.docker.internal:host-gateway"
- ports:
- # The HTTP port
- - "443:443"
- volumes:
- # So that Traefik can listen to the Docker events
- - /var/run/docker.sock:/var/run/docker.sock
- - ./rules.yml:/rules.yml
- # make the IP of this service deterministic
- networks:
- app:
- ipv4_address: 172.28.0.99
- ipv6_address: 2001:3990:3990::99
- postgres:
- image: postgres:15
- volumes:
- - postgres-data:/var/lib/postgresql/data
- environment:
- # same value as ## DB section above
- POSTGRES_DB: ${DATABASE_NAME:-firezone}
- POSTGRES_USER: ${DATABASE_USER:-postgres}
- POSTGRES_PASSWORD: ${DATABASE_PASSWORD:?err}
- deploy:
- <<: *default-deploy
- update_config:
- order: stop-first
-
-# Postgres needs a named volume to prevent perms issues on non-linux platforms
-volumes:
- postgres-data:
-```
-
-### SSL `rules.yml`
-
-```yaml
-http:
- routers:
- test:
- entryPoints:
- - "web"
- service: test
- rule: "Host(`44.200.42.78`)"
- tls: {}
- services:
- test:
- loadBalancer:
- servers:
- - url: "http://firezone:13000"
-tls:
- stores:
- default:
- defaultCertificate:
- certFile: /path/to/your/cert.crt
- keyFile: /path/to/your/key.key
-```
diff --git a/www/docs/reference/security-controls.mdx b/www/docs/reference/security-controls.mdx
deleted file mode 100644
index bd19eea62..000000000
--- a/www/docs/reference/security-controls.mdx
+++ /dev/null
@@ -1,65 +0,0 @@
----
-title: Security Controls
-sidebar_position: 10
----
-
-Firezone employs a few different security controls to keep data secure in
-transit and at rest.
-
-## Overview of Cryptography Used
-
-Below is a table of cryptography used and to which contexts they apply.
-
-| Cryptography | Context | Notes |
-| --- | --- | --- |
-| AES-GCM | Data at rest | Used to encrypt sensitive database fields such as device preshared keys and multi-factor authentication secrets. |
-| Argon2 | Data at rest | Used to hash user passwords for the local authentication method. |
-| TLSv1.2/TLSv1.3 | Data in transit | Used by the Caddy server to encrypt HTTP connections to the portal. Read more at https://caddyserver.com/docs/caddyfile/directives/tls. SSL certificates are provisioned automatically with the ACME protocol by Let's Encrypt by default. |
-| ChaCha20, Poly1305, Curve25519, BLAKE2s, SipHash24, HKDF | Data in transit | Used by WireGuard® for VPN tunnels. Read more at https://wireguard.com/protocol. Firezone uses Linux kernel WireGuard without modification. |
-
-## Security policy
-
-We take security issues very seriously and strive to fix all security issues
-as soon as they're reported.
-
-### Announcements
-
-We'll announce major security issues on our security mailing list located at:
-
-https://discourse.firez.one/?utm_source=docs.firezone.dev
-
-### Supported Versions
-
-We release security patches for supported versions of Firezone. We recommend
-running the latest version of Firezone at all times.
-
-### Reporting a Vulnerability
-
-Please **do not** open a Github Issue for security issues you encounter.
-Instead, please send an email to `security AT firezone.dev` describing the issue
-and we'll respond as soon as possible.
-
-### PGP Key
-
-You may use the public key below to encrypt emails to `security AT firezone.dev`.
-You can also find this key at:
-
-https://pgp.mit.edu/pks/lookup?op=get&search=0x45113BA04AD83D8A
-
-```
------BEGIN PGP PUBLIC KEY BLOCK-----
-Version: SKS 1.1.6
-Comment: Hostname: pgp.mit.edu
-
-mDMEYYwK5BYJKwYBBAHaRw8BAQdA4ooDpwDy3V0wHCftM/LHD5e713LSr0SQy49joUMgHoS0
-JkZpcmV6b25lIFNlY3VyaXR5IDxzZWN1cml0eUBmaXJlei5vbmU+iJoEExYKAEIWIQQlD4tW
-gEEHBC38anNFETugStg9igUCYYwK5AIbAwUJA8JnAAULCQgHAgMiAgEGFQoJCAsCBBYCAwEC
-HgcCF4AACgkQRRE7oErYPYoORwEAiYi3arrcR2e5OfqsoAbCN0O6M0HWeo1K/ZoFWH2jLy0B
-AMsWk58vepKqNhUKhuDb8bSjK8TOr/IxB63lSkQaz9MIuDgEYYwK5BIKKwYBBAGXVQEFAQEH
-QPLzia/me7FOsFfAJKWm0X1qC5byv2GWn6LZPV013AdoAwEIB4h+BBgWCgAmFiEEJQ+LVoBB
-BwQt/GpzRRE7oErYPYoFAmGMCuQCGwwFCQPCZwAACgkQRRE7oErYPYr0ZQEAig86wu+zrNiT
-B4t3dk3psHRj+Kdn4uURLjUBZqYNvXoA+QEBUPtP7hNjum+1FrzYmHUFdCBA/cszz7x7PQ36
-5gcE
-=0gEr
------END PGP PUBLIC KEY BLOCK-----
-```
diff --git a/www/docs/reference/telemetry.mdx b/www/docs/reference/telemetry.mdx
deleted file mode 100644
index 620e450ab..000000000
--- a/www/docs/reference/telemetry.mdx
+++ /dev/null
@@ -1,90 +0,0 @@
----
-title: Telemetry
-sidebar_position: 4
----
-
-This document presents an overview of the telemetry Firezone collects from your
-self-hosted instance and how to disable it.
-
-## Why Firezone collects telemetry
-
-We _rely_ on telemetry to prioritize our roadmap and optimize the engineering
-resources we have to make Firezone better for everyone.
-
-The telemetry we collect aims to answer the following questions:
-
-- How many people install, use, and stop using Firezone?
-- What features are most valuable, and which ones don’t see any use?
-- What functionality needs the most improvement?
-- When something breaks, why did it break, and how can we prevent it from happening
- in the future?
-
-## How we collect telemetry
-
-There are three main places where telemetry is collected in Firezone:
-
-1. Package telemetry. Includes events such as install, uninstall, and upgrade.
-2. CLI telemetry from `firezone-ctl` commands.
-3. Product telemetry associated with the Web portal.
-
-In each of these three contexts, we capture the minimum amount of data necessary
-to answer the questions in the section above.
-
-Admin emails are collected **only if** you explicitly opt-in to product updates.
-Otherwise, personally-identifiable information is **_never_** collected.
-
-We store telemetry in [PostHog](https://posthog.com) only accessible by the Firezone team.
-Here is an example of a telemetry event that is sent from your instance of
-Firezone to our telemetry server:
-
-```json
-{
- "id": "0182272d-0b88-0000-d419-7b9a413713f1",
- "timestamp": "2022-07-22T18:30:39.748000+00:00",
- "event": "fz_http_started",
- "distinct_id": "1ec2e794-1c3e-43fc-a78f-1db6d1a37f54",
- "properties": {
- "$geoip_city_name": "Ashburn",
- "$geoip_continent_code": "NA",
- "$geoip_continent_name": "North America",
- "$geoip_country_code": "US",
- "$geoip_country_name": "United States",
- "$geoip_latitude": 39.0469,
- "$geoip_longitude": -77.4903,
- "$geoip_postal_code": "20149",
- "$geoip_subdivision_1_code": "VA",
- "$geoip_subdivision_1_name": "Virginia",
- "$geoip_time_zone": "America/New_York",
- "$ip": "52.200.241.107",
- "$plugins_deferred": [],
- "$plugins_failed": [],
- "$plugins_succeeded": ["GeoIP (3)"],
- "distinct_id": "1zc2e794-1c3e-43fc-a78f-1db6d1a37f54",
- "fqdn": "awsdemo.firezone.dev",
- "kernel_version": "linux 5.13.0",
- "version": "0.4.6"
- },
- "elements_chain": ""
-}
-```
-
-## How to disable telemetry
-
-:::note
-We _rely_ on product analytics to make Firezone better for everyone.
-Leaving telemetry enabled is the **single most valuable contribution** you can
-make to Firezone’s development. That said, we understand some users have higher
-privacy or security requirements and would prefer to disable telemetry altogether.
-If that’s you, keep reading.
-:::
-
-Telemetry is enabled by default. To completely disable product telemetry:
-
-
-
-
-Set the `TELEMETRY_ENABLED` environment variable to `false` and
-restart the `firezone` container.
-
-
-
diff --git a/www/docs/user-guides/README.mdx b/www/docs/user-guides/README.mdx
deleted file mode 100644
index 28e51db73..000000000
--- a/www/docs/user-guides/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: User Guides
-sidebar_position: 5
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/user-guides/add-devices.mdx b/www/docs/user-guides/add-devices.mdx
deleted file mode 100644
index a468029e6..000000000
--- a/www/docs/user-guides/add-devices.mdx
+++ /dev/null
@@ -1,32 +0,0 @@
----
-title: Add Devices
-sidebar_position: 2
----
-
-# Add or remove devices
-
-When a device is created, Firezone generates the WireGuard private key
-ephemerally in the user's browser. This key is **never saved**, and cannot
-be shown again once it is no longer displayed.
-
-**We recommend asking end users to generate their own device configs so the
-WireGuard private key is not exposed.** Users can follow instructions
-on the [Client Instructions](/docs/user-guides/client-instructions/) page to
-generate their own WireGuard configs.
-
-## Admin device config generation
-
-Firezone admins can generate device configs for all users. This can be done by
-clicking the "Add Device" button on the user profile page found in `/users`.
-
-
-
-Once the device profile is created, the admin can download and send the
-WireGuard configuration file to the user over a secure channel.
-
-See [Add Users](/docs/user-guides/add-users/) for more information on how to add a
-user.
-
-## Related guides
-
-- [Client Instructions](/docs/user-guides/client-instructions/)
diff --git a/www/docs/user-guides/add-users.mdx b/www/docs/user-guides/add-users.mdx
deleted file mode 100644
index 585841e62..000000000
--- a/www/docs/user-guides/add-users.mdx
+++ /dev/null
@@ -1,24 +0,0 @@
----
-title: Add Users
-sidebar_position: 1
----
-
-# Add or remove users
-
-Once you have successfully installed Firezone you'll need to add users to grant
-them access to your network. This can be done through the Web UI or the
-[REST API](/docs/reference/rest-api/users).
-
-## Web UI
-
-Add a user by clicking the "Add User" button under `/users`. You will be asked
-to specify an email and a password for the user. Firezone can also integrate and
-sync with an identity provider to automatically grant access to users in your
-organization. See [Authenticate](/docs/authenticate/) for more
-information.
-
-
-
-## Related guides
-
-- [Authenticate](/docs/authenticate/)
diff --git a/www/docs/user-guides/client-instructions.mdx b/www/docs/user-guides/client-instructions.mdx
deleted file mode 100644
index 2f56b1a43..000000000
--- a/www/docs/user-guides/client-instructions.mdx
+++ /dev/null
@@ -1,185 +0,0 @@
----
-title: Client Instructions
-sidebar_position: 4
-description:
- Set up your client app to connect to your organization's private
- networks and resources. Download the open-source WireGuard® app
- for your operating system (Windows, MacOS, iOS, Android, Linux) to
- get started.
----
-
-# End-user client instructions
-
-Follow these instructions if you're an end-user trying to set up your WireGuard client to work with Firezone.
-
-## Install and setup
-
-Follow this guide to establish a VPN session
-through the WireGuard native client.
-
-### Step 1: Install the native WireGuard client
-
-Firezone is compatible with the official WireGuard clients found here:
-
-* [macOS](https://itunes.apple.com/us/app/wireguard/id1451685025)
-* [Windows](https://download.wireguard.com/windows-client/wireguard-installer.exe)
-* [iOS](https://itunes.apple.com/us/app/wireguard/id1441195209)
-* [Android](https://play.google.com/store/apps/details?id=com.wireguard.android)
-
-For operating systems not listed above see the Official WireGuard site: [
-https://www.wireguard.com/install/](https://www.wireguard.com/install/).
-
-### Step 2: Download the device config file
-
-The device config file can either be obtained from your Firezone administrator
-or self-generated via the Firezone portal.
-
-To self generate a device config file, visit the domain provided by your Firezone
-administrator. This URL will be specific to your company
-(in this example it is `https://firezone.example.com`)
-
-
-
-### Step 3 (optional): Enable on boot
-
-Open the WireGuard client and import the `.conf` file.
-Activate the VPN session by toggling the `Activate` switch.
-
-
-
-## Re-authenticating your session
-
-If your network admin has required periodic authentication to maintain your VPN session,
-follow the steps below. You will need:
-
-* **URL of the Firezone portal**: Ask your Network Admin for the link.
-* **Credentials**: Your username and password should be provided by your Network
-Admin. If your company is using a Single Sign On provider (like Google or Okta),
-the Firezone portal will prompt you to authenticate via that provider.
-
-### Step 1: Deactivate VPN session
-
-
-
-### Step 2: Re-authenticate
-
-Visit the URL of your Firezone portal and sign in using credentials provided by your
-network admin. If you are already logged into the portal,
-click the `Reauthenticate` button, then sign in again.
-
-
-
-### Step 3: Activate VPN session
-
-
-
-## Linux: Network Manager
-
-The following steps can be used on Linux devices to import the WireGuard
-configuration profile using Network Manager CLI (`nmcli`).
-
-:::note
-Importing the configuration file using the Network Manager GUI may fail
-with the following error if the profile has IPv6 support enabled:
-
-```text
-ipv6.method: method "auto" is not supported for WireGuard
-```
-
-:::
-
-### Step 1: Install the WireGuard tools
-
-The WireGuard userspace tools need to be installed. For most Linux
-distributions this will be a package named `wireguard` or `wireguard-tools`.
-
-For Debian/Ubuntu:
-
-```shell
-sudo apt install wireguard
-```
-
-For Fedora:
-
-```shell
-sudo dnf install wireguard-tools
-```
-
-For Arch Linux:
-
-```shell
-sudo pacman -S wireguard-tools
-```
-
-For distributions not listed above see the Official WireGuard site: [
-https://www.wireguard.com/install/](https://www.wireguard.com/install/).
-
-### Step 2: Download configuration
-
-The device config file can either be obtained from your Firezone administrator
-or self-generated via the Firezone portal.
-
-To self generate a device config file, visit the domain provided by your Firezone
-administrator. This URL will be specific to your company
-(in this example it is `https://firezone.example.com`)
-
-
-
-### Step 3: Import configuration
-
-Using `nmcli`, import the downloaded configuration file:
-
-```shell
-sudo nmcli connection import type wireguard file /path/to/configuration.conf
-```
-
-:::note
-The WireGuard connection/interface will match the name of the configuration
-file. If required, the connection can be renamed after import:
-
-```shell
-nmcli connection modify [old name] connection.id [new name]
-```
-
-:::
-
-### Step 4: Connect/disconnect
-
-To connect to the VPN via the command line:
-
-```shell
-nmcli connection up [vpn name]
-```
-
-To disconnect:
-
-```shell
-nmcli connection down [vpn name]
-```
-
-If using a GUI, the relevant Network Manager applet can also be used to control
-the connection.
-
-### Auto connection
-
-The VPN connection can be set to automatically connect by setting the `autoconnect`
-option to `yes`:
-
-```shell
-nmcli connection modify [vpn name] connection.autoconnect yes
-```
-
-To disable the automatic connection set it back to `no`:
-
-```shell
-nmcli connection modify [vpn name] connection.autoconnect no
-```
-
-## Enable multi-factor authentication
-
-To enable MFA navigate to `/user_account/register_mfa` in the Firezone portal.
-After generating the QR code, scan using your authenticator app and
-input the 6 digit code.
-
-If you lose your authenticator app, contact your Admin to reset
-access to your account.
diff --git a/www/docs/user-guides/egress-rules.mdx b/www/docs/user-guides/egress-rules.mdx
deleted file mode 100644
index 8101cbc06..000000000
--- a/www/docs/user-guides/egress-rules.mdx
+++ /dev/null
@@ -1,18 +0,0 @@
----
-title: Egress Rules
-sidebar_position: 3
-description:
- Define access policies with egress filtering rules using
- Firezone's WireGuard®-based secure access platform.
----
-
-# Network access control
-
-Firezone supports egress filtering controls to explicitly DROP or ACCEPT packets
-via the kernel's netfilter system. By default, all traffic is allowed.
-
-The Allowlist and Denylist support both IPv4 and IPv6 CIDRs and IP addresses.
-When adding a rule, you may optionally scope it to a user which applies the
-rule to all their devices.
-
-
diff --git a/www/docs/user-guides/use-cases/README.mdx b/www/docs/user-guides/use-cases/README.mdx
deleted file mode 100644
index e2e467551..000000000
--- a/www/docs/user-guides/use-cases/README.mdx
+++ /dev/null
@@ -1,11 +0,0 @@
----
-title: Common Use Cases
-sidebar_position: 10
----
-
-```mdx-code-block
-import DocCardList from '@theme/DocCardList';
-import {useCurrentSidebarCategory} from '@docusaurus/theme-common';
-
-
-```
diff --git a/www/docs/user-guides/use-cases/nat-gateway/README.mdx b/www/docs/user-guides/use-cases/nat-gateway/README.mdx
deleted file mode 100644
index e83b5c9b9..000000000
--- a/www/docs/user-guides/use-cases/nat-gateway/README.mdx
+++ /dev/null
@@ -1,71 +0,0 @@
----
-title: NAT Gateway
-sidebar_position: 3
-description: Set a static IP for egress traffic with Firezone's WireGuard®-based secure access platform.
----
-
-# Static egress IP with a NAT gateway
-
-Firezone can be used as NAT gateway in order to provide a single,
-static egress IP for all of your team's traffic to flow out of.
-This is commonly used in the following scenarios:
-
-- Consulting engagements: Ask your client to whitelist a single static
- IP address associated with your engagement instead of your employees'
- individual device IPs.
-- Masking your device IP or proxying your source IP for privacy or
- security reasons.
-
-This guide will walk through a simple example restricting access for a
-self-hosted web app to a single whitelisted static IP running Firezone.
-
-This is commonly done in place of maintaining an IP whitelist for
-multiple team members, which becomes impossible to manage as the
-access list grows and team members' IP addresses change.
-
-
-
-## AWS example
-
-Our goal is to configure VPN traffic to the restricted resource to be routed
-through a Firezone server on an EC2 instance. In this case Firezone is acting as
-a network proxy or NAT gateway to provide a single public egress IP for all the
-devices connected to it.
-
-In this example the protected resource and Firezone are in separate VPC regions.
-
-### Step 1: Deploy Firezone server
-
-In this example, a Firezone instance has been set up on a `tc2.micro`
-EC2 instance. See the
-[Deployment Guide](/docs/deploy/)
-for details on deploying Firezone. Specific to AWS, ensure:
-
-1. The security group of the Firezone EC2 instance allows outbound traffic to the
- IP of the protected resource.
-1. An Elastic IP is associated with the Firezone instance. This will be the
- source IP address of traffic routed through the Firezone instance to external destinations.
- In this case, the IP is `52.202.88.54`.
-
-
-
-### Step 2: Restrict access to the protected resource
-
-In this example, the protected resource is a self-hosted web app. Access to the
-web app is restricted to only requests from `52.202.88.54`.
-Depending on the resource, inbound traffic on different ports and traffic types
-may need to be allowed. This is outside the scope of this guide.
-
-
-
-If the protected resource is controlled by a 3rd party, please inform the 3rd
-party to allow traffic from the static IP set in Step 1 (in this case `52.202.88.54`).
-
-### Step 3: Route traffic to the protected resource through the VPN server
-
-By default, all traffic from team members will be routed through Firezone
-and will originate from the static IP set in Step 1 (in this case `52.202.88.54`).
-However, if
-[split tunneling](/docs/user-guides/use-cases/split-tunnel/)
-has been enabled, configuration may be required to ensure the destination IP of
-the protected resource is included in the `Allowed IPs`.
diff --git a/www/docs/user-guides/use-cases/nat-gateway/_whitelist-sso.mdx b/www/docs/user-guides/use-cases/nat-gateway/_whitelist-sso.mdx
deleted file mode 100644
index 605f5a616..000000000
--- a/www/docs/user-guides/use-cases/nat-gateway/_whitelist-sso.mdx
+++ /dev/null
@@ -1,89 +0,0 @@
----
-title: Restrict SSO to Firezone Users
-sidebar_position: 1
-description: Configure your identity provider to whitelist traffic from Firezone's WireGuard®-based secure access platform.
----
-
-# Restrict application authentication to VPN users
-
-Some identity providers support restricting SSO functionality
-Some identity providers support restricting SSO access to a predefined CIDR range or list of IP addresses. You can set this to the IP address of
-your Firezone gateway to restrict SSO to users connected to Firezone.
-
-This adds an additional layer of security to any service that uses
-your identity provider for SSO.
-
-We have identified a few common providers that support this
-feature and included basic instructions below on how you can set
-this up. The pre-requisites to this guide are a deployed Firezone
-server with a static IP
-([see NAT Gateway](.../nat-gateway))
-and ensuring traffic to the identity provider's SSO services are
-routed from client devices through the Firezone gateway
-([see Split Tunnel](.../split-tunnel)).
-
-## Okta
-
-Okta supports restricting SSO authentication to a "network zone" on
-a per application basis.
-
-:::note
-If you have split tunneling enabled, ensure the AllowedIPs are
-correctly configured to direct traffic to
-[Okta's IPs](https://help.okta.com/en-us/Content/Topics/Security/ip-address-allow-listing.htm)
-through the Firezone gateway.
-:::
-
-:::caution
-Sign-on policies are assigned on an application level. We advise
-excluding the Firezone application from the IP restriction policy above if Okta
-is being used for Firezone authentication.
-
-With
-[periodic authentication](../../authenticate#enforce-periodic-re-authentication)
-enabled, you may be locked out of Okta entirely when your VPN session
-expires.
-:::
-
-### Create the network zone
-
-_This section is based on Okta's
-[documentation](https://help.okta.com/oie/en-us/Content/Topics/Security/network/create-ip-zone.htm)._
-
-Navigate to **Security > Networks**. Add an **IP Zone** with the
-static IP of the Firezone Gateway in **Gateway IPs**.
-
-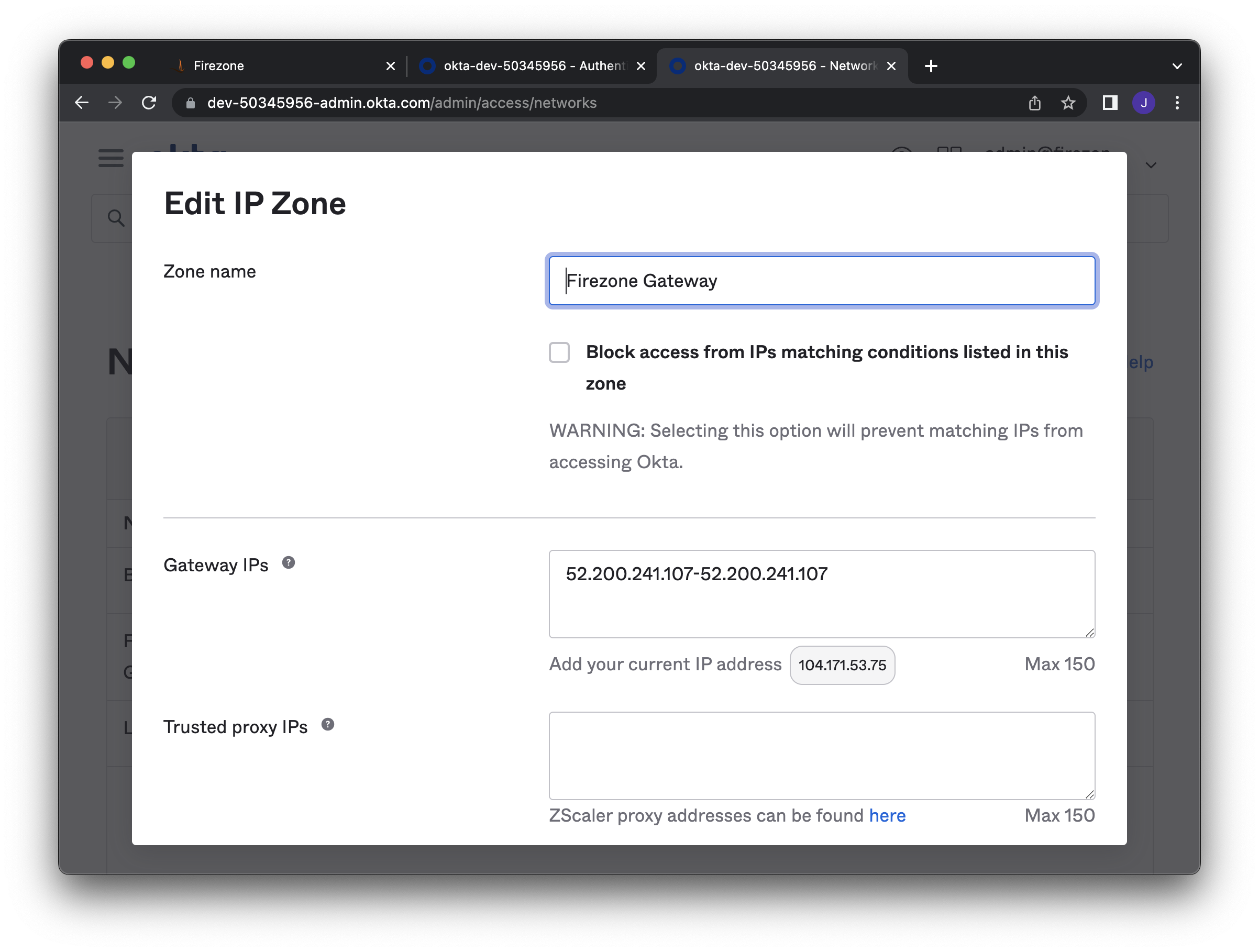
-
-### Create a sign-on policy
-
-_This section is based on Okta's
-[documentation](https://help.okta.com/oie/en-us/Content/Topics/Security/network/add-network-zone-signon-policy.htm)._
-
-Navigate to **Security > Authentication policies**. Create a new
-policy that denies access when a user
-is **NOT** on the network zone defined above.
-
-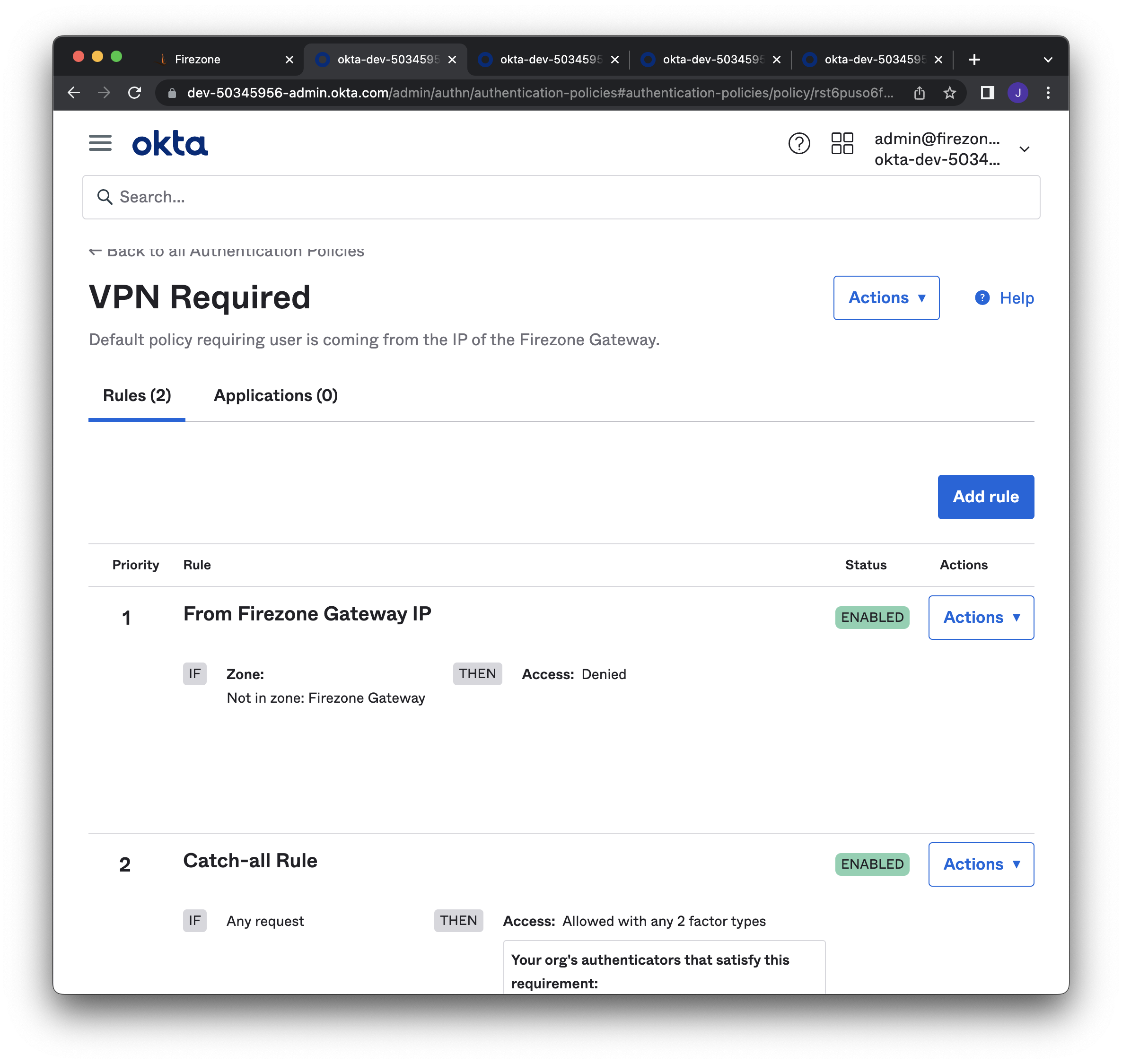
-
-### Associate sign-on policy to application
-
-Under the **Sign On** tab, set the **Authentication policy** to the
-policy defined above. Do this for applications where authentication
-should be restricted only to users on the VPN.
-
-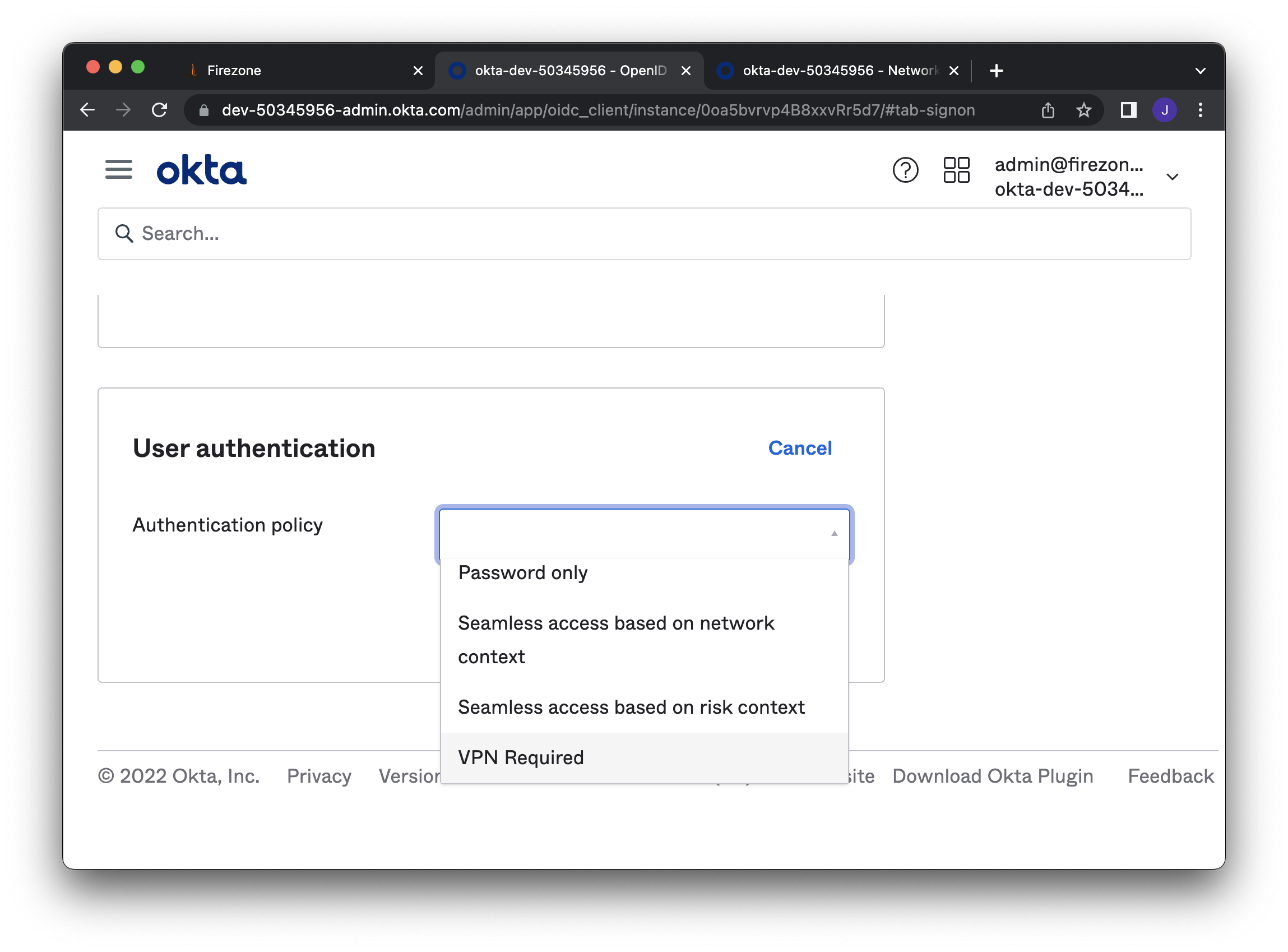
-
-### Configure VPN notification (optional)
-
-_This section is based on Okta's
-[documentation](https://help.okta.com/oie/en-us/Content/Topics/Security/network/vpn-notification.htm)._
-
-Optionally configure a notification to alert users why
-their access was denied.
-On the details page of your Okta application, configure the
-**General > VPN Notification** section.
-
-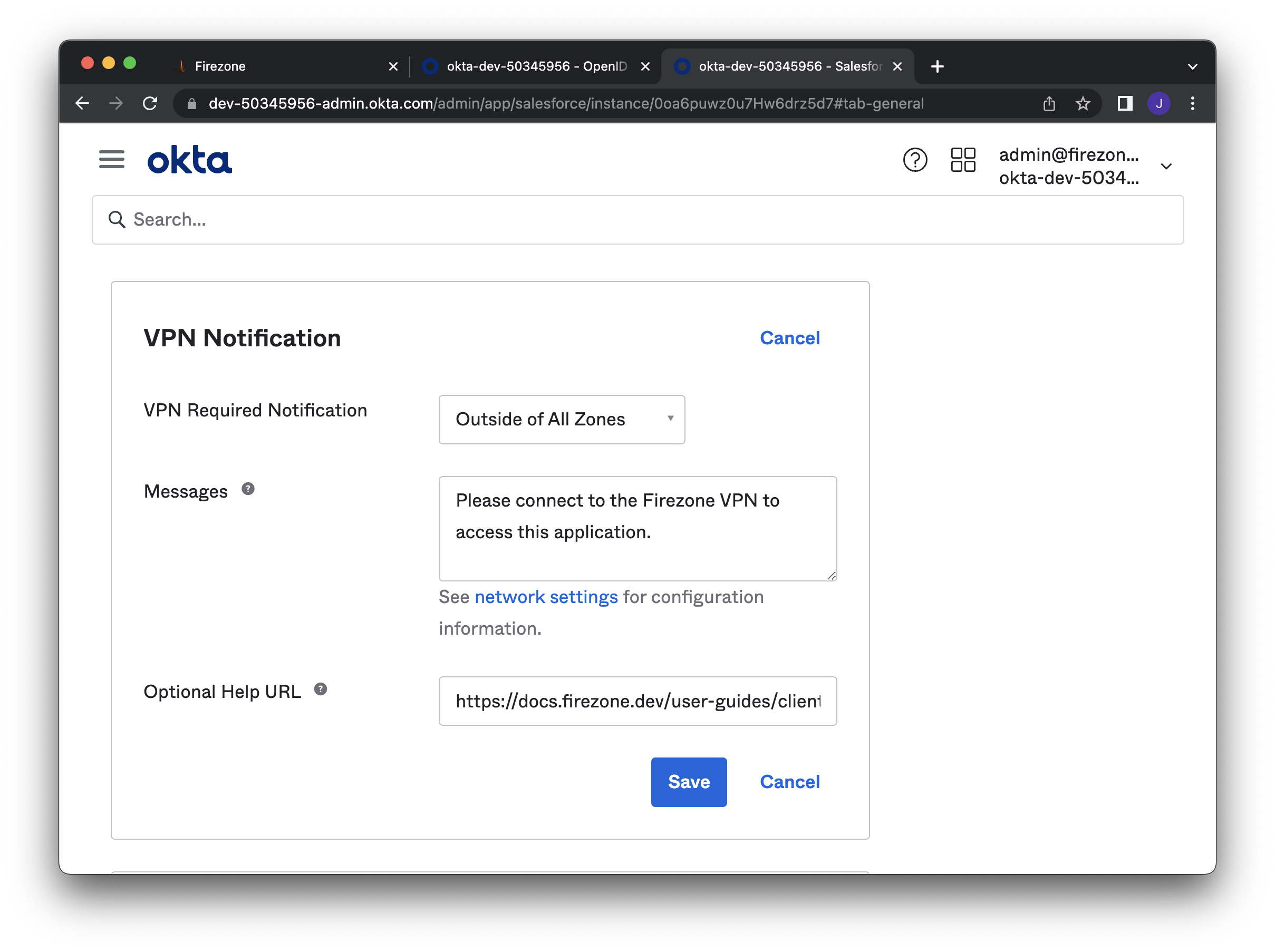
diff --git a/www/docs/user-guides/use-cases/reverse-tunnel.mdx b/www/docs/user-guides/use-cases/reverse-tunnel.mdx
deleted file mode 100644
index 2759cf518..000000000
--- a/www/docs/user-guides/use-cases/reverse-tunnel.mdx
+++ /dev/null
@@ -1,83 +0,0 @@
----
-title: Reverse Tunnel
-sidebar_position: 2
-description: Configure Firezone as a relay to connect two or more devices.
----
-
-This guide will walk through using Firezone as a relay to connect
-two devices. A typical use case for this configuration is to enable an
-administrator to access a server, container, or machine that is normally
-behind a NAT or firewall.
-
-## General case: node to node
-
-This example demonstrates a simple scenario where a tunnel is established
-between Device A and Device B.
-
-
-Start by creating Device A and Device B by navigating to `/users/[user_id]/new_device`.
-In the settings for each device, ensure the following parameters are set to the
-values listed below. You can set device settings when creating the device config
-(see [Add Devices](/docs/user-guides/add-devices/)).
-If you need to update settings on an existing device, you can do so by generating
-a new device config.
-
-Note `PersistentKeepalive` can also be set in on the
-`/settings/defaults` page for all devices.
-
-Device A
-
-- `AllowedIPs = 10.3.2.3/32`: This is the IP or range of IPs of Device B
-- `PersistentKeepalive = 25` If the device is behind a NAT, this ensures the
- device is able to keep the tunnel alive and continue to receive packets from
- the WireGuard interface. Usually a value of `25` is sufficient, but you may
- need to decrease this value depending on your environment.
-
-Device B
-
-- `AllowedIPs = 10.3.2.2/32`: This is the IP or range of IPs of Device A
-- `PersistentKeepalive = 25`
-
-## Admin case: one to many nodes
-
-This example demonstrates a scenario where Device A can communicate
-bi-directionally with Devices B through D. This configuration could represent an
-administrator or engineer accessing multiple resources
-(servers, containers, or machines) in different networks.
-
-
-
-In the settings for each device, ensure the following parameters are set to the
-values listed below. You can set device settings when creating the device config
-(see [Add Devices](/docs/user-guides/add-devices/)).
-If you need to update settings on an existing device, you can do so by generating
-a new device config.
-
-Device A (Administrator Node)
-
-- `AllowedIPs = 10.3.2.3/32, 10.3.2.4/32, 10.3.2.5/32`: This is the IP of
- devices B through D. Optionally you could set a range of IPs as long as it
- includes the IPs of Devices B through D.
-- `PersistentKeepalive = 25` If the device is behind a NAT, this ensures the
- device is able to keep the tunnel alive and continue to receive packets from
- the WireGuard interface. Usually a value of `25` is sufficient, but you may
- need to decrease this value depending on your environment.
-
-Device B
-
-- `AllowedIPs = 10.3.2.2/32`: This is the IP or range of IPs of Device A
-- `PersistentKeepalive = 25`
-
-Device C
-
-- `AllowedIPs = 10.3.2.2/32`: This is the IP or range of IPs of Device A
-- `PersistentKeepalive = 25`
-
-Device D
-
-- `AllowedIPs = 10.3.2.2/32`: This is the IP or range of IPs of Device A
-- `PersistentKeepalive = 25`
-
-## Related guides
-
-- [NAT Gateway](/docs/user-guides/use-cases/nat-gateway/)
diff --git a/www/docs/user-guides/use-cases/split-tunnel.mdx b/www/docs/user-guides/use-cases/split-tunnel.mdx
deleted file mode 100644
index 9de66e4c2..000000000
--- a/www/docs/user-guides/use-cases/split-tunnel.mdx
+++ /dev/null
@@ -1,61 +0,0 @@
----
-title: Split Tunnel VPN
-sidebar_position: 1
-description: Configure Firezone for split tunneling. Route some network traffic
- from end users through the encrypted WireGuard® tunnel.
----
-
-# Set up IP-based split tunneling with Firezone
-
-This guide will describe the steps required to enable split tunneling with
-WireGuard using Firezone so only traffic to defined IP ranges will be routed
-through the VPN.
-
-Firezone sets the `Allowed IPs` field so traffic destined for
-specific IPs are encrypted and routed through the gateway.
-
-## Step 1: Set AllowedIPs
-
-AllowedIPs can be set globally on the `/settings/default` page or individually
-for each device during creation. Changes will only apply to new WireGuard
-tunnel configurations generated by Firezone.
-
-
-
-Some examples of values in this field are:
-
-- `0.0.0.0/0, ::/0` - all network traffic will be routed to the VPN server.
-- `192.0.2.3/32` - only traffic to a single IP address
- will be routed to the VPN server.
-- `3.5.140.0/22` - only traffic to IPs in the `3.5.140.1 - 3.5.143.254` range
- will be routed to the VPN server.
- In this example, the CIDR range for the `ap-northeast-2` AWS region was used.
-
-:::note
-When deciding where to route a packet, Firezone chooses the egress
-interface corresponding to the most specific route first.
-:::
-
-## Step 2 (optional): Set the DNS server(s)
-
-You can define the DNS server(s) used by devices when the WireGuard tunnel
-is active. By default, it uses Cloudflare's DNS servers (`1.1.1.1, 1.0.0.1`).
-Visit the `/settings/default` page to override this value.
-
-For split tunneling, this may be desired if you run a DNS server that
-resolves internal hosts to private IPs reachable via Firezone.
-
-:::note
-If you wish to resolve DNS queries
-over the encrypted VPN tunnel (recommended), ensure the DNS IPs are included in `AllowedIPs`.
-:::
-
-## Step 3: Regenerate the device configurations
-
-Changes made to global settings in the **Defaults** tab are only applied to
-future device configurations generated by Firezone.
-
-Users need to regenerate device configurations to update existing devices
-for the updated configuration changes to `AllowedIPs`, `DNS`, `PersistentKeepalive`, `MTU`, and `Endpoint`.
-
-See [add device](/docs/user-guides/add-devices/) for instructions.
diff --git a/www/docusaurus.config.js b/www/docusaurus.config.js
deleted file mode 100644
index 2e4861806..000000000
--- a/www/docusaurus.config.js
+++ /dev/null
@@ -1,199 +0,0 @@
-// @ts-check
-// Note: type annotations allow type checking and IDEs autocompletion
-
-const lightCodeTheme = require("prism-react-renderer/themes/github");
-const darkCodeTheme = require("prism-react-renderer/themes/dracula");
-
-/** @type {import('@docusaurus/types').Config} */
-const config = {
- title: "firezone",
- tagline: "Open-source secure remote access built on WireGuard®",
- url: "https://www.firezone.dev",
- baseUrl: "/",
- onBrokenLinks: "throw",
- onBrokenMarkdownLinks: "warn",
- trailingSlash: true,
- favicon: "img/favicon.ico",
-
- // GitHub pages deployment config.
- // If you aren't using GitHub pages, you don't need these.
- organizationName: "firezone", // Usually your GitHub org/user name.
- projectName: "firezone", // Usually your repo name.
-
- // Even if you don't use internalization, you can use this field to set useful
- // metadata like html lang. For example, if your site is Chinese, you may want
- // to replace 'en' with 'zh-Hans'.
- i18n: {
- defaultLocale: "en",
- locales: ["en"],
- },
-
- // An array of scripts to load. The values can be either strings or plain
- // objects of attribute-value maps. The
-
diff --git a/www/static/js/posthog.js b/www/static/js/posthog.js
deleted file mode 100644
index 4a71be7f9..000000000
--- a/www/static/js/posthog.js
+++ /dev/null
@@ -1,2 +0,0 @@
-!function(t,e){var o,n,p,r;e.__SV||(window.posthog=e,e._i=[],e.init=function(i,s,a){function g(t,e){var o=e.split(".");2==o.length&&(t=t[o[0]],e=o[1]),t[e]=function(){t.push([e].concat(Array.prototype.slice.call(arguments,0)))}}(p=t.createElement("script")).type="text/javascript",p.async=!0,p.src=s.api_host+"/static/array.js",(r=t.getElementsByTagName("script")[0]).parentNode.insertBefore(p,r);var u=e;for(void 0!==a?u=e[a]=[]:a="posthog",u.people=u.people||[],u.toString=function(t){var e="posthog";return"posthog"!==a&&(e+="."+a),t||(e+=" (stub)"),e},u.people.toString=function(){return u.toString(1)+".people (stub)"},o="capture identify alias people.set people.set_once set_config register register_once unregister opt_out_capturing has_opted_out_capturing opt_in_capturing reset isFeatureEnabled onFeatureFlags".split(" "),n=0;n= 1.43.0 < 2"
-
-compression@^1.7.4:
- version "1.7.4"
- resolved "https://registry.yarnpkg.com/compression/-/compression-1.7.4.tgz#95523eff170ca57c29a0ca41e6fe131f41e5bb8f"
- integrity sha512-jaSIDzP9pZVS4ZfQ+TzvtiWhdpFhE2RDHz8QJkpX9SIpLq88VueF5jJw6t+6CUQcAoA6t+x89MLrWAqpfDE8iQ==
- dependencies:
- accepts "~1.3.5"
- bytes "3.0.0"
- compressible "~2.0.16"
- debug "2.6.9"
- on-headers "~1.0.2"
- safe-buffer "5.1.2"
- vary "~1.1.2"
-
-concat-map@0.0.1:
- version "0.0.1"
- resolved "https://registry.yarnpkg.com/concat-map/-/concat-map-0.0.1.tgz#d8a96bd77fd68df7793a73036a3ba0d5405d477b"
- integrity sha512-/Srv4dswyQNBfohGpz9o6Yb3Gz3SrUDqBH5rTuhGR7ahtlbYKnVxw2bCFMRljaA7EXHaXZ8wsHdodFvbkhKmqg==
-
-concat-stream@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/concat-stream/-/concat-stream-2.0.0.tgz#414cf5af790a48c60ab9be4527d56d5e41133cb1"
- integrity sha512-MWufYdFw53ccGjCA+Ol7XJYpAlW6/prSMzuPOTRnJGcGzuhLn4Scrz7qf6o8bROZ514ltazcIFJZevcfbo0x7A==
- dependencies:
- buffer-from "^1.0.0"
- inherits "^2.0.3"
- readable-stream "^3.0.2"
- typedarray "^0.0.6"
-
-configstore@^5.0.1:
- version "5.0.1"
- resolved "https://registry.yarnpkg.com/configstore/-/configstore-5.0.1.tgz#d365021b5df4b98cdd187d6a3b0e3f6a7cc5ed96"
- integrity sha512-aMKprgk5YhBNyH25hj8wGt2+D52Sw1DRRIzqBwLp2Ya9mFmY8KPvvtvmna8SxVR9JMZ4kzMD68N22vlaRpkeFA==
- dependencies:
- dot-prop "^5.2.0"
- graceful-fs "^4.1.2"
- make-dir "^3.0.0"
- unique-string "^2.0.0"
- write-file-atomic "^3.0.0"
- xdg-basedir "^4.0.0"
-
-connect-history-api-fallback@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/connect-history-api-fallback/-/connect-history-api-fallback-2.0.0.tgz#647264845251a0daf25b97ce87834cace0f5f1c8"
- integrity sha512-U73+6lQFmfiNPrYbXqr6kZ1i1wiRqXnp2nhMsINseWXO8lDau0LGEffJ8kQi4EjLZympVgRdvqjAgiZ1tgzDDA==
-
-consola@^2.15.3:
- version "2.15.3"
- resolved "https://registry.yarnpkg.com/consola/-/consola-2.15.3.tgz#2e11f98d6a4be71ff72e0bdf07bd23e12cb61550"
- integrity sha512-9vAdYbHj6x2fLKC4+oPH0kFzY/orMZyG2Aj+kNylHxKGJ/Ed4dpNyAQYwJOdqO4zdM7XpVHmyejQDcQHrnuXbw==
-
-content-disposition@0.5.2:
- version "0.5.2"
- resolved "https://registry.yarnpkg.com/content-disposition/-/content-disposition-0.5.2.tgz#0cf68bb9ddf5f2be7961c3a85178cb85dba78cb4"
- integrity sha512-kRGRZw3bLlFISDBgwTSA1TMBFN6J6GWDeubmDE3AF+3+yXL8hTWv8r5rkLbqYXY4RjPk/EzHnClI3zQf1cFmHA==
-
-content-disposition@0.5.4:
- version "0.5.4"
- resolved "https://registry.yarnpkg.com/content-disposition/-/content-disposition-0.5.4.tgz#8b82b4efac82512a02bb0b1dcec9d2c5e8eb5bfe"
- integrity sha512-FveZTNuGw04cxlAiWbzi6zTAL/lhehaWbTtgluJh4/E95DqMwTmha3KZN1aAWA8cFIhHzMZUvLevkw5Rqk+tSQ==
- dependencies:
- safe-buffer "5.2.1"
-
-content-type@~1.0.4:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/content-type/-/content-type-1.0.5.tgz#8b773162656d1d1086784c8f23a54ce6d73d7918"
- integrity sha512-nTjqfcBFEipKdXCv4YDQWCfmcLZKm81ldF0pAopTvyrFGVbcR6P/VAAd5G7N+0tTr8QqiU0tFadD6FK4NtJwOA==
-
-convert-source-map@^1.7.0:
- version "1.9.0"
- resolved "https://registry.yarnpkg.com/convert-source-map/-/convert-source-map-1.9.0.tgz#7faae62353fb4213366d0ca98358d22e8368b05f"
- integrity sha512-ASFBup0Mz1uyiIjANan1jzLQami9z1PoYSZCiiYW2FczPbenXc45FZdBZLzOT+r6+iciuEModtmCti+hjaAk0A==
-
-cookie-signature@1.0.6:
- version "1.0.6"
- resolved "https://registry.yarnpkg.com/cookie-signature/-/cookie-signature-1.0.6.tgz#e303a882b342cc3ee8ca513a79999734dab3ae2c"
- integrity sha512-QADzlaHc8icV8I7vbaJXJwod9HWYp8uCqf1xa4OfNu1T7JVxQIrUgOWtHdNDtPiywmFbiS12VjotIXLrKM3orQ==
-
-cookie@0.5.0:
- version "0.5.0"
- resolved "https://registry.yarnpkg.com/cookie/-/cookie-0.5.0.tgz#d1f5d71adec6558c58f389987c366aa47e994f8b"
- integrity sha512-YZ3GUyn/o8gfKJlnlX7g7xq4gyO6OSuhGPKaaGssGB2qgDUS0gPgtTvoyZLTt9Ab6dC4hfc9dV5arkvc/OCmrw==
-
-copy-text-to-clipboard@^3.0.1:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/copy-text-to-clipboard/-/copy-text-to-clipboard-3.0.1.tgz#8cbf8f90e0a47f12e4a24743736265d157bce69c"
- integrity sha512-rvVsHrpFcL4F2P8ihsoLdFHmd404+CMg71S756oRSeQgqk51U3kicGdnvfkrxva0xXH92SjGS62B0XIJsbh+9Q==
-
-copy-webpack-plugin@^11.0.0:
- version "11.0.0"
- resolved "https://registry.yarnpkg.com/copy-webpack-plugin/-/copy-webpack-plugin-11.0.0.tgz#96d4dbdb5f73d02dd72d0528d1958721ab72e04a"
- integrity sha512-fX2MWpamkW0hZxMEg0+mYnA40LTosOSa5TqZ9GYIBzyJa9C3QUaMPSE2xAi/buNr8u89SfD9wHSQVBzrRa/SOQ==
- dependencies:
- fast-glob "^3.2.11"
- glob-parent "^6.0.1"
- globby "^13.1.1"
- normalize-path "^3.0.0"
- schema-utils "^4.0.0"
- serialize-javascript "^6.0.0"
-
-core-js-compat@^3.25.1:
- version "3.28.0"
- resolved "https://registry.yarnpkg.com/core-js-compat/-/core-js-compat-3.28.0.tgz#c08456d854608a7264530a2afa281fadf20ecee6"
- integrity sha512-myzPgE7QodMg4nnd3K1TDoES/nADRStM8Gpz0D6nhkwbmwEnE0ZGJgoWsvQ722FR8D7xS0n0LV556RcEicjTyg==
- dependencies:
- browserslist "^4.21.5"
-
-core-js-pure@^3.25.1:
- version "3.28.0"
- resolved "https://registry.yarnpkg.com/core-js-pure/-/core-js-pure-3.28.0.tgz#4ef2888475b6c856ef6f5aeef8b4f618b76ad048"
- integrity sha512-DSOVleA9/v3LNj/vFxAPfUHttKTzrB2RXhAPvR5TPXn4vrra3Z2ssytvRyt8eruJwAfwAiFADEbrjcRdcvPLQQ==
-
-core-js@^3.23.3:
- version "3.28.0"
- resolved "https://registry.yarnpkg.com/core-js/-/core-js-3.28.0.tgz#ed8b9e99c273879fdfff0edfc77ee709a5800e4a"
- integrity sha512-GiZn9D4Z/rSYvTeg1ljAIsEqFm0LaN9gVtwDCrKL80zHtS31p9BAjmTxVqTQDMpwlMolJZOFntUG2uwyj7DAqw==
-
-core-util-is@~1.0.0:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/core-util-is/-/core-util-is-1.0.3.tgz#a6042d3634c2b27e9328f837b965fac83808db85"
- integrity sha512-ZQBvi1DcpJ4GDqanjucZ2Hj3wEO5pZDS89BWbkcrvdxksJorwUDDZamX9ldFkp9aw2lmBDLgkObEA4DWNJ9FYQ==
-
-cosmiconfig@^6.0.0:
- version "6.0.0"
- resolved "https://registry.yarnpkg.com/cosmiconfig/-/cosmiconfig-6.0.0.tgz#da4fee853c52f6b1e6935f41c1a2fc50bd4a9982"
- integrity sha512-xb3ZL6+L8b9JLLCx3ZdoZy4+2ECphCMo2PwqgP1tlfVq6M6YReyzBJtvWWtbDSpNr9hn96pkCiZqUcFEc+54Qg==
- dependencies:
- "@types/parse-json" "^4.0.0"
- import-fresh "^3.1.0"
- parse-json "^5.0.0"
- path-type "^4.0.0"
- yaml "^1.7.2"
-
-cosmiconfig@^7.0.0, cosmiconfig@^7.0.1:
- version "7.1.0"
- resolved "https://registry.yarnpkg.com/cosmiconfig/-/cosmiconfig-7.1.0.tgz#1443b9afa596b670082ea46cbd8f6a62b84635f6"
- integrity sha512-AdmX6xUzdNASswsFtmwSt7Vj8po9IuqXm0UXz7QKPuEUmPB4XyjGfaAr2PSuELMwkRMVH1EpIkX5bTZGRB3eCA==
- dependencies:
- "@types/parse-json" "^4.0.0"
- import-fresh "^3.2.1"
- parse-json "^5.0.0"
- path-type "^4.0.0"
- yaml "^1.10.0"
-
-cross-fetch@^3.1.5:
- version "3.1.5"
- resolved "https://registry.yarnpkg.com/cross-fetch/-/cross-fetch-3.1.5.tgz#e1389f44d9e7ba767907f7af8454787952ab534f"
- integrity sha512-lvb1SBsI0Z7GDwmuid+mU3kWVBwTVUbe7S0H52yaaAdQOXq2YktTCZdlAcNKFzE6QtRz0snpw9bNiPeOIkkQvw==
- dependencies:
- node-fetch "2.6.7"
-
-cross-spawn@^7.0.3:
- version "7.0.3"
- resolved "https://registry.yarnpkg.com/cross-spawn/-/cross-spawn-7.0.3.tgz#f73a85b9d5d41d045551c177e2882d4ac85728a6"
- integrity sha512-iRDPJKUPVEND7dHPO8rkbOnPpyDygcDFtWjpeWNCgy8WP2rXcxXL8TskReQl6OrB2G7+UJrags1q15Fudc7G6w==
- dependencies:
- path-key "^3.1.0"
- shebang-command "^2.0.0"
- which "^2.0.1"
-
-crypto-random-string@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/crypto-random-string/-/crypto-random-string-2.0.0.tgz#ef2a7a966ec11083388369baa02ebead229b30d5"
- integrity sha512-v1plID3y9r/lPhviJ1wrXpLeyUIGAZ2SHNYTEapm7/8A9nLPoyvVp3RK/EPFqn5kEznyWgYZNsRtYYIWbuG8KA==
-
-css-declaration-sorter@^6.3.1:
- version "6.3.1"
- resolved "https://registry.yarnpkg.com/css-declaration-sorter/-/css-declaration-sorter-6.3.1.tgz#be5e1d71b7a992433fb1c542c7a1b835e45682ec"
- integrity sha512-fBffmak0bPAnyqc/HO8C3n2sHrp9wcqQz6ES9koRF2/mLOVAx9zIQ3Y7R29sYCteTPqMCwns4WYQoCX91Xl3+w==
-
-css-loader@^6.7.1:
- version "6.7.3"
- resolved "https://registry.yarnpkg.com/css-loader/-/css-loader-6.7.3.tgz#1e8799f3ccc5874fdd55461af51137fcc5befbcd"
- integrity sha512-qhOH1KlBMnZP8FzRO6YCH9UHXQhVMcEGLyNdb7Hv2cpcmJbW0YrddO+tG1ab5nT41KpHIYGsbeHqxB9xPu1pKQ==
- dependencies:
- icss-utils "^5.1.0"
- postcss "^8.4.19"
- postcss-modules-extract-imports "^3.0.0"
- postcss-modules-local-by-default "^4.0.0"
- postcss-modules-scope "^3.0.0"
- postcss-modules-values "^4.0.0"
- postcss-value-parser "^4.2.0"
- semver "^7.3.8"
-
-css-minimizer-webpack-plugin@4.1.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/css-minimizer-webpack-plugin/-/css-minimizer-webpack-plugin-4.1.0.tgz#2ab9f7d8148c48f5d498604025e6e62cf9528855"
- integrity sha512-Zd+yz4nta4GXi3pMqF6skO8kjzuCUbr62z8SLMGZZtxWxTGTLopOiabPGNDEyjHCRhnhdA1EfHmqLa2Oekjtng==
- dependencies:
- cssnano "^5.1.8"
- jest-worker "^27.5.1"
- postcss "^8.4.13"
- schema-utils "^4.0.0"
- serialize-javascript "^6.0.0"
- source-map "^0.6.1"
-
-css-minimizer-webpack-plugin@^4.0.0:
- version "4.2.2"
- resolved "https://registry.yarnpkg.com/css-minimizer-webpack-plugin/-/css-minimizer-webpack-plugin-4.2.2.tgz#79f6199eb5adf1ff7ba57f105e3752d15211eb35"
- integrity sha512-s3Of/4jKfw1Hj9CxEO1E5oXhQAxlayuHO2y/ML+C6I9sQ7FdzfEV6QgMLN3vI+qFsjJGIAFLKtQK7t8BOXAIyA==
- dependencies:
- cssnano "^5.1.8"
- jest-worker "^29.1.2"
- postcss "^8.4.17"
- schema-utils "^4.0.0"
- serialize-javascript "^6.0.0"
- source-map "^0.6.1"
-
-css-select@^4.1.3:
- version "4.3.0"
- resolved "https://registry.yarnpkg.com/css-select/-/css-select-4.3.0.tgz#db7129b2846662fd8628cfc496abb2b59e41529b"
- integrity sha512-wPpOYtnsVontu2mODhA19JrqWxNsfdatRKd64kmpRbQgh1KtItko5sTnEpPdpSaJszTOhEMlF/RPz28qj4HqhQ==
- dependencies:
- boolbase "^1.0.0"
- css-what "^6.0.1"
- domhandler "^4.3.1"
- domutils "^2.8.0"
- nth-check "^2.0.1"
-
-css-select@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/css-select/-/css-select-5.1.0.tgz#b8ebd6554c3637ccc76688804ad3f6a6fdaea8a6"
- integrity sha512-nwoRF1rvRRnnCqqY7updORDsuqKzqYJ28+oSMaJMMgOauh3fvwHqMS7EZpIPqK8GL+g9mKxF1vP/ZjSeNjEVHg==
- dependencies:
- boolbase "^1.0.0"
- css-what "^6.1.0"
- domhandler "^5.0.2"
- domutils "^3.0.1"
- nth-check "^2.0.1"
-
-css-tree@^1.1.2, css-tree@^1.1.3:
- version "1.1.3"
- resolved "https://registry.yarnpkg.com/css-tree/-/css-tree-1.1.3.tgz#eb4870fb6fd7707327ec95c2ff2ab09b5e8db91d"
- integrity sha512-tRpdppF7TRazZrjJ6v3stzv93qxRcSsFmW6cX0Zm2NVKpxE1WV1HblnghVv9TreireHkqI/VDEsfolRF1p6y7Q==
- dependencies:
- mdn-data "2.0.14"
- source-map "^0.6.1"
-
-css-what@^6.0.1, css-what@^6.1.0:
- version "6.1.0"
- resolved "https://registry.yarnpkg.com/css-what/-/css-what-6.1.0.tgz#fb5effcf76f1ddea2c81bdfaa4de44e79bac70f4"
- integrity sha512-HTUrgRJ7r4dsZKU6GjmpfRK1O76h97Z8MfS1G0FozR+oF2kG6Vfe8JE6zwrkbxigziPHinCJ+gCPjA9EaBDtRw==
-
-cssesc@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/cssesc/-/cssesc-3.0.0.tgz#37741919903b868565e1c09ea747445cd18983ee"
- integrity sha512-/Tb/JcjK111nNScGob5MNtsntNM1aCNUDipB/TkwZFhyDrrE47SOx/18wF2bbjgc3ZzCSKW1T5nt5EbFoAz/Vg==
-
-cssnano-preset-advanced@^5.3.8:
- version "5.3.9"
- resolved "https://registry.yarnpkg.com/cssnano-preset-advanced/-/cssnano-preset-advanced-5.3.9.tgz#99e1cdf81a467a5e6c366cfc6d874a166c4d9a67"
- integrity sha512-njnh4pp1xCsibJcEHnWZb4EEzni0ePMqPuPNyuWT4Z+YeXmsgqNuTPIljXFEXhxGsWs9183JkXgHxc1TcsahIg==
- dependencies:
- autoprefixer "^10.4.12"
- cssnano-preset-default "^5.2.13"
- postcss-discard-unused "^5.1.0"
- postcss-merge-idents "^5.1.1"
- postcss-reduce-idents "^5.2.0"
- postcss-zindex "^5.1.0"
-
-cssnano-preset-default@^5.2.13:
- version "5.2.13"
- resolved "https://registry.yarnpkg.com/cssnano-preset-default/-/cssnano-preset-default-5.2.13.tgz#e7353b0c57975d1bdd97ac96e68e5c1b8c68e990"
- integrity sha512-PX7sQ4Pb+UtOWuz8A1d+Rbi+WimBIxJTRyBdgGp1J75VU0r/HFQeLnMYgHiCAp6AR4rqrc7Y4R+1Rjk3KJz6DQ==
- dependencies:
- css-declaration-sorter "^6.3.1"
- cssnano-utils "^3.1.0"
- postcss-calc "^8.2.3"
- postcss-colormin "^5.3.0"
- postcss-convert-values "^5.1.3"
- postcss-discard-comments "^5.1.2"
- postcss-discard-duplicates "^5.1.0"
- postcss-discard-empty "^5.1.1"
- postcss-discard-overridden "^5.1.0"
- postcss-merge-longhand "^5.1.7"
- postcss-merge-rules "^5.1.3"
- postcss-minify-font-values "^5.1.0"
- postcss-minify-gradients "^5.1.1"
- postcss-minify-params "^5.1.4"
- postcss-minify-selectors "^5.2.1"
- postcss-normalize-charset "^5.1.0"
- postcss-normalize-display-values "^5.1.0"
- postcss-normalize-positions "^5.1.1"
- postcss-normalize-repeat-style "^5.1.1"
- postcss-normalize-string "^5.1.0"
- postcss-normalize-timing-functions "^5.1.0"
- postcss-normalize-unicode "^5.1.1"
- postcss-normalize-url "^5.1.0"
- postcss-normalize-whitespace "^5.1.1"
- postcss-ordered-values "^5.1.3"
- postcss-reduce-initial "^5.1.1"
- postcss-reduce-transforms "^5.1.0"
- postcss-svgo "^5.1.0"
- postcss-unique-selectors "^5.1.1"
-
-cssnano-utils@^3.1.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/cssnano-utils/-/cssnano-utils-3.1.0.tgz#95684d08c91511edfc70d2636338ca37ef3a6861"
- integrity sha512-JQNR19/YZhz4psLX/rQ9M83e3z2Wf/HdJbryzte4a3NSuafyp9w/I4U+hx5C2S9g41qlstH7DEWnZaaj83OuEA==
-
-cssnano@^5.1.12, cssnano@^5.1.8:
- version "5.1.14"
- resolved "https://registry.yarnpkg.com/cssnano/-/cssnano-5.1.14.tgz#07b0af6da73641276fe5a6d45757702ebae2eb05"
- integrity sha512-Oou7ihiTocbKqi0J1bB+TRJIQX5RMR3JghA8hcWSw9mjBLQ5Y3RWqEDoYG3sRNlAbCIXpqMoZGbq5KDR3vdzgw==
- dependencies:
- cssnano-preset-default "^5.2.13"
- lilconfig "^2.0.3"
- yaml "^1.10.2"
-
-csso@^4.2.0:
- version "4.2.0"
- resolved "https://registry.yarnpkg.com/csso/-/csso-4.2.0.tgz#ea3a561346e8dc9f546d6febedd50187cf389529"
- integrity sha512-wvlcdIbf6pwKEk7vHj8/Bkc0B4ylXZruLvOgs9doS5eOsOpuodOV2zJChSpkp+pRpYQLQMeF04nr3Z68Sta9jA==
- dependencies:
- css-tree "^1.1.2"
-
-csstype@^3.0.2, csstype@^3.1.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/csstype/-/csstype-3.1.1.tgz#841b532c45c758ee546a11d5bd7b7b473c8c30b9"
- integrity sha512-DJR/VvkAvSZW9bTouZue2sSxDwdTN92uHjqeKVm+0dAqdfNykRzQ95tay8aXMBAAPpUiq4Qcug2L7neoRh2Egw==
-
-debug@2.6.9, debug@^2.6.0:
- version "2.6.9"
- resolved "https://registry.yarnpkg.com/debug/-/debug-2.6.9.tgz#5d128515df134ff327e90a4c93f4e077a536341f"
- integrity sha512-bC7ElrdJaJnPbAP+1EotYvqZsb3ecl5wi6Bfi6BJTUcNowp6cvspg0jXznRTKDjm/E7AdgFBVeAPVMNcKGsHMA==
- dependencies:
- ms "2.0.0"
-
-debug@4, debug@^4.0.0, debug@^4.1.0, debug@^4.1.1:
- version "4.3.4"
- resolved "https://registry.yarnpkg.com/debug/-/debug-4.3.4.tgz#1319f6579357f2338d3337d2cdd4914bb5dcc865"
- integrity sha512-PRWFHuSU3eDtQJPvnNY7Jcket1j0t5OuOsFzPPzsekD52Zl8qUfFIPEiswXqIvHWGVHOgX+7G/vCNNhehwxfkQ==
- dependencies:
- ms "2.1.2"
-
-decode-named-character-reference@^1.0.0:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/decode-named-character-reference/-/decode-named-character-reference-1.0.2.tgz#daabac9690874c394c81e4162a0304b35d824f0e"
- integrity sha512-O8x12RzrUF8xyVcY0KJowWsmaJxQbmy0/EtnNtHRpsOcT7dFk5W598coHqBVpmWo1oQQfsCqfCmkZN5DJrZVdg==
- dependencies:
- character-entities "^2.0.0"
-
-decompress-response@^3.3.0:
- version "3.3.0"
- resolved "https://registry.yarnpkg.com/decompress-response/-/decompress-response-3.3.0.tgz#80a4dd323748384bfa248083622aedec982adff3"
- integrity sha512-BzRPQuY1ip+qDonAOz42gRm/pg9F768C+npV/4JOsxRC2sq+Rlk+Q4ZCAsOhnIaMrgarILY+RMUIvMmmX1qAEA==
- dependencies:
- mimic-response "^1.0.0"
-
-deep-extend@^0.6.0:
- version "0.6.0"
- resolved "https://registry.yarnpkg.com/deep-extend/-/deep-extend-0.6.0.tgz#c4fa7c95404a17a9c3e8ca7e1537312b736330ac"
- integrity sha512-LOHxIOaPYdHlJRtCQfDIVZtfw/ufM8+rVj649RIHzcm/vGwQRXFt6OPqIFWsm2XEMrNIEtWR64sY1LEKD2vAOA==
-
-deepmerge@^4.2.2:
- version "4.3.0"
- resolved "https://registry.yarnpkg.com/deepmerge/-/deepmerge-4.3.0.tgz#65491893ec47756d44719ae520e0e2609233b59b"
- integrity sha512-z2wJZXrmeHdvYJp/Ux55wIjqo81G5Bp4c+oELTW+7ar6SogWHajt5a9gO3s3IDaGSAXjDk0vlQKN3rms8ab3og==
-
-default-gateway@^6.0.3:
- version "6.0.3"
- resolved "https://registry.yarnpkg.com/default-gateway/-/default-gateway-6.0.3.tgz#819494c888053bdb743edbf343d6cdf7f2943a71"
- integrity sha512-fwSOJsbbNzZ/CUFpqFBqYfYNLj1NbMPm8MMCIzHjC83iSJRBEGmDUxU+WP661BaBQImeC2yHwXtz+P/O9o+XEg==
- dependencies:
- execa "^5.0.0"
-
-defer-to-connect@^1.0.1:
- version "1.1.3"
- resolved "https://registry.yarnpkg.com/defer-to-connect/-/defer-to-connect-1.1.3.tgz#331ae050c08dcf789f8c83a7b81f0ed94f4ac591"
- integrity sha512-0ISdNousHvZT2EiFlZeZAHBUvSxmKswVCEf8hW7KWgG4a8MVEu/3Vb6uWYozkjylyCxe0JBIiRB1jV45S70WVQ==
-
-define-lazy-prop@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/define-lazy-prop/-/define-lazy-prop-2.0.0.tgz#3f7ae421129bcaaac9bc74905c98a0009ec9ee7f"
- integrity sha512-Ds09qNh8yw3khSjiJjiUInaGX9xlqZDY7JVryGxdxV7NPeuqQfplOpQ66yJFZut3jLa5zOwkXw1g9EI2uKh4Og==
-
-define-properties@^1.1.4:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/define-properties/-/define-properties-1.2.0.tgz#52988570670c9eacedd8064f4a990f2405849bd5"
- integrity sha512-xvqAVKGfT1+UAvPwKTVw/njhdQ8ZhXK4lI0bCIuCMrp2up9nPnaDftrLtmpTazqd1o+UY4zgzU+avtMbDP+ldA==
- dependencies:
- has-property-descriptors "^1.0.0"
- object-keys "^1.1.1"
-
-del@^6.1.1:
- version "6.1.1"
- resolved "https://registry.yarnpkg.com/del/-/del-6.1.1.tgz#3b70314f1ec0aa325c6b14eb36b95786671edb7a"
- integrity sha512-ua8BhapfP0JUJKC/zV9yHHDW/rDoDxP4Zhn3AkA6/xT6gY7jYXJiaeyBZznYVujhZZET+UgcbZiQ7sN3WqcImg==
- dependencies:
- globby "^11.0.1"
- graceful-fs "^4.2.4"
- is-glob "^4.0.1"
- is-path-cwd "^2.2.0"
- is-path-inside "^3.0.2"
- p-map "^4.0.0"
- rimraf "^3.0.2"
- slash "^3.0.0"
-
-depd@2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/depd/-/depd-2.0.0.tgz#b696163cc757560d09cf22cc8fad1571b79e76df"
- integrity sha512-g7nH6P6dyDioJogAAGprGpCtVImJhpPk/roCzdb3fIh61/s/nPsfR6onyMwkCAR/OlC3yBC0lESvUoQEAssIrw==
-
-depd@~1.1.2:
- version "1.1.2"
- resolved "https://registry.yarnpkg.com/depd/-/depd-1.1.2.tgz#9bcd52e14c097763e749b274c4346ed2e560b5a9"
- integrity sha512-7emPTl6Dpo6JRXOXjLRxck+FlLRX5847cLKEn00PLAgc3g2hTZZgr+e4c2v6QpSmLeFP3n5yUo7ft6avBK/5jQ==
-
-dequal@^2.0.0:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/dequal/-/dequal-2.0.3.tgz#2644214f1997d39ed0ee0ece72335490a7ac67be"
- integrity sha512-0je+qPKHEMohvfRTCEo3CrPG6cAzAYgmzKyxRiYSSDkS6eGJdyVJm7WaYA5ECaAD9wLB2T4EEeymA5aFVcYXCA==
-
-destroy@1.2.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/destroy/-/destroy-1.2.0.tgz#4803735509ad8be552934c67df614f94e66fa015"
- integrity sha512-2sJGJTaXIIaR1w4iJSNoN0hnMY7Gpc/n8D4qSCJw8QqFWXf7cuAgnEHxBpweaVcPevC2l3KpjYCx3NypQQgaJg==
-
-detab@2.0.4:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/detab/-/detab-2.0.4.tgz#b927892069aff405fbb9a186fe97a44a92a94b43"
- integrity sha512-8zdsQA5bIkoRECvCrNKPla84lyoR7DSAyf7p0YgXzBO9PDJx8KntPUay7NS6yp+KdxdVtiE5SpHKtbp2ZQyA9g==
- dependencies:
- repeat-string "^1.5.4"
-
-detect-node@^2.0.4:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/detect-node/-/detect-node-2.1.0.tgz#c9c70775a49c3d03bc2c06d9a73be550f978f8b1"
- integrity sha512-T0NIuQpnTvFDATNuHN5roPwSBG83rFsuO+MXXH9/3N1eFbn4wcPjttvjMLEPWJ0RGUYgQE7cGgS3tNxbqCGM7g==
-
-detect-port-alt@^1.1.6:
- version "1.1.6"
- resolved "https://registry.yarnpkg.com/detect-port-alt/-/detect-port-alt-1.1.6.tgz#24707deabe932d4a3cf621302027c2b266568275"
- integrity sha512-5tQykt+LqfJFBEYaDITx7S7cR7mJ/zQmLXZ2qt5w04ainYZw6tBf9dBunMjVeVOdYVRUzUOE4HkY5J7+uttb5Q==
- dependencies:
- address "^1.0.1"
- debug "^2.6.0"
-
-detect-port@^1.3.0:
- version "1.5.1"
- resolved "https://registry.yarnpkg.com/detect-port/-/detect-port-1.5.1.tgz#451ca9b6eaf20451acb0799b8ab40dff7718727b"
- integrity sha512-aBzdj76lueB6uUst5iAs7+0H/oOjqI5D16XUWxlWMIMROhcM0rfsNVk93zTngq1dDNpoXRr++Sus7ETAExppAQ==
- dependencies:
- address "^1.0.1"
- debug "4"
-
-diff@^5.0.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/diff/-/diff-5.1.0.tgz#bc52d298c5ea8df9194800224445ed43ffc87e40"
- integrity sha512-D+mk+qE8VC/PAUrlAU34N+VfXev0ghe5ywmpqrawphmVZc1bEfn56uo9qpyGp1p4xpzOHkSW4ztBd6L7Xx4ACw==
-
-dir-glob@^3.0.1:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/dir-glob/-/dir-glob-3.0.1.tgz#56dbf73d992a4a93ba1584f4534063fd2e41717f"
- integrity sha512-WkrWp9GR4KXfKGYzOLmTuGVi1UWFfws377n9cc55/tb6DuqyF6pcQ5AbiHEshaDpY9v6oaSr2XCDidGmMwdzIA==
- dependencies:
- path-type "^4.0.0"
-
-dns-equal@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/dns-equal/-/dns-equal-1.0.0.tgz#b39e7f1da6eb0a75ba9c17324b34753c47e0654d"
- integrity sha512-z+paD6YUQsk+AbGCEM4PrOXSss5gd66QfcVBFTKR/HpFL9jCqikS94HYwKww6fQyO7IxrIIyUu+g0Ka9tUS2Cg==
-
-dns-packet@^5.2.2:
- version "5.4.0"
- resolved "https://registry.yarnpkg.com/dns-packet/-/dns-packet-5.4.0.tgz#1f88477cf9f27e78a213fb6d118ae38e759a879b"
- integrity sha512-EgqGeaBB8hLiHLZtp/IbaDQTL8pZ0+IvwzSHA6d7VyMDM+B9hgddEMa9xjK5oYnw0ci0JQ6g2XCD7/f6cafU6g==
- dependencies:
- "@leichtgewicht/ip-codec" "^2.0.1"
-
-dom-converter@^0.2.0:
- version "0.2.0"
- resolved "https://registry.yarnpkg.com/dom-converter/-/dom-converter-0.2.0.tgz#6721a9daee2e293682955b6afe416771627bb768"
- integrity sha512-gd3ypIPfOMr9h5jIKq8E3sHOTCjeirnl0WK5ZdS1AW0Odt0b1PaWaHdJ4Qk4klv+YB9aJBS7mESXjFoDQPu6DA==
- dependencies:
- utila "~0.4"
-
-dom-serializer@^1.0.1:
- version "1.4.1"
- resolved "https://registry.yarnpkg.com/dom-serializer/-/dom-serializer-1.4.1.tgz#de5d41b1aea290215dc45a6dae8adcf1d32e2d30"
- integrity sha512-VHwB3KfrcOOkelEG2ZOfxqLZdfkil8PtJi4P8N2MMXucZq2yLp75ClViUlOVwyoHEDjYU433Aq+5zWP61+RGag==
- dependencies:
- domelementtype "^2.0.1"
- domhandler "^4.2.0"
- entities "^2.0.0"
-
-dom-serializer@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/dom-serializer/-/dom-serializer-2.0.0.tgz#e41b802e1eedf9f6cae183ce5e622d789d7d8e53"
- integrity sha512-wIkAryiqt/nV5EQKqQpo3SToSOV9J0DnbJqwK7Wv/Trc92zIAYZ4FlMu+JPFW1DfGFt81ZTCGgDEabffXeLyJg==
- dependencies:
- domelementtype "^2.3.0"
- domhandler "^5.0.2"
- entities "^4.2.0"
-
-domelementtype@^2.0.1, domelementtype@^2.2.0, domelementtype@^2.3.0:
- version "2.3.0"
- resolved "https://registry.yarnpkg.com/domelementtype/-/domelementtype-2.3.0.tgz#5c45e8e869952626331d7aab326d01daf65d589d"
- integrity sha512-OLETBj6w0OsagBwdXnPdN0cnMfF9opN69co+7ZrbfPGrdpPVNBUj02spi6B1N7wChLQiPn4CSH/zJvXw56gmHw==
-
-domhandler@^4.0.0, domhandler@^4.2.0, domhandler@^4.3.1:
- version "4.3.1"
- resolved "https://registry.yarnpkg.com/domhandler/-/domhandler-4.3.1.tgz#8d792033416f59d68bc03a5aa7b018c1ca89279c"
- integrity sha512-GrwoxYN+uWlzO8uhUXRl0P+kHE4GtVPfYzVLcUxPL7KNdHKj66vvlhiweIHqYYXWlw+T8iLMp42Lm67ghw4WMQ==
- dependencies:
- domelementtype "^2.2.0"
-
-domhandler@^5.0.1, domhandler@^5.0.2, domhandler@^5.0.3:
- version "5.0.3"
- resolved "https://registry.yarnpkg.com/domhandler/-/domhandler-5.0.3.tgz#cc385f7f751f1d1fc650c21374804254538c7d31"
- integrity sha512-cgwlv/1iFQiFnU96XXgROh8xTeetsnJiDsTc7TYCLFd9+/WNkIqPTxiM/8pSd8VIrhXGTf1Ny1q1hquVqDJB5w==
- dependencies:
- domelementtype "^2.3.0"
-
-domutils@^2.5.2, domutils@^2.8.0:
- version "2.8.0"
- resolved "https://registry.yarnpkg.com/domutils/-/domutils-2.8.0.tgz#4437def5db6e2d1f5d6ee859bd95ca7d02048135"
- integrity sha512-w96Cjofp72M5IIhpjgobBimYEfoPjx1Vx0BSX9P30WBdZW2WIKU0T1Bd0kz2eNZ9ikjKgHbEyKx8BB6H1L3h3A==
- dependencies:
- dom-serializer "^1.0.1"
- domelementtype "^2.2.0"
- domhandler "^4.2.0"
-
-domutils@^3.0.1:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/domutils/-/domutils-3.0.1.tgz#696b3875238338cb186b6c0612bd4901c89a4f1c"
- integrity sha512-z08c1l761iKhDFtfXO04C7kTdPBLi41zwOZl00WS8b5eiaebNpY00HKbztwBq+e3vyqWNwWF3mP9YLUeqIrF+Q==
- dependencies:
- dom-serializer "^2.0.0"
- domelementtype "^2.3.0"
- domhandler "^5.0.1"
-
-dot-case@^3.0.4:
- version "3.0.4"
- resolved "https://registry.yarnpkg.com/dot-case/-/dot-case-3.0.4.tgz#9b2b670d00a431667a8a75ba29cd1b98809ce751"
- integrity sha512-Kv5nKlh6yRrdrGvxeJ2e5y2eRUpkUosIW4A2AS38zwSz27zu7ufDwQPi5Jhs3XAlGNetl3bmnGhQsMtkKJnj3w==
- dependencies:
- no-case "^3.0.4"
- tslib "^2.0.3"
-
-dot-prop@^5.2.0:
- version "5.3.0"
- resolved "https://registry.yarnpkg.com/dot-prop/-/dot-prop-5.3.0.tgz#90ccce708cd9cd82cc4dc8c3ddd9abdd55b20e88"
- integrity sha512-QM8q3zDe58hqUqjraQOmzZ1LIH9SWQJTlEKCH4kJ2oQvLZk7RbQXvtDM2XEq3fwkV9CCvvH4LA0AV+ogFsBM2Q==
- dependencies:
- is-obj "^2.0.0"
-
-duplexer3@^0.1.4:
- version "0.1.5"
- resolved "https://registry.yarnpkg.com/duplexer3/-/duplexer3-0.1.5.tgz#0b5e4d7bad5de8901ea4440624c8e1d20099217e"
- integrity sha512-1A8za6ws41LQgv9HrE/66jyC5yuSjQ3L/KOpFtoBilsAK2iA2wuS5rTt1OCzIvtS2V7nVmedsUU+DGRcjBmOYA==
-
-duplexer@^0.1.2:
- version "0.1.2"
- resolved "https://registry.yarnpkg.com/duplexer/-/duplexer-0.1.2.tgz#3abe43aef3835f8ae077d136ddce0f276b0400e6"
- integrity sha512-jtD6YG370ZCIi/9GTaJKQxWTZD045+4R4hTk/x1UyoqadyJ9x9CgSi1RlVDQF8U2sxLLSnFkCaMihqljHIWgMg==
-
-eastasianwidth@^0.2.0:
- version "0.2.0"
- resolved "https://registry.yarnpkg.com/eastasianwidth/-/eastasianwidth-0.2.0.tgz#696ce2ec0aa0e6ea93a397ffcf24aa7840c827cb"
- integrity sha512-I88TYZWc9XiYHRQ4/3c5rjjfgkjhLyW2luGIheGERbNQ6OY7yTybanSpDXZa8y7VUP9YmDcYa+eyq4ca7iLqWA==
-
-ee-first@1.1.1:
- version "1.1.1"
- resolved "https://registry.yarnpkg.com/ee-first/-/ee-first-1.1.1.tgz#590c61156b0ae2f4f0255732a158b266bc56b21d"
- integrity sha512-WMwm9LhRUo+WUaRN+vRuETqG89IgZphVSNkdFgeb6sS/E4OrDIN7t48CAewSHXc6C8lefD8KKfr5vY61brQlow==
-
-electron-to-chromium@^1.4.284:
- version "1.4.295"
- resolved "https://registry.yarnpkg.com/electron-to-chromium/-/electron-to-chromium-1.4.295.tgz#911d5df67542bf7554336142eb302c5ec90bba66"
- integrity sha512-lEO94zqf1bDA3aepxwnWoHUjA8sZ+2owgcSZjYQy0+uOSEclJX0VieZC+r+wLpSxUHRd6gG32znTWmr+5iGzFw==
-
-emoji-regex@^8.0.0:
- version "8.0.0"
- resolved "https://registry.yarnpkg.com/emoji-regex/-/emoji-regex-8.0.0.tgz#e818fd69ce5ccfcb404594f842963bf53164cc37"
- integrity sha512-MSjYzcWNOA0ewAHpz0MxpYFvwg6yjy1NG3xteoqz644VCo/RPgnr1/GGt+ic3iJTzQ8Eu3TdM14SawnVUmGE6A==
-
-emoji-regex@^9.2.2:
- version "9.2.2"
- resolved "https://registry.yarnpkg.com/emoji-regex/-/emoji-regex-9.2.2.tgz#840c8803b0d8047f4ff0cf963176b32d4ef3ed72"
- integrity sha512-L18DaJsXSUk2+42pv8mLs5jJT2hqFkFE4j21wOmgbUqsZ2hL72NsUU785g9RXgo3s0ZNgVl42TiHp3ZtOv/Vyg==
-
-emojis-list@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/emojis-list/-/emojis-list-3.0.0.tgz#5570662046ad29e2e916e71aae260abdff4f6a78"
- integrity sha512-/kyM18EfinwXZbno9FyUGeFh87KC8HRQBQGildHZbEuRyWFOmv1U10o9BBp8XVZDVNNuQKyIGIu5ZYAAXJ0V2Q==
-
-emoticon@^3.2.0:
- version "3.2.0"
- resolved "https://registry.yarnpkg.com/emoticon/-/emoticon-3.2.0.tgz#c008ca7d7620fac742fe1bf4af8ff8fed154ae7f"
- integrity sha512-SNujglcLTTg+lDAcApPNgEdudaqQFiAbJCqzjNxJkvN9vAwCGi0uu8IUVvx+f16h+V44KCY6Y2yboroc9pilHg==
-
-encodeurl@~1.0.2:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/encodeurl/-/encodeurl-1.0.2.tgz#ad3ff4c86ec2d029322f5a02c3a9a606c95b3f59"
- integrity sha512-TPJXq8JqFaVYm2CWmPvnP2Iyo4ZSM7/QKcSmuMLDObfpH5fi7RUGmd/rTDf+rut/saiDiQEeVTNgAmJEdAOx0w==
-
-end-of-stream@^1.1.0:
- version "1.4.4"
- resolved "https://registry.yarnpkg.com/end-of-stream/-/end-of-stream-1.4.4.tgz#5ae64a5f45057baf3626ec14da0ca5e4b2431eb0"
- integrity sha512-+uw1inIHVPQoaVuHzRyXd21icM+cnt4CzD5rW+NC1wjOUSTOs+Te7FOv7AhN7vS9x/oIyhLP5PR1H+phQAHu5Q==
- dependencies:
- once "^1.4.0"
-
-enhanced-resolve@^5.10.0:
- version "5.12.0"
- resolved "https://registry.yarnpkg.com/enhanced-resolve/-/enhanced-resolve-5.12.0.tgz#300e1c90228f5b570c4d35babf263f6da7155634"
- integrity sha512-QHTXI/sZQmko1cbDoNAa3mJ5qhWUUNAq3vR0/YiD379fWQrcfuoX1+HW2S0MTt7XmoPLapdaDKUtelUSPic7hQ==
- dependencies:
- graceful-fs "^4.2.4"
- tapable "^2.2.0"
-
-entities@^2.0.0:
- version "2.2.0"
- resolved "https://registry.yarnpkg.com/entities/-/entities-2.2.0.tgz#098dc90ebb83d8dffa089d55256b351d34c4da55"
- integrity sha512-p92if5Nz619I0w+akJrLZH0MX0Pb5DX39XOwQTtXSdQQOaYH03S1uIQp4mhOZtAXrxq4ViO67YTiLBo2638o9A==
-
-entities@^4.2.0, entities@^4.3.0, entities@^4.4.0:
- version "4.4.0"
- resolved "https://registry.yarnpkg.com/entities/-/entities-4.4.0.tgz#97bdaba170339446495e653cfd2db78962900174"
- integrity sha512-oYp7156SP8LkeGD0GF85ad1X9Ai79WtRsZ2gxJqtBuzH+98YUV6jkHEKlZkMbcrjJjIVJNIDP/3WL9wQkoPbWA==
-
-entities@~2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/entities/-/entities-2.1.0.tgz#992d3129cf7df6870b96c57858c249a120f8b8b5"
- integrity sha512-hCx1oky9PFrJ611mf0ifBLBRW8lUUVRlFolb5gWRfIELabBlbp9xZvrqZLZAs+NxFnbfQoeGd8wDkygjg7U85w==
-
-error-ex@^1.3.1, error-ex@^1.3.2:
- version "1.3.2"
- resolved "https://registry.yarnpkg.com/error-ex/-/error-ex-1.3.2.tgz#b4ac40648107fdcdcfae242f428bea8a14d4f1bf"
- integrity sha512-7dFHNmqeFSEt2ZBsCriorKnn3Z2pj+fd9kmI6QoWw4//DL+icEBfc0U7qJCisqrTsKTjw4fNFy2pW9OqStD84g==
- dependencies:
- is-arrayish "^0.2.1"
-
-es-module-lexer@^0.9.0:
- version "0.9.3"
- resolved "https://registry.yarnpkg.com/es-module-lexer/-/es-module-lexer-0.9.3.tgz#6f13db00cc38417137daf74366f535c8eb438f19"
- integrity sha512-1HQ2M2sPtxwnvOvT1ZClHyQDiggdNjURWpY2we6aMKCQiUVxTmVs2UYPLIrD84sS+kMdUwfBSylbJPwNnBrnHQ==
-
-escalade@^3.1.1:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/escalade/-/escalade-3.1.1.tgz#d8cfdc7000965c5a0174b4a82eaa5c0552742e40"
- integrity sha512-k0er2gUkLf8O0zKJiAhmkTnJlTvINGv7ygDNPbeIsX/TJjGJZHuh9B2UxbsaEkmlEo9MfhrSzmhIlhRlI2GXnw==
-
-escape-goat@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/escape-goat/-/escape-goat-2.1.1.tgz#1b2dc77003676c457ec760b2dc68edb648188675"
- integrity sha512-8/uIhbG12Csjy2JEW7D9pHbreaVaS/OpN3ycnyvElTdwM5n6GY6W6e2IPemfvGZeUMqZ9A/3GqIZMgKnBhAw/Q==
-
-escape-html@^1.0.3, escape-html@~1.0.3:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/escape-html/-/escape-html-1.0.3.tgz#0258eae4d3d0c0974de1c169188ef0051d1d1988"
- integrity sha512-NiSupZ4OeuGwr68lGIeym/ksIZMJodUGOSCZ/FSnTxcrekbvqrgdUxlJOMpijaKZVjAJrWrGs/6Jy8OMuyj9ow==
-
-escape-string-regexp@^1.0.5:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/escape-string-regexp/-/escape-string-regexp-1.0.5.tgz#1b61c0562190a8dff6ae3bb2cf0200ca130b86d4"
- integrity sha512-vbRorB5FUQWvla16U8R/qgaFIya2qGzwDrNmCZuYKrbdSUMG6I1ZCGQRefkRVhuOkIGVne7BQ35DSfo1qvJqFg==
-
-escape-string-regexp@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/escape-string-regexp/-/escape-string-regexp-4.0.0.tgz#14ba83a5d373e3d311e5afca29cf5bfad965bf34"
- integrity sha512-TtpcNJ3XAzx3Gq8sWRzJaVajRs0uVxA2YAkdb1jm2YkPz4G6egUFAyA3n5vtEIZefPk5Wa4UXbKuS5fKkJWdgA==
-
-eslint-scope@5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/eslint-scope/-/eslint-scope-5.1.1.tgz#e786e59a66cb92b3f6c1fb0d508aab174848f48c"
- integrity sha512-2NxwbF/hZ0KpepYN0cNbo+FN6XoK7GaHlQhgx/hIZl6Va0bF45RQOOwhLIy8lQDbuCiadSLCBnH2CFYquit5bw==
- dependencies:
- esrecurse "^4.3.0"
- estraverse "^4.1.1"
-
-esprima@^4.0.0:
- version "4.0.1"
- resolved "https://registry.yarnpkg.com/esprima/-/esprima-4.0.1.tgz#13b04cdb3e6c5d19df91ab6987a8695619b0aa71"
- integrity sha512-eGuFFw7Upda+g4p+QHvnW0RyTX/SVeJBDM/gCtMARO0cLuT2HcEKnTPvhjV6aGeqrCB/sbNop0Kszm0jsaWU4A==
-
-esrecurse@^4.3.0:
- version "4.3.0"
- resolved "https://registry.yarnpkg.com/esrecurse/-/esrecurse-4.3.0.tgz#7ad7964d679abb28bee72cec63758b1c5d2c9921"
- integrity sha512-KmfKL3b6G+RXvP8N1vr3Tq1kL/oCFgn2NYXEtqP8/L3pKapUA4G8cFVaoF3SU323CD4XypR/ffioHmkti6/Tag==
- dependencies:
- estraverse "^5.2.0"
-
-estraverse@^4.1.1:
- version "4.3.0"
- resolved "https://registry.yarnpkg.com/estraverse/-/estraverse-4.3.0.tgz#398ad3f3c5a24948be7725e83d11a7de28cdbd1d"
- integrity sha512-39nnKffWz8xN1BU/2c79n9nB9HDzo0niYUqx6xyqUnyoAnQyyWpOTdZEeiCch8BBu515t4wp9ZmgVfVhn9EBpw==
-
-estraverse@^5.2.0:
- version "5.3.0"
- resolved "https://registry.yarnpkg.com/estraverse/-/estraverse-5.3.0.tgz#2eea5290702f26ab8fe5370370ff86c965d21123"
- integrity sha512-MMdARuVEQziNTeJD8DgMqmhwR11BRQ/cBP+pLtYdSTnf3MIO8fFeiINEbX36ZdNlfU/7A9f3gUw49B3oQsvwBA==
-
-estree-util-is-identifier-name@^2.0.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/estree-util-is-identifier-name/-/estree-util-is-identifier-name-2.1.0.tgz#fb70a432dcb19045e77b05c8e732f1364b4b49b2"
- integrity sha512-bEN9VHRyXAUOjkKVQVvArFym08BTWB0aJPppZZr0UNyAqWsLaVfAqP7hbaTJjzHifmB5ebnR8Wm7r7yGN/HonQ==
-
-estree-util-visit@^1.0.0:
- version "1.2.1"
- resolved "https://registry.yarnpkg.com/estree-util-visit/-/estree-util-visit-1.2.1.tgz#8bc2bc09f25b00827294703835aabee1cc9ec69d"
- integrity sha512-xbgqcrkIVbIG+lI/gzbvd9SGTJL4zqJKBFttUl5pP27KhAjtMKbX/mQXJ7qgyXpMgVy/zvpm0xoQQaGL8OloOw==
- dependencies:
- "@types/estree-jsx" "^1.0.0"
- "@types/unist" "^2.0.0"
-
-esutils@^2.0.2:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/esutils/-/esutils-2.0.3.tgz#74d2eb4de0b8da1293711910d50775b9b710ef64"
- integrity sha512-kVscqXk4OCp68SZ0dkgEKVi6/8ij300KBWTJq32P/dYeWTSwK41WyTxalN1eRmA5Z9UU/LX9D7FWSmV9SAYx6g==
-
-eta@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/eta/-/eta-2.0.0.tgz#376865fadebc899e5b6dfce82fae64cbbe47e594"
- integrity sha512-NqE7S2VmVwgMS8yBxsH4VgNQjNjLq1gfGU0u9I6Cjh468nPRMoDfGdK9n1p/3Dvsw3ebklDkZsFAnKJ9sefjBA==
-
-etag@~1.8.1:
- version "1.8.1"
- resolved "https://registry.yarnpkg.com/etag/-/etag-1.8.1.tgz#41ae2eeb65efa62268aebfea83ac7d79299b0887"
- integrity sha512-aIL5Fx7mawVa300al2BnEE4iNvo1qETxLrPI/o05L7z6go7fCw1J6EQmbK4FmJ2AS7kgVF/KEZWufBfdClMcPg==
-
-eval@^0.1.8:
- version "0.1.8"
- resolved "https://registry.yarnpkg.com/eval/-/eval-0.1.8.tgz#2b903473b8cc1d1989b83a1e7923f883eb357f85"
- integrity sha512-EzV94NYKoO09GLXGjXj9JIlXijVck4ONSr5wiCWDvhsvj5jxSrzTmRU/9C1DyB6uToszLs8aifA6NQ7lEQdvFw==
- dependencies:
- "@types/node" "*"
- require-like ">= 0.1.1"
-
-eventemitter3@^4.0.0:
- version "4.0.7"
- resolved "https://registry.yarnpkg.com/eventemitter3/-/eventemitter3-4.0.7.tgz#2de9b68f6528d5644ef5c59526a1b4a07306169f"
- integrity sha512-8guHBZCwKnFhYdHr2ysuRWErTwhoN2X8XELRlrRwpmfeY2jjuUN4taQMsULKUVo1K4DvZl+0pgfyoysHxvmvEw==
-
-events@^3.2.0:
- version "3.3.0"
- resolved "https://registry.yarnpkg.com/events/-/events-3.3.0.tgz#31a95ad0a924e2d2c419a813aeb2c4e878ea7400"
- integrity sha512-mQw+2fkQbALzQ7V0MY0IqdnXNOeTtP4r0lN9z7AAawCXgqea7bDii20AYrIBrFd/Hx0M2Ocz6S111CaFkUcb0Q==
-
-execa@^5.0.0:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/execa/-/execa-5.1.1.tgz#f80ad9cbf4298f7bd1d4c9555c21e93741c411dd"
- integrity sha512-8uSpZZocAZRBAPIEINJj3Lo9HyGitllczc27Eh5YYojjMFMn8yHMDMaUHE2Jqfq05D/wucwI4JGURyXt1vchyg==
- dependencies:
- cross-spawn "^7.0.3"
- get-stream "^6.0.0"
- human-signals "^2.1.0"
- is-stream "^2.0.0"
- merge-stream "^2.0.0"
- npm-run-path "^4.0.1"
- onetime "^5.1.2"
- signal-exit "^3.0.3"
- strip-final-newline "^2.0.0"
-
-express@^4.17.3:
- version "4.18.2"
- resolved "https://registry.yarnpkg.com/express/-/express-4.18.2.tgz#3fabe08296e930c796c19e3c516979386ba9fd59"
- integrity sha512-5/PsL6iGPdfQ/lKM1UuielYgv3BUoJfz1aUwU9vHZ+J7gyvwdQXFEBIEIaxeGf0GIcreATNyBExtalisDbuMqQ==
- dependencies:
- accepts "~1.3.8"
- array-flatten "1.1.1"
- body-parser "1.20.1"
- content-disposition "0.5.4"
- content-type "~1.0.4"
- cookie "0.5.0"
- cookie-signature "1.0.6"
- debug "2.6.9"
- depd "2.0.0"
- encodeurl "~1.0.2"
- escape-html "~1.0.3"
- etag "~1.8.1"
- finalhandler "1.2.0"
- fresh "0.5.2"
- http-errors "2.0.0"
- merge-descriptors "1.0.1"
- methods "~1.1.2"
- on-finished "2.4.1"
- parseurl "~1.3.3"
- path-to-regexp "0.1.7"
- proxy-addr "~2.0.7"
- qs "6.11.0"
- range-parser "~1.2.1"
- safe-buffer "5.2.1"
- send "0.18.0"
- serve-static "1.15.0"
- setprototypeof "1.2.0"
- statuses "2.0.1"
- type-is "~1.6.18"
- utils-merge "1.0.1"
- vary "~1.1.2"
-
-extend-shallow@^2.0.1:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/extend-shallow/-/extend-shallow-2.0.1.tgz#51af7d614ad9a9f610ea1bafbb989d6b1c56890f"
- integrity sha512-zCnTtlxNoAiDc3gqY2aYAWFx7XWWiasuF2K8Me5WbN8otHKTUKBwjPtNpRs/rbUZm7KxWAaNj7P1a/p52GbVug==
- dependencies:
- is-extendable "^0.1.0"
-
-extend@^3.0.0:
- version "3.0.2"
- resolved "https://registry.yarnpkg.com/extend/-/extend-3.0.2.tgz#f8b1136b4071fbd8eb140aff858b1019ec2915fa"
- integrity sha512-fjquC59cD7CyW6urNXK0FBufkZcoiGG80wTuPujX590cB5Ttln20E2UB4S/WARVqhXffZl2LNgS+gQdPIIim/g==
-
-fast-deep-equal@^3.1.1, fast-deep-equal@^3.1.3:
- version "3.1.3"
- resolved "https://registry.yarnpkg.com/fast-deep-equal/-/fast-deep-equal-3.1.3.tgz#3a7d56b559d6cbc3eb512325244e619a65c6c525"
- integrity sha512-f3qQ9oQy9j2AhBe/H9VC91wLmKBCCU/gDOnKNAYG5hswO7BLKj09Hc5HYNz9cGI++xlpDCIgDaitVs03ATR84Q==
-
-fast-glob@^3.2.11, fast-glob@^3.2.9:
- version "3.2.12"
- resolved "https://registry.yarnpkg.com/fast-glob/-/fast-glob-3.2.12.tgz#7f39ec99c2e6ab030337142da9e0c18f37afae80"
- integrity sha512-DVj4CQIYYow0BlaelwK1pHl5n5cRSJfM60UA0zK891sVInoPri2Ekj7+e1CT3/3qxXenpI+nBBmQAcJPJgaj4w==
- dependencies:
- "@nodelib/fs.stat" "^2.0.2"
- "@nodelib/fs.walk" "^1.2.3"
- glob-parent "^5.1.2"
- merge2 "^1.3.0"
- micromatch "^4.0.4"
-
-fast-json-stable-stringify@^2.0.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/fast-json-stable-stringify/-/fast-json-stable-stringify-2.1.0.tgz#874bf69c6f404c2b5d99c481341399fd55892633"
- integrity sha512-lhd/wF+Lk98HZoTCtlVraHtfh5XYijIjalXck7saUtuanSDyLMxnHhSXEDJqHxD7msR8D0uCmqlkwjCV8xvwHw==
-
-fast-url-parser@1.1.3:
- version "1.1.3"
- resolved "https://registry.yarnpkg.com/fast-url-parser/-/fast-url-parser-1.1.3.tgz#f4af3ea9f34d8a271cf58ad2b3759f431f0b318d"
- integrity sha512-5jOCVXADYNuRkKFzNJ0dCCewsZiYo0dz8QNYljkOpFC6r2U4OBmKtvm/Tsuh4w1YYdDqDb31a8TVhBJ2OJKdqQ==
- dependencies:
- punycode "^1.3.2"
-
-fastq@^1.6.0:
- version "1.15.0"
- resolved "https://registry.yarnpkg.com/fastq/-/fastq-1.15.0.tgz#d04d07c6a2a68fe4599fea8d2e103a937fae6b3a"
- integrity sha512-wBrocU2LCXXa+lWBt8RoIRD89Fi8OdABODa/kEnyeyjS5aZO5/GNvI5sEINADqP/h8M29UHTHUb53sUu5Ihqdw==
- dependencies:
- reusify "^1.0.4"
-
-fault@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/fault/-/fault-2.0.1.tgz#d47ca9f37ca26e4bd38374a7c500b5a384755b6c"
- integrity sha512-WtySTkS4OKev5JtpHXnib4Gxiurzh5NCGvWrFaZ34m6JehfTUhKZvn9njTfw48t6JumVQOmrKqpmGcdwxnhqBQ==
- dependencies:
- format "^0.2.0"
-
-faye-websocket@^0.11.3:
- version "0.11.4"
- resolved "https://registry.yarnpkg.com/faye-websocket/-/faye-websocket-0.11.4.tgz#7f0d9275cfdd86a1c963dc8b65fcc451edcbb1da"
- integrity sha512-CzbClwlXAuiRQAlUyfqPgvPoNKTckTPGfwZV4ZdAhVcP2lh9KUxJg2b5GkE7XbjKQ3YJnQ9z6D9ntLAlB+tP8g==
- dependencies:
- websocket-driver ">=0.5.1"
-
-fbemitter@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/fbemitter/-/fbemitter-3.0.0.tgz#00b2a1af5411254aab416cd75f9e6289bee4bff3"
- integrity sha512-KWKaceCwKQU0+HPoop6gn4eOHk50bBv/VxjJtGMfwmJt3D29JpN4H4eisCtIPA+a8GVBam+ldMMpMjJUvpDyHw==
- dependencies:
- fbjs "^3.0.0"
-
-fbjs-css-vars@^1.0.0:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/fbjs-css-vars/-/fbjs-css-vars-1.0.2.tgz#216551136ae02fe255932c3ec8775f18e2c078b8"
- integrity sha512-b2XGFAFdWZWg0phtAWLHCk836A1Xann+I+Dgd3Gk64MHKZO44FfoD1KxyvbSh0qZsIoXQGGlVztIY+oitJPpRQ==
-
-fbjs@^3.0.0, fbjs@^3.0.1:
- version "3.0.4"
- resolved "https://registry.yarnpkg.com/fbjs/-/fbjs-3.0.4.tgz#e1871c6bd3083bac71ff2da868ad5067d37716c6"
- integrity sha512-ucV0tDODnGV3JCnnkmoszb5lf4bNpzjv80K41wd4k798Etq+UYD0y0TIfalLjZoKgjive6/adkRnszwapiDgBQ==
- dependencies:
- cross-fetch "^3.1.5"
- fbjs-css-vars "^1.0.0"
- loose-envify "^1.0.0"
- object-assign "^4.1.0"
- promise "^7.1.1"
- setimmediate "^1.0.5"
- ua-parser-js "^0.7.30"
-
-feed@^4.2.2:
- version "4.2.2"
- resolved "https://registry.yarnpkg.com/feed/-/feed-4.2.2.tgz#865783ef6ed12579e2c44bbef3c9113bc4956a7e"
- integrity sha512-u5/sxGfiMfZNtJ3OvQpXcvotFpYkL0n9u9mM2vkui2nGo8b4wvDkJ8gAkYqbA8QpGyFCv3RK0Z+Iv+9veCS9bQ==
- dependencies:
- xml-js "^1.6.11"
-
-file-loader@^6.2.0:
- version "6.2.0"
- resolved "https://registry.yarnpkg.com/file-loader/-/file-loader-6.2.0.tgz#baef7cf8e1840df325e4390b4484879480eebe4d"
- integrity sha512-qo3glqyTa61Ytg4u73GultjHGjdRyig3tG6lPtyX/jOEJvHif9uB0/OCI2Kif6ctF3caQTW2G5gym21oAsI4pw==
- dependencies:
- loader-utils "^2.0.0"
- schema-utils "^3.0.0"
-
-filesize@^8.0.6:
- version "8.0.7"
- resolved "https://registry.yarnpkg.com/filesize/-/filesize-8.0.7.tgz#695e70d80f4e47012c132d57a059e80c6b580bd8"
- integrity sha512-pjmC+bkIF8XI7fWaH8KxHcZL3DPybs1roSKP4rKDvy20tAWwIObE4+JIseG2byfGKhud5ZnM4YSGKBz7Sh0ndQ==
-
-fill-range@^7.0.1:
- version "7.0.1"
- resolved "https://registry.yarnpkg.com/fill-range/-/fill-range-7.0.1.tgz#1919a6a7c75fe38b2c7c77e5198535da9acdda40"
- integrity sha512-qOo9F+dMUmC2Lcb4BbVvnKJxTPjCm+RRpe4gDuGrzkL7mEVl/djYSu2OdQ2Pa302N4oqkSg9ir6jaLWJ2USVpQ==
- dependencies:
- to-regex-range "^5.0.1"
-
-finalhandler@1.2.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/finalhandler/-/finalhandler-1.2.0.tgz#7d23fe5731b207b4640e4fcd00aec1f9207a7b32"
- integrity sha512-5uXcUVftlQMFnWC9qu/svkWv3GTd2PfUhK/3PLkYNAe7FbqJMt3515HaxE6eRL74GdsriiwujiawdaB1BpEISg==
- dependencies:
- debug "2.6.9"
- encodeurl "~1.0.2"
- escape-html "~1.0.3"
- on-finished "2.4.1"
- parseurl "~1.3.3"
- statuses "2.0.1"
- unpipe "~1.0.0"
-
-find-cache-dir@^3.3.1:
- version "3.3.2"
- resolved "https://registry.yarnpkg.com/find-cache-dir/-/find-cache-dir-3.3.2.tgz#b30c5b6eff0730731aea9bbd9dbecbd80256d64b"
- integrity sha512-wXZV5emFEjrridIgED11OoUKLxiYjAcqot/NJdAkOhlJ+vGzwhOAfcG5OX1jP+S0PcjEn8bdMJv+g2jwQ3Onig==
- dependencies:
- commondir "^1.0.1"
- make-dir "^3.0.2"
- pkg-dir "^4.1.0"
-
-find-up@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/find-up/-/find-up-3.0.0.tgz#49169f1d7993430646da61ecc5ae355c21c97b73"
- integrity sha512-1yD6RmLI1XBfxugvORwlck6f75tYL+iR0jqwsOrOxMZyGYqUuDhJ0l4AXdO1iX/FTs9cBAMEk1gWSEx1kSbylg==
- dependencies:
- locate-path "^3.0.0"
-
-find-up@^4.0.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/find-up/-/find-up-4.1.0.tgz#97afe7d6cdc0bc5928584b7c8d7b16e8a9aa5d19"
- integrity sha512-PpOwAdQ/YlXQ2vj8a3h8IipDuYRi3wceVQQGYWxNINccq40Anw7BlsEXCMbt1Zt+OLA6Fq9suIpIWD0OsnISlw==
- dependencies:
- locate-path "^5.0.0"
- path-exists "^4.0.0"
-
-find-up@^5.0.0:
- version "5.0.0"
- resolved "https://registry.yarnpkg.com/find-up/-/find-up-5.0.0.tgz#4c92819ecb7083561e4f4a240a86be5198f536fc"
- integrity sha512-78/PXT1wlLLDgTzDs7sjq9hzz0vXD+zn+7wypEe4fXQxCmdmqfGsEPQxmiCSQI3ajFV91bVSsvNtrJRiW6nGng==
- dependencies:
- locate-path "^6.0.0"
- path-exists "^4.0.0"
-
-flux@^4.0.1:
- version "4.0.3"
- resolved "https://registry.yarnpkg.com/flux/-/flux-4.0.3.tgz#573b504a24982c4768fdfb59d8d2ea5637d72ee7"
- integrity sha512-yKAbrp7JhZhj6uiT1FTuVMlIAT1J4jqEyBpFApi1kxpGZCvacMVc/t1pMQyotqHhAgvoE3bNvAykhCo2CLjnYw==
- dependencies:
- fbemitter "^3.0.0"
- fbjs "^3.0.1"
-
-follow-redirects@^1.0.0, follow-redirects@^1.14.7:
- version "1.15.2"
- resolved "https://registry.yarnpkg.com/follow-redirects/-/follow-redirects-1.15.2.tgz#b460864144ba63f2681096f274c4e57026da2c13"
- integrity sha512-VQLG33o04KaQ8uYi2tVNbdrWp1QWxNNea+nmIB4EVM28v0hmP17z7aG1+wAkNzVq4KeXTq3221ye5qTJP91JwA==
-
-fork-ts-checker-webpack-plugin@^6.5.0:
- version "6.5.2"
- resolved "https://registry.yarnpkg.com/fork-ts-checker-webpack-plugin/-/fork-ts-checker-webpack-plugin-6.5.2.tgz#4f67183f2f9eb8ba7df7177ce3cf3e75cdafb340"
- integrity sha512-m5cUmF30xkZ7h4tWUgTAcEaKmUW7tfyUyTqNNOz7OxWJ0v1VWKTcOvH8FWHUwSjlW/356Ijc9vi3XfcPstpQKA==
- dependencies:
- "@babel/code-frame" "^7.8.3"
- "@types/json-schema" "^7.0.5"
- chalk "^4.1.0"
- chokidar "^3.4.2"
- cosmiconfig "^6.0.0"
- deepmerge "^4.2.2"
- fs-extra "^9.0.0"
- glob "^7.1.6"
- memfs "^3.1.2"
- minimatch "^3.0.4"
- schema-utils "2.7.0"
- semver "^7.3.2"
- tapable "^1.0.0"
-
-format@^0.2.0:
- version "0.2.2"
- resolved "https://registry.yarnpkg.com/format/-/format-0.2.2.tgz#d6170107e9efdc4ed30c9dc39016df942b5cb58b"
- integrity sha512-wzsgA6WOq+09wrU1tsJ09udeR/YZRaeArL9e1wPbFg3GG2yDnC2ldKpxs4xunpFF9DgqCqOIra3bc1HWrJ37Ww==
-
-forwarded@0.2.0:
- version "0.2.0"
- resolved "https://registry.yarnpkg.com/forwarded/-/forwarded-0.2.0.tgz#2269936428aad4c15c7ebe9779a84bf0b2a81811"
- integrity sha512-buRG0fpBtRHSTCOASe6hD258tEubFoRLb4ZNA6NxMVHNw2gOcwHo9wyablzMzOA5z9xA9L1KNjk/Nt6MT9aYow==
-
-fraction.js@^4.2.0:
- version "4.2.0"
- resolved "https://registry.yarnpkg.com/fraction.js/-/fraction.js-4.2.0.tgz#448e5109a313a3527f5a3ab2119ec4cf0e0e2950"
- integrity sha512-MhLuK+2gUcnZe8ZHlaaINnQLl0xRIGRfcGk2yl8xoQAfHrSsL3rYu6FCmBdkdbhc9EPlwyGHewaRsvwRMJtAlA==
-
-fresh@0.5.2:
- version "0.5.2"
- resolved "https://registry.yarnpkg.com/fresh/-/fresh-0.5.2.tgz#3d8cadd90d976569fa835ab1f8e4b23a105605a7"
- integrity sha512-zJ2mQYM18rEFOudeV4GShTGIQ7RbzA7ozbU9I/XBpm7kqgMywgmylMwXHxZJmkVoYkna9d2pVXVXPdYTP9ej8Q==
-
-fs-extra@^10.1.0:
- version "10.1.0"
- resolved "https://registry.yarnpkg.com/fs-extra/-/fs-extra-10.1.0.tgz#02873cfbc4084dde127eaa5f9905eef2325d1abf"
- integrity sha512-oRXApq54ETRj4eMiFzGnHWGy+zo5raudjuxN0b8H7s/RU2oW0Wvsx9O0ACRN/kRq9E8Vu/ReskGB5o3ji+FzHQ==
- dependencies:
- graceful-fs "^4.2.0"
- jsonfile "^6.0.1"
- universalify "^2.0.0"
-
-fs-extra@^9.0.0:
- version "9.1.0"
- resolved "https://registry.yarnpkg.com/fs-extra/-/fs-extra-9.1.0.tgz#5954460c764a8da2094ba3554bf839e6b9a7c86d"
- integrity sha512-hcg3ZmepS30/7BSFqRvoo3DOMQu7IjqxO5nCDt+zM9XWjb33Wg7ziNT+Qvqbuc3+gWpzO02JubVyk2G4Zvo1OQ==
- dependencies:
- at-least-node "^1.0.0"
- graceful-fs "^4.2.0"
- jsonfile "^6.0.1"
- universalify "^2.0.0"
-
-fs-monkey@^1.0.3:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/fs-monkey/-/fs-monkey-1.0.3.tgz#ae3ac92d53bb328efe0e9a1d9541f6ad8d48e2d3"
- integrity sha512-cybjIfiiE+pTWicSCLFHSrXZ6EilF30oh91FDP9S2B051prEa7QWfrVTQm10/dDpswBDXZugPa1Ogu8Yh+HV0Q==
-
-fs.realpath@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/fs.realpath/-/fs.realpath-1.0.0.tgz#1504ad2523158caa40db4a2787cb01411994ea4f"
- integrity sha512-OO0pH2lK6a0hZnAdau5ItzHPI6pUlvI7jMVnxUQRtw4owF2wk8lOSabtGDCTP4Ggrg2MbGnWO9X8K1t4+fGMDw==
-
-fsevents@~2.3.2:
- version "2.3.2"
- resolved "https://registry.yarnpkg.com/fsevents/-/fsevents-2.3.2.tgz#8a526f78b8fdf4623b709e0b975c52c24c02fd1a"
- integrity sha512-xiqMQR4xAeHTuB9uWm+fFRcIOgKBMiOBP+eXiyT7jsgVCq1bkVygt00oASowB7EdtpOHaaPgKt812P9ab+DDKA==
-
-function-bind@^1.1.1:
- version "1.1.1"
- resolved "https://registry.yarnpkg.com/function-bind/-/function-bind-1.1.1.tgz#a56899d3ea3c9bab874bb9773b7c5ede92f4895d"
- integrity sha512-yIovAzMX49sF8Yl58fSCWJ5svSLuaibPxXQJFLmBObTuCr0Mf1KiPopGM9NiFjiYBCbfaa2Fh6breQ6ANVTI0A==
-
-gensync@^1.0.0-beta.1, gensync@^1.0.0-beta.2:
- version "1.0.0-beta.2"
- resolved "https://registry.yarnpkg.com/gensync/-/gensync-1.0.0-beta.2.tgz#32a6ee76c3d7f52d46b2b1ae5d93fea8580a25e0"
- integrity sha512-3hN7NaskYvMDLQY55gnW3NQ+mesEAepTqlg+VEbj7zzqEMBVNhzcGYYeqFo/TlYz6eQiFcp1HcsCZO+nGgS8zg==
-
-get-intrinsic@^1.0.2, get-intrinsic@^1.1.1:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/get-intrinsic/-/get-intrinsic-1.2.0.tgz#7ad1dc0535f3a2904bba075772763e5051f6d05f"
- integrity sha512-L049y6nFOuom5wGyRc3/gdTLO94dySVKRACj1RmJZBQXlbTMhtNIgkWkUHq+jYmZvKf14EW1EoJnnjbmoHij0Q==
- dependencies:
- function-bind "^1.1.1"
- has "^1.0.3"
- has-symbols "^1.0.3"
-
-get-own-enumerable-property-symbols@^3.0.0:
- version "3.0.2"
- resolved "https://registry.yarnpkg.com/get-own-enumerable-property-symbols/-/get-own-enumerable-property-symbols-3.0.2.tgz#b5fde77f22cbe35f390b4e089922c50bce6ef664"
- integrity sha512-I0UBV/XOz1XkIJHEUDMZAbzCThU/H8DxmSfmdGcKPnVhu2VfFqr34jr9777IyaTYvxjedWhqVIilEDsCdP5G6g==
-
-get-stdin@~9.0.0:
- version "9.0.0"
- resolved "https://registry.yarnpkg.com/get-stdin/-/get-stdin-9.0.0.tgz#3983ff82e03d56f1b2ea0d3e60325f39d703a575"
- integrity sha512-dVKBjfWisLAicarI2Sf+JuBE/DghV4UzNAVe9yhEJuzeREd3JhOTE9cUaJTeSa77fsbQUK3pcOpJfM59+VKZaA==
-
-get-stream@^4.1.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/get-stream/-/get-stream-4.1.0.tgz#c1b255575f3dc21d59bfc79cd3d2b46b1c3a54b5"
- integrity sha512-GMat4EJ5161kIy2HevLlr4luNjBgvmj413KaQA7jt4V8B4RDsfpHk7WQ9GVqfYyyx8OS/L66Kox+rJRNklLK7w==
- dependencies:
- pump "^3.0.0"
-
-get-stream@^5.1.0:
- version "5.2.0"
- resolved "https://registry.yarnpkg.com/get-stream/-/get-stream-5.2.0.tgz#4966a1795ee5ace65e706c4b7beb71257d6e22d3"
- integrity sha512-nBF+F1rAZVCu/p7rjzgA+Yb4lfYXrpl7a6VmJrU8wF9I1CKvP/QwPNZHnOlwbTkY6dvtFIzFMSyQXbLoTQPRpA==
- dependencies:
- pump "^3.0.0"
-
-get-stream@^6.0.0:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/get-stream/-/get-stream-6.0.1.tgz#a262d8eef67aced57c2852ad6167526a43cbf7b7"
- integrity sha512-ts6Wi+2j3jQjqi70w5AlN8DFnkSwC+MqmxEzdEALB2qXZYV3X/b1CTfgPLGJNMeAWxdPfU8FO1ms3NUfaHCPYg==
-
-github-slugger@^1.4.0:
- version "1.5.0"
- resolved "https://registry.yarnpkg.com/github-slugger/-/github-slugger-1.5.0.tgz#17891bbc73232051474d68bd867a34625c955f7d"
- integrity sha512-wIh+gKBI9Nshz2o46B0B3f5k/W+WI9ZAv6y5Dn5WJ5SK1t0TnDimB4WE5rmTD05ZAIn8HALCZVmCsvj0w0v0lw==
-
-glob-parent@^5.1.2, glob-parent@~5.1.2:
- version "5.1.2"
- resolved "https://registry.yarnpkg.com/glob-parent/-/glob-parent-5.1.2.tgz#869832c58034fe68a4093c17dc15e8340d8401c4"
- integrity sha512-AOIgSQCepiJYwP3ARnGx+5VnTu2HBYdzbGP45eLw1vr3zB3vZLeyed1sC9hnbcOc9/SrMyM5RPQrkGz4aS9Zow==
- dependencies:
- is-glob "^4.0.1"
-
-glob-parent@^6.0.1:
- version "6.0.2"
- resolved "https://registry.yarnpkg.com/glob-parent/-/glob-parent-6.0.2.tgz#6d237d99083950c79290f24c7642a3de9a28f9e3"
- integrity sha512-XxwI8EOhVQgWp6iDL+3b0r86f4d6AX6zSU55HfB4ydCEuXLXc5FcYeOu+nnGftS4TEju/11rt4KJPTMgbfmv4A==
- dependencies:
- is-glob "^4.0.3"
-
-glob-to-regexp@^0.4.1:
- version "0.4.1"
- resolved "https://registry.yarnpkg.com/glob-to-regexp/-/glob-to-regexp-0.4.1.tgz#c75297087c851b9a578bd217dd59a92f59fe546e"
- integrity sha512-lkX1HJXwyMcprw/5YUZc2s7DrpAiHB21/V+E1rHUrVNokkvB6bqMzT0VfV6/86ZNabt1k14YOIaT7nDvOX3Iiw==
-
-glob@^7.0.0, glob@^7.1.3, glob@^7.1.6, glob@~7.2.0:
- version "7.2.3"
- resolved "https://registry.yarnpkg.com/glob/-/glob-7.2.3.tgz#b8df0fb802bbfa8e89bd1d938b4e16578ed44f2b"
- integrity sha512-nFR0zLpU2YCaRxwoCJvL6UvCH2JFyFVIvwTLsIf21AuHlMskA1hhTdk+LlYJtOlYt9v6dvszD2BGRqBL+iQK9Q==
- dependencies:
- fs.realpath "^1.0.0"
- inflight "^1.0.4"
- inherits "2"
- minimatch "^3.1.1"
- once "^1.3.0"
- path-is-absolute "^1.0.0"
-
-glob@^8.0.0, glob@^8.0.1:
- version "8.1.0"
- resolved "https://registry.yarnpkg.com/glob/-/glob-8.1.0.tgz#d388f656593ef708ee3e34640fdfb99a9fd1c33e"
- integrity sha512-r8hpEjiQEYlF2QU0df3dS+nxxSIreXQS1qRhMJM0Q5NDdR386C7jb7Hwwod8Fgiuex+k0GFjgft18yvxm5XoCQ==
- dependencies:
- fs.realpath "^1.0.0"
- inflight "^1.0.4"
- inherits "2"
- minimatch "^5.0.1"
- once "^1.3.0"
-
-global-dirs@^3.0.0:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/global-dirs/-/global-dirs-3.0.1.tgz#0c488971f066baceda21447aecb1a8b911d22485"
- integrity sha512-NBcGGFbBA9s1VzD41QXDG+3++t9Mn5t1FpLdhESY6oKY4gYTFpX4wO3sqGUa0Srjtbfj3szX0RnemmrVRUdULA==
- dependencies:
- ini "2.0.0"
-
-global-modules@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/global-modules/-/global-modules-2.0.0.tgz#997605ad2345f27f51539bea26574421215c7780"
- integrity sha512-NGbfmJBp9x8IxyJSd1P+otYK8vonoJactOogrVfFRIAEY1ukil8RSKDz2Yo7wh1oihl51l/r6W4epkeKJHqL8A==
- dependencies:
- global-prefix "^3.0.0"
-
-global-prefix@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/global-prefix/-/global-prefix-3.0.0.tgz#fc85f73064df69f50421f47f883fe5b913ba9b97"
- integrity sha512-awConJSVCHVGND6x3tmMaKcQvwXLhjdkmomy2W+Goaui8YPgYgXJZewhg3fWC+DlfqqQuWg8AwqjGTD2nAPVWg==
- dependencies:
- ini "^1.3.5"
- kind-of "^6.0.2"
- which "^1.3.1"
-
-globals@^11.1.0:
- version "11.12.0"
- resolved "https://registry.yarnpkg.com/globals/-/globals-11.12.0.tgz#ab8795338868a0babd8525758018c2a7eb95c42e"
- integrity sha512-WOBp/EEGUiIsJSp7wcv/y6MO+lV9UoncWqxuFfm8eBwzWNgyfBd6Gz+IeKQ9jCmyhoH99g15M3T+QaVHFjizVA==
-
-globby@^11.0.1, globby@^11.0.4, globby@^11.1.0:
- version "11.1.0"
- resolved "https://registry.yarnpkg.com/globby/-/globby-11.1.0.tgz#bd4be98bb042f83d796f7e3811991fbe82a0d34b"
- integrity sha512-jhIXaOzy1sb8IyocaruWSn1TjmnBVs8Ayhcy83rmxNJ8q2uWKCAj3CnJY+KpGSXCueAPc0i05kVvVKtP1t9S3g==
- dependencies:
- array-union "^2.1.0"
- dir-glob "^3.0.1"
- fast-glob "^3.2.9"
- ignore "^5.2.0"
- merge2 "^1.4.1"
- slash "^3.0.0"
-
-globby@^13.1.1:
- version "13.1.3"
- resolved "https://registry.yarnpkg.com/globby/-/globby-13.1.3.tgz#f62baf5720bcb2c1330c8d4ef222ee12318563ff"
- integrity sha512-8krCNHXvlCgHDpegPzleMq07yMYTO2sXKASmZmquEYWEmCx6J5UTRbp5RwMJkTJGtcQ44YpiUYUiN0b9mzy8Bw==
- dependencies:
- dir-glob "^3.0.1"
- fast-glob "^3.2.11"
- ignore "^5.2.0"
- merge2 "^1.4.1"
- slash "^4.0.0"
-
-got@^9.6.0:
- version "9.6.0"
- resolved "https://registry.yarnpkg.com/got/-/got-9.6.0.tgz#edf45e7d67f99545705de1f7bbeeeb121765ed85"
- integrity sha512-R7eWptXuGYxwijs0eV+v3o6+XH1IqVK8dJOEecQfTmkncw9AV4dcw/Dhxi8MdlqPthxxpZyizMzyg8RTmEsG+Q==
- dependencies:
- "@sindresorhus/is" "^0.14.0"
- "@szmarczak/http-timer" "^1.1.2"
- cacheable-request "^6.0.0"
- decompress-response "^3.3.0"
- duplexer3 "^0.1.4"
- get-stream "^4.1.0"
- lowercase-keys "^1.0.1"
- mimic-response "^1.0.1"
- p-cancelable "^1.0.0"
- to-readable-stream "^1.0.0"
- url-parse-lax "^3.0.0"
-
-graceful-fs@^4.1.2, graceful-fs@^4.1.6, graceful-fs@^4.2.0, graceful-fs@^4.2.4, graceful-fs@^4.2.6, graceful-fs@^4.2.9:
- version "4.2.10"
- resolved "https://registry.yarnpkg.com/graceful-fs/-/graceful-fs-4.2.10.tgz#147d3a006da4ca3ce14728c7aefc287c367d7a6c"
- integrity sha512-9ByhssR2fPVsNZj478qUUbKfmL0+t5BDVyjShtyZZLiK7ZDAArFFfopyOTj0M05wE2tJPisA4iTnnXl2YoPvOA==
-
-gray-matter@^4.0.3:
- version "4.0.3"
- resolved "https://registry.yarnpkg.com/gray-matter/-/gray-matter-4.0.3.tgz#e893c064825de73ea1f5f7d88c7a9f7274288798"
- integrity sha512-5v6yZd4JK3eMI3FqqCouswVqwugaA9r4dNZB1wwcmrD02QkV5H0y7XBQW8QwQqEaZY1pM9aqORSORhJRdNK44Q==
- dependencies:
- js-yaml "^3.13.1"
- kind-of "^6.0.2"
- section-matter "^1.0.0"
- strip-bom-string "^1.0.0"
-
-gzip-size@^6.0.0:
- version "6.0.0"
- resolved "https://registry.yarnpkg.com/gzip-size/-/gzip-size-6.0.0.tgz#065367fd50c239c0671cbcbad5be3e2eeb10e462"
- integrity sha512-ax7ZYomf6jqPTQ4+XCpUGyXKHk5WweS+e05MBO4/y3WJ5RkmPXNKvX+bx1behVILVwr6JSQvZAku021CHPXG3Q==
- dependencies:
- duplexer "^0.1.2"
-
-handle-thing@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/handle-thing/-/handle-thing-2.0.1.tgz#857f79ce359580c340d43081cc648970d0bb234e"
- integrity sha512-9Qn4yBxelxoh2Ow62nP+Ka/kMnOXRi8BXnRaUwezLNhqelnN49xKz4F/dPP8OYLxLxq6JDtZb2i9XznUQbNPTg==
-
-has-flag@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/has-flag/-/has-flag-3.0.0.tgz#b5d454dc2199ae225699f3467e5a07f3b955bafd"
- integrity sha512-sKJf1+ceQBr4SMkvQnBDNDtf4TXpVhVGateu0t918bl30FnbE2m4vNLX+VWe/dpjlb+HugGYzW7uQXH98HPEYw==
-
-has-flag@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/has-flag/-/has-flag-4.0.0.tgz#944771fd9c81c81265c4d6941860da06bb59479b"
- integrity sha512-EykJT/Q1KjTWctppgIAgfSO0tKVuZUjhgMr17kqTumMl6Afv3EISleU7qZUzoXDFTAHTDC4NOoG/ZxU3EvlMPQ==
-
-has-property-descriptors@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/has-property-descriptors/-/has-property-descriptors-1.0.0.tgz#610708600606d36961ed04c196193b6a607fa861"
- integrity sha512-62DVLZGoiEBDHQyqG4w9xCuZ7eJEwNmJRWw2VY84Oedb7WFcA27fiEVe8oUQx9hAUJ4ekurquucTGwsyO1XGdQ==
- dependencies:
- get-intrinsic "^1.1.1"
-
-has-symbols@^1.0.3:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/has-symbols/-/has-symbols-1.0.3.tgz#bb7b2c4349251dce87b125f7bdf874aa7c8b39f8"
- integrity sha512-l3LCuF6MgDNwTDKkdYGEihYjt5pRPbEg46rtlmnSPlUbgmB8LOIrKJbYYFBSbnPaJexMKtiPO8hmeRjRz2Td+A==
-
-has-yarn@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/has-yarn/-/has-yarn-2.1.0.tgz#137e11354a7b5bf11aa5cb649cf0c6f3ff2b2e77"
- integrity sha512-UqBRqi4ju7T+TqGNdqAO0PaSVGsDGJUBQvk9eUWNGRY1CFGDzYhLWoM7JQEemnlvVcv/YEmc2wNW8BC24EnUsw==
-
-has@^1.0.3:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/has/-/has-1.0.3.tgz#722d7cbfc1f6aa8241f16dd814e011e1f41e8796"
- integrity sha512-f2dvO0VU6Oej7RkWJGrehjbzMAjFp5/VKPp5tTpWIV4JHHZK1/BxbFRtf/siA2SWTe09caDmVtYYzWEIbBS4zw==
- dependencies:
- function-bind "^1.1.1"
-
-hast-to-hyperscript@^9.0.0:
- version "9.0.1"
- resolved "https://registry.yarnpkg.com/hast-to-hyperscript/-/hast-to-hyperscript-9.0.1.tgz#9b67fd188e4c81e8ad66f803855334173920218d"
- integrity sha512-zQgLKqF+O2F72S1aa4y2ivxzSlko3MAvxkwG8ehGmNiqd98BIN3JM1rAJPmplEyLmGLO2QZYJtIneOSZ2YbJuA==
- dependencies:
- "@types/unist" "^2.0.3"
- comma-separated-tokens "^1.0.0"
- property-information "^5.3.0"
- space-separated-tokens "^1.0.0"
- style-to-object "^0.3.0"
- unist-util-is "^4.0.0"
- web-namespaces "^1.0.0"
-
-hast-util-from-parse5@^6.0.0:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/hast-util-from-parse5/-/hast-util-from-parse5-6.0.1.tgz#554e34abdeea25ac76f5bd950a1f0180e0b3bc2a"
- integrity sha512-jeJUWiN5pSxW12Rh01smtVkZgZr33wBokLzKLwinYOUfSzm1Nl/c3GUGebDyOKjdsRgMvoVbV0VpAcpjF4NrJA==
- dependencies:
- "@types/parse5" "^5.0.0"
- hastscript "^6.0.0"
- property-information "^5.0.0"
- vfile "^4.0.0"
- vfile-location "^3.2.0"
- web-namespaces "^1.0.0"
-
-hast-util-parse-selector@^2.0.0:
- version "2.2.5"
- resolved "https://registry.yarnpkg.com/hast-util-parse-selector/-/hast-util-parse-selector-2.2.5.tgz#d57c23f4da16ae3c63b3b6ca4616683313499c3a"
- integrity sha512-7j6mrk/qqkSehsM92wQjdIgWM2/BW61u/53G6xmC8i1OmEdKLHbk419QKQUjz6LglWsfqoiHmyMRkP1BGjecNQ==
-
-hast-util-raw@6.0.1:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/hast-util-raw/-/hast-util-raw-6.0.1.tgz#973b15930b7529a7b66984c98148b46526885977"
- integrity sha512-ZMuiYA+UF7BXBtsTBNcLBF5HzXzkyE6MLzJnL605LKE8GJylNjGc4jjxazAHUtcwT5/CEt6afRKViYB4X66dig==
- dependencies:
- "@types/hast" "^2.0.0"
- hast-util-from-parse5 "^6.0.0"
- hast-util-to-parse5 "^6.0.0"
- html-void-elements "^1.0.0"
- parse5 "^6.0.0"
- unist-util-position "^3.0.0"
- vfile "^4.0.0"
- web-namespaces "^1.0.0"
- xtend "^4.0.0"
- zwitch "^1.0.0"
-
-hast-util-to-parse5@^6.0.0:
- version "6.0.0"
- resolved "https://registry.yarnpkg.com/hast-util-to-parse5/-/hast-util-to-parse5-6.0.0.tgz#1ec44650b631d72952066cea9b1445df699f8479"
- integrity sha512-Lu5m6Lgm/fWuz8eWnrKezHtVY83JeRGaNQ2kn9aJgqaxvVkFCZQBEhgodZUDUvoodgyROHDb3r5IxAEdl6suJQ==
- dependencies:
- hast-to-hyperscript "^9.0.0"
- property-information "^5.0.0"
- web-namespaces "^1.0.0"
- xtend "^4.0.0"
- zwitch "^1.0.0"
-
-hastscript@^6.0.0:
- version "6.0.0"
- resolved "https://registry.yarnpkg.com/hastscript/-/hastscript-6.0.0.tgz#e8768d7eac56c3fdeac8a92830d58e811e5bf640"
- integrity sha512-nDM6bvd7lIqDUiYEiu5Sl/+6ReP0BMk/2f4U/Rooccxkj0P5nm+acM5PrGJ/t5I8qPGiqZSE6hVAwZEdZIvP4w==
- dependencies:
- "@types/hast" "^2.0.0"
- comma-separated-tokens "^1.0.0"
- hast-util-parse-selector "^2.0.0"
- property-information "^5.0.0"
- space-separated-tokens "^1.0.0"
-
-he@^1.2.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/he/-/he-1.2.0.tgz#84ae65fa7eafb165fddb61566ae14baf05664f0f"
- integrity sha512-F/1DnUGPopORZi0ni+CvrCgHQ5FyEAHRLSApuYWMmrbSwoN2Mn/7k+Gl38gJnR7yyDZk6WLXwiGod1JOWNDKGw==
-
-history@^4.9.0:
- version "4.10.1"
- resolved "https://registry.yarnpkg.com/history/-/history-4.10.1.tgz#33371a65e3a83b267434e2b3f3b1b4c58aad4cf3"
- integrity sha512-36nwAD620w12kuzPAsyINPWJqlNbij+hpK1k9XRloDtym8mxzGYl2c17LnV6IAGB2Dmg4tEa7G7DlawS0+qjew==
- dependencies:
- "@babel/runtime" "^7.1.2"
- loose-envify "^1.2.0"
- resolve-pathname "^3.0.0"
- tiny-invariant "^1.0.2"
- tiny-warning "^1.0.0"
- value-equal "^1.0.1"
-
-hoist-non-react-statics@^3.1.0:
- version "3.3.2"
- resolved "https://registry.yarnpkg.com/hoist-non-react-statics/-/hoist-non-react-statics-3.3.2.tgz#ece0acaf71d62c2969c2ec59feff42a4b1a85b45"
- integrity sha512-/gGivxi8JPKWNm/W0jSmzcMPpfpPLc3dY/6GxhX2hQ9iGj3aDfklV4ET7NjKpSinLpJ5vafa9iiGIEZg10SfBw==
- dependencies:
- react-is "^16.7.0"
-
-hpack.js@^2.1.6:
- version "2.1.6"
- resolved "https://registry.yarnpkg.com/hpack.js/-/hpack.js-2.1.6.tgz#87774c0949e513f42e84575b3c45681fade2a0b2"
- integrity sha512-zJxVehUdMGIKsRaNt7apO2Gqp0BdqW5yaiGHXXmbpvxgBYVZnAql+BJb4RO5ad2MgpbZKn5G6nMnegrH1FcNYQ==
- dependencies:
- inherits "^2.0.1"
- obuf "^1.0.0"
- readable-stream "^2.0.1"
- wbuf "^1.1.0"
-
-html-entities@^2.3.2:
- version "2.3.3"
- resolved "https://registry.yarnpkg.com/html-entities/-/html-entities-2.3.3.tgz#117d7626bece327fc8baace8868fa6f5ef856e46"
- integrity sha512-DV5Ln36z34NNTDgnz0EWGBLZENelNAtkiFA4kyNOG2tDI6Mz1uSWiq1wAKdyjnJwyDiDO7Fa2SO1CTxPXL8VxA==
-
-html-minifier-terser@^6.0.2, html-minifier-terser@^6.1.0:
- version "6.1.0"
- resolved "https://registry.yarnpkg.com/html-minifier-terser/-/html-minifier-terser-6.1.0.tgz#bfc818934cc07918f6b3669f5774ecdfd48f32ab"
- integrity sha512-YXxSlJBZTP7RS3tWnQw74ooKa6L9b9i9QYXY21eUEvhZ3u9XLfv6OnFsQq6RxkhHygsaUMvYsZRV5rU/OVNZxw==
- dependencies:
- camel-case "^4.1.2"
- clean-css "^5.2.2"
- commander "^8.3.0"
- he "^1.2.0"
- param-case "^3.0.4"
- relateurl "^0.2.7"
- terser "^5.10.0"
-
-html-tags@^3.2.0:
- version "3.2.0"
- resolved "https://registry.yarnpkg.com/html-tags/-/html-tags-3.2.0.tgz#dbb3518d20b726524e4dd43de397eb0a95726961"
- integrity sha512-vy7ClnArOZwCnqZgvv+ddgHgJiAFXe3Ge9ML5/mBctVJoUoYPCdxVucOywjDARn6CVoh3dRSFdPHy2sX80L0Wg==
-
-html-void-elements@^1.0.0:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/html-void-elements/-/html-void-elements-1.0.5.tgz#ce9159494e86d95e45795b166c2021c2cfca4483"
- integrity sha512-uE/TxKuyNIcx44cIWnjr/rfIATDH7ZaOMmstu0CwhFG1Dunhlp4OC6/NMbhiwoq5BpW0ubi303qnEk/PZj614w==
-
-html-webpack-plugin@^5.5.0:
- version "5.5.0"
- resolved "https://registry.yarnpkg.com/html-webpack-plugin/-/html-webpack-plugin-5.5.0.tgz#c3911936f57681c1f9f4d8b68c158cd9dfe52f50"
- integrity sha512-sy88PC2cRTVxvETRgUHFrL4No3UxvcH8G1NepGhqaTT+GXN2kTamqasot0inS5hXeg1cMbFDt27zzo9p35lZVw==
- dependencies:
- "@types/html-minifier-terser" "^6.0.0"
- html-minifier-terser "^6.0.2"
- lodash "^4.17.21"
- pretty-error "^4.0.0"
- tapable "^2.0.0"
-
-htmlparser2@^6.1.0:
- version "6.1.0"
- resolved "https://registry.yarnpkg.com/htmlparser2/-/htmlparser2-6.1.0.tgz#c4d762b6c3371a05dbe65e94ae43a9f845fb8fb7"
- integrity sha512-gyyPk6rgonLFEDGoeRgQNaEUvdJ4ktTmmUh/h2t7s+M8oPpIPxgNACWa+6ESR57kXstwqPiCut0V8NRpcwgU7A==
- dependencies:
- domelementtype "^2.0.1"
- domhandler "^4.0.0"
- domutils "^2.5.2"
- entities "^2.0.0"
-
-htmlparser2@^8.0.1:
- version "8.0.1"
- resolved "https://registry.yarnpkg.com/htmlparser2/-/htmlparser2-8.0.1.tgz#abaa985474fcefe269bc761a779b544d7196d010"
- integrity sha512-4lVbmc1diZC7GUJQtRQ5yBAeUCL1exyMwmForWkRLnwyzWBFxN633SALPMGYaWZvKe9j1pRZJpauvmxENSp/EA==
- dependencies:
- domelementtype "^2.3.0"
- domhandler "^5.0.2"
- domutils "^3.0.1"
- entities "^4.3.0"
-
-http-cache-semantics@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/http-cache-semantics/-/http-cache-semantics-4.1.1.tgz#abe02fcb2985460bf0323be664436ec3476a6d5a"
- integrity sha512-er295DKPVsV82j5kw1Gjt+ADA/XYHsajl82cGNQG2eyoPkvgUhX+nDIyelzhIWbbsXP39EHcI6l5tYs2FYqYXQ==
-
-http-deceiver@^1.2.7:
- version "1.2.7"
- resolved "https://registry.yarnpkg.com/http-deceiver/-/http-deceiver-1.2.7.tgz#fa7168944ab9a519d337cb0bec7284dc3e723d87"
- integrity sha512-LmpOGxTfbpgtGVxJrj5k7asXHCgNZp5nLfp+hWc8QQRqtb7fUy6kRY3BO1h9ddF6yIPYUARgxGOwB42DnxIaNw==
-
-http-errors@2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/http-errors/-/http-errors-2.0.0.tgz#b7774a1486ef73cf7667ac9ae0858c012c57b9d3"
- integrity sha512-FtwrG/euBzaEjYeRqOgly7G0qviiXoJWnvEH2Z1plBdXgbyjv34pHTSb9zoeHMyDy33+DWy5Wt9Wo+TURtOYSQ==
- dependencies:
- depd "2.0.0"
- inherits "2.0.4"
- setprototypeof "1.2.0"
- statuses "2.0.1"
- toidentifier "1.0.1"
-
-http-errors@~1.6.2:
- version "1.6.3"
- resolved "https://registry.yarnpkg.com/http-errors/-/http-errors-1.6.3.tgz#8b55680bb4be283a0b5bf4ea2e38580be1d9320d"
- integrity sha512-lks+lVC8dgGyh97jxvxeYTWQFvh4uw4yC12gVl63Cg30sjPX4wuGcdkICVXDAESr6OJGjqGA8Iz5mkeN6zlD7A==
- dependencies:
- depd "~1.1.2"
- inherits "2.0.3"
- setprototypeof "1.1.0"
- statuses ">= 1.4.0 < 2"
-
-http-parser-js@>=0.5.1:
- version "0.5.8"
- resolved "https://registry.yarnpkg.com/http-parser-js/-/http-parser-js-0.5.8.tgz#af23090d9ac4e24573de6f6aecc9d84a48bf20e3"
- integrity sha512-SGeBX54F94Wgu5RH3X5jsDtf4eHyRogWX1XGT3b4HuW3tQPM4AaBzoUji/4AAJNXCEOWZ5O0DgZmJw1947gD5Q==
-
-http-proxy-middleware@^2.0.3:
- version "2.0.6"
- resolved "https://registry.yarnpkg.com/http-proxy-middleware/-/http-proxy-middleware-2.0.6.tgz#e1a4dd6979572c7ab5a4e4b55095d1f32a74963f"
- integrity sha512-ya/UeJ6HVBYxrgYotAZo1KvPWlgB48kUJLDePFeneHsVujFaW5WNj2NgWCAE//B1Dl02BIfYlpNgBy8Kf8Rjmw==
- dependencies:
- "@types/http-proxy" "^1.17.8"
- http-proxy "^1.18.1"
- is-glob "^4.0.1"
- is-plain-obj "^3.0.0"
- micromatch "^4.0.2"
-
-http-proxy@^1.18.1:
- version "1.18.1"
- resolved "https://registry.yarnpkg.com/http-proxy/-/http-proxy-1.18.1.tgz#401541f0534884bbf95260334e72f88ee3976549"
- integrity sha512-7mz/721AbnJwIVbnaSv1Cz3Am0ZLT/UBwkC92VlxhXv/k/BBQfM2fXElQNC27BVGr0uwUpplYPQM9LnaBMR5NQ==
- dependencies:
- eventemitter3 "^4.0.0"
- follow-redirects "^1.0.0"
- requires-port "^1.0.0"
-
-human-signals@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/human-signals/-/human-signals-2.1.0.tgz#dc91fcba42e4d06e4abaed33b3e7a3c02f514ea0"
- integrity sha512-B4FFZ6q/T2jhhksgkbEW3HBvWIfDW85snkQgawt07S7J5QXTk6BkNV+0yAeZrM5QpMAdYlocGoljn0sJ/WQkFw==
-
-iconv-lite@0.4.24:
- version "0.4.24"
- resolved "https://registry.yarnpkg.com/iconv-lite/-/iconv-lite-0.4.24.tgz#2022b4b25fbddc21d2f524974a474aafe733908b"
- integrity sha512-v3MXnZAcvnywkTUEZomIActle7RXXeedOR31wwl7VlyoXO4Qi9arvSenNQWne1TcRwhCL1HwLI21bEqdpj8/rA==
- dependencies:
- safer-buffer ">= 2.1.2 < 3"
-
-icss-utils@^5.0.0, icss-utils@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/icss-utils/-/icss-utils-5.1.0.tgz#c6be6858abd013d768e98366ae47e25d5887b1ae"
- integrity sha512-soFhflCVWLfRNOPU3iv5Z9VUdT44xFRbzjLsEzSr5AQmgqPMTHdU3PMT1Cf1ssx8fLNJDA1juftYl+PUcv3MqA==
-
-ignore@^5.0.0, ignore@^5.2.0, ignore@~5.2.0:
- version "5.2.4"
- resolved "https://registry.yarnpkg.com/ignore/-/ignore-5.2.4.tgz#a291c0c6178ff1b960befe47fcdec301674a6324"
- integrity sha512-MAb38BcSbH0eHNBxn7ql2NH/kX33OkB3lZ1BNdh7ENeRChHTYsTvWrMubiIAMNS2llXEEgZ1MUOBtXChP3kaFQ==
-
-image-size@^1.0.1:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/image-size/-/image-size-1.0.2.tgz#d778b6d0ab75b2737c1556dd631652eb963bc486"
- integrity sha512-xfOoWjceHntRb3qFCrh5ZFORYH8XCdYpASltMhZ/Q0KZiOwjdE/Yl2QCiWdwD+lygV5bMCvauzgu5PxBX/Yerg==
- dependencies:
- queue "6.0.2"
-
-immer@^9.0.7:
- version "9.0.19"
- resolved "https://registry.yarnpkg.com/immer/-/immer-9.0.19.tgz#67fb97310555690b5f9cd8380d38fc0aabb6b38b"
- integrity sha512-eY+Y0qcsB4TZKwgQzLaE/lqYMlKhv5J9dyd2RhhtGhNo2njPXDqU9XPfcNfa3MIDsdtZt5KlkIsirlo4dHsWdQ==
-
-import-fresh@^3.1.0, import-fresh@^3.2.1, import-fresh@^3.3.0:
- version "3.3.0"
- resolved "https://registry.yarnpkg.com/import-fresh/-/import-fresh-3.3.0.tgz#37162c25fcb9ebaa2e6e53d5b4d88ce17d9e0c2b"
- integrity sha512-veYYhQa+D1QBKznvhUHxb8faxlrwUnxseDAbAp457E0wLNio2bOSKnjYDhMj+YiAq61xrMGhQk9iXVk5FzgQMw==
- dependencies:
- parent-module "^1.0.0"
- resolve-from "^4.0.0"
-
-import-lazy@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/import-lazy/-/import-lazy-2.1.0.tgz#05698e3d45c88e8d7e9d92cb0584e77f096f3e43"
- integrity sha512-m7ZEHgtw69qOGw+jwxXkHlrlIPdTGkyh66zXZ1ajZbxkDBNjSY/LGbmjc7h0s2ELsUDTAhFr55TrPSSqJGPG0A==
-
-import-meta-resolve@^2.0.0:
- version "2.2.1"
- resolved "https://registry.yarnpkg.com/import-meta-resolve/-/import-meta-resolve-2.2.1.tgz#80fdeddbc15d7f3992c37425023ffb4aca7cb583"
- integrity sha512-C6lLL7EJPY44kBvA80gq4uMsVFw5x3oSKfuMl1cuZ2RkI5+UJqQXgn+6hlUew0y4ig7Ypt4CObAAIzU53Nfpuw==
-
-imurmurhash@^0.1.4:
- version "0.1.4"
- resolved "https://registry.yarnpkg.com/imurmurhash/-/imurmurhash-0.1.4.tgz#9218b9b2b928a238b13dc4fb6b6d576f231453ea"
- integrity sha512-JmXMZ6wuvDmLiHEml9ykzqO6lwFbof0GG4IkcGaENdCRDDmMVnny7s5HsIgHCbaq0w2MyPhDqkhTUgS2LU2PHA==
-
-indent-string@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/indent-string/-/indent-string-4.0.0.tgz#624f8f4497d619b2d9768531d58f4122854d7251"
- integrity sha512-EdDDZu4A2OyIK7Lr/2zG+w5jmbuk1DVBnEwREQvBzspBJkCEbRa8GxU1lghYcaGJCnRWibjDXlq779X1/y5xwg==
-
-infima@0.2.0-alpha.42:
- version "0.2.0-alpha.42"
- resolved "https://registry.yarnpkg.com/infima/-/infima-0.2.0-alpha.42.tgz#f6e86a655ad40877c6b4d11b2ede681eb5470aa5"
- integrity sha512-ift8OXNbQQwtbIt6z16KnSWP7uJ/SysSMFI4F87MNRTicypfl4Pv3E2OGVv6N3nSZFJvA8imYulCBS64iyHYww==
-
-inflight@^1.0.4:
- version "1.0.6"
- resolved "https://registry.yarnpkg.com/inflight/-/inflight-1.0.6.tgz#49bd6331d7d02d0c09bc910a1075ba8165b56df9"
- integrity sha512-k92I/b08q4wvFscXCLvqfsHCrjrF7yiXsQuIVvVE7N82W3+aqpzuUdBbfhWcy/FZR3/4IgflMgKLOsvPDrGCJA==
- dependencies:
- once "^1.3.0"
- wrappy "1"
-
-inherits@2, inherits@2.0.4, inherits@^2.0.0, inherits@^2.0.1, inherits@^2.0.3, inherits@~2.0.3:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/inherits/-/inherits-2.0.4.tgz#0fa2c64f932917c3433a0ded55363aae37416b7c"
- integrity sha512-k/vGaX4/Yla3WzyMCvTQOXYeIHvqOKtnqBduzTHpzpQZzAskKMhZ2K+EnBiSM9zGSoIFeMpXKxa4dYeZIQqewQ==
-
-inherits@2.0.3:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/inherits/-/inherits-2.0.3.tgz#633c2c83e3da42a502f52466022480f4208261de"
- integrity sha512-x00IRNXNy63jwGkJmzPigoySHbaqpNuzKbBOmzK+g2OdZpQ9w+sxCN+VSB3ja7IAge2OP2qpfxTjeNcyjmW1uw==
-
-ini@2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/ini/-/ini-2.0.0.tgz#e5fd556ecdd5726be978fa1001862eacb0a94bc5"
- integrity sha512-7PnF4oN3CvZF23ADhA5wRaYEQpJ8qygSkbtTXWBeXWXmEVRXK+1ITciHWwHhsjv1TmW0MgacIv6hEi5pX5NQdA==
-
-ini@^1.3.5, ini@~1.3.0:
- version "1.3.8"
- resolved "https://registry.yarnpkg.com/ini/-/ini-1.3.8.tgz#a29da425b48806f34767a4efce397269af28432c"
- integrity sha512-JV/yugV2uzW5iMRSiZAyDtQd+nxtUnjeLt0acNdw98kKLrvuRVyB80tsREOE7yvGVgalhZ6RNXCmEHkUKBKxew==
-
-ini@^3.0.0, ini@~3.0.0:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/ini/-/ini-3.0.1.tgz#c76ec81007875bc44d544ff7a11a55d12294102d"
- integrity sha512-it4HyVAUTKBc6m8e1iXWvXSTdndF7HbdN713+kvLrymxTaU4AUBWrJ4vEooP+V7fexnVD3LKcBshjGGPefSMUQ==
-
-inline-style-parser@0.1.1:
- version "0.1.1"
- resolved "https://registry.yarnpkg.com/inline-style-parser/-/inline-style-parser-0.1.1.tgz#ec8a3b429274e9c0a1f1c4ffa9453a7fef72cea1"
- integrity sha512-7NXolsK4CAS5+xvdj5OMMbI962hU/wvwoxk+LWR9Ek9bVtyuuYScDN6eS0rUm6TxApFpw7CX1o4uJzcd4AyD3Q==
-
-interpret@^1.0.0:
- version "1.4.0"
- resolved "https://registry.yarnpkg.com/interpret/-/interpret-1.4.0.tgz#665ab8bc4da27a774a40584e812e3e0fa45b1a1e"
- integrity sha512-agE4QfB2Lkp9uICn7BAqoscw4SZP9kTE2hxiFI3jBPmXJfdqiahTbUuKGsMoN2GtqL9AxhYioAcVvgsb1HvRbA==
-
-invariant@^2.2.4:
- version "2.2.4"
- resolved "https://registry.yarnpkg.com/invariant/-/invariant-2.2.4.tgz#610f3c92c9359ce1db616e538008d23ff35158e6"
- integrity sha512-phJfQVBuaJM5raOpJjSfkiD6BpbCE4Ns//LaXl6wGYtUBY83nWS6Rf9tXm2e8VaK60JEjYldbPif/A2B1C2gNA==
- dependencies:
- loose-envify "^1.0.0"
-
-ipaddr.js@1.9.1:
- version "1.9.1"
- resolved "https://registry.yarnpkg.com/ipaddr.js/-/ipaddr.js-1.9.1.tgz#bff38543eeb8984825079ff3a2a8e6cbd46781b3"
- integrity sha512-0KI/607xoxSToH7GjN1FfSbLoU0+btTicjsQSWQlh/hZykN8KpmMf7uYwPW3R+akZ6R/w18ZlXSHBYXiYUPO3g==
-
-ipaddr.js@^2.0.1:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/ipaddr.js/-/ipaddr.js-2.0.1.tgz#eca256a7a877e917aeb368b0a7497ddf42ef81c0"
- integrity sha512-1qTgH9NG+IIJ4yfKs2e6Pp1bZg8wbDbKHT21HrLIeYBTRLgMYKnMTPAuI3Lcs61nfx5h1xlXnbJtH1kX5/d/ng==
-
-is-alphabetical@1.0.4, is-alphabetical@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/is-alphabetical/-/is-alphabetical-1.0.4.tgz#9e7d6b94916be22153745d184c298cbf986a686d"
- integrity sha512-DwzsA04LQ10FHTZuL0/grVDk4rFoVH1pjAToYwBrHSxcrBIGQuXrQMtD5U1b0U2XVgKZCTLLP8u2Qxqhy3l2Vg==
-
-is-alphabetical@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/is-alphabetical/-/is-alphabetical-2.0.1.tgz#01072053ea7c1036df3c7d19a6daaec7f19e789b"
- integrity sha512-FWyyY60MeTNyeSRpkM2Iry0G9hpr7/9kD40mD/cGQEuilcZYS4okz8SN2Q6rLCJ8gbCt6fN+rC+6tMGS99LaxQ==
-
-is-alphanumerical@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/is-alphanumerical/-/is-alphanumerical-1.0.4.tgz#7eb9a2431f855f6b1ef1a78e326df515696c4dbf"
- integrity sha512-UzoZUr+XfVz3t3v4KyGEniVL9BDRoQtY7tOyrRybkVNjDFWyo1yhXNGrrBTQxp3ib9BLAWs7k2YKBQsFRkZG9A==
- dependencies:
- is-alphabetical "^1.0.0"
- is-decimal "^1.0.0"
-
-is-alphanumerical@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/is-alphanumerical/-/is-alphanumerical-2.0.1.tgz#7c03fbe96e3e931113e57f964b0a368cc2dfd875"
- integrity sha512-hmbYhX/9MUMF5uh7tOXyK/n0ZvWpad5caBA17GsC6vyuCqaWliRG5K1qS9inmUhEMaOBIW7/whAnSwveW/LtZw==
- dependencies:
- is-alphabetical "^2.0.0"
- is-decimal "^2.0.0"
-
-is-arrayish@^0.2.1:
- version "0.2.1"
- resolved "https://registry.yarnpkg.com/is-arrayish/-/is-arrayish-0.2.1.tgz#77c99840527aa8ecb1a8ba697b80645a7a926a9d"
- integrity sha512-zz06S8t0ozoDXMG+ube26zeCTNXcKIPJZJi8hBrF4idCLms4CG9QtK7qBl1boi5ODzFpjswb5JPmHCbMpjaYzg==
-
-is-binary-path@~2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/is-binary-path/-/is-binary-path-2.1.0.tgz#ea1f7f3b80f064236e83470f86c09c254fb45b09"
- integrity sha512-ZMERYes6pDydyuGidse7OsHxtbI7WVeUEozgR/g7rd0xUimYNlvZRE/K2MgZTjWy725IfelLeVcEM97mmtRGXw==
- dependencies:
- binary-extensions "^2.0.0"
-
-is-buffer@^2.0.0:
- version "2.0.5"
- resolved "https://registry.yarnpkg.com/is-buffer/-/is-buffer-2.0.5.tgz#ebc252e400d22ff8d77fa09888821a24a658c191"
- integrity sha512-i2R6zNFDwgEHJyQUtJEk0XFi1i0dPFn/oqjK3/vPCcDeJvW5NQ83V8QbicfF1SupOaB0h8ntgBC2YiE7dfyctQ==
-
-is-ci@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/is-ci/-/is-ci-2.0.0.tgz#6bc6334181810e04b5c22b3d589fdca55026404c"
- integrity sha512-YfJT7rkpQB0updsdHLGWrvhBJfcfzNNawYDNIyQXJz0IViGf75O8EBPKSdvw2rF+LGCsX4FZ8tcr3b19LcZq4w==
- dependencies:
- ci-info "^2.0.0"
-
-is-core-module@^2.9.0:
- version "2.11.0"
- resolved "https://registry.yarnpkg.com/is-core-module/-/is-core-module-2.11.0.tgz#ad4cb3e3863e814523c96f3f58d26cc570ff0144"
- integrity sha512-RRjxlvLDkD1YJwDbroBHMb+cukurkDWNyHx7D3oNB5x9rb5ogcksMC5wHCadcXoo67gVr/+3GFySh3134zi6rw==
- dependencies:
- has "^1.0.3"
-
-is-decimal@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/is-decimal/-/is-decimal-1.0.4.tgz#65a3a5958a1c5b63a706e1b333d7cd9f630d3fa5"
- integrity sha512-RGdriMmQQvZ2aqaQq3awNA6dCGtKpiDFcOzrTWrDAT2MiWrKQVPmxLGHl7Y2nNu6led0kEyoX0enY0qXYsv9zw==
-
-is-decimal@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/is-decimal/-/is-decimal-2.0.1.tgz#9469d2dc190d0214fd87d78b78caecc0cc14eef7"
- integrity sha512-AAB9hiomQs5DXWcRB1rqsxGUstbRroFOPPVAomNk/3XHR5JyEZChOyTWe2oayKnsSsr/kcGqF+z6yuH6HHpN0A==
-
-is-docker@^2.0.0, is-docker@^2.1.1:
- version "2.2.1"
- resolved "https://registry.yarnpkg.com/is-docker/-/is-docker-2.2.1.tgz#33eeabe23cfe86f14bde4408a02c0cfb853acdaa"
- integrity sha512-F+i2BKsFrH66iaUFc0woD8sLy8getkwTwtOBjvs56Cx4CgJDeKQeqfz8wAYiSb8JOprWhHH5p77PbmYCvvUuXQ==
-
-is-empty@^1.0.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/is-empty/-/is-empty-1.2.0.tgz#de9bb5b278738a05a0b09a57e1fb4d4a341a9f6b"
- integrity sha512-F2FnH/otLNJv0J6wc73A5Xo7oHLNnqplYqZhUu01tD54DIPvxIRSTSLkrUB/M0nHO4vo1O9PDfN4KoTxCzLh/w==
-
-is-extendable@^0.1.0:
- version "0.1.1"
- resolved "https://registry.yarnpkg.com/is-extendable/-/is-extendable-0.1.1.tgz#62b110e289a471418e3ec36a617d472e301dfc89"
- integrity sha512-5BMULNob1vgFX6EjQw5izWDxrecWK9AM72rugNr0TFldMOi0fj6Jk+zeKIt0xGj4cEfQIJth4w3OKWOJ4f+AFw==
-
-is-extglob@^2.1.1:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/is-extglob/-/is-extglob-2.1.1.tgz#a88c02535791f02ed37c76a1b9ea9773c833f8c2"
- integrity sha512-SbKbANkN603Vi4jEZv49LeVJMn4yGwsbzZworEoyEiutsN3nJYdbO36zfhGJ6QEDpOZIFkDtnq5JRxmvl3jsoQ==
-
-is-fullwidth-code-point@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/is-fullwidth-code-point/-/is-fullwidth-code-point-3.0.0.tgz#f116f8064fe90b3f7844a38997c0b75051269f1d"
- integrity sha512-zymm5+u+sCsSWyD9qNaejV3DFvhCKclKdizYaJUuHA83RLjb7nSuGnddCHGv0hk+KY7BMAlsWeK4Ueg6EV6XQg==
-
-is-glob@^4.0.1, is-glob@^4.0.3, is-glob@~4.0.1:
- version "4.0.3"
- resolved "https://registry.yarnpkg.com/is-glob/-/is-glob-4.0.3.tgz#64f61e42cbbb2eec2071a9dac0b28ba1e65d5084"
- integrity sha512-xelSayHH36ZgE7ZWhli7pW34hNbNl8Ojv5KVmkJD4hBdD3th8Tfk9vYasLM+mXWOZhFkgZfxhLSnrwRr4elSSg==
- dependencies:
- is-extglob "^2.1.1"
-
-is-hexadecimal@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/is-hexadecimal/-/is-hexadecimal-1.0.4.tgz#cc35c97588da4bd49a8eedd6bc4082d44dcb23a7"
- integrity sha512-gyPJuv83bHMpocVYoqof5VDiZveEoGoFL8m3BXNb2VW8Xs+rz9kqO8LOQ5DH6EsuvilT1ApazU0pyl+ytbPtlw==
-
-is-hexadecimal@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/is-hexadecimal/-/is-hexadecimal-2.0.1.tgz#86b5bf668fca307498d319dfc03289d781a90027"
- integrity sha512-DgZQp241c8oO6cA1SbTEWiXeoxV42vlcJxgH+B3hi1AiqqKruZR3ZGF8In3fj4+/y/7rHvlOZLZtgJ/4ttYGZg==
-
-is-installed-globally@^0.4.0:
- version "0.4.0"
- resolved "https://registry.yarnpkg.com/is-installed-globally/-/is-installed-globally-0.4.0.tgz#9a0fd407949c30f86eb6959ef1b7994ed0b7b520"
- integrity sha512-iwGqO3J21aaSkC7jWnHP/difazwS7SFeIqxv6wEtLU8Y5KlzFTjyqcSIT0d8s4+dDhKytsk9PJZ2BkS5eZwQRQ==
- dependencies:
- global-dirs "^3.0.0"
- is-path-inside "^3.0.2"
-
-is-npm@^5.0.0:
- version "5.0.0"
- resolved "https://registry.yarnpkg.com/is-npm/-/is-npm-5.0.0.tgz#43e8d65cc56e1b67f8d47262cf667099193f45a8"
- integrity sha512-WW/rQLOazUq+ST/bCAVBp/2oMERWLsR7OrKyt052dNDk4DHcDE0/7QSXITlmi+VBcV13DfIbysG3tZJm5RfdBA==
-
-is-number@^7.0.0:
- version "7.0.0"
- resolved "https://registry.yarnpkg.com/is-number/-/is-number-7.0.0.tgz#7535345b896734d5f80c4d06c50955527a14f12b"
- integrity sha512-41Cifkg6e8TylSpdtTpeLVMqvSBEVzTttHvERD741+pnZ8ANv0004MRL43QKPDlK9cGvNp6NZWZUBlbGXYxxng==
-
-is-obj@^1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/is-obj/-/is-obj-1.0.1.tgz#3e4729ac1f5fde025cd7d83a896dab9f4f67db0f"
- integrity sha512-l4RyHgRqGN4Y3+9JHVrNqO+tN0rV5My76uW5/nuO4K1b6vw5G8d/cmFjP9tRfEsdhZNt0IFdZuK/c2Vr4Nb+Qg==
-
-is-obj@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/is-obj/-/is-obj-2.0.0.tgz#473fb05d973705e3fd9620545018ca8e22ef4982"
- integrity sha512-drqDG3cbczxxEJRoOXcOjtdp1J/lyp1mNn0xaznRs8+muBhgQcrnbspox5X5fOw0HnMnbfDzvnEMEtqDEJEo8w==
-
-is-path-cwd@^2.2.0:
- version "2.2.0"
- resolved "https://registry.yarnpkg.com/is-path-cwd/-/is-path-cwd-2.2.0.tgz#67d43b82664a7b5191fd9119127eb300048a9fdb"
- integrity sha512-w942bTcih8fdJPJmQHFzkS76NEP8Kzzvmw92cXsazb8intwLqPibPPdXf4ANdKV3rYMuuQYGIWtvz9JilB3NFQ==
-
-is-path-inside@^3.0.2:
- version "3.0.3"
- resolved "https://registry.yarnpkg.com/is-path-inside/-/is-path-inside-3.0.3.tgz#d231362e53a07ff2b0e0ea7fed049161ffd16283"
- integrity sha512-Fd4gABb+ycGAmKou8eMftCupSir5lRxqf4aD/vd0cD2qc4HL07OjCeuHMr8Ro4CoMaeCKDB0/ECBOVWjTwUvPQ==
-
-is-plain-obj@^2.0.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/is-plain-obj/-/is-plain-obj-2.1.0.tgz#45e42e37fccf1f40da8e5f76ee21515840c09287"
- integrity sha512-YWnfyRwxL/+SsrWYfOpUtz5b3YD+nyfkHvjbcanzk8zgyO4ASD67uVMRt8k5bM4lLMDnXfriRhOpemw+NfT1eA==
-
-is-plain-obj@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/is-plain-obj/-/is-plain-obj-3.0.0.tgz#af6f2ea14ac5a646183a5bbdb5baabbc156ad9d7"
- integrity sha512-gwsOE28k+23GP1B6vFl1oVh/WOzmawBrKwo5Ev6wMKzPkaXaCDIQKzLnvsA42DRlbVTWorkgTKIviAKCWkfUwA==
-
-is-plain-obj@^4.0.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/is-plain-obj/-/is-plain-obj-4.1.0.tgz#d65025edec3657ce032fd7db63c97883eaed71f0"
- integrity sha512-+Pgi+vMuUNkJyExiMBt5IlFoMyKnr5zhJ4Uspz58WOhBF5QoIZkFyNHIbBAtHwzVAgk5RtndVNsDRN61/mmDqg==
-
-is-plain-object@^2.0.4:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/is-plain-object/-/is-plain-object-2.0.4.tgz#2c163b3fafb1b606d9d17928f05c2a1c38e07677"
- integrity sha512-h5PpgXkWitc38BBMYawTYMWJHFZJVnBquFE57xFpjB8pJFiF6gZ+bU+WyI/yqXiFR5mdLsgYNaPe8uao6Uv9Og==
- dependencies:
- isobject "^3.0.1"
-
-is-regexp@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/is-regexp/-/is-regexp-1.0.0.tgz#fd2d883545c46bac5a633e7b9a09e87fa2cb5069"
- integrity sha512-7zjFAPO4/gwyQAAgRRmqeEeyIICSdmCqa3tsVHMdBzaXXRiqopZL4Cyghg/XulGWrtABTpbnYYzzIRffLkP4oA==
-
-is-root@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/is-root/-/is-root-2.1.0.tgz#809e18129cf1129644302a4f8544035d51984a9c"
- integrity sha512-AGOriNp96vNBd3HtU+RzFEc75FfR5ymiYv8E553I71SCeXBiMsVDUtdio1OEFvrPyLIQ9tVR5RxXIFe5PUFjMg==
-
-is-stream@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/is-stream/-/is-stream-2.0.1.tgz#fac1e3d53b97ad5a9d0ae9cef2389f5810a5c077"
- integrity sha512-hFoiJiTl63nn+kstHGBtewWSKnQLpyb155KHheA1l39uvtO9nWIop1p3udqPcUd/xbF1VLMO4n7OI6p7RbngDg==
-
-is-typedarray@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/is-typedarray/-/is-typedarray-1.0.0.tgz#e479c80858df0c1b11ddda6940f96011fcda4a9a"
- integrity sha512-cyA56iCMHAh5CdzjJIa4aohJyeO1YbwLi3Jc35MmRU6poroFjIGZzUzupGiRPOjgHg9TLu43xbpwXk523fMxKA==
-
-is-whitespace-character@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/is-whitespace-character/-/is-whitespace-character-1.0.4.tgz#0858edd94a95594c7c9dd0b5c174ec6e45ee4aa7"
- integrity sha512-SDweEzfIZM0SJV0EUga669UTKlmL0Pq8Lno0QDQsPnvECB3IM2aP0gdx5TrU0A01MAPfViaZiI2V1QMZLaKK5w==
-
-is-word-character@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/is-word-character/-/is-word-character-1.0.4.tgz#ce0e73216f98599060592f62ff31354ddbeb0230"
- integrity sha512-5SMO8RVennx3nZrqtKwCGyyetPE9VDba5ugvKLaD4KopPG5kR4mQ7tNt/r7feL5yt5h3lpuBbIUmCOG2eSzXHA==
-
-is-wsl@^2.2.0:
- version "2.2.0"
- resolved "https://registry.yarnpkg.com/is-wsl/-/is-wsl-2.2.0.tgz#74a4c76e77ca9fd3f932f290c17ea326cd157271"
- integrity sha512-fKzAra0rGJUUBwGBgNkHZuToZcn+TtXHpeCgmkMJMMYx1sQDYaCSyjJBSCa2nH1DGm7s3n1oBnohoVTBaN7Lww==
- dependencies:
- is-docker "^2.0.0"
-
-is-yarn-global@^0.3.0:
- version "0.3.0"
- resolved "https://registry.yarnpkg.com/is-yarn-global/-/is-yarn-global-0.3.0.tgz#d502d3382590ea3004893746754c89139973e232"
- integrity sha512-VjSeb/lHmkoyd8ryPVIKvOCn4D1koMqY+vqyjjUfc3xyKtP4dYOxM44sZrnqQSzSds3xyOrUTLTC9LVCVgLngw==
-
-isarray@0.0.1:
- version "0.0.1"
- resolved "https://registry.yarnpkg.com/isarray/-/isarray-0.0.1.tgz#8a18acfca9a8f4177e09abfc6038939b05d1eedf"
- integrity sha512-D2S+3GLxWH+uhrNEcoh/fnmYeP8E8/zHl644d/jdA0g2uyXvy3sb0qxotE+ne0LtccHknQzWwZEzhak7oJ0COQ==
-
-isarray@~1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/isarray/-/isarray-1.0.0.tgz#bb935d48582cba168c06834957a54a3e07124f11"
- integrity sha512-VLghIWNM6ELQzo7zwmcg0NmTVyWKYjvIeM83yjp0wRDTmUnrM678fQbcKBo6n2CJEF0szoG//ytg+TKla89ALQ==
-
-isexe@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/isexe/-/isexe-2.0.0.tgz#e8fbf374dc556ff8947a10dcb0572d633f2cfa10"
- integrity sha512-RHxMLp9lnKHGHRng9QFhRCMbYAcVpn69smSGcq3f36xjgVVWThj4qqLbTLlq7Ssj8B+fIQ1EuCEGI2lKsyQeIw==
-
-isobject@^3.0.1:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/isobject/-/isobject-3.0.1.tgz#4e431e92b11a9731636aa1f9c8d1ccbcfdab78df"
- integrity sha512-WhB9zCku7EGTj/HQQRz5aUQEUeoQZH2bWcltRErOpymJ4boYE6wL9Tbr23krRPSZ+C5zqNSrSw+Cc7sZZ4b7vg==
-
-jest-util@^29.4.2:
- version "29.4.2"
- resolved "https://registry.yarnpkg.com/jest-util/-/jest-util-29.4.2.tgz#3db8580b295df453a97de4a1b42dd2578dabd2c2"
- integrity sha512-wKnm6XpJgzMUSRFB7YF48CuwdzuDIHenVuoIb1PLuJ6F+uErZsuDkU+EiExkChf6473XcawBrSfDSnXl+/YG4g==
- dependencies:
- "@jest/types" "^29.4.2"
- "@types/node" "*"
- chalk "^4.0.0"
- ci-info "^3.2.0"
- graceful-fs "^4.2.9"
- picomatch "^2.2.3"
-
-jest-worker@^27.4.5, jest-worker@^27.5.1:
- version "27.5.1"
- resolved "https://registry.yarnpkg.com/jest-worker/-/jest-worker-27.5.1.tgz#8d146f0900e8973b106b6f73cc1e9a8cb86f8db0"
- integrity sha512-7vuh85V5cdDofPyxn58nrPjBktZo0u9x1g8WtjQol+jZDaE+fhN+cIvTj11GndBnMnyfrUOG1sZQxCdjKh+DKg==
- dependencies:
- "@types/node" "*"
- merge-stream "^2.0.0"
- supports-color "^8.0.0"
-
-jest-worker@^29.1.2:
- version "29.4.2"
- resolved "https://registry.yarnpkg.com/jest-worker/-/jest-worker-29.4.2.tgz#d9b2c3bafc69311d84d94e7fb45677fc8976296f"
- integrity sha512-VIuZA2hZmFyRbchsUCHEehoSf2HEl0YVF8SDJqtPnKorAaBuh42V8QsLnde0XP5F6TyCynGPEGgBOn3Fc+wZGw==
- dependencies:
- "@types/node" "*"
- jest-util "^29.4.2"
- merge-stream "^2.0.0"
- supports-color "^8.0.0"
-
-joi@^17.6.0:
- version "17.7.1"
- resolved "https://registry.yarnpkg.com/joi/-/joi-17.7.1.tgz#854fc85c7fa3cfc47c91124d30bffdbb58e06cec"
- integrity sha512-teoLhIvWE298R6AeJywcjR4sX2hHjB3/xJX4qPjg+gTg+c0mzUDsziYlqPmLomq9gVsfaMcgPaGc7VxtD/9StA==
- dependencies:
- "@hapi/hoek" "^9.0.0"
- "@hapi/topo" "^5.0.0"
- "@sideway/address" "^4.1.3"
- "@sideway/formula" "^3.0.1"
- "@sideway/pinpoint" "^2.0.0"
-
-"js-tokens@^3.0.0 || ^4.0.0", js-tokens@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/js-tokens/-/js-tokens-4.0.0.tgz#19203fb59991df98e3a287050d4647cdeaf32499"
- integrity sha512-RdJUflcE3cUzKiMqQgsCu06FPu9UdIJO0beYbPhHN4k6apgJtifcoCtT9bcxOpYBtpD2kCM6Sbzg4CausW/PKQ==
-
-js-yaml@^3.13.1:
- version "3.14.1"
- resolved "https://registry.yarnpkg.com/js-yaml/-/js-yaml-3.14.1.tgz#dae812fdb3825fa306609a8717383c50c36a0537"
- integrity sha512-okMH7OXXJ7YrN9Ok3/SXrnu4iX9yOk+25nqX4imS2npuvTYDmo/QEZoqwZkYaIDk3jVvBOTOIEgEhaLOynBS9g==
- dependencies:
- argparse "^1.0.7"
- esprima "^4.0.0"
-
-js-yaml@^4.1.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/js-yaml/-/js-yaml-4.1.0.tgz#c1fb65f8f5017901cdd2c951864ba18458a10602"
- integrity sha512-wpxZs9NoxZaJESJGIZTyDEaYpl0FKSA+FB9aJiyemKhMwkxQg63h4T1KJgUGHpTqPDNRcmmYLugrRjJlBtWvRA==
- dependencies:
- argparse "^2.0.1"
-
-jsesc@^2.5.1:
- version "2.5.2"
- resolved "https://registry.yarnpkg.com/jsesc/-/jsesc-2.5.2.tgz#80564d2e483dacf6e8ef209650a67df3f0c283a4"
- integrity sha512-OYu7XEzjkCQ3C5Ps3QIZsQfNpqoJyZZA99wd9aWd05NCtC5pWOkShK2mkL6HXQR6/Cy2lbNdPlZBpuQHXE63gA==
-
-jsesc@~0.5.0:
- version "0.5.0"
- resolved "https://registry.yarnpkg.com/jsesc/-/jsesc-0.5.0.tgz#e7dee66e35d6fc16f710fe91d5cf69f70f08911d"
- integrity sha512-uZz5UnB7u4T9LvwmFqXii7pZSouaRPorGs5who1Ip7VO0wxanFvBL7GkM6dTHlgX+jhBApRetaWpnDabOeTcnA==
-
-json-buffer@3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/json-buffer/-/json-buffer-3.0.0.tgz#5b1f397afc75d677bde8bcfc0e47e1f9a3d9a898"
- integrity sha512-CuUqjv0FUZIdXkHPI8MezCnFCdaTAacej1TZYulLoAg1h/PhwkdXFN4V/gzY4g+fMBCOV2xF+rp7t2XD2ns/NQ==
-
-json-parse-even-better-errors@^2.3.0, json-parse-even-better-errors@^2.3.1:
- version "2.3.1"
- resolved "https://registry.yarnpkg.com/json-parse-even-better-errors/-/json-parse-even-better-errors-2.3.1.tgz#7c47805a94319928e05777405dc12e1f7a4ee02d"
- integrity sha512-xyFwyhro/JEof6Ghe2iz2NcXoj2sloNsWr/XsERDK/oiPCfaNhl5ONfp+jQdAZRQQ0IJWNzH9zIZF7li91kh2w==
-
-json-parse-even-better-errors@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/json-parse-even-better-errors/-/json-parse-even-better-errors-3.0.0.tgz#2cb2ee33069a78870a0c7e3da560026b89669cf7"
- integrity sha512-iZbGHafX/59r39gPwVPRBGw0QQKnA7tte5pSMrhWOW7swGsVvVTjmfyAV9pNqk8YGT7tRCdxRu8uzcgZwoDooA==
-
-json-schema-traverse@^0.4.1:
- version "0.4.1"
- resolved "https://registry.yarnpkg.com/json-schema-traverse/-/json-schema-traverse-0.4.1.tgz#69f6a87d9513ab8bb8fe63bdb0979c448e684660"
- integrity sha512-xbbCH5dCYU5T8LcEhhuh7HJ88HXuW3qsI3Y0zOZFKfZEHcpWiHU/Jxzk629Brsab/mMiHQti9wMP+845RPe3Vg==
-
-json-schema-traverse@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/json-schema-traverse/-/json-schema-traverse-1.0.0.tgz#ae7bcb3656ab77a73ba5c49bf654f38e6b6860e2"
- integrity sha512-NM8/P9n3XjXhIZn1lLhkFaACTOURQXjWhV4BA/RnOv8xvgqtqpAX9IO4mRQxSx1Rlo4tqzeqb0sOlruaOy3dug==
-
-json5@^2.0.0, json5@^2.1.2, json5@^2.2.2:
- version "2.2.3"
- resolved "https://registry.yarnpkg.com/json5/-/json5-2.2.3.tgz#78cd6f1a19bdc12b73db5ad0c61efd66c1e29283"
- integrity sha512-XmOWe7eyHYH14cLdVPoyg+GOH3rYX++KpzrylJwSW98t3Nk+U8XOl8FWKOgwtzdb8lXGf6zYwDUzeHMWfxasyg==
-
-jsonc-parser@~3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/jsonc-parser/-/jsonc-parser-3.0.0.tgz#abdd785701c7e7eaca8a9ec8cf070ca51a745a22"
- integrity sha512-fQzRfAbIBnR0IQvftw9FJveWiHp72Fg20giDrHz6TdfB12UH/uue0D3hm57UB5KgAVuniLMCaS8P1IMj9NR7cA==
-
-jsonfile@^6.0.1:
- version "6.1.0"
- resolved "https://registry.yarnpkg.com/jsonfile/-/jsonfile-6.1.0.tgz#bc55b2634793c679ec6403094eb13698a6ec0aae"
- integrity sha512-5dgndWOriYSm5cnYaJNhalLNDKOqFwyDB/rr1E9ZsGciGvKPs8R2xYGCacuf3z6K1YKDz182fd+fY3cn3pMqXQ==
- dependencies:
- universalify "^2.0.0"
- optionalDependencies:
- graceful-fs "^4.1.6"
-
-keyv@^3.0.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/keyv/-/keyv-3.1.0.tgz#ecc228486f69991e49e9476485a5be1e8fc5c4d9"
- integrity sha512-9ykJ/46SN/9KPM/sichzQ7OvXyGDYKGTaDlKMGCAlg2UK8KRy4jb0d8sFc+0Tt0YYnThq8X2RZgCg74RPxgcVA==
- dependencies:
- json-buffer "3.0.0"
-
-kind-of@^6.0.0, kind-of@^6.0.2:
- version "6.0.3"
- resolved "https://registry.yarnpkg.com/kind-of/-/kind-of-6.0.3.tgz#07c05034a6c349fa06e24fa35aa76db4580ce4dd"
- integrity sha512-dcS1ul+9tmeD95T+x28/ehLgd9mENa3LsvDTtzm3vyBEO7RPptvAD+t44WVXaUjTBRcrpFeFlC8WCruUR456hw==
-
-kleur@^3.0.3:
- version "3.0.3"
- resolved "https://registry.yarnpkg.com/kleur/-/kleur-3.0.3.tgz#a79c9ecc86ee1ce3fa6206d1216c501f147fc07e"
- integrity sha512-eTIzlVOSUR+JxdDFepEYcBMtZ9Qqdef+rnzWdRZuMbOywu5tO2w2N7rqjoANZ5k9vywhL6Br1VRjUIgTQx4E8w==
-
-kleur@^4.0.3:
- version "4.1.5"
- resolved "https://registry.yarnpkg.com/kleur/-/kleur-4.1.5.tgz#95106101795f7050c6c650f350c683febddb1780"
- integrity sha512-o+NO+8WrRiQEE4/7nwRJhN1HWpVmJm511pBHUxPLtp0BUISzlBplORYSmTclCnJvQq2tKu/sgl3xVpkc7ZWuQQ==
-
-klona@^2.0.5:
- version "2.0.6"
- resolved "https://registry.yarnpkg.com/klona/-/klona-2.0.6.tgz#85bffbf819c03b2f53270412420a4555ef882e22"
- integrity sha512-dhG34DXATL5hSxJbIexCft8FChFXtmskoZYnoPWjXQuebWYCNkVeV3KkGegCK9CP1oswI/vQibS2GY7Em/sJJA==
-
-latest-version@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/latest-version/-/latest-version-5.1.0.tgz#119dfe908fe38d15dfa43ecd13fa12ec8832face"
- integrity sha512-weT+r0kTkRQdCdYCNtkMwWXQTMEswKrFBkm4ckQOMVhhqhIMI1UT2hMj+1iigIhgSZm5gTmrRXBNoGUgaTY1xA==
- dependencies:
- package-json "^6.3.0"
-
-leven@^3.1.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/leven/-/leven-3.1.0.tgz#77891de834064cccba82ae7842bb6b14a13ed7f2"
- integrity sha512-qsda+H8jTaUaN/x5vzW2rzc+8Rw4TAQ/4KjB46IwK5VH+IlVeeeje/EoZRpiXvIqjFgK84QffqPztGI3VBLG1A==
-
-lilconfig@^2.0.3:
- version "2.0.6"
- resolved "https://registry.yarnpkg.com/lilconfig/-/lilconfig-2.0.6.tgz#32a384558bd58af3d4c6e077dd1ad1d397bc69d4"
- integrity sha512-9JROoBW7pobfsx+Sq2JsASvCo6Pfo6WWoUW79HuB1BCoBXD4PLWJPqDF6fNj67pqBYTbAHkE57M1kS/+L1neOg==
-
-lines-and-columns@^1.1.6:
- version "1.2.4"
- resolved "https://registry.yarnpkg.com/lines-and-columns/-/lines-and-columns-1.2.4.tgz#eca284f75d2965079309dc0ad9255abb2ebc1632"
- integrity sha512-7ylylesZQ/PV29jhEDl3Ufjo6ZX7gCqJr5F7PKrqc93v7fzSymt1BpwEU8nAUXs8qzzvqhbjhK5QZg6Mt/HkBg==
-
-lines-and-columns@^2.0.2:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/lines-and-columns/-/lines-and-columns-2.0.3.tgz#b2f0badedb556b747020ab8ea7f0373e22efac1b"
- integrity sha512-cNOjgCnLB+FnvWWtyRTzmB3POJ+cXxTA81LoW7u8JdmhfXzriropYwpjShnz1QLLWsQwY7nIxoDmcPTwphDK9w==
-
-linkify-it@^3.0.1:
- version "3.0.3"
- resolved "https://registry.yarnpkg.com/linkify-it/-/linkify-it-3.0.3.tgz#a98baf44ce45a550efb4d49c769d07524cc2fa2e"
- integrity sha512-ynTsyrFSdE5oZ/O9GEf00kPngmOfVwazR5GKDq6EYfhlpFug3J2zybX56a2PRRpc9P+FuSoGNAwjlbDs9jJBPQ==
- dependencies:
- uc.micro "^1.0.1"
-
-load-plugin@^5.0.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/load-plugin/-/load-plugin-5.1.0.tgz#15600f5191c742b16e058cfc908c227c13db0104"
- integrity sha512-Lg1CZa1CFj2CbNaxijTL6PCbzd4qGTlZov+iH2p5Xwy/ApcZJh+i6jMN2cYePouTfjJfrNu3nXFdEw8LvbjPFQ==
- dependencies:
- "@npmcli/config" "^6.0.0"
- import-meta-resolve "^2.0.0"
-
-loader-runner@^4.2.0:
- version "4.3.0"
- resolved "https://registry.yarnpkg.com/loader-runner/-/loader-runner-4.3.0.tgz#c1b4a163b99f614830353b16755e7149ac2314e1"
- integrity sha512-3R/1M+yS3j5ou80Me59j7F9IMs4PXs3VqRrm0TU3AbKPxlmpoY1TNscJV/oGJXo8qCatFGTfDbY6W6ipGOYXfg==
-
-loader-utils@^2.0.0:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/loader-utils/-/loader-utils-2.0.4.tgz#8b5cb38b5c34a9a018ee1fc0e6a066d1dfcc528c"
- integrity sha512-xXqpXoINfFhgua9xiqD8fPFHgkoq1mmmpE92WlDbm9rNRd/EbRb+Gqf908T2DMfuHjjJlksiK2RbHVOdD/MqSw==
- dependencies:
- big.js "^5.2.2"
- emojis-list "^3.0.0"
- json5 "^2.1.2"
-
-loader-utils@^3.2.0:
- version "3.2.1"
- resolved "https://registry.yarnpkg.com/loader-utils/-/loader-utils-3.2.1.tgz#4fb104b599daafd82ef3e1a41fb9265f87e1f576"
- integrity sha512-ZvFw1KWS3GVyYBYb7qkmRM/WwL2TQQBxgCK62rlvm4WpVQ23Nb4tYjApUlfjrEGvOs7KHEsmyUn75OHZrJMWPw==
-
-locate-path@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/locate-path/-/locate-path-3.0.0.tgz#dbec3b3ab759758071b58fe59fc41871af21400e"
- integrity sha512-7AO748wWnIhNqAuaty2ZWHkQHRSNfPVIsPIfwEOWO22AmaoVrWavlOcMR5nzTLNYvp36X220/maaRsrec1G65A==
- dependencies:
- p-locate "^3.0.0"
- path-exists "^3.0.0"
-
-locate-path@^5.0.0:
- version "5.0.0"
- resolved "https://registry.yarnpkg.com/locate-path/-/locate-path-5.0.0.tgz#1afba396afd676a6d42504d0a67a3a7eb9f62aa0"
- integrity sha512-t7hw9pI+WvuwNJXwk5zVHpyhIqzg2qTlklJOf0mVxGSbe3Fp2VieZcduNYjaLDoy6p9uGpQEGWG87WpMKlNq8g==
- dependencies:
- p-locate "^4.1.0"
-
-locate-path@^6.0.0:
- version "6.0.0"
- resolved "https://registry.yarnpkg.com/locate-path/-/locate-path-6.0.0.tgz#55321eb309febbc59c4801d931a72452a681d286"
- integrity sha512-iPZK6eYjbxRu3uB4/WZ3EsEIMJFMqAoopl3R+zuq0UjcAm/MO6KCweDgPfP3elTztoKP3KtnVHxTn2NHBSDVUw==
- dependencies:
- p-locate "^5.0.0"
-
-lodash.curry@^4.0.1:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/lodash.curry/-/lodash.curry-4.1.1.tgz#248e36072ede906501d75966200a86dab8b23170"
- integrity sha512-/u14pXGviLaweY5JI0IUzgzF2J6Ne8INyzAZjImcryjgkZ+ebruBxy2/JaOOkTqScddcYtakjhSaeemV8lR0tA==
-
-lodash.debounce@^4.0.8:
- version "4.0.8"
- resolved "https://registry.yarnpkg.com/lodash.debounce/-/lodash.debounce-4.0.8.tgz#82d79bff30a67c4005ffd5e2515300ad9ca4d7af"
- integrity sha512-FT1yDzDYEoYWhnSGnpE/4Kj1fLZkDFyqRb7fNt6FdYOSxlUWAtp42Eh6Wb0rGIv/m9Bgo7x4GhQbm5Ys4SG5ow==
-
-lodash.flow@^3.3.0:
- version "3.5.0"
- resolved "https://registry.yarnpkg.com/lodash.flow/-/lodash.flow-3.5.0.tgz#87bf40292b8cf83e4e8ce1a3ae4209e20071675a"
- integrity sha512-ff3BX/tSioo+XojX4MOsOMhJw0nZoUEF011LX8g8d3gvjVbxd89cCio4BCXronjxcTUIJUoqKEUA+n4CqvvRPw==
-
-lodash.memoize@^4.1.2:
- version "4.1.2"
- resolved "https://registry.yarnpkg.com/lodash.memoize/-/lodash.memoize-4.1.2.tgz#bcc6c49a42a2840ed997f323eada5ecd182e0bfe"
- integrity sha512-t7j+NzmgnQzTAYXcsHYLgimltOV1MXHtlOWf6GjL9Kj8GK5FInw5JotxvbOs+IvV1/Dzo04/fCGfLVs7aXb4Ag==
-
-lodash.uniq@4.5.0, lodash.uniq@^4.5.0:
- version "4.5.0"
- resolved "https://registry.yarnpkg.com/lodash.uniq/-/lodash.uniq-4.5.0.tgz#d0225373aeb652adc1bc82e4945339a842754773"
- integrity sha512-xfBaXQd9ryd9dlSDvnvI0lvxfLJlYAZzXomUYzLKtUeOQvOP5piqAWuGtrhWeqaXK9hhoM/iyJc5AV+XfsX3HQ==
-
-lodash@^4.17.19, lodash@^4.17.20, lodash@^4.17.21:
- version "4.17.21"
- resolved "https://registry.yarnpkg.com/lodash/-/lodash-4.17.21.tgz#679591c564c3bffaae8454cf0b3df370c3d6911c"
- integrity sha512-v2kDEe57lecTulaDIuNTPy3Ry4gLGJ6Z1O3vE1krgXZNrsQ+LFTGHVxVjcXPs17LhbZVGedAJv8XZ1tvj5FvSg==
-
-longest-streak@^3.0.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/longest-streak/-/longest-streak-3.1.0.tgz#62fa67cd958742a1574af9f39866364102d90cd4"
- integrity sha512-9Ri+o0JYgehTaVBBDoMqIl8GXtbWg711O3srftcHhZ0dqnETqLaoIK0x17fUw9rFSlK/0NlsKe0Ahhyl5pXE2g==
-
-loose-envify@^1.0.0, loose-envify@^1.1.0, loose-envify@^1.2.0, loose-envify@^1.3.1, loose-envify@^1.4.0:
- version "1.4.0"
- resolved "https://registry.yarnpkg.com/loose-envify/-/loose-envify-1.4.0.tgz#71ee51fa7be4caec1a63839f7e682d8132d30caf"
- integrity sha512-lyuxPGr/Wfhrlem2CL/UcnUc1zcqKAImBDzukY7Y5F/yQiNdko6+fRLevlw1HgMySw7f611UIY408EtxRSoK3Q==
- dependencies:
- js-tokens "^3.0.0 || ^4.0.0"
-
-lower-case@^2.0.2:
- version "2.0.2"
- resolved "https://registry.yarnpkg.com/lower-case/-/lower-case-2.0.2.tgz#6fa237c63dbdc4a82ca0fd882e4722dc5e634e28"
- integrity sha512-7fm3l3NAF9WfN6W3JOmf5drwpVqX78JtoGJ3A6W0a6ZnldM41w2fV5D490psKFTpMds8TJse/eHLFFsNHHjHgg==
- dependencies:
- tslib "^2.0.3"
-
-lowercase-keys@^1.0.0, lowercase-keys@^1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/lowercase-keys/-/lowercase-keys-1.0.1.tgz#6f9e30b47084d971a7c820ff15a6c5167b74c26f"
- integrity sha512-G2Lj61tXDnVFFOi8VZds+SoQjtQC3dgokKdDG2mTm1tx4m50NUHBOZSBwQQHyy0V12A0JTG4icfZQH+xPyh8VA==
-
-lowercase-keys@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/lowercase-keys/-/lowercase-keys-2.0.0.tgz#2603e78b7b4b0006cbca2fbcc8a3202558ac9479"
- integrity sha512-tqNXrS78oMOE73NMxK4EMLQsQowWf8jKooH9g7xPavRT706R6bkQJ6DY2Te7QukaZsulxa30wQ7bk0pm4XiHmA==
-
-lru-cache@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/lru-cache/-/lru-cache-5.1.1.tgz#1da27e6710271947695daf6848e847f01d84b920"
- integrity sha512-KpNARQA3Iwv+jTA0utUVVbrh+Jlrr1Fv0e56GGzAFOXN7dk/FviaDW8LHmK52DlcH4WP2n6gI8vN1aesBFgo9w==
- dependencies:
- yallist "^3.0.2"
-
-lru-cache@^6.0.0:
- version "6.0.0"
- resolved "https://registry.yarnpkg.com/lru-cache/-/lru-cache-6.0.0.tgz#6d6fe6570ebd96aaf90fcad1dafa3b2566db3a94"
- integrity sha512-Jo6dJ04CmSjuznwJSS3pUeWmd/H0ffTlkXXgwZi+eq1UCmqQwCh+eLsYOYCwY991i2Fah4h1BEMCx4qThGbsiA==
- dependencies:
- yallist "^4.0.0"
-
-make-dir@^3.0.0, make-dir@^3.0.2, make-dir@^3.1.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/make-dir/-/make-dir-3.1.0.tgz#415e967046b3a7f1d185277d84aa58203726a13f"
- integrity sha512-g3FeP20LNwhALb/6Cz6Dd4F2ngze0jz7tbzrD2wAV+o9FeNHe4rL+yK2md0J/fiSf1sa1ADhXqi5+oVwOM/eGw==
- dependencies:
- semver "^6.0.0"
-
-markdown-escapes@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/markdown-escapes/-/markdown-escapes-1.0.4.tgz#c95415ef451499d7602b91095f3c8e8975f78535"
- integrity sha512-8z4efJYk43E0upd0NbVXwgSTQs6cT3T06etieCMEg7dRbzCbxUCK/GHlX8mhHRDcp+OLlHkPKsvqQTCvsRl2cg==
-
-markdown-it@12.3.2:
- version "12.3.2"
- resolved "https://registry.yarnpkg.com/markdown-it/-/markdown-it-12.3.2.tgz#bf92ac92283fe983fe4de8ff8abfb5ad72cd0c90"
- integrity sha512-TchMembfxfNVpHkbtriWltGWc+m3xszaRD0CZup7GFFhzIgQqxIfn3eGj1yZpfuflzPvfkt611B2Q/Bsk1YnGg==
- dependencies:
- argparse "^2.0.1"
- entities "~2.1.0"
- linkify-it "^3.0.1"
- mdurl "^1.0.1"
- uc.micro "^1.0.5"
-
-markdownlint-cli@^0.31.1:
- version "0.31.1"
- resolved "https://registry.yarnpkg.com/markdownlint-cli/-/markdownlint-cli-0.31.1.tgz#8db34eec453e84bed06a954c8a289333f7c2c1c7"
- integrity sha512-keIOMwQn+Ch7MoBwA+TdkyVMuxAeZFEGmIIlvwgV0Z1TGS5MxPnRr29XCLhkNzCHU+uNKGjU+VEjLX+Z9kli6g==
- dependencies:
- commander "~9.0.0"
- get-stdin "~9.0.0"
- glob "~7.2.0"
- ignore "~5.2.0"
- js-yaml "^4.1.0"
- jsonc-parser "~3.0.0"
- markdownlint "~0.25.1"
- markdownlint-rule-helpers "~0.16.0"
- minimatch "~3.0.5"
- run-con "~1.2.10"
-
-markdownlint-rule-helpers@~0.16.0:
- version "0.16.0"
- resolved "https://registry.yarnpkg.com/markdownlint-rule-helpers/-/markdownlint-rule-helpers-0.16.0.tgz#c327f72782bd2b9475127a240508231f0413a25e"
- integrity sha512-oEacRUVeTJ5D5hW1UYd2qExYI0oELdYK72k1TKGvIeYJIbqQWAz476NAc7LNixSySUhcNl++d02DvX0ccDk9/w==
-
-markdownlint@~0.25.1:
- version "0.25.1"
- resolved "https://registry.yarnpkg.com/markdownlint/-/markdownlint-0.25.1.tgz#df04536607ebeeda5ccd5e4f38138823ed623788"
- integrity sha512-AG7UkLzNa1fxiOv5B+owPsPhtM4D6DoODhsJgiaNg1xowXovrYgOnLqAgOOFQpWOlHFVQUzjMY5ypNNTeov92g==
- dependencies:
- markdown-it "12.3.2"
-
-mdast-comment-marker@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/mdast-comment-marker/-/mdast-comment-marker-2.1.1.tgz#1c8540dc25d38c384c506068f97ca3447d1db92a"
- integrity sha512-ktFfySmbRfOPiWoLkRKqkkyYkDnBVX5b5FqXwnvV1TmgVOl49ETsYK4hPKqrlM15y7AtxNDKIKwJRkZa3TWkng==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-mdx-expression "^1.1.0"
-
-mdast-squeeze-paragraphs@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/mdast-squeeze-paragraphs/-/mdast-squeeze-paragraphs-4.0.0.tgz#7c4c114679c3bee27ef10b58e2e015be79f1ef97"
- integrity sha512-zxdPn69hkQ1rm4J+2Cs2j6wDEv7O17TfXTJ33tl/+JPIoEmtV9t2ZzBM5LPHE8QlHsmVD8t3vPKCyY3oH+H8MQ==
- dependencies:
- unist-util-remove "^2.0.0"
-
-mdast-util-definitions@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/mdast-util-definitions/-/mdast-util-definitions-4.0.0.tgz#c5c1a84db799173b4dcf7643cda999e440c24db2"
- integrity sha512-k8AJ6aNnUkB7IE+5azR9h81O5EQ/cTDXtWdMq9Kk5KcEW/8ritU5CeLg/9HhOC++nALHBlaogJ5jz0Ybk3kPMQ==
- dependencies:
- unist-util-visit "^2.0.0"
-
-mdast-util-from-markdown@^1.0.0, mdast-util-from-markdown@^1.1.0:
- version "1.3.0"
- resolved "https://registry.yarnpkg.com/mdast-util-from-markdown/-/mdast-util-from-markdown-1.3.0.tgz#0214124154f26154a2b3f9d401155509be45e894"
- integrity sha512-HN3W1gRIuN/ZW295c7zi7g9lVBllMgZE40RxCX37wrTPWXCWtpvOZdfnuK+1WNpvZje6XuJeI3Wnb4TJEUem+g==
- dependencies:
- "@types/mdast" "^3.0.0"
- "@types/unist" "^2.0.0"
- decode-named-character-reference "^1.0.0"
- mdast-util-to-string "^3.1.0"
- micromark "^3.0.0"
- micromark-util-decode-numeric-character-reference "^1.0.0"
- micromark-util-decode-string "^1.0.0"
- micromark-util-normalize-identifier "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- unist-util-stringify-position "^3.0.0"
- uvu "^0.5.0"
-
-mdast-util-heading-style@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/mdast-util-heading-style/-/mdast-util-heading-style-2.0.1.tgz#078cb0120a06af777c60413f7ba10f6d071b4672"
- integrity sha512-0L5rthU4xKDVbw+UQ7D8Y8xOEsX4JXZvemWoEAsL+WAaeSH+TvVVwFnTb3G/OrjyP4VYQULoNWU+PdZfkmNu4A==
- dependencies:
- "@types/mdast" "^3.0.0"
-
-mdast-util-mdx-expression@^1.0.0, mdast-util-mdx-expression@^1.1.0:
- version "1.3.2"
- resolved "https://registry.yarnpkg.com/mdast-util-mdx-expression/-/mdast-util-mdx-expression-1.3.2.tgz#d027789e67524d541d6de543f36d51ae2586f220"
- integrity sha512-xIPmR5ReJDu/DHH1OoIT1HkuybIfRGYRywC+gJtI7qHjCJp/M9jrmBEJW22O8lskDWm562BX2W8TiAwRTb0rKA==
- dependencies:
- "@types/estree-jsx" "^1.0.0"
- "@types/hast" "^2.0.0"
- "@types/mdast" "^3.0.0"
- mdast-util-from-markdown "^1.0.0"
- mdast-util-to-markdown "^1.0.0"
-
-mdast-util-mdx-jsx@^2.0.0:
- version "2.1.2"
- resolved "https://registry.yarnpkg.com/mdast-util-mdx-jsx/-/mdast-util-mdx-jsx-2.1.2.tgz#694a46164db10c0e9d674a3772b8748dfddd0817"
- integrity sha512-o9vBCYQK5ZLGEj3tCGISJGjvafyHRVJlZmfJzSE7xjiogSzIeph/Z4zMY65q4WGRMezQBeAwPlrdymDYYYx0tA==
- dependencies:
- "@types/estree-jsx" "^1.0.0"
- "@types/hast" "^2.0.0"
- "@types/mdast" "^3.0.0"
- "@types/unist" "^2.0.0"
- ccount "^2.0.0"
- mdast-util-from-markdown "^1.1.0"
- mdast-util-to-markdown "^1.3.0"
- parse-entities "^4.0.0"
- stringify-entities "^4.0.0"
- unist-util-remove-position "^4.0.0"
- unist-util-stringify-position "^3.0.0"
- vfile-message "^3.0.0"
-
-mdast-util-mdx@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/mdast-util-mdx/-/mdast-util-mdx-2.0.1.tgz#49b6e70819b99bb615d7223c088d295e53bb810f"
- integrity sha512-38w5y+r8nyKlGvNjSEqWrhG0w5PmnRA+wnBvm+ulYCct7nsGYhFVb0lljS9bQav4psDAS1eGkP2LMVcZBi/aqw==
- dependencies:
- mdast-util-from-markdown "^1.0.0"
- mdast-util-mdx-expression "^1.0.0"
- mdast-util-mdx-jsx "^2.0.0"
- mdast-util-mdxjs-esm "^1.0.0"
- mdast-util-to-markdown "^1.0.0"
-
-mdast-util-mdxjs-esm@^1.0.0:
- version "1.3.1"
- resolved "https://registry.yarnpkg.com/mdast-util-mdxjs-esm/-/mdast-util-mdxjs-esm-1.3.1.tgz#645d02cd607a227b49721d146fd81796b2e2d15b"
- integrity sha512-SXqglS0HrEvSdUEfoXFtcg7DRl7S2cwOXc7jkuusG472Mmjag34DUDeOJUZtl+BVnyeO1frIgVpHlNRWc2gk/w==
- dependencies:
- "@types/estree-jsx" "^1.0.0"
- "@types/hast" "^2.0.0"
- "@types/mdast" "^3.0.0"
- mdast-util-from-markdown "^1.0.0"
- mdast-util-to-markdown "^1.0.0"
-
-mdast-util-phrasing@^3.0.0:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/mdast-util-phrasing/-/mdast-util-phrasing-3.0.1.tgz#c7c21d0d435d7fb90956038f02e8702781f95463"
- integrity sha512-WmI1gTXUBJo4/ZmSk79Wcb2HcjPJBzM1nlI/OUWA8yk2X9ik3ffNbBGsU+09BFmXaL1IBb9fiuvq6/KMiNycSg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unist-util-is "^5.0.0"
-
-mdast-util-to-hast@10.0.1:
- version "10.0.1"
- resolved "https://registry.yarnpkg.com/mdast-util-to-hast/-/mdast-util-to-hast-10.0.1.tgz#0cfc82089494c52d46eb0e3edb7a4eb2aea021eb"
- integrity sha512-BW3LM9SEMnjf4HXXVApZMt8gLQWVNXc3jryK0nJu/rOXPOnlkUjmdkDlmxMirpbU9ILncGFIwLH/ubnWBbcdgA==
- dependencies:
- "@types/mdast" "^3.0.0"
- "@types/unist" "^2.0.0"
- mdast-util-definitions "^4.0.0"
- mdurl "^1.0.0"
- unist-builder "^2.0.0"
- unist-util-generated "^1.0.0"
- unist-util-position "^3.0.0"
- unist-util-visit "^2.0.0"
-
-mdast-util-to-markdown@^1.0.0, mdast-util-to-markdown@^1.3.0:
- version "1.5.0"
- resolved "https://registry.yarnpkg.com/mdast-util-to-markdown/-/mdast-util-to-markdown-1.5.0.tgz#c13343cb3fc98621911d33b5cd42e7d0731171c6"
- integrity sha512-bbv7TPv/WC49thZPg3jXuqzuvI45IL2EVAr/KxF0BSdHsU0ceFHOmwQn6evxAh1GaoK/6GQ1wp4R4oW2+LFL/A==
- dependencies:
- "@types/mdast" "^3.0.0"
- "@types/unist" "^2.0.0"
- longest-streak "^3.0.0"
- mdast-util-phrasing "^3.0.0"
- mdast-util-to-string "^3.0.0"
- micromark-util-decode-string "^1.0.0"
- unist-util-visit "^4.0.0"
- zwitch "^2.0.0"
-
-mdast-util-to-string@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/mdast-util-to-string/-/mdast-util-to-string-2.0.0.tgz#b8cfe6a713e1091cb5b728fc48885a4767f8b97b"
- integrity sha512-AW4DRS3QbBayY/jJmD8437V1Gombjf8RSOUCMFBuo5iHi58AGEgVCKQ+ezHkZZDpAQS75hcBMpLqjpJTjtUL7w==
-
-mdast-util-to-string@^3.0.0, mdast-util-to-string@^3.1.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/mdast-util-to-string/-/mdast-util-to-string-3.1.1.tgz#db859050d79d48cf9896d294de06f3ede7474d16"
- integrity sha512-tGvhT94e+cVnQt8JWE9/b3cUQZWS732TJxXHktvP+BYo62PpYD53Ls/6cC60rW21dW+txxiM4zMdc6abASvZKA==
- dependencies:
- "@types/mdast" "^3.0.0"
-
-mdn-data@2.0.14:
- version "2.0.14"
- resolved "https://registry.yarnpkg.com/mdn-data/-/mdn-data-2.0.14.tgz#7113fc4281917d63ce29b43446f701e68c25ba50"
- integrity sha512-dn6wd0uw5GsdswPFfsgMp5NSB0/aDe6fK94YJV/AJDYXL6HVLWBsxeq7js7Ad+mU2K9LAlwpk6kN2D5mwCPVow==
-
-mdurl@^1.0.0, mdurl@^1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/mdurl/-/mdurl-1.0.1.tgz#fe85b2ec75a59037f2adfec100fd6c601761152e"
- integrity sha512-/sKlQJCBYVY9Ers9hqzKou4H6V5UWc/M59TH2dvkt+84itfnq7uFOMLpOiOS4ujvHP4etln18fmIxA5R5fll0g==
-
-media-typer@0.3.0:
- version "0.3.0"
- resolved "https://registry.yarnpkg.com/media-typer/-/media-typer-0.3.0.tgz#8710d7af0aa626f8fffa1ce00168545263255748"
- integrity sha512-dq+qelQ9akHpcOl/gUVRTxVIOkAJ1wR3QAvb4RsVjS8oVoFjDGTc679wJYmUmknUF5HwMLOgb5O+a3KxfWapPQ==
-
-memfs@^3.1.2, memfs@^3.4.3:
- version "3.4.13"
- resolved "https://registry.yarnpkg.com/memfs/-/memfs-3.4.13.tgz#248a8bd239b3c240175cd5ec548de5227fc4f345"
- integrity sha512-omTM41g3Skpvx5dSYeZIbXKcXoAVc/AoMNwn9TKx++L/gaen/+4TTttmu8ZSch5vfVJ8uJvGbroTsIlslRg6lg==
- dependencies:
- fs-monkey "^1.0.3"
-
-merge-descriptors@1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/merge-descriptors/-/merge-descriptors-1.0.1.tgz#b00aaa556dd8b44568150ec9d1b953f3f90cbb61"
- integrity sha512-cCi6g3/Zr1iqQi6ySbseM1Xvooa98N0w31jzUYrXPX2xqObmFGHJ0tQ5u74H3mVh7wLouTseZyYIq39g8cNp1w==
-
-merge-stream@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/merge-stream/-/merge-stream-2.0.0.tgz#52823629a14dd00c9770fb6ad47dc6310f2c1f60"
- integrity sha512-abv/qOcuPfk3URPfDzmZU1LKmuw8kT+0nIHvKrKgFrwifol/doWcdA4ZqsWQ8ENrFKkd67Mfpo/LovbIUsbt3w==
-
-merge2@^1.3.0, merge2@^1.4.1:
- version "1.4.1"
- resolved "https://registry.yarnpkg.com/merge2/-/merge2-1.4.1.tgz#4368892f885e907455a6fd7dc55c0c9d404990ae"
- integrity sha512-8q7VEgMJW4J8tcfVPy8g09NcQwZdbwFEqhe/WZkoIzjn/3TGDwtOCYtXGxA3O8tPzpczCCDgv+P2P5y00ZJOOg==
-
-methods@~1.1.2:
- version "1.1.2"
- resolved "https://registry.yarnpkg.com/methods/-/methods-1.1.2.tgz#5529a4d67654134edcc5266656835b0f851afcee"
- integrity sha512-iclAHeNqNm68zFtnZ0e+1L2yUIdvzNoauKU4WBA3VvH/vPFieF7qfRlwUZU+DA9P9bPXIS90ulxoUoCH23sV2w==
-
-micromark-core-commonmark@^1.0.0, micromark-core-commonmark@^1.0.1:
- version "1.0.6"
- resolved "https://registry.yarnpkg.com/micromark-core-commonmark/-/micromark-core-commonmark-1.0.6.tgz#edff4c72e5993d93724a3c206970f5a15b0585ad"
- integrity sha512-K+PkJTxqjFfSNkfAhp4GB+cZPfQd6dxtTXnf+RjZOV7T4EEXnvgzOcnp+eSTmpGk9d1S9sL6/lqrgSNn/s0HZA==
- dependencies:
- decode-named-character-reference "^1.0.0"
- micromark-factory-destination "^1.0.0"
- micromark-factory-label "^1.0.0"
- micromark-factory-space "^1.0.0"
- micromark-factory-title "^1.0.0"
- micromark-factory-whitespace "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-chunked "^1.0.0"
- micromark-util-classify-character "^1.0.0"
- micromark-util-html-tag-name "^1.0.0"
- micromark-util-normalize-identifier "^1.0.0"
- micromark-util-resolve-all "^1.0.0"
- micromark-util-subtokenize "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.1"
- uvu "^0.5.0"
-
-micromark-extension-mdx-expression@^1.0.0:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/micromark-extension-mdx-expression/-/micromark-extension-mdx-expression-1.0.4.tgz#33fe2c6ee214738255de175a084281c11894ddda"
- integrity sha512-TCgLxqW6ReQ3AJgtj1P0P+8ZThBTloLbeb7jNaqr6mCOLDpxUiBFE/9STgooMZttEwOQu5iEcCCa3ZSDhY9FGw==
- dependencies:
- micromark-factory-mdx-expression "^1.0.0"
- micromark-factory-space "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-events-to-acorn "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- uvu "^0.5.0"
-
-micromark-extension-mdx-jsx@^1.0.0:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/micromark-extension-mdx-jsx/-/micromark-extension-mdx-jsx-1.0.3.tgz#9f196be5f65eb09d2a49b237a7b3398bba2999be"
- integrity sha512-VfA369RdqUISF0qGgv2FfV7gGjHDfn9+Qfiv5hEwpyr1xscRj/CiVRkU7rywGFCO7JwJ5L0e7CJz60lY52+qOA==
- dependencies:
- "@types/acorn" "^4.0.0"
- estree-util-is-identifier-name "^2.0.0"
- micromark-factory-mdx-expression "^1.0.0"
- micromark-factory-space "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- uvu "^0.5.0"
- vfile-message "^3.0.0"
-
-micromark-extension-mdx-md@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-extension-mdx-md/-/micromark-extension-mdx-md-1.0.0.tgz#382f5df9ee3706dd120b51782a211f31f4760d22"
- integrity sha512-xaRAMoSkKdqZXDAoSgp20Azm0aRQKGOl0RrS81yGu8Hr/JhMsBmfs4wR7m9kgVUIO36cMUQjNyiyDKPrsv8gOw==
- dependencies:
- micromark-util-types "^1.0.0"
-
-micromark-extension-mdxjs-esm@^1.0.0:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/micromark-extension-mdxjs-esm/-/micromark-extension-mdxjs-esm-1.0.3.tgz#630d9dc9db2c2fd470cac8c1e7a824851267404d"
- integrity sha512-2N13ol4KMoxb85rdDwTAC6uzs8lMX0zeqpcyx7FhS7PxXomOnLactu8WI8iBNXW8AVyea3KIJd/1CKnUmwrK9A==
- dependencies:
- micromark-core-commonmark "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-events-to-acorn "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- unist-util-position-from-estree "^1.1.0"
- uvu "^0.5.0"
- vfile-message "^3.0.0"
-
-micromark-extension-mdxjs@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-extension-mdxjs/-/micromark-extension-mdxjs-1.0.0.tgz#772644e12fc8299a33e50f59c5aa15727f6689dd"
- integrity sha512-TZZRZgeHvtgm+IhtgC2+uDMR7h8eTKF0QUX9YsgoL9+bADBpBY6SiLvWqnBlLbCEevITmTqmEuY3FoxMKVs1rQ==
- dependencies:
- acorn "^8.0.0"
- acorn-jsx "^5.0.0"
- micromark-extension-mdx-expression "^1.0.0"
- micromark-extension-mdx-jsx "^1.0.0"
- micromark-extension-mdx-md "^1.0.0"
- micromark-extension-mdxjs-esm "^1.0.0"
- micromark-util-combine-extensions "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-factory-destination@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-factory-destination/-/micromark-factory-destination-1.0.0.tgz#fef1cb59ad4997c496f887b6977aa3034a5a277e"
- integrity sha512-eUBA7Rs1/xtTVun9TmV3gjfPz2wEwgK5R5xcbIM5ZYAtvGF6JkyaDsj0agx8urXnO31tEO6Ug83iVH3tdedLnw==
- dependencies:
- micromark-util-character "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-factory-label@^1.0.0:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/micromark-factory-label/-/micromark-factory-label-1.0.2.tgz#6be2551fa8d13542fcbbac478258fb7a20047137"
- integrity sha512-CTIwxlOnU7dEshXDQ+dsr2n+yxpP0+fn271pu0bwDIS8uqfFcumXpj5mLn3hSC8iw2MUr6Gx8EcKng1dD7i6hg==
- dependencies:
- micromark-util-character "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- uvu "^0.5.0"
-
-micromark-factory-mdx-expression@^1.0.0:
- version "1.0.7"
- resolved "https://registry.yarnpkg.com/micromark-factory-mdx-expression/-/micromark-factory-mdx-expression-1.0.7.tgz#e38298dc1f7eaf6ba1d9f210531ceae17155c00f"
- integrity sha512-QAdFbkQagTZ/eKb8zDGqmjvgevgJH3+aQpvvKrXWxNJp3o8/l2cAbbrBd0E04r0Gx6nssPpqWIjnbHFvZu5qsQ==
- dependencies:
- micromark-factory-space "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-events-to-acorn "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- unist-util-position-from-estree "^1.0.0"
- uvu "^0.5.0"
- vfile-message "^3.0.0"
-
-micromark-factory-space@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-factory-space/-/micromark-factory-space-1.0.0.tgz#cebff49968f2b9616c0fcb239e96685cb9497633"
- integrity sha512-qUmqs4kj9a5yBnk3JMLyjtWYN6Mzfcx8uJfi5XAveBniDevmZasdGBba5b4QsvRcAkmvGo5ACmSUmyGiKTLZew==
- dependencies:
- micromark-util-character "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-factory-title@^1.0.0:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/micromark-factory-title/-/micromark-factory-title-1.0.2.tgz#7e09287c3748ff1693930f176e1c4a328382494f"
- integrity sha512-zily+Nr4yFqgMGRKLpTVsNl5L4PMu485fGFDOQJQBl2NFpjGte1e86zC0da93wf97jrc4+2G2GQudFMHn3IX+A==
- dependencies:
- micromark-factory-space "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- uvu "^0.5.0"
-
-micromark-factory-whitespace@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-factory-whitespace/-/micromark-factory-whitespace-1.0.0.tgz#e991e043ad376c1ba52f4e49858ce0794678621c"
- integrity sha512-Qx7uEyahU1lt1RnsECBiuEbfr9INjQTGa6Err+gF3g0Tx4YEviPbqqGKNv/NrBaE7dVHdn1bVZKM/n5I/Bak7A==
- dependencies:
- micromark-factory-space "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-util-character@^1.0.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/micromark-util-character/-/micromark-util-character-1.1.0.tgz#d97c54d5742a0d9611a68ca0cd4124331f264d86"
- integrity sha512-agJ5B3unGNJ9rJvADMJ5ZiYjBRyDpzKAOk01Kpi1TKhlT1APx3XZk6eN7RtSz1erbWHC2L8T3xLZ81wdtGRZzg==
- dependencies:
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-util-chunked@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-util-chunked/-/micromark-util-chunked-1.0.0.tgz#5b40d83f3d53b84c4c6bce30ed4257e9a4c79d06"
- integrity sha512-5e8xTis5tEZKgesfbQMKRCyzvffRRUX+lK/y+DvsMFdabAicPkkZV6gO+FEWi9RfuKKoxxPwNL+dFF0SMImc1g==
- dependencies:
- micromark-util-symbol "^1.0.0"
-
-micromark-util-classify-character@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-util-classify-character/-/micromark-util-classify-character-1.0.0.tgz#cbd7b447cb79ee6997dd274a46fc4eb806460a20"
- integrity sha512-F8oW2KKrQRb3vS5ud5HIqBVkCqQi224Nm55o5wYLzY/9PwHGXC01tr3d7+TqHHz6zrKQ72Okwtvm/xQm6OVNZA==
- dependencies:
- micromark-util-character "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-util-combine-extensions@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-util-combine-extensions/-/micromark-util-combine-extensions-1.0.0.tgz#91418e1e74fb893e3628b8d496085639124ff3d5"
- integrity sha512-J8H058vFBdo/6+AsjHp2NF7AJ02SZtWaVUjsayNFeAiydTxUwViQPxN0Hf8dp4FmCQi0UUFovFsEyRSUmFH3MA==
- dependencies:
- micromark-util-chunked "^1.0.0"
- micromark-util-types "^1.0.0"
-
-micromark-util-decode-numeric-character-reference@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-util-decode-numeric-character-reference/-/micromark-util-decode-numeric-character-reference-1.0.0.tgz#dcc85f13b5bd93ff8d2868c3dba28039d490b946"
- integrity sha512-OzO9AI5VUtrTD7KSdagf4MWgHMtET17Ua1fIpXTpuhclCqD8egFWo85GxSGvxgkGS74bEahvtM0WP0HjvV0e4w==
- dependencies:
- micromark-util-symbol "^1.0.0"
-
-micromark-util-decode-string@^1.0.0:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/micromark-util-decode-string/-/micromark-util-decode-string-1.0.2.tgz#942252ab7a76dec2dbf089cc32505ee2bc3acf02"
- integrity sha512-DLT5Ho02qr6QWVNYbRZ3RYOSSWWFuH3tJexd3dgN1odEuPNxCngTCXJum7+ViRAd9BbdxCvMToPOD/IvVhzG6Q==
- dependencies:
- decode-named-character-reference "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-decode-numeric-character-reference "^1.0.0"
- micromark-util-symbol "^1.0.0"
-
-micromark-util-encode@^1.0.0:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/micromark-util-encode/-/micromark-util-encode-1.0.1.tgz#2c1c22d3800870ad770ece5686ebca5920353383"
- integrity sha512-U2s5YdnAYexjKDel31SVMPbfi+eF8y1U4pfiRW/Y8EFVCy/vgxk/2wWTxzcqE71LHtCuCzlBDRU2a5CQ5j+mQA==
-
-micromark-util-events-to-acorn@^1.0.0:
- version "1.2.1"
- resolved "https://registry.yarnpkg.com/micromark-util-events-to-acorn/-/micromark-util-events-to-acorn-1.2.1.tgz#d5b9dfbc589ece7917de24de0a57b909c0d36583"
- integrity sha512-mkg3BaWlw6ZTkQORrKVBW4o9ICXPxLtGz51vml5mQpKFdo9vqIX68CAx5JhTOdjQyAHH7JFmm4rh8toSPQZUmg==
- dependencies:
- "@types/acorn" "^4.0.0"
- "@types/estree" "^1.0.0"
- estree-util-visit "^1.0.0"
- micromark-util-types "^1.0.0"
- uvu "^0.5.0"
- vfile-location "^4.0.0"
- vfile-message "^3.0.0"
-
-micromark-util-html-tag-name@^1.0.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/micromark-util-html-tag-name/-/micromark-util-html-tag-name-1.1.0.tgz#eb227118befd51f48858e879b7a419fc0df20497"
- integrity sha512-BKlClMmYROy9UiV03SwNmckkjn8QHVaWkqoAqzivabvdGcwNGMMMH/5szAnywmsTBUzDsU57/mFi0sp4BQO6dA==
-
-micromark-util-normalize-identifier@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-util-normalize-identifier/-/micromark-util-normalize-identifier-1.0.0.tgz#4a3539cb8db954bbec5203952bfe8cedadae7828"
- integrity sha512-yg+zrL14bBTFrQ7n35CmByWUTFsgst5JhA4gJYoty4Dqzj4Z4Fr/DHekSS5aLfH9bdlfnSvKAWsAgJhIbogyBg==
- dependencies:
- micromark-util-symbol "^1.0.0"
-
-micromark-util-resolve-all@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/micromark-util-resolve-all/-/micromark-util-resolve-all-1.0.0.tgz#a7c363f49a0162e931960c44f3127ab58f031d88"
- integrity sha512-CB/AGk98u50k42kvgaMM94wzBqozSzDDaonKU7P7jwQIuH2RU0TeBqGYJz2WY1UdihhjweivStrJ2JdkdEmcfw==
- dependencies:
- micromark-util-types "^1.0.0"
-
-micromark-util-sanitize-uri@^1.0.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/micromark-util-sanitize-uri/-/micromark-util-sanitize-uri-1.1.0.tgz#f12e07a85106b902645e0364feb07cf253a85aee"
- integrity sha512-RoxtuSCX6sUNtxhbmsEFQfWzs8VN7cTctmBPvYivo98xb/kDEoTCtJQX5wyzIYEmk/lvNFTat4hL8oW0KndFpg==
- dependencies:
- micromark-util-character "^1.0.0"
- micromark-util-encode "^1.0.0"
- micromark-util-symbol "^1.0.0"
-
-micromark-util-subtokenize@^1.0.0:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/micromark-util-subtokenize/-/micromark-util-subtokenize-1.0.2.tgz#ff6f1af6ac836f8bfdbf9b02f40431760ad89105"
- integrity sha512-d90uqCnXp/cy4G881Ub4psE57Sf8YD0pim9QdjCRNjfas2M1u6Lbt+XZK9gnHL2XFhnozZiEdCa9CNfXSfQ6xA==
- dependencies:
- micromark-util-chunked "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.0"
- uvu "^0.5.0"
-
-micromark-util-symbol@^1.0.0:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/micromark-util-symbol/-/micromark-util-symbol-1.0.1.tgz#b90344db62042ce454f351cf0bebcc0a6da4920e"
- integrity sha512-oKDEMK2u5qqAptasDAwWDXq0tG9AssVwAx3E9bBF3t/shRIGsWIRG+cGafs2p/SnDSOecnt6hZPCE2o6lHfFmQ==
-
-micromark-util-types@^1.0.0, micromark-util-types@^1.0.1:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/micromark-util-types/-/micromark-util-types-1.0.2.tgz#f4220fdb319205812f99c40f8c87a9be83eded20"
- integrity sha512-DCfg/T8fcrhrRKTPjRrw/5LLvdGV7BHySf/1LOZx7TzWZdYRjogNtyNq885z3nNallwr3QUKARjqvHqX1/7t+w==
-
-micromark@^3.0.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/micromark/-/micromark-3.1.0.tgz#eeba0fe0ac1c9aaef675157b52c166f125e89f62"
- integrity sha512-6Mj0yHLdUZjHnOPgr5xfWIMqMWS12zDN6iws9SLuSz76W8jTtAv24MN4/CL7gJrl5vtxGInkkqDv/JIoRsQOvA==
- dependencies:
- "@types/debug" "^4.0.0"
- debug "^4.0.0"
- decode-named-character-reference "^1.0.0"
- micromark-core-commonmark "^1.0.1"
- micromark-factory-space "^1.0.0"
- micromark-util-character "^1.0.0"
- micromark-util-chunked "^1.0.0"
- micromark-util-combine-extensions "^1.0.0"
- micromark-util-decode-numeric-character-reference "^1.0.0"
- micromark-util-encode "^1.0.0"
- micromark-util-normalize-identifier "^1.0.0"
- micromark-util-resolve-all "^1.0.0"
- micromark-util-sanitize-uri "^1.0.0"
- micromark-util-subtokenize "^1.0.0"
- micromark-util-symbol "^1.0.0"
- micromark-util-types "^1.0.1"
- uvu "^0.5.0"
-
-micromatch@^4.0.2, micromatch@^4.0.4, micromatch@^4.0.5:
- version "4.0.5"
- resolved "https://registry.yarnpkg.com/micromatch/-/micromatch-4.0.5.tgz#bc8999a7cbbf77cdc89f132f6e467051b49090c6"
- integrity sha512-DMy+ERcEW2q8Z2Po+WNXuw3c5YaUSFjAO5GsJqfEl7UjvtIuFKO6ZrKvcItdy98dwFI2N1tg3zNIdKaQT+aNdA==
- dependencies:
- braces "^3.0.2"
- picomatch "^2.3.1"
-
-mime-db@1.52.0, "mime-db@>= 1.43.0 < 2":
- version "1.52.0"
- resolved "https://registry.yarnpkg.com/mime-db/-/mime-db-1.52.0.tgz#bbabcdc02859f4987301c856e3387ce5ec43bf70"
- integrity sha512-sPU4uV7dYlvtWJxwwxHD0PuihVNiE7TyAbQ5SWxDCB9mUYvOgroQOwYQQOKPJ8CIbE+1ETVlOoK1UC2nU3gYvg==
-
-mime-db@~1.33.0:
- version "1.33.0"
- resolved "https://registry.yarnpkg.com/mime-db/-/mime-db-1.33.0.tgz#a3492050a5cb9b63450541e39d9788d2272783db"
- integrity sha512-BHJ/EKruNIqJf/QahvxwQZXKygOQ256myeN/Ew+THcAa5q+PjyTTMMeNQC4DZw5AwfvelsUrA6B67NKMqXDbzQ==
-
-mime-types@2.1.18:
- version "2.1.18"
- resolved "https://registry.yarnpkg.com/mime-types/-/mime-types-2.1.18.tgz#6f323f60a83d11146f831ff11fd66e2fe5503bb8"
- integrity sha512-lc/aahn+t4/SWV/qcmumYjymLsWfN3ELhpmVuUFjgsORruuZPVSwAQryq+HHGvO/SI2KVX26bx+En+zhM8g8hQ==
- dependencies:
- mime-db "~1.33.0"
-
-mime-types@^2.1.27, mime-types@^2.1.31, mime-types@~2.1.17, mime-types@~2.1.24, mime-types@~2.1.34:
- version "2.1.35"
- resolved "https://registry.yarnpkg.com/mime-types/-/mime-types-2.1.35.tgz#381a871b62a734450660ae3deee44813f70d959a"
- integrity sha512-ZDY+bPm5zTTF+YpCrAU9nK0UgICYPT0QtT1NZWFv4s++TNkcgVaT0g6+4R2uI4MjQjzysHB1zxuWL50hzaeXiw==
- dependencies:
- mime-db "1.52.0"
-
-mime@1.6.0:
- version "1.6.0"
- resolved "https://registry.yarnpkg.com/mime/-/mime-1.6.0.tgz#32cd9e5c64553bd58d19a568af452acff04981b1"
- integrity sha512-x0Vn8spI+wuJ1O6S7gnbaQg8Pxh4NNHb7KSINmEWKiPE4RKOplvijn+NkmYmmRgP68mc70j2EbeTFRsrswaQeg==
-
-mimic-fn@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/mimic-fn/-/mimic-fn-2.1.0.tgz#7ed2c2ccccaf84d3ffcb7a69b57711fc2083401b"
- integrity sha512-OqbOk5oEQeAZ8WXWydlu9HJjz9WVdEIvamMCcXmuqUYjTknH/sqsWvhQ3vgwKFRR1HpjvNBKQ37nbJgYzGqGcg==
-
-mimic-response@^1.0.0, mimic-response@^1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/mimic-response/-/mimic-response-1.0.1.tgz#4923538878eef42063cb8a3e3b0798781487ab1b"
- integrity sha512-j5EctnkH7amfV/q5Hgmoal1g2QHFJRraOtmx0JpIqkxhBhI/lJSl1nMpQ45hVarwNETOoWEimndZ4QK0RHxuxQ==
-
-mini-css-extract-plugin@^2.6.1:
- version "2.7.2"
- resolved "https://registry.yarnpkg.com/mini-css-extract-plugin/-/mini-css-extract-plugin-2.7.2.tgz#e049d3ea7d3e4e773aad585c6cb329ce0c7b72d7"
- integrity sha512-EdlUizq13o0Pd+uCp+WO/JpkLvHRVGt97RqfeGhXqAcorYo1ypJSpkV+WDT0vY/kmh/p7wRdJNJtuyK540PXDw==
- dependencies:
- schema-utils "^4.0.0"
-
-minimalistic-assert@^1.0.0:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/minimalistic-assert/-/minimalistic-assert-1.0.1.tgz#2e194de044626d4a10e7f7fbc00ce73e83e4d5c7"
- integrity sha512-UtJcAD4yEaGtjPezWuO9wC4nwUnVH/8/Im3yEHQP4b67cXlD/Qr9hdITCU1xDbSEXg2XKNaP8jsReV7vQd00/A==
-
-minimatch@3.1.2, minimatch@^3.0.4, minimatch@^3.0.5, minimatch@^3.1.1:
- version "3.1.2"
- resolved "https://registry.yarnpkg.com/minimatch/-/minimatch-3.1.2.tgz#19cd194bfd3e428f049a70817c038d89ab4be35b"
- integrity sha512-J7p63hRiAjw1NDEww1W7i37+ByIrOWO5XQQAzZ3VOcL0PNybwpfmV/N05zFAzwQ9USyEcX6t3UO+K5aqBQOIHw==
- dependencies:
- brace-expansion "^1.1.7"
-
-minimatch@^5.0.1:
- version "5.1.6"
- resolved "https://registry.yarnpkg.com/minimatch/-/minimatch-5.1.6.tgz#1cfcb8cf5522ea69952cd2af95ae09477f122a96"
- integrity sha512-lKwV/1brpG6mBUFHtb7NUmtABCb2WZZmm2wNiOA5hAb8VdCS4B3dtMWyvcoViccwAW/COERjXLt0zP1zXUN26g==
- dependencies:
- brace-expansion "^2.0.1"
-
-minimatch@^6.1.6:
- version "6.2.0"
- resolved "https://registry.yarnpkg.com/minimatch/-/minimatch-6.2.0.tgz#2b70fd13294178c69c04dfc05aebdb97a4e79e42"
- integrity sha512-sauLxniAmvnhhRjFwPNnJKaPFYyddAgbYdeUpHULtCT/GhzdCx/MDNy+Y40lBxTQUrMzDE8e0S43Z5uqfO0REg==
- dependencies:
- brace-expansion "^2.0.1"
-
-minimatch@~3.0.5:
- version "3.0.8"
- resolved "https://registry.yarnpkg.com/minimatch/-/minimatch-3.0.8.tgz#5e6a59bd11e2ab0de1cfb843eb2d82e546c321c1"
- integrity sha512-6FsRAQsxQ61mw+qP1ZzbL9Bc78x2p5OqNgNpnoAFLTrX8n5Kxph0CsnhmKKNXTWjXqU5L0pGPR7hYk+XWZr60Q==
- dependencies:
- brace-expansion "^1.1.7"
-
-minimist@^1.0.0, minimist@^1.2.0, minimist@^1.2.5, minimist@^1.2.6:
- version "1.2.8"
- resolved "https://registry.yarnpkg.com/minimist/-/minimist-1.2.8.tgz#c1a464e7693302e082a075cee0c057741ac4772c"
- integrity sha512-2yyAR8qBkN3YuheJanUpWC5U3bb5osDywNB8RzDVlDwDHbocAJveqqj1u8+SVD7jkWT4yvsHCpWqqWqAxb0zCA==
-
-mri@^1.1.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/mri/-/mri-1.2.0.tgz#6721480fec2a11a4889861115a48b6cbe7cc8f0b"
- integrity sha512-tzzskb3bG8LvYGFF/mDTpq3jpI6Q9wc3LEmBaghu+DdCssd1FakN7Bc0hVNmEyGq1bq3RgfkCb3cmQLpNPOroA==
-
-mrmime@^1.0.0:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/mrmime/-/mrmime-1.0.1.tgz#5f90c825fad4bdd41dc914eff5d1a8cfdaf24f27"
- integrity sha512-hzzEagAgDyoU1Q6yg5uI+AorQgdvMCur3FcKf7NhMKWsaYg+RnbTyHRa/9IlLF9rf455MOCtcqqrQQ83pPP7Uw==
-
-ms@2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/ms/-/ms-2.0.0.tgz#5608aeadfc00be6c2901df5f9861788de0d597c8"
- integrity sha512-Tpp60P6IUJDTuOq/5Z8cdskzJujfwqfOTkrwIwj7IRISpnkJnT6SyJ4PCPnGMoFjC9ddhal5KVIYtAt97ix05A==
-
-ms@2.1.2:
- version "2.1.2"
- resolved "https://registry.yarnpkg.com/ms/-/ms-2.1.2.tgz#d09d1f357b443f493382a8eb3ccd183872ae6009"
- integrity sha512-sGkPx+VjMtmA6MX27oA4FBFELFCZZ4S4XqeGOXCv68tT+jb3vk/RyaKWP0PTKyWtmLSM0b+adUTEvbs1PEaH2w==
-
-ms@2.1.3:
- version "2.1.3"
- resolved "https://registry.yarnpkg.com/ms/-/ms-2.1.3.tgz#574c8138ce1d2b5861f0b44579dbadd60c6615b2"
- integrity sha512-6FlzubTLZG3J2a/NVCAleEhjzq5oxgHyaCU9yYXvcLsvoVaHJq/s5xXI6/XXP6tz7R9xAOtHnSO/tXtF3WRTlA==
-
-multicast-dns@^7.2.5:
- version "7.2.5"
- resolved "https://registry.yarnpkg.com/multicast-dns/-/multicast-dns-7.2.5.tgz#77eb46057f4d7adbd16d9290fa7299f6fa64cced"
- integrity sha512-2eznPJP8z2BFLX50tf0LuODrpINqP1RVIm/CObbTcBRITQgmC/TjcREF1NeTBzIcR5XO/ukWo+YHOjBbFwIupg==
- dependencies:
- dns-packet "^5.2.2"
- thunky "^1.0.2"
-
-nanoid@^3.3.4:
- version "3.3.4"
- resolved "https://registry.yarnpkg.com/nanoid/-/nanoid-3.3.4.tgz#730b67e3cd09e2deacf03c027c81c9d9dbc5e8ab"
- integrity sha512-MqBkQh/OHTS2egovRtLk45wEyNXwF+cokD+1YPf9u5VfJiRdAiRwB2froX5Co9Rh20xs4siNPm8naNotSD6RBw==
-
-negotiator@0.6.3:
- version "0.6.3"
- resolved "https://registry.yarnpkg.com/negotiator/-/negotiator-0.6.3.tgz#58e323a72fedc0d6f9cd4d31fe49f51479590ccd"
- integrity sha512-+EUsqGPLsM+j/zdChZjsnX51g4XrHFOIXwfnCVPGlQk/k5giakcKsuxCObBRu6DSm9opw/O6slWbJdghQM4bBg==
-
-neo-async@^2.6.2:
- version "2.6.2"
- resolved "https://registry.yarnpkg.com/neo-async/-/neo-async-2.6.2.tgz#b4aafb93e3aeb2d8174ca53cf163ab7d7308305f"
- integrity sha512-Yd3UES5mWCSqR+qNT93S3UoYUkqAZ9lLg8a7g9rimsWmYGK8cVToA4/sF3RrshdyV3sAGMXVUmpMYOw+dLpOuw==
-
-no-case@^3.0.4:
- version "3.0.4"
- resolved "https://registry.yarnpkg.com/no-case/-/no-case-3.0.4.tgz#d361fd5c9800f558551a8369fc0dcd4662b6124d"
- integrity sha512-fgAN3jGAh+RoxUGZHTSOLJIqUc2wmoBwGR4tbpNAKmmovFoWq0OdRkb0VkldReO2a2iBT/OEulG9XSUc10r3zg==
- dependencies:
- lower-case "^2.0.2"
- tslib "^2.0.3"
-
-node-emoji@^1.10.0:
- version "1.11.0"
- resolved "https://registry.yarnpkg.com/node-emoji/-/node-emoji-1.11.0.tgz#69a0150e6946e2f115e9d7ea4df7971e2628301c"
- integrity sha512-wo2DpQkQp7Sjm2A0cq+sN7EHKO6Sl0ctXeBdFZrL9T9+UywORbufTcTZxom8YqpLQt/FqNMUkOpkZrJVYSKD3A==
- dependencies:
- lodash "^4.17.21"
-
-node-fetch@2.6.7:
- version "2.6.7"
- resolved "https://registry.yarnpkg.com/node-fetch/-/node-fetch-2.6.7.tgz#24de9fba827e3b4ae44dc8b20256a379160052ad"
- integrity sha512-ZjMPFEfVx5j+y2yF35Kzx5sF7kDzxuDj6ziH4FFbOp87zKDZNx8yExJIb05OGF4Nlt9IHFIMBkRl41VdvcNdbQ==
- dependencies:
- whatwg-url "^5.0.0"
-
-node-forge@^1:
- version "1.3.1"
- resolved "https://registry.yarnpkg.com/node-forge/-/node-forge-1.3.1.tgz#be8da2af243b2417d5f646a770663a92b7e9ded3"
- integrity sha512-dPEtOeMvF9VMcYV/1Wb8CPoVAXtp6MKMlcbAt4ddqmGqUJ6fQZFXkNZNkNlfevtNkGtaSoXf/vNNNSvgrdXwtA==
-
-node-releases@^2.0.8:
- version "2.0.10"
- resolved "https://registry.yarnpkg.com/node-releases/-/node-releases-2.0.10.tgz#c311ebae3b6a148c89b1813fd7c4d3c024ef537f"
- integrity sha512-5GFldHPXVG/YZmFzJvKK2zDSzPKhEp0+ZR5SVaoSag9fsL5YgHbUHDfnG5494ISANDcK4KwPXAx2xqVEydmd7w==
-
-nopt@^7.0.0:
- version "7.0.0"
- resolved "https://registry.yarnpkg.com/nopt/-/nopt-7.0.0.tgz#09220f930c072109c98ef8aaf39e1d5f0ff9b0d4"
- integrity sha512-e6Qw1rcrGoSxEH0hQ4GBSdUjkMOtXGhGFXdNT/3ZR0S37eR9DMj5za3dEDWE6o1T3/DP8ZOsPP4MIiky0c3QeA==
- dependencies:
- abbrev "^2.0.0"
-
-normalize-path@^3.0.0, normalize-path@~3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/normalize-path/-/normalize-path-3.0.0.tgz#0dcd69ff23a1c9b11fd0978316644a0388216a65"
- integrity sha512-6eZs5Ls3WtCisHWp9S2GUy8dqkpGi4BVSz3GaqiE6ezub0512ESztXUwUB6C6IKbQkY2Pnb/mD4WYojCRwcwLA==
-
-normalize-range@^0.1.2:
- version "0.1.2"
- resolved "https://registry.yarnpkg.com/normalize-range/-/normalize-range-0.1.2.tgz#2d10c06bdfd312ea9777695a4d28439456b75942"
- integrity sha512-bdok/XvKII3nUpklnV6P2hxtMNrCboOjAcyBuQnWEhO665FwrSNRxU+AqpsyvO6LgGYPspN+lu5CLtw4jPRKNA==
-
-normalize-url@^4.1.0:
- version "4.5.1"
- resolved "https://registry.yarnpkg.com/normalize-url/-/normalize-url-4.5.1.tgz#0dd90cf1288ee1d1313b87081c9a5932ee48518a"
- integrity sha512-9UZCFRHQdNrfTpGg8+1INIg93B6zE0aXMVFkw1WFwvO4SlZywU6aLg5Of0Ap/PgcbSw4LNxvMWXMeugwMCX0AA==
-
-normalize-url@^6.0.1:
- version "6.1.0"
- resolved "https://registry.yarnpkg.com/normalize-url/-/normalize-url-6.1.0.tgz#40d0885b535deffe3f3147bec877d05fe4c5668a"
- integrity sha512-DlL+XwOy3NxAQ8xuC0okPgK46iuVNAK01YN7RueYBqqFeGsBjV9XmCAzAdgt+667bCl5kPh9EqKKDwnaPG1I7A==
-
-npm-normalize-package-bin@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/npm-normalize-package-bin/-/npm-normalize-package-bin-3.0.0.tgz#6097436adb4ef09e2628b59a7882576fe53ce485"
- integrity sha512-g+DPQSkusnk7HYXr75NtzkIP4+N81i3RPsGFidF3DzHd9MT9wWngmqoeg/fnHFz5MNdtG4w03s+QnhewSLTT2Q==
-
-npm-run-path@^4.0.1:
- version "4.0.1"
- resolved "https://registry.yarnpkg.com/npm-run-path/-/npm-run-path-4.0.1.tgz#b7ecd1e5ed53da8e37a55e1c2269e0b97ed748ea"
- integrity sha512-S48WzZW777zhNIrn7gxOlISNAqi9ZC/uQFnRdbeIHhZhCA6UqpkOT8T1G7BvfdgP4Er8gF4sUbaS0i7QvIfCWw==
- dependencies:
- path-key "^3.0.0"
-
-nprogress@^0.2.0:
- version "0.2.0"
- resolved "https://registry.yarnpkg.com/nprogress/-/nprogress-0.2.0.tgz#cb8f34c53213d895723fcbab907e9422adbcafb1"
- integrity sha512-I19aIingLgR1fmhftnbWWO3dXc0hSxqHQHQb3H8m+K3TnEn/iSeTZZOyvKXWqQESMwuUVnatlCnZdLBZZt2VSA==
-
-nth-check@^2.0.1:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/nth-check/-/nth-check-2.1.1.tgz#c9eab428effce36cd6b92c924bdb000ef1f1ed1d"
- integrity sha512-lqjrjmaOoAnWfMmBPL+XNnynZh2+swxiX3WUE0s4yEHI6m+AwrK2UZOimIRl3X/4QctVqS8AiZjFqyOGrMXb/w==
- dependencies:
- boolbase "^1.0.0"
-
-object-assign@^4.1.0, object-assign@^4.1.1:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/object-assign/-/object-assign-4.1.1.tgz#2109adc7965887cfc05cbbd442cac8bfbb360863"
- integrity sha512-rJgTQnkUnH1sFw8yT6VSU3zD3sWmu6sZhIseY8VX+GRu3P6F7Fu+JNDoXfklElbLJSnc3FUQHVe4cU5hj+BcUg==
-
-object-inspect@^1.9.0:
- version "1.12.3"
- resolved "https://registry.yarnpkg.com/object-inspect/-/object-inspect-1.12.3.tgz#ba62dffd67ee256c8c086dfae69e016cd1f198b9"
- integrity sha512-geUvdk7c+eizMNUDkRpW1wJwgfOiOeHbxBR/hLXK1aT6zmVSO0jsQcs7fj6MGw89jC/cjGfLcNOrtMYtGqm81g==
-
-object-keys@^1.1.1:
- version "1.1.1"
- resolved "https://registry.yarnpkg.com/object-keys/-/object-keys-1.1.1.tgz#1c47f272df277f3b1daf061677d9c82e2322c60e"
- integrity sha512-NuAESUOUMrlIXOfHKzD6bpPu3tYt3xvjNdRIQ+FeT0lNb4K8WR70CaDxhuNguS2XG+GjkyMwOzsN5ZktImfhLA==
-
-object.assign@^4.1.0:
- version "4.1.4"
- resolved "https://registry.yarnpkg.com/object.assign/-/object.assign-4.1.4.tgz#9673c7c7c351ab8c4d0b516f4343ebf4dfb7799f"
- integrity sha512-1mxKf0e58bvyjSCtKYY4sRe9itRk3PJpquJOjeIkz885CczcI4IvJJDLPS72oowuSh+pBxUFROpX+TU++hxhZQ==
- dependencies:
- call-bind "^1.0.2"
- define-properties "^1.1.4"
- has-symbols "^1.0.3"
- object-keys "^1.1.1"
-
-obuf@^1.0.0, obuf@^1.1.2:
- version "1.1.2"
- resolved "https://registry.yarnpkg.com/obuf/-/obuf-1.1.2.tgz#09bea3343d41859ebd446292d11c9d4db619084e"
- integrity sha512-PX1wu0AmAdPqOL1mWhqmlOd8kOIZQwGZw6rh7uby9fTc5lhaOWFLX3I6R1hrF9k3zUY40e6igsLGkDXK92LJNg==
-
-on-finished@2.4.1:
- version "2.4.1"
- resolved "https://registry.yarnpkg.com/on-finished/-/on-finished-2.4.1.tgz#58c8c44116e54845ad57f14ab10b03533184ac3f"
- integrity sha512-oVlzkg3ENAhCk2zdv7IJwd/QUD4z2RxRwpkcGY8psCVcCYZNq4wYnVWALHM+brtuJjePWiYF/ClmuDr8Ch5+kg==
- dependencies:
- ee-first "1.1.1"
-
-on-headers@~1.0.2:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/on-headers/-/on-headers-1.0.2.tgz#772b0ae6aaa525c399e489adfad90c403eb3c28f"
- integrity sha512-pZAE+FJLoyITytdqK0U5s+FIpjN0JP3OzFi/u8Rx+EV5/W+JTWGXG8xFzevE7AjBfDqHv/8vL8qQsIhHnqRkrA==
-
-once@^1.3.0, once@^1.3.1, once@^1.4.0:
- version "1.4.0"
- resolved "https://registry.yarnpkg.com/once/-/once-1.4.0.tgz#583b1aa775961d4b113ac17d9c50baef9dd76bd1"
- integrity sha512-lNaJgI+2Q5URQBkccEKHTQOPaXdUxnZZElQTZY0MFUAuaEqe1E+Nyvgdz/aIyNi6Z9MzO5dv1H8n58/GELp3+w==
- dependencies:
- wrappy "1"
-
-onetime@^5.1.2:
- version "5.1.2"
- resolved "https://registry.yarnpkg.com/onetime/-/onetime-5.1.2.tgz#d0e96ebb56b07476df1dd9c4806e5237985ca45e"
- integrity sha512-kbpaSSGJTWdAY5KPVeMOKXSrPtr8C8C7wodJbcsd51jRnmD+GZu8Y0VoU6Dm5Z4vWr0Ig/1NKuWRKf7j5aaYSg==
- dependencies:
- mimic-fn "^2.1.0"
-
-open@^8.0.9, open@^8.4.0:
- version "8.4.1"
- resolved "https://registry.yarnpkg.com/open/-/open-8.4.1.tgz#2ab3754c07f5d1f99a7a8d6a82737c95e3101cff"
- integrity sha512-/4b7qZNhv6Uhd7jjnREh1NjnPxlTq+XNWPG88Ydkj5AILcA5m3ajvcg57pB24EQjKv0dK62XnDqk9c/hkIG5Kg==
- dependencies:
- define-lazy-prop "^2.0.0"
- is-docker "^2.1.1"
- is-wsl "^2.2.0"
-
-opener@^1.5.2:
- version "1.5.2"
- resolved "https://registry.yarnpkg.com/opener/-/opener-1.5.2.tgz#5d37e1f35077b9dcac4301372271afdeb2a13598"
- integrity sha512-ur5UIdyw5Y7yEj9wLzhqXiy6GZ3Mwx0yGI+5sMn2r0N0v3cKJvUmFH5yPP+WXh9e0xfyzyJX95D8l088DNFj7A==
-
-p-cancelable@^1.0.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/p-cancelable/-/p-cancelable-1.1.0.tgz#d078d15a3af409220c886f1d9a0ca2e441ab26cc"
- integrity sha512-s73XxOZ4zpt1edZYZzvhqFa6uvQc1vwUa0K0BdtIZgQMAJj9IbebH+JkgKZc9h+B05PKHLOTl4ajG1BmNrVZlw==
-
-p-limit@^2.0.0, p-limit@^2.2.0:
- version "2.3.0"
- resolved "https://registry.yarnpkg.com/p-limit/-/p-limit-2.3.0.tgz#3dd33c647a214fdfffd835933eb086da0dc21db1"
- integrity sha512-//88mFWSJx8lxCzwdAABTJL2MyWB12+eIY7MDL2SqLmAkeKU9qxRvWuSyTjm3FUmpBEMuFfckAIqEaVGUDxb6w==
- dependencies:
- p-try "^2.0.0"
-
-p-limit@^3.0.2:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/p-limit/-/p-limit-3.1.0.tgz#e1daccbe78d0d1388ca18c64fea38e3e57e3706b"
- integrity sha512-TYOanM3wGwNGsZN2cVTYPArw454xnXj5qmWF1bEoAc4+cU/ol7GVh7odevjp1FNHduHc3KZMcFduxU5Xc6uJRQ==
- dependencies:
- yocto-queue "^0.1.0"
-
-p-locate@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/p-locate/-/p-locate-3.0.0.tgz#322d69a05c0264b25997d9f40cd8a891ab0064a4"
- integrity sha512-x+12w/To+4GFfgJhBEpiDcLozRJGegY+Ei7/z0tSLkMmxGZNybVMSfWj9aJn8Z5Fc7dBUNJOOVgPv2H7IwulSQ==
- dependencies:
- p-limit "^2.0.0"
-
-p-locate@^4.1.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/p-locate/-/p-locate-4.1.0.tgz#a3428bb7088b3a60292f66919278b7c297ad4f07"
- integrity sha512-R79ZZ/0wAxKGu3oYMlz8jy/kbhsNrS7SKZ7PxEHBgJ5+F2mtFW2fK2cOtBh1cHYkQsbzFV7I+EoRKe6Yt0oK7A==
- dependencies:
- p-limit "^2.2.0"
-
-p-locate@^5.0.0:
- version "5.0.0"
- resolved "https://registry.yarnpkg.com/p-locate/-/p-locate-5.0.0.tgz#83c8315c6785005e3bd021839411c9e110e6d834"
- integrity sha512-LaNjtRWUBY++zB5nE/NwcaoMylSPk+S+ZHNB1TzdbMJMny6dynpAGt7X/tl/QYq3TIeE6nxHppbo2LGymrG5Pw==
- dependencies:
- p-limit "^3.0.2"
-
-p-map@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/p-map/-/p-map-4.0.0.tgz#bb2f95a5eda2ec168ec9274e06a747c3e2904d2b"
- integrity sha512-/bjOqmgETBYB5BoEeGVea8dmvHb2m9GLy1E9W43yeyfP6QQCZGFNa+XRceJEuDB6zqr+gKpIAmlLebMpykw/MQ==
- dependencies:
- aggregate-error "^3.0.0"
-
-p-retry@^4.5.0:
- version "4.6.2"
- resolved "https://registry.yarnpkg.com/p-retry/-/p-retry-4.6.2.tgz#9baae7184057edd4e17231cee04264106e092a16"
- integrity sha512-312Id396EbJdvRONlngUx0NydfrIQ5lsYu0znKVUzVvArzEIt08V1qhtyESbGVd1FGX7UKtiFp5uwKZdM8wIuQ==
- dependencies:
- "@types/retry" "0.12.0"
- retry "^0.13.1"
-
-p-try@^2.0.0:
- version "2.2.0"
- resolved "https://registry.yarnpkg.com/p-try/-/p-try-2.2.0.tgz#cb2868540e313d61de58fafbe35ce9004d5540e6"
- integrity sha512-R4nPAVTAU0B9D35/Gk3uJf/7XYbQcyohSKdvAxIRSNghFl4e71hVoGnBNQz9cWaXxO2I10KTC+3jMdvvoKw6dQ==
-
-package-json@^6.3.0:
- version "6.5.0"
- resolved "https://registry.yarnpkg.com/package-json/-/package-json-6.5.0.tgz#6feedaca35e75725876d0b0e64974697fed145b0"
- integrity sha512-k3bdm2n25tkyxcjSKzB5x8kfVxlMdgsbPr0GkZcwHsLpba6cBjqCt1KlcChKEvxHIcTB1FVMuwoijZ26xex5MQ==
- dependencies:
- got "^9.6.0"
- registry-auth-token "^4.0.0"
- registry-url "^5.0.0"
- semver "^6.2.0"
-
-param-case@^3.0.4:
- version "3.0.4"
- resolved "https://registry.yarnpkg.com/param-case/-/param-case-3.0.4.tgz#7d17fe4aa12bde34d4a77d91acfb6219caad01c5"
- integrity sha512-RXlj7zCYokReqWpOPH9oYivUzLYZ5vAPIfEmCTNViosC78F8F0H9y7T7gG2M39ymgutxF5gcFEsyZQSph9Bp3A==
- dependencies:
- dot-case "^3.0.4"
- tslib "^2.0.3"
-
-parent-module@^1.0.0:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/parent-module/-/parent-module-1.0.1.tgz#691d2709e78c79fae3a156622452d00762caaaa2"
- integrity sha512-GQ2EWRpQV8/o+Aw8YqtfZZPfNRWZYkbidE9k5rpl/hC3vtHHBfGm2Ifi6qWV+coDGkrUKZAxE3Lot5kcsRlh+g==
- dependencies:
- callsites "^3.0.0"
-
-parse-entities@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/parse-entities/-/parse-entities-2.0.0.tgz#53c6eb5b9314a1f4ec99fa0fdf7ce01ecda0cbe8"
- integrity sha512-kkywGpCcRYhqQIchaWqZ875wzpS/bMKhz5HnN3p7wveJTkTtyAB/AlnS0f8DFSqYW1T82t6yEAkEcB+A1I3MbQ==
- dependencies:
- character-entities "^1.0.0"
- character-entities-legacy "^1.0.0"
- character-reference-invalid "^1.0.0"
- is-alphanumerical "^1.0.0"
- is-decimal "^1.0.0"
- is-hexadecimal "^1.0.0"
-
-parse-entities@^4.0.0:
- version "4.0.1"
- resolved "https://registry.yarnpkg.com/parse-entities/-/parse-entities-4.0.1.tgz#4e2a01111fb1c986549b944af39eeda258fc9e4e"
- integrity sha512-SWzvYcSJh4d/SGLIOQfZ/CoNv6BTlI6YEQ7Nj82oDVnRpwe/Z/F1EMx42x3JAOwGBlCjeCH0BRJQbQ/opHL17w==
- dependencies:
- "@types/unist" "^2.0.0"
- character-entities "^2.0.0"
- character-entities-legacy "^3.0.0"
- character-reference-invalid "^2.0.0"
- decode-named-character-reference "^1.0.0"
- is-alphanumerical "^2.0.0"
- is-decimal "^2.0.0"
- is-hexadecimal "^2.0.0"
-
-parse-json@^5.0.0:
- version "5.2.0"
- resolved "https://registry.yarnpkg.com/parse-json/-/parse-json-5.2.0.tgz#c76fc66dee54231c962b22bcc8a72cf2f99753cd"
- integrity sha512-ayCKvm/phCGxOkYRSCM82iDwct8/EonSEgCSxWxD7ve6jHggsFl4fZVQBPRNgQoKiuV/odhFrGzQXZwbifC8Rg==
- dependencies:
- "@babel/code-frame" "^7.0.0"
- error-ex "^1.3.1"
- json-parse-even-better-errors "^2.3.0"
- lines-and-columns "^1.1.6"
-
-parse-json@^6.0.0:
- version "6.0.2"
- resolved "https://registry.yarnpkg.com/parse-json/-/parse-json-6.0.2.tgz#6bf79c201351cc12d5d66eba48d5a097c13dc200"
- integrity sha512-SA5aMiaIjXkAiBrW/yPgLgQAQg42f7K3ACO+2l/zOvtQBwX58DMUsFJXelW2fx3yMBmWOVkR6j1MGsdSbCA4UA==
- dependencies:
- "@babel/code-frame" "^7.16.0"
- error-ex "^1.3.2"
- json-parse-even-better-errors "^2.3.1"
- lines-and-columns "^2.0.2"
-
-parse-numeric-range@^1.3.0:
- version "1.3.0"
- resolved "https://registry.yarnpkg.com/parse-numeric-range/-/parse-numeric-range-1.3.0.tgz#7c63b61190d61e4d53a1197f0c83c47bb670ffa3"
- integrity sha512-twN+njEipszzlMJd4ONUYgSfZPDxgHhT9Ahed5uTigpQn90FggW4SA/AIPq/6a149fTbE9qBEcSwE3FAEp6wQQ==
-
-parse5-htmlparser2-tree-adapter@^7.0.0:
- version "7.0.0"
- resolved "https://registry.yarnpkg.com/parse5-htmlparser2-tree-adapter/-/parse5-htmlparser2-tree-adapter-7.0.0.tgz#23c2cc233bcf09bb7beba8b8a69d46b08c62c2f1"
- integrity sha512-B77tOZrqqfUfnVcOrUvfdLbz4pu4RopLD/4vmu3HUPswwTA8OH0EMW9BlWR2B0RCoiZRAHEUu7IxeP1Pd1UU+g==
- dependencies:
- domhandler "^5.0.2"
- parse5 "^7.0.0"
-
-parse5@^6.0.0:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/parse5/-/parse5-6.0.1.tgz#e1a1c085c569b3dc08321184f19a39cc27f7c30b"
- integrity sha512-Ofn/CTFzRGTTxwpNEs9PP93gXShHcTq255nzRYSKe8AkVpZY7e1fpmTfOyoIvjP5HG7Z2ZM7VS9PPhQGW2pOpw==
-
-parse5@^7.0.0:
- version "7.1.2"
- resolved "https://registry.yarnpkg.com/parse5/-/parse5-7.1.2.tgz#0736bebbfd77793823240a23b7fc5e010b7f8e32"
- integrity sha512-Czj1WaSVpaoj0wbhMzLmWD69anp2WH7FXMB9n1Sy8/ZFF9jolSQVMu1Ij5WIyGmcBmhk7EOndpO4mIpihVqAXw==
- dependencies:
- entities "^4.4.0"
-
-parseurl@~1.3.2, parseurl@~1.3.3:
- version "1.3.3"
- resolved "https://registry.yarnpkg.com/parseurl/-/parseurl-1.3.3.tgz#9da19e7bee8d12dff0513ed5b76957793bc2e8d4"
- integrity sha512-CiyeOxFT/JZyN5m0z9PfXw4SCBJ6Sygz1Dpl0wqjlhDEGGBP1GnsUVEL0p63hoG1fcj3fHynXi9NYO4nWOL+qQ==
-
-pascal-case@^3.1.2:
- version "3.1.2"
- resolved "https://registry.yarnpkg.com/pascal-case/-/pascal-case-3.1.2.tgz#b48e0ef2b98e205e7c1dae747d0b1508237660eb"
- integrity sha512-uWlGT3YSnK9x3BQJaOdcZwrnV6hPpd8jFH1/ucpiLRPh/2zCVJKS19E4GvYHvaCcACn3foXZ0cLB9Wrx1KGe5g==
- dependencies:
- no-case "^3.0.4"
- tslib "^2.0.3"
-
-path-exists@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/path-exists/-/path-exists-3.0.0.tgz#ce0ebeaa5f78cb18925ea7d810d7b59b010fd515"
- integrity sha512-bpC7GYwiDYQ4wYLe+FA8lhRjhQCMcQGuSgGGqDkg/QerRWw9CmGRT0iSOVRSZJ29NMLZgIzqaljJ63oaL4NIJQ==
-
-path-exists@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/path-exists/-/path-exists-4.0.0.tgz#513bdbe2d3b95d7762e8c1137efa195c6c61b5b3"
- integrity sha512-ak9Qy5Q7jYb2Wwcey5Fpvg2KoAc/ZIhLSLOSBmRmygPsGwkVVt0fZa0qrtMz+m6tJTAHfZQ8FnmB4MG4LWy7/w==
-
-path-is-absolute@^1.0.0:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/path-is-absolute/-/path-is-absolute-1.0.1.tgz#174b9268735534ffbc7ace6bf53a5a9e1b5c5f5f"
- integrity sha512-AVbw3UJ2e9bq64vSaS9Am0fje1Pa8pbGqTTsmXfaIiMpnr5DlDhfJOuLj9Sf95ZPVDAUerDfEk88MPmPe7UCQg==
-
-path-is-inside@1.0.2:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/path-is-inside/-/path-is-inside-1.0.2.tgz#365417dede44430d1c11af61027facf074bdfc53"
- integrity sha512-DUWJr3+ULp4zXmol/SZkFf3JGsS9/SIv+Y3Rt93/UjPpDpklB5f1er4O3POIbUuUJ3FXgqte2Q7SrU6zAqwk8w==
-
-path-key@^3.0.0, path-key@^3.1.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/path-key/-/path-key-3.1.1.tgz#581f6ade658cbba65a0d3380de7753295054f375"
- integrity sha512-ojmeN0qd+y0jszEtoY48r0Peq5dwMEkIlCOu6Q5f41lfkswXuKtYrhgoTpLnyIcHm24Uhqx+5Tqm2InSwLhE6Q==
-
-path-parse@^1.0.7:
- version "1.0.7"
- resolved "https://registry.yarnpkg.com/path-parse/-/path-parse-1.0.7.tgz#fbc114b60ca42b30d9daf5858e4bd68bbedb6735"
- integrity sha512-LDJzPVEEEPR+y48z93A0Ed0yXb8pAByGWo/k5YYdYgpY2/2EsOsksJrq7lOHxryrVOn1ejG6oAp8ahvOIQD8sw==
-
-path-to-regexp@0.1.7:
- version "0.1.7"
- resolved "https://registry.yarnpkg.com/path-to-regexp/-/path-to-regexp-0.1.7.tgz#df604178005f522f15eb4490e7247a1bfaa67f8c"
- integrity sha512-5DFkuoqlv1uYQKxy8omFBeJPQcdoE07Kv2sferDCrAq1ohOU+MSDswDIbnx3YAM60qIOnYa53wBhXW0EbMonrQ==
-
-path-to-regexp@2.2.1:
- version "2.2.1"
- resolved "https://registry.yarnpkg.com/path-to-regexp/-/path-to-regexp-2.2.1.tgz#90b617025a16381a879bc82a38d4e8bdeb2bcf45"
- integrity sha512-gu9bD6Ta5bwGrrU8muHzVOBFFREpp2iRkVfhBJahwJ6p6Xw20SjT0MxLnwkjOibQmGSYhiUnf2FLe7k+jcFmGQ==
-
-path-to-regexp@^1.7.0:
- version "1.8.0"
- resolved "https://registry.yarnpkg.com/path-to-regexp/-/path-to-regexp-1.8.0.tgz#887b3ba9d84393e87a0a0b9f4cb756198b53548a"
- integrity sha512-n43JRhlUKUAlibEJhPeir1ncUID16QnEjNpwzNdO3Lm4ywrBpBZ5oLD0I6br9evr1Y9JTqwRtAh7JLoOzAQdVA==
- dependencies:
- isarray "0.0.1"
-
-path-type@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/path-type/-/path-type-4.0.0.tgz#84ed01c0a7ba380afe09d90a8c180dcd9d03043b"
- integrity sha512-gDKb8aZMDeD/tZWs9P6+q0J9Mwkdl6xMV8TjnGP3qJVJ06bdMgkbBlLU8IdfOsIsFz2BW1rNVT3XuNEl8zPAvw==
-
-picocolors@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/picocolors/-/picocolors-1.0.0.tgz#cb5bdc74ff3f51892236eaf79d68bc44564ab81c"
- integrity sha512-1fygroTLlHu66zi26VoTDv8yRgm0Fccecssto+MhsZ0D/DGW2sm8E8AjW7NU5VVTRt5GxbeZ5qBuJr+HyLYkjQ==
-
-picomatch@^2.0.4, picomatch@^2.2.1, picomatch@^2.2.3, picomatch@^2.3.1:
- version "2.3.1"
- resolved "https://registry.yarnpkg.com/picomatch/-/picomatch-2.3.1.tgz#3ba3833733646d9d3e4995946c1365a67fb07a42"
- integrity sha512-JU3teHTNjmE2VCGFzuY8EXzCDVwEqB2a8fsIvwaStHhAWJEeVd1o1QD80CU6+ZdEXXSLbSsuLwJjkCBWqRQUVA==
-
-pkg-dir@^4.1.0:
- version "4.2.0"
- resolved "https://registry.yarnpkg.com/pkg-dir/-/pkg-dir-4.2.0.tgz#f099133df7ede422e81d1d8448270eeb3e4261f3"
- integrity sha512-HRDzbaKjC+AOWVXxAU/x54COGeIv9eb+6CkDSQoNTt4XyWoIJvuPsXizxu/Fr23EiekbtZwmh1IcIG/l/a10GQ==
- dependencies:
- find-up "^4.0.0"
-
-pkg-up@^3.1.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/pkg-up/-/pkg-up-3.1.0.tgz#100ec235cc150e4fd42519412596a28512a0def5"
- integrity sha512-nDywThFk1i4BQK4twPQ6TA4RT8bDY96yeuCVBWL3ePARCiEKDRSrNGbFIgUJpLp+XeIR65v8ra7WuJOFUBtkMA==
- dependencies:
- find-up "^3.0.0"
-
-pluralize@^8.0.0:
- version "8.0.0"
- resolved "https://registry.yarnpkg.com/pluralize/-/pluralize-8.0.0.tgz#1a6fa16a38d12a1901e0320fa017051c539ce3b1"
- integrity sha512-Nc3IT5yHzflTfbjgqWcCPpo7DaKy4FnpB0l/zCAW0Tc7jxAiuqSxHasntB3D7887LSrA93kDJ9IXovxJYxyLCA==
-
-postcss-calc@^8.2.3:
- version "8.2.4"
- resolved "https://registry.yarnpkg.com/postcss-calc/-/postcss-calc-8.2.4.tgz#77b9c29bfcbe8a07ff6693dc87050828889739a5"
- integrity sha512-SmWMSJmB8MRnnULldx0lQIyhSNvuDl9HfrZkaqqE/WHAhToYsAvDq+yAsA/kIyINDszOp3Rh0GFoNuH5Ypsm3Q==
- dependencies:
- postcss-selector-parser "^6.0.9"
- postcss-value-parser "^4.2.0"
-
-postcss-colormin@^5.3.0:
- version "5.3.0"
- resolved "https://registry.yarnpkg.com/postcss-colormin/-/postcss-colormin-5.3.0.tgz#3cee9e5ca62b2c27e84fce63affc0cfb5901956a"
- integrity sha512-WdDO4gOFG2Z8n4P8TWBpshnL3JpmNmJwdnfP2gbk2qBA8PWwOYcmjmI/t3CmMeL72a7Hkd+x/Mg9O2/0rD54Pg==
- dependencies:
- browserslist "^4.16.6"
- caniuse-api "^3.0.0"
- colord "^2.9.1"
- postcss-value-parser "^4.2.0"
-
-postcss-convert-values@^5.1.3:
- version "5.1.3"
- resolved "https://registry.yarnpkg.com/postcss-convert-values/-/postcss-convert-values-5.1.3.tgz#04998bb9ba6b65aa31035d669a6af342c5f9d393"
- integrity sha512-82pC1xkJZtcJEfiLw6UXnXVXScgtBrjlO5CBmuDQc+dlb88ZYheFsjTn40+zBVi3DkfF7iezO0nJUPLcJK3pvA==
- dependencies:
- browserslist "^4.21.4"
- postcss-value-parser "^4.2.0"
-
-postcss-discard-comments@^5.1.2:
- version "5.1.2"
- resolved "https://registry.yarnpkg.com/postcss-discard-comments/-/postcss-discard-comments-5.1.2.tgz#8df5e81d2925af2780075840c1526f0660e53696"
- integrity sha512-+L8208OVbHVF2UQf1iDmRcbdjJkuBF6IS29yBDSiWUIzpYaAhtNl6JYnYm12FnkeCwQqF5LeklOu6rAqgfBZqQ==
-
-postcss-discard-duplicates@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-discard-duplicates/-/postcss-discard-duplicates-5.1.0.tgz#9eb4fe8456706a4eebd6d3b7b777d07bad03e848"
- integrity sha512-zmX3IoSI2aoenxHV6C7plngHWWhUOV3sP1T8y2ifzxzbtnuhk1EdPwm0S1bIUNaJ2eNbWeGLEwzw8huPD67aQw==
-
-postcss-discard-empty@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-discard-empty/-/postcss-discard-empty-5.1.1.tgz#e57762343ff7f503fe53fca553d18d7f0c369c6c"
- integrity sha512-zPz4WljiSuLWsI0ir4Mcnr4qQQ5e1Ukc3i7UfE2XcrwKK2LIPIqE5jxMRxO6GbI3cv//ztXDsXwEWT3BHOGh3A==
-
-postcss-discard-overridden@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-discard-overridden/-/postcss-discard-overridden-5.1.0.tgz#7e8c5b53325747e9d90131bb88635282fb4a276e"
- integrity sha512-21nOL7RqWR1kasIVdKs8HNqQJhFxLsyRfAnUDm4Fe4t4mCWL9OJiHvlHPjcd8zc5Myu89b/7wZDnOSjFgeWRtw==
-
-postcss-discard-unused@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-discard-unused/-/postcss-discard-unused-5.1.0.tgz#8974e9b143d887677304e558c1166d3762501142"
- integrity sha512-KwLWymI9hbwXmJa0dkrzpRbSJEh0vVUd7r8t0yOGPcfKzyJJxFM8kLyC5Ev9avji6nY95pOp1W6HqIrfT+0VGw==
- dependencies:
- postcss-selector-parser "^6.0.5"
-
-postcss-loader@^7.0.0:
- version "7.0.2"
- resolved "https://registry.yarnpkg.com/postcss-loader/-/postcss-loader-7.0.2.tgz#b53ff44a26fba3688eee92a048c7f2d4802e23bb"
- integrity sha512-fUJzV/QH7NXUAqV8dWJ9Lg4aTkDCezpTS5HgJ2DvqznexTbSTxgi/dTECvTZ15BwKTtk8G/bqI/QTu2HPd3ZCg==
- dependencies:
- cosmiconfig "^7.0.0"
- klona "^2.0.5"
- semver "^7.3.8"
-
-postcss-merge-idents@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-merge-idents/-/postcss-merge-idents-5.1.1.tgz#7753817c2e0b75d0853b56f78a89771e15ca04a1"
- integrity sha512-pCijL1TREiCoog5nQp7wUe+TUonA2tC2sQ54UGeMmryK3UFGIYKqDyjnqd6RcuI4znFn9hWSLNN8xKE/vWcUQw==
- dependencies:
- cssnano-utils "^3.1.0"
- postcss-value-parser "^4.2.0"
-
-postcss-merge-longhand@^5.1.7:
- version "5.1.7"
- resolved "https://registry.yarnpkg.com/postcss-merge-longhand/-/postcss-merge-longhand-5.1.7.tgz#24a1bdf402d9ef0e70f568f39bdc0344d568fb16"
- integrity sha512-YCI9gZB+PLNskrK0BB3/2OzPnGhPkBEwmwhfYk1ilBHYVAZB7/tkTHFBAnCrvBBOmeYyMYw3DMjT55SyxMBzjQ==
- dependencies:
- postcss-value-parser "^4.2.0"
- stylehacks "^5.1.1"
-
-postcss-merge-rules@^5.1.3:
- version "5.1.3"
- resolved "https://registry.yarnpkg.com/postcss-merge-rules/-/postcss-merge-rules-5.1.3.tgz#8f97679e67cc8d08677a6519afca41edf2220894"
- integrity sha512-LbLd7uFC00vpOuMvyZop8+vvhnfRGpp2S+IMQKeuOZZapPRY4SMq5ErjQeHbHsjCUgJkRNrlU+LmxsKIqPKQlA==
- dependencies:
- browserslist "^4.21.4"
- caniuse-api "^3.0.0"
- cssnano-utils "^3.1.0"
- postcss-selector-parser "^6.0.5"
-
-postcss-minify-font-values@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-minify-font-values/-/postcss-minify-font-values-5.1.0.tgz#f1df0014a726083d260d3bd85d7385fb89d1f01b"
- integrity sha512-el3mYTgx13ZAPPirSVsHqFzl+BBBDrXvbySvPGFnQcTI4iNslrPaFq4muTkLZmKlGk4gyFAYUBMH30+HurREyA==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-minify-gradients@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-minify-gradients/-/postcss-minify-gradients-5.1.1.tgz#f1fe1b4f498134a5068240c2f25d46fcd236ba2c"
- integrity sha512-VGvXMTpCEo4qHTNSa9A0a3D+dxGFZCYwR6Jokk+/3oB6flu2/PnPXAh2x7x52EkY5xlIHLm+Le8tJxe/7TNhzw==
- dependencies:
- colord "^2.9.1"
- cssnano-utils "^3.1.0"
- postcss-value-parser "^4.2.0"
-
-postcss-minify-params@^5.1.4:
- version "5.1.4"
- resolved "https://registry.yarnpkg.com/postcss-minify-params/-/postcss-minify-params-5.1.4.tgz#c06a6c787128b3208b38c9364cfc40c8aa5d7352"
- integrity sha512-+mePA3MgdmVmv6g+30rn57USjOGSAyuxUmkfiWpzalZ8aiBkdPYjXWtHuwJGm1v5Ojy0Z0LaSYhHaLJQB0P8Jw==
- dependencies:
- browserslist "^4.21.4"
- cssnano-utils "^3.1.0"
- postcss-value-parser "^4.2.0"
-
-postcss-minify-selectors@^5.2.1:
- version "5.2.1"
- resolved "https://registry.yarnpkg.com/postcss-minify-selectors/-/postcss-minify-selectors-5.2.1.tgz#d4e7e6b46147b8117ea9325a915a801d5fe656c6"
- integrity sha512-nPJu7OjZJTsVUmPdm2TcaiohIwxP+v8ha9NehQ2ye9szv4orirRU3SDdtUmKH+10nzn0bAyOXZ0UEr7OpvLehg==
- dependencies:
- postcss-selector-parser "^6.0.5"
-
-postcss-modules-extract-imports@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/postcss-modules-extract-imports/-/postcss-modules-extract-imports-3.0.0.tgz#cda1f047c0ae80c97dbe28c3e76a43b88025741d"
- integrity sha512-bdHleFnP3kZ4NYDhuGlVK+CMrQ/pqUm8bx/oGL93K6gVwiclvX5x0n76fYMKuIGKzlABOy13zsvqjb0f92TEXw==
-
-postcss-modules-local-by-default@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/postcss-modules-local-by-default/-/postcss-modules-local-by-default-4.0.0.tgz#ebbb54fae1598eecfdf691a02b3ff3b390a5a51c"
- integrity sha512-sT7ihtmGSF9yhm6ggikHdV0hlziDTX7oFoXtuVWeDd3hHObNkcHRo9V3yg7vCAY7cONyxJC/XXCmmiHHcvX7bQ==
- dependencies:
- icss-utils "^5.0.0"
- postcss-selector-parser "^6.0.2"
- postcss-value-parser "^4.1.0"
-
-postcss-modules-scope@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/postcss-modules-scope/-/postcss-modules-scope-3.0.0.tgz#9ef3151456d3bbfa120ca44898dfca6f2fa01f06"
- integrity sha512-hncihwFA2yPath8oZ15PZqvWGkWf+XUfQgUGamS4LqoP1anQLOsOJw0vr7J7IwLpoY9fatA2qiGUGmuZL0Iqlg==
- dependencies:
- postcss-selector-parser "^6.0.4"
-
-postcss-modules-values@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/postcss-modules-values/-/postcss-modules-values-4.0.0.tgz#d7c5e7e68c3bb3c9b27cbf48ca0bb3ffb4602c9c"
- integrity sha512-RDxHkAiEGI78gS2ofyvCsu7iycRv7oqw5xMWn9iMoR0N/7mf9D50ecQqUo5BZ9Zh2vH4bCUR/ktCqbB9m8vJjQ==
- dependencies:
- icss-utils "^5.0.0"
-
-postcss-normalize-charset@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-normalize-charset/-/postcss-normalize-charset-5.1.0.tgz#9302de0b29094b52c259e9b2cf8dc0879879f0ed"
- integrity sha512-mSgUJ+pd/ldRGVx26p2wz9dNZ7ji6Pn8VWBajMXFf8jk7vUoSrZ2lt/wZR7DtlZYKesmZI680qjr2CeFF2fbUg==
-
-postcss-normalize-display-values@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-normalize-display-values/-/postcss-normalize-display-values-5.1.0.tgz#72abbae58081960e9edd7200fcf21ab8325c3da8"
- integrity sha512-WP4KIM4o2dazQXWmFaqMmcvsKmhdINFblgSeRgn8BJ6vxaMyaJkwAzpPpuvSIoG/rmX3M+IrRZEz2H0glrQNEA==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-positions@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-normalize-positions/-/postcss-normalize-positions-5.1.1.tgz#ef97279d894087b59325b45c47f1e863daefbb92"
- integrity sha512-6UpCb0G4eofTCQLFVuI3EVNZzBNPiIKcA1AKVka+31fTVySphr3VUgAIULBhxZkKgwLImhzMR2Bw1ORK+37INg==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-repeat-style@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-normalize-repeat-style/-/postcss-normalize-repeat-style-5.1.1.tgz#e9eb96805204f4766df66fd09ed2e13545420fb2"
- integrity sha512-mFpLspGWkQtBcWIRFLmewo8aC3ImN2i/J3v8YCFUwDnPu3Xz4rLohDO26lGjwNsQxB3YF0KKRwspGzE2JEuS0g==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-string@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-normalize-string/-/postcss-normalize-string-5.1.0.tgz#411961169e07308c82c1f8c55f3e8a337757e228"
- integrity sha512-oYiIJOf4T9T1N4i+abeIc7Vgm/xPCGih4bZz5Nm0/ARVJ7K6xrDlLwvwqOydvyL3RHNf8qZk6vo3aatiw/go3w==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-timing-functions@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-normalize-timing-functions/-/postcss-normalize-timing-functions-5.1.0.tgz#d5614410f8f0b2388e9f240aa6011ba6f52dafbb"
- integrity sha512-DOEkzJ4SAXv5xkHl0Wa9cZLF3WCBhF3o1SKVxKQAa+0pYKlueTpCgvkFAHfk+Y64ezX9+nITGrDZeVGgITJXjg==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-unicode@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-normalize-unicode/-/postcss-normalize-unicode-5.1.1.tgz#f67297fca3fea7f17e0d2caa40769afc487aa030"
- integrity sha512-qnCL5jzkNUmKVhZoENp1mJiGNPcsJCs1aaRmURmeJGES23Z/ajaln+EPTD+rBeNkSryI+2WTdW+lwcVdOikrpA==
- dependencies:
- browserslist "^4.21.4"
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-url@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-normalize-url/-/postcss-normalize-url-5.1.0.tgz#ed9d88ca82e21abef99f743457d3729a042adcdc"
- integrity sha512-5upGeDO+PVthOxSmds43ZeMeZfKH+/DKgGRD7TElkkyS46JXAUhMzIKiCa7BabPeIy3AQcTkXwVVN7DbqsiCew==
- dependencies:
- normalize-url "^6.0.1"
- postcss-value-parser "^4.2.0"
-
-postcss-normalize-whitespace@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-normalize-whitespace/-/postcss-normalize-whitespace-5.1.1.tgz#08a1a0d1ffa17a7cc6efe1e6c9da969cc4493cfa"
- integrity sha512-83ZJ4t3NUDETIHTa3uEg6asWjSBYL5EdkVB0sDncx9ERzOKBVJIUeDO9RyA9Zwtig8El1d79HBp0JEi8wvGQnA==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-ordered-values@^5.1.3:
- version "5.1.3"
- resolved "https://registry.yarnpkg.com/postcss-ordered-values/-/postcss-ordered-values-5.1.3.tgz#b6fd2bd10f937b23d86bc829c69e7732ce76ea38"
- integrity sha512-9UO79VUhPwEkzbb3RNpqqghc6lcYej1aveQteWY+4POIwlqkYE21HKWaLDF6lWNuqCobEAyTovVhtI32Rbv2RQ==
- dependencies:
- cssnano-utils "^3.1.0"
- postcss-value-parser "^4.2.0"
-
-postcss-reduce-idents@^5.2.0:
- version "5.2.0"
- resolved "https://registry.yarnpkg.com/postcss-reduce-idents/-/postcss-reduce-idents-5.2.0.tgz#c89c11336c432ac4b28792f24778859a67dfba95"
- integrity sha512-BTrLjICoSB6gxbc58D5mdBK8OhXRDqud/zodYfdSi52qvDHdMwk+9kB9xsM8yJThH/sZU5A6QVSmMmaN001gIg==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-reduce-initial@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-reduce-initial/-/postcss-reduce-initial-5.1.1.tgz#c18b7dfb88aee24b1f8e4936541c29adbd35224e"
- integrity sha512-//jeDqWcHPuXGZLoolFrUXBDyuEGbr9S2rMo19bkTIjBQ4PqkaO+oI8wua5BOUxpfi97i3PCoInsiFIEBfkm9w==
- dependencies:
- browserslist "^4.21.4"
- caniuse-api "^3.0.0"
-
-postcss-reduce-transforms@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-reduce-transforms/-/postcss-reduce-transforms-5.1.0.tgz#333b70e7758b802f3dd0ddfe98bb1ccfef96b6e9"
- integrity sha512-2fbdbmgir5AvpW9RLtdONx1QoYG2/EtqpNQbFASDlixBbAYuTcJ0dECwlqNqH7VbaUnEnh8SrxOe2sRIn24XyQ==
- dependencies:
- postcss-value-parser "^4.2.0"
-
-postcss-selector-parser@^6.0.2, postcss-selector-parser@^6.0.4, postcss-selector-parser@^6.0.5, postcss-selector-parser@^6.0.9:
- version "6.0.11"
- resolved "https://registry.yarnpkg.com/postcss-selector-parser/-/postcss-selector-parser-6.0.11.tgz#2e41dc39b7ad74046e1615185185cd0b17d0c8dc"
- integrity sha512-zbARubNdogI9j7WY4nQJBiNqQf3sLS3wCP4WfOidu+p28LofJqDH1tcXypGrcmMHhDk2t9wGhCsYe/+szLTy1g==
- dependencies:
- cssesc "^3.0.0"
- util-deprecate "^1.0.2"
-
-postcss-sort-media-queries@^4.2.1:
- version "4.3.0"
- resolved "https://registry.yarnpkg.com/postcss-sort-media-queries/-/postcss-sort-media-queries-4.3.0.tgz#f48a77d6ce379e86676fc3f140cf1b10a06f6051"
- integrity sha512-jAl8gJM2DvuIJiI9sL1CuiHtKM4s5aEIomkU8G3LFvbP+p8i7Sz8VV63uieTgoewGqKbi+hxBTiOKJlB35upCg==
- dependencies:
- sort-css-media-queries "2.1.0"
-
-postcss-svgo@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-svgo/-/postcss-svgo-5.1.0.tgz#0a317400ced789f233a28826e77523f15857d80d"
- integrity sha512-D75KsH1zm5ZrHyxPakAxJWtkyXew5qwS70v56exwvw542d9CRtTo78K0WeFxZB4G7JXKKMbEZtZayTGdIky/eA==
- dependencies:
- postcss-value-parser "^4.2.0"
- svgo "^2.7.0"
-
-postcss-unique-selectors@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/postcss-unique-selectors/-/postcss-unique-selectors-5.1.1.tgz#a9f273d1eacd09e9aa6088f4b0507b18b1b541b6"
- integrity sha512-5JiODlELrz8L2HwxfPnhOWZYWDxVHWL83ufOv84NrcgipI7TaeRsatAhK4Tr2/ZiYldpK/wBvw5BD3qfaK96GA==
- dependencies:
- postcss-selector-parser "^6.0.5"
-
-postcss-value-parser@^4.1.0, postcss-value-parser@^4.2.0:
- version "4.2.0"
- resolved "https://registry.yarnpkg.com/postcss-value-parser/-/postcss-value-parser-4.2.0.tgz#723c09920836ba6d3e5af019f92bc0971c02e514"
- integrity sha512-1NNCs6uurfkVbeXG4S8JFT9t19m45ICnif8zWLd5oPSZ50QnwMfK+H3jv408d4jw/7Bttv5axS5IiHoLaVNHeQ==
-
-postcss-zindex@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/postcss-zindex/-/postcss-zindex-5.1.0.tgz#4a5c7e5ff1050bd4c01d95b1847dfdcc58a496ff"
- integrity sha512-fgFMf0OtVSBR1va1JNHYgMxYk73yhn/qb4uQDq1DLGYolz8gHCyr/sesEuGUaYs58E3ZJRcpoGuPVoB7Meiq9A==
-
-postcss@^8.3.11, postcss@^8.4.13, postcss@^8.4.14, postcss@^8.4.17, postcss@^8.4.19:
- version "8.4.21"
- resolved "https://registry.yarnpkg.com/postcss/-/postcss-8.4.21.tgz#c639b719a57efc3187b13a1d765675485f4134f4"
- integrity sha512-tP7u/Sn/dVxK2NnruI4H9BG+x+Wxz6oeZ1cJ8P6G/PZY0IKk4k/63TDsQf2kQq3+qoJeLm2kIBUNlZe3zgb4Zg==
- dependencies:
- nanoid "^3.3.4"
- picocolors "^1.0.0"
- source-map-js "^1.0.2"
-
-prepend-http@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/prepend-http/-/prepend-http-2.0.0.tgz#e92434bfa5ea8c19f41cdfd401d741a3c819d897"
- integrity sha512-ravE6m9Atw9Z/jjttRUZ+clIXogdghyZAuWJ3qEzjT+jI/dL1ifAqhZeC5VHzQp1MSt1+jxKkFNemj/iO7tVUA==
-
-pretty-error@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/pretty-error/-/pretty-error-4.0.0.tgz#90a703f46dd7234adb46d0f84823e9d1cb8f10d6"
- integrity sha512-AoJ5YMAcXKYxKhuJGdcvse+Voc6v1RgnsR3nWcYU7q4t6z0Q6T86sv5Zq8VIRbOWWFpvdGE83LtdSMNd+6Y0xw==
- dependencies:
- lodash "^4.17.20"
- renderkid "^3.0.0"
-
-pretty-time@^1.1.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/pretty-time/-/pretty-time-1.1.0.tgz#ffb7429afabb8535c346a34e41873adf3d74dd0e"
- integrity sha512-28iF6xPQrP8Oa6uxE6a1biz+lWeTOAPKggvjB8HAs6nVMKZwf5bG++632Dx614hIWgUPkgivRfG+a8uAXGTIbA==
-
-prism-react-renderer@^1.3.3, prism-react-renderer@^1.3.5:
- version "1.3.5"
- resolved "https://registry.yarnpkg.com/prism-react-renderer/-/prism-react-renderer-1.3.5.tgz#786bb69aa6f73c32ba1ee813fbe17a0115435085"
- integrity sha512-IJ+MSwBWKG+SM3b2SUfdrhC+gu01QkV2KmRQgREThBfSQRoufqRfxfHUxpG1WcaFjP+kojcFyO9Qqtpgt3qLCg==
-
-prismjs@^1.28.0:
- version "1.29.0"
- resolved "https://registry.yarnpkg.com/prismjs/-/prismjs-1.29.0.tgz#f113555a8fa9b57c35e637bba27509dcf802dd12"
- integrity sha512-Kx/1w86q/epKcmte75LNrEoT+lX8pBpavuAbvJWRXar7Hz8jrtF+e3vY751p0R8H9HdArwaCTNDDzHg/ScJK1Q==
-
-proc-log@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/proc-log/-/proc-log-3.0.0.tgz#fb05ef83ccd64fd7b20bbe9c8c1070fc08338dd8"
- integrity sha512-++Vn7NS4Xf9NacaU9Xq3URUuqZETPsf8L4j5/ckhaRYsfPeRyzGw+iDjFhV/Jr3uNmTvvddEJFWh5R1gRgUH8A==
-
-process-nextick-args@~2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/process-nextick-args/-/process-nextick-args-2.0.1.tgz#7820d9b16120cc55ca9ae7792680ae7dba6d7fe2"
- integrity sha512-3ouUOpQhtgrbOa17J7+uxOTpITYWaGP7/AhoR3+A+/1e9skrzelGi/dXzEYyvbxubEF6Wn2ypscTKiKJFFn1ag==
-
-promise@^7.1.1:
- version "7.3.1"
- resolved "https://registry.yarnpkg.com/promise/-/promise-7.3.1.tgz#064b72602b18f90f29192b8b1bc418ffd1ebd3bf"
- integrity sha512-nolQXZ/4L+bP/UGlkfaIujX9BKxGwmQ9OT4mOt5yvy8iK1h3wqTEJCijzGANTCCl9nWjY41juyAn2K3Q1hLLTg==
- dependencies:
- asap "~2.0.3"
-
-prompts@^2.4.2:
- version "2.4.2"
- resolved "https://registry.yarnpkg.com/prompts/-/prompts-2.4.2.tgz#7b57e73b3a48029ad10ebd44f74b01722a4cb069"
- integrity sha512-NxNv/kLguCA7p3jE8oL2aEBsrJWgAakBpgmgK6lpPWV+WuOmY6r2/zbAVnP+T8bQlA0nzHXSJSJW0Hq7ylaD2Q==
- dependencies:
- kleur "^3.0.3"
- sisteransi "^1.0.5"
-
-prop-types@^15.6.2, prop-types@^15.7.2:
- version "15.8.1"
- resolved "https://registry.yarnpkg.com/prop-types/-/prop-types-15.8.1.tgz#67d87bf1a694f48435cf332c24af10214a3140b5"
- integrity sha512-oj87CgZICdulUohogVAR7AjlC0327U4el4L6eAvOqCeudMDVU0NThNaV+b9Df4dXgSP1gXMTnPdhfe/2qDH5cg==
- dependencies:
- loose-envify "^1.4.0"
- object-assign "^4.1.1"
- react-is "^16.13.1"
-
-property-information@^5.0.0, property-information@^5.3.0:
- version "5.6.0"
- resolved "https://registry.yarnpkg.com/property-information/-/property-information-5.6.0.tgz#61675545fb23002f245c6540ec46077d4da3ed69"
- integrity sha512-YUHSPk+A30YPv+0Qf8i9Mbfe/C0hdPXk1s1jPVToV8pk8BQtpw10ct89Eo7OWkutrwqvT0eicAxlOg3dOAu8JA==
- dependencies:
- xtend "^4.0.0"
-
-proxy-addr@~2.0.7:
- version "2.0.7"
- resolved "https://registry.yarnpkg.com/proxy-addr/-/proxy-addr-2.0.7.tgz#f19fe69ceab311eeb94b42e70e8c2070f9ba1025"
- integrity sha512-llQsMLSUDUPT44jdrU/O37qlnifitDP+ZwrmmZcoSKyLKvtZxpyV0n2/bD/N4tBAAZ/gJEdZU7KMraoK1+XYAg==
- dependencies:
- forwarded "0.2.0"
- ipaddr.js "1.9.1"
-
-pump@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/pump/-/pump-3.0.0.tgz#b4a2116815bde2f4e1ea602354e8c75565107a64"
- integrity sha512-LwZy+p3SFs1Pytd/jYct4wpv49HiYCqd9Rlc5ZVdk0V+8Yzv6jR5Blk3TRmPL1ft69TxP0IMZGJ+WPFU2BFhww==
- dependencies:
- end-of-stream "^1.1.0"
- once "^1.3.1"
-
-punycode@^1.3.2:
- version "1.4.1"
- resolved "https://registry.yarnpkg.com/punycode/-/punycode-1.4.1.tgz#c0d5a63b2718800ad8e1eb0fa5269c84dd41845e"
- integrity sha512-jmYNElW7yvO7TV33CjSmvSiE2yco3bV2czu/OzDKdMNVZQWfxCblURLhf+47syQRBntjfLdd/H0egrzIG+oaFQ==
-
-punycode@^2.1.0:
- version "2.3.0"
- resolved "https://registry.yarnpkg.com/punycode/-/punycode-2.3.0.tgz#f67fa67c94da8f4d0cfff981aee4118064199b8f"
- integrity sha512-rRV+zQD8tVFys26lAGR9WUuS4iUAngJScM+ZRSKtvl5tKeZ2t5bvdNFdNHBW9FWR4guGHlgmsZ1G7BSm2wTbuA==
-
-pupa@^2.1.1:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/pupa/-/pupa-2.1.1.tgz#f5e8fd4afc2c5d97828faa523549ed8744a20d62"
- integrity sha512-l1jNAspIBSFqbT+y+5FosojNpVpF94nlI+wDUpqP9enwOTfHx9f0gh5nB96vl+6yTpsJsypeNrwfzPrKuHB41A==
- dependencies:
- escape-goat "^2.0.0"
-
-pure-color@^1.2.0:
- version "1.3.0"
- resolved "https://registry.yarnpkg.com/pure-color/-/pure-color-1.3.0.tgz#1fe064fb0ac851f0de61320a8bf796836422f33e"
- integrity sha512-QFADYnsVoBMw1srW7OVKEYjG+MbIa49s54w1MA1EDY6r2r/sTcKKYqRX1f4GYvnXP7eN/Pe9HFcX+hwzmrXRHA==
-
-qs@6.11.0:
- version "6.11.0"
- resolved "https://registry.yarnpkg.com/qs/-/qs-6.11.0.tgz#fd0d963446f7a65e1367e01abd85429453f0c37a"
- integrity sha512-MvjoMCJwEarSbUYk5O+nmoSzSutSsTwF85zcHPQ9OrlFoZOYIjaqBAJIqIXjptyD5vThxGq52Xu/MaJzRkIk4Q==
- dependencies:
- side-channel "^1.0.4"
-
-queue-microtask@^1.2.2:
- version "1.2.3"
- resolved "https://registry.yarnpkg.com/queue-microtask/-/queue-microtask-1.2.3.tgz#4929228bbc724dfac43e0efb058caf7b6cfb6243"
- integrity sha512-NuaNSa6flKT5JaSYQzJok04JzTL1CA6aGhv5rfLW3PgqA+M2ChpZQnAC8h8i4ZFkBS8X5RqkDBHA7r4hej3K9A==
-
-queue@6.0.2:
- version "6.0.2"
- resolved "https://registry.yarnpkg.com/queue/-/queue-6.0.2.tgz#b91525283e2315c7553d2efa18d83e76432fed65"
- integrity sha512-iHZWu+q3IdFZFX36ro/lKBkSvfkztY5Y7HMiPlOUjhupPcG2JMfst2KKEpu5XndviX/3UhFbRngUPNKtgvtZiA==
- dependencies:
- inherits "~2.0.3"
-
-randombytes@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/randombytes/-/randombytes-2.1.0.tgz#df6f84372f0270dc65cdf6291349ab7a473d4f2a"
- integrity sha512-vYl3iOX+4CKUWuxGi9Ukhie6fsqXqS9FE2Zaic4tNFD2N2QQaXOMFbuKK4QmDHC0JO6B1Zp41J0LpT0oR68amQ==
- dependencies:
- safe-buffer "^5.1.0"
-
-range-parser@1.2.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/range-parser/-/range-parser-1.2.0.tgz#f49be6b487894ddc40dcc94a322f611092e00d5e"
- integrity sha512-kA5WQoNVo4t9lNx2kQNFCxKeBl5IbbSNBl1M/tLkw9WCn+hxNBAW5Qh8gdhs63CJnhjJ2zQWFoqPJP2sK1AV5A==
-
-range-parser@^1.2.1, range-parser@~1.2.1:
- version "1.2.1"
- resolved "https://registry.yarnpkg.com/range-parser/-/range-parser-1.2.1.tgz#3cf37023d199e1c24d1a55b84800c2f3e6468031"
- integrity sha512-Hrgsx+orqoygnmhFbKaHE6c296J+HTAQXoxEF6gNupROmmGJRoyzfG3ccAveqCBrwr/2yxQ5BVd/GTl5agOwSg==
-
-raw-body@2.5.1:
- version "2.5.1"
- resolved "https://registry.yarnpkg.com/raw-body/-/raw-body-2.5.1.tgz#fe1b1628b181b700215e5fd42389f98b71392857"
- integrity sha512-qqJBtEyVgS0ZmPGdCFPWJ3FreoqvG4MVQln/kCgF7Olq95IbOp0/BWyMwbdtn4VTvkM8Y7khCQ2Xgk/tcrCXig==
- dependencies:
- bytes "3.1.2"
- http-errors "2.0.0"
- iconv-lite "0.4.24"
- unpipe "1.0.0"
-
-rc@1.2.8, rc@^1.2.8:
- version "1.2.8"
- resolved "https://registry.yarnpkg.com/rc/-/rc-1.2.8.tgz#cd924bf5200a075b83c188cd6b9e211b7fc0d3ed"
- integrity sha512-y3bGgqKj3QBdxLbLkomlohkvsA8gdAiUQlSBJnBhfn+BPxg4bc62d8TcBW15wavDfgexCgccckhcZvywyQYPOw==
- dependencies:
- deep-extend "^0.6.0"
- ini "~1.3.0"
- minimist "^1.2.0"
- strip-json-comments "~2.0.1"
-
-react-base16-styling@^0.6.0:
- version "0.6.0"
- resolved "https://registry.yarnpkg.com/react-base16-styling/-/react-base16-styling-0.6.0.tgz#ef2156d66cf4139695c8a167886cb69ea660792c"
- integrity sha512-yvh/7CArceR/jNATXOKDlvTnPKPmGZz7zsenQ3jUwLzHkNUR0CvY3yGYJbWJ/nnxsL8Sgmt5cO3/SILVuPO6TQ==
- dependencies:
- base16 "^1.0.0"
- lodash.curry "^4.0.1"
- lodash.flow "^3.3.0"
- pure-color "^1.2.0"
-
-react-dev-utils@^12.0.1:
- version "12.0.1"
- resolved "https://registry.yarnpkg.com/react-dev-utils/-/react-dev-utils-12.0.1.tgz#ba92edb4a1f379bd46ccd6bcd4e7bc398df33e73"
- integrity sha512-84Ivxmr17KjUupyqzFode6xKhjwuEJDROWKJy/BthkL7Wn6NJ8h4WE6k/exAv6ImS+0oZLRRW5j/aINMHyeGeQ==
- dependencies:
- "@babel/code-frame" "^7.16.0"
- address "^1.1.2"
- browserslist "^4.18.1"
- chalk "^4.1.2"
- cross-spawn "^7.0.3"
- detect-port-alt "^1.1.6"
- escape-string-regexp "^4.0.0"
- filesize "^8.0.6"
- find-up "^5.0.0"
- fork-ts-checker-webpack-plugin "^6.5.0"
- global-modules "^2.0.0"
- globby "^11.0.4"
- gzip-size "^6.0.0"
- immer "^9.0.7"
- is-root "^2.1.0"
- loader-utils "^3.2.0"
- open "^8.4.0"
- pkg-up "^3.1.0"
- prompts "^2.4.2"
- react-error-overlay "^6.0.11"
- recursive-readdir "^2.2.2"
- shell-quote "^1.7.3"
- strip-ansi "^6.0.1"
- text-table "^0.2.0"
-
-react-dom@^17.0.2:
- version "17.0.2"
- resolved "https://registry.yarnpkg.com/react-dom/-/react-dom-17.0.2.tgz#ecffb6845e3ad8dbfcdc498f0d0a939736502c23"
- integrity sha512-s4h96KtLDUQlsENhMn1ar8t2bEa+q/YAtj8pPPdIjPDGBDIVNsrD9aXNWqspUe6AzKCIG0C1HZZLqLV7qpOBGA==
- dependencies:
- loose-envify "^1.1.0"
- object-assign "^4.1.1"
- scheduler "^0.20.2"
-
-react-error-overlay@^6.0.11:
- version "6.0.11"
- resolved "https://registry.yarnpkg.com/react-error-overlay/-/react-error-overlay-6.0.11.tgz#92835de5841c5cf08ba00ddd2d677b6d17ff9adb"
- integrity sha512-/6UZ2qgEyH2aqzYZgQPxEnz33NJ2gNsnHA2o5+o4wW9bLM/JYQitNP9xPhsXwC08hMMovfGe/8retsdDsczPRg==
-
-react-fast-compare@^3.2.0:
- version "3.2.0"
- resolved "https://registry.yarnpkg.com/react-fast-compare/-/react-fast-compare-3.2.0.tgz#641a9da81b6a6320f270e89724fb45a0b39e43bb"
- integrity sha512-rtGImPZ0YyLrscKI9xTpV8psd6I8VAtjKCzQDlzyDvqJA8XOW78TXYQwNRNd8g8JZnDu8q9Fu/1v4HPAVwVdHA==
-
-react-helmet-async@*, react-helmet-async@^1.3.0:
- version "1.3.0"
- resolved "https://registry.yarnpkg.com/react-helmet-async/-/react-helmet-async-1.3.0.tgz#7bd5bf8c5c69ea9f02f6083f14ce33ef545c222e"
- integrity sha512-9jZ57/dAn9t3q6hneQS0wukqC2ENOBgMNVEhb/ZG9ZSxUetzVIw4iAmEU38IaVg3QGYauQPhSeUTuIUtFglWpg==
- dependencies:
- "@babel/runtime" "^7.12.5"
- invariant "^2.2.4"
- prop-types "^15.7.2"
- react-fast-compare "^3.2.0"
- shallowequal "^1.1.0"
-
-react-is@^16.13.1, react-is@^16.6.0, react-is@^16.7.0:
- version "16.13.1"
- resolved "https://registry.yarnpkg.com/react-is/-/react-is-16.13.1.tgz#789729a4dc36de2999dc156dd6c1d9c18cea56a4"
- integrity sha512-24e6ynE2H+OKt4kqsOvNd8kBpV65zoxbA4BVsEOB3ARVWQki/DHzaUoC5KuON/BiccDaCCTZBuOcfZs70kR8bQ==
-
-react-json-view@^1.21.3:
- version "1.21.3"
- resolved "https://registry.yarnpkg.com/react-json-view/-/react-json-view-1.21.3.tgz#f184209ee8f1bf374fb0c41b0813cff54549c475"
- integrity sha512-13p8IREj9/x/Ye4WI/JpjhoIwuzEgUAtgJZNBJckfzJt1qyh24BdTm6UQNGnyTq9dapQdrqvquZTo3dz1X6Cjw==
- dependencies:
- flux "^4.0.1"
- react-base16-styling "^0.6.0"
- react-lifecycles-compat "^3.0.4"
- react-textarea-autosize "^8.3.2"
-
-react-lifecycles-compat@^3.0.4:
- version "3.0.4"
- resolved "https://registry.yarnpkg.com/react-lifecycles-compat/-/react-lifecycles-compat-3.0.4.tgz#4f1a273afdfc8f3488a8c516bfda78f872352362"
- integrity sha512-fBASbA6LnOU9dOU2eW7aQ8xmYBSXUIWr+UmF9b1efZBazGNO+rcXT/icdKnYm2pTwcRylVUYwW7H1PHfLekVzA==
-
-react-loadable-ssr-addon-v5-slorber@^1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/react-loadable-ssr-addon-v5-slorber/-/react-loadable-ssr-addon-v5-slorber-1.0.1.tgz#2cdc91e8a744ffdf9e3556caabeb6e4278689883"
- integrity sha512-lq3Lyw1lGku8zUEJPDxsNm1AfYHBrO9Y1+olAYwpUJ2IGFBskM0DMKok97A6LWUpHm+o7IvQBOWu9MLenp9Z+A==
- dependencies:
- "@babel/runtime" "^7.10.3"
-
-react-router-config@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/react-router-config/-/react-router-config-5.1.1.tgz#0f4263d1a80c6b2dc7b9c1902c9526478194a988"
- integrity sha512-DuanZjaD8mQp1ppHjgnnUnyOlqYXZVjnov/JzFhjLEwd3Z4dYjMSnqrEzzGThH47vpCOqPPwJM2FtthLeJ8Pbg==
- dependencies:
- "@babel/runtime" "^7.1.2"
-
-react-router-dom@^5.3.3:
- version "5.3.4"
- resolved "https://registry.yarnpkg.com/react-router-dom/-/react-router-dom-5.3.4.tgz#2ed62ffd88cae6db134445f4a0c0ae8b91d2e5e6"
- integrity sha512-m4EqFMHv/Ih4kpcBCONHbkT68KoAeHN4p3lAGoNryfHi0dMy0kCzEZakiKRsvg5wHZ/JLrLW8o8KomWiz/qbYQ==
- dependencies:
- "@babel/runtime" "^7.12.13"
- history "^4.9.0"
- loose-envify "^1.3.1"
- prop-types "^15.6.2"
- react-router "5.3.4"
- tiny-invariant "^1.0.2"
- tiny-warning "^1.0.0"
-
-react-router@5.3.4, react-router@^5.3.3:
- version "5.3.4"
- resolved "https://registry.yarnpkg.com/react-router/-/react-router-5.3.4.tgz#8ca252d70fcc37841e31473c7a151cf777887bb5"
- integrity sha512-Ys9K+ppnJah3QuaRiLxk+jDWOR1MekYQrlytiXxC1RyfbdsZkS5pvKAzCCr031xHixZwpnsYNT5xysdFHQaYsA==
- dependencies:
- "@babel/runtime" "^7.12.13"
- history "^4.9.0"
- hoist-non-react-statics "^3.1.0"
- loose-envify "^1.3.1"
- path-to-regexp "^1.7.0"
- prop-types "^15.6.2"
- react-is "^16.6.0"
- tiny-invariant "^1.0.2"
- tiny-warning "^1.0.0"
-
-react-textarea-autosize@^8.3.2:
- version "8.4.0"
- resolved "https://registry.yarnpkg.com/react-textarea-autosize/-/react-textarea-autosize-8.4.0.tgz#4d0244d6a50caa897806b8c44abc0540a69bfc8c"
- integrity sha512-YrTFaEHLgJsi8sJVYHBzYn+mkP3prGkmP2DKb/tm0t7CLJY5t1Rxix8070LAKb0wby7bl/lf2EeHkuMihMZMwQ==
- dependencies:
- "@babel/runtime" "^7.10.2"
- use-composed-ref "^1.3.0"
- use-latest "^1.2.1"
-
-react@^17.0.2:
- version "17.0.2"
- resolved "https://registry.yarnpkg.com/react/-/react-17.0.2.tgz#d0b5cc516d29eb3eee383f75b62864cfb6800037"
- integrity sha512-gnhPt75i/dq/z3/6q/0asP78D0u592D5L1pd7M8P+dck6Fu/jJeL6iVVK23fptSUZj8Vjf++7wXA8UNclGQcbA==
- dependencies:
- loose-envify "^1.1.0"
- object-assign "^4.1.1"
-
-read-package-json-fast@^3.0.0, read-package-json-fast@^3.0.2:
- version "3.0.2"
- resolved "https://registry.yarnpkg.com/read-package-json-fast/-/read-package-json-fast-3.0.2.tgz#394908a9725dc7a5f14e70c8e7556dff1d2b1049"
- integrity sha512-0J+Msgym3vrLOUB3hzQCuZHII0xkNGCtz/HJH9xZshwv9DbDwkw1KaE3gx/e2J5rpEY5rtOy6cyhKOPrkP7FZw==
- dependencies:
- json-parse-even-better-errors "^3.0.0"
- npm-normalize-package-bin "^3.0.0"
-
-readable-stream@^2.0.1:
- version "2.3.7"
- resolved "https://registry.yarnpkg.com/readable-stream/-/readable-stream-2.3.7.tgz#1eca1cf711aef814c04f62252a36a62f6cb23b57"
- integrity sha512-Ebho8K4jIbHAxnuxi7o42OrZgF/ZTNcsZj6nRKyUmkhLFq8CHItp/fy6hQZuZmP/n3yZ9VBUbp4zz/mX8hmYPw==
- dependencies:
- core-util-is "~1.0.0"
- inherits "~2.0.3"
- isarray "~1.0.0"
- process-nextick-args "~2.0.0"
- safe-buffer "~5.1.1"
- string_decoder "~1.1.1"
- util-deprecate "~1.0.1"
-
-readable-stream@^3.0.2, readable-stream@^3.0.6:
- version "3.6.0"
- resolved "https://registry.yarnpkg.com/readable-stream/-/readable-stream-3.6.0.tgz#337bbda3adc0706bd3e024426a286d4b4b2c9198"
- integrity sha512-BViHy7LKeTz4oNnkcLJ+lVSL6vpiFeX6/d3oSH8zCW7UxP2onchk+vTGB143xuFjHS3deTgkKoXXymXqymiIdA==
- dependencies:
- inherits "^2.0.3"
- string_decoder "^1.1.1"
- util-deprecate "^1.0.1"
-
-readdirp@~3.6.0:
- version "3.6.0"
- resolved "https://registry.yarnpkg.com/readdirp/-/readdirp-3.6.0.tgz#74a370bd857116e245b29cc97340cd431a02a6c7"
- integrity sha512-hOS089on8RduqdbhvQ5Z37A0ESjsqz6qnRcffsMU3495FuTdqSm+7bhJ29JvIOsBDEEnan5DPu9t3To9VRlMzA==
- dependencies:
- picomatch "^2.2.1"
-
-reading-time@^1.5.0:
- version "1.5.0"
- resolved "https://registry.yarnpkg.com/reading-time/-/reading-time-1.5.0.tgz#d2a7f1b6057cb2e169beaf87113cc3411b5bc5bb"
- integrity sha512-onYyVhBNr4CmAxFsKS7bz+uTLRakypIe4R+5A824vBSkQy/hB3fZepoVEf8OVAxzLvK+H/jm9TzpI3ETSm64Kg==
-
-rechoir@^0.6.2:
- version "0.6.2"
- resolved "https://registry.yarnpkg.com/rechoir/-/rechoir-0.6.2.tgz#85204b54dba82d5742e28c96756ef43af50e3384"
- integrity sha512-HFM8rkZ+i3zrV+4LQjwQ0W+ez98pApMGM3HUrN04j3CqzPOzl9nmP15Y8YXNm8QHGv/eacOVEjqhmWpkRV0NAw==
- dependencies:
- resolve "^1.1.6"
-
-recursive-readdir@^2.2.2:
- version "2.2.3"
- resolved "https://registry.yarnpkg.com/recursive-readdir/-/recursive-readdir-2.2.3.tgz#e726f328c0d69153bcabd5c322d3195252379372"
- integrity sha512-8HrF5ZsXk5FAH9dgsx3BlUer73nIhuj+9OrQwEbLTPOBzGkL1lsFCR01am+v+0m2Cmbs1nP12hLDl5FA7EszKA==
- dependencies:
- minimatch "^3.0.5"
-
-regenerate-unicode-properties@^10.1.0:
- version "10.1.0"
- resolved "https://registry.yarnpkg.com/regenerate-unicode-properties/-/regenerate-unicode-properties-10.1.0.tgz#7c3192cab6dd24e21cb4461e5ddd7dd24fa8374c"
- integrity sha512-d1VudCLoIGitcU/hEg2QqvyGZQmdC0Lf8BqdOMXGFSvJP4bNV1+XqbPQeHHLD51Jh4QJJ225dlIFvY4Ly6MXmQ==
- dependencies:
- regenerate "^1.4.2"
-
-regenerate@^1.4.2:
- version "1.4.2"
- resolved "https://registry.yarnpkg.com/regenerate/-/regenerate-1.4.2.tgz#b9346d8827e8f5a32f7ba29637d398b69014848a"
- integrity sha512-zrceR/XhGYU/d/opr2EKO7aRHUeiBI8qjtfHqADTwZd6Szfy16la6kqD0MIUs5z5hx6AaKa+PixpPrR289+I0A==
-
-regenerator-runtime@^0.13.11:
- version "0.13.11"
- resolved "https://registry.yarnpkg.com/regenerator-runtime/-/regenerator-runtime-0.13.11.tgz#f6dca3e7ceec20590d07ada785636a90cdca17f9"
- integrity sha512-kY1AZVr2Ra+t+piVaJ4gxaFaReZVH40AKNo7UCX6W+dEwBo/2oZJzqfuN1qLq1oL45o56cPaTXELwrTh8Fpggg==
-
-regenerator-transform@^0.15.1:
- version "0.15.1"
- resolved "https://registry.yarnpkg.com/regenerator-transform/-/regenerator-transform-0.15.1.tgz#f6c4e99fc1b4591f780db2586328e4d9a9d8dc56"
- integrity sha512-knzmNAcuyxV+gQCufkYcvOqX/qIIfHLv0u5x79kRxuGojfYVky1f15TzZEu2Avte8QGepvUNTnLskf8E6X6Vyg==
- dependencies:
- "@babel/runtime" "^7.8.4"
-
-regexpu-core@^5.2.1:
- version "5.3.0"
- resolved "https://registry.yarnpkg.com/regexpu-core/-/regexpu-core-5.3.0.tgz#4d0d044b76fedbad6238703ae84bfdedee2cf074"
- integrity sha512-ZdhUQlng0RoscyW7jADnUZ25F5eVtHdMyXSb2PiwafvteRAOJUjFoUPEYZSIfP99fBIs3maLIRfpEddT78wAAQ==
- dependencies:
- "@babel/regjsgen" "^0.8.0"
- regenerate "^1.4.2"
- regenerate-unicode-properties "^10.1.0"
- regjsparser "^0.9.1"
- unicode-match-property-ecmascript "^2.0.0"
- unicode-match-property-value-ecmascript "^2.1.0"
-
-registry-auth-token@^4.0.0:
- version "4.2.2"
- resolved "https://registry.yarnpkg.com/registry-auth-token/-/registry-auth-token-4.2.2.tgz#f02d49c3668884612ca031419491a13539e21fac"
- integrity sha512-PC5ZysNb42zpFME6D/XlIgtNGdTl8bBOCw90xQLVMpzuuubJKYDWFAEuUNc+Cn8Z8724tg2SDhDRrkVEsqfDMg==
- dependencies:
- rc "1.2.8"
-
-registry-url@^5.0.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/registry-url/-/registry-url-5.1.0.tgz#e98334b50d5434b81136b44ec638d9c2009c5009"
- integrity sha512-8acYXXTI0AkQv6RAOjE3vOaIXZkT9wo4LOFbBKYQEEnnMNBpKqdUrI6S4NT0KPIo/WVvJ5tE/X5LF/TQUf0ekw==
- dependencies:
- rc "^1.2.8"
-
-regjsparser@^0.9.1:
- version "0.9.1"
- resolved "https://registry.yarnpkg.com/regjsparser/-/regjsparser-0.9.1.tgz#272d05aa10c7c1f67095b1ff0addae8442fc5709"
- integrity sha512-dQUtn90WanSNl+7mQKcXAgZxvUe7Z0SqXlgzv0za4LwiUhyzBC58yQO3liFoUgu8GiJVInAhJjkj1N0EtQ5nkQ==
- dependencies:
- jsesc "~0.5.0"
-
-relateurl@^0.2.7:
- version "0.2.7"
- resolved "https://registry.yarnpkg.com/relateurl/-/relateurl-0.2.7.tgz#54dbf377e51440aca90a4cd274600d3ff2d888a9"
- integrity sha512-G08Dxvm4iDN3MLM0EsP62EDV9IuhXPR6blNz6Utcp7zyV3tr4HVNINt6MpaRWbxoOHT3Q7YN2P+jaHX8vUbgog==
-
-remark-cli@^11.0.0:
- version "11.0.0"
- resolved "https://registry.yarnpkg.com/remark-cli/-/remark-cli-11.0.0.tgz#302c15c5e73c0b422a6709f65adb74cac3b5eb53"
- integrity sha512-8JEWwArXquRq1/In4Ftz7gSG9Scwb1ijT2/dEuBETW9omqhmMRxcfjZ3iKqrak3BnCJeZSXCdWEmPhFKC8+RUQ==
- dependencies:
- remark "^14.0.0"
- unified-args "^10.0.0"
-
-remark-emoji@^2.2.0:
- version "2.2.0"
- resolved "https://registry.yarnpkg.com/remark-emoji/-/remark-emoji-2.2.0.tgz#1c702090a1525da5b80e15a8f963ef2c8236cac7"
- integrity sha512-P3cj9s5ggsUvWw5fS2uzCHJMGuXYRb0NnZqYlNecewXt8QBU9n5vW3DUUKOhepS8F9CwdMx9B8a3i7pqFWAI5w==
- dependencies:
- emoticon "^3.2.0"
- node-emoji "^1.10.0"
- unist-util-visit "^2.0.3"
-
-remark-footnotes@2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/remark-footnotes/-/remark-footnotes-2.0.0.tgz#9001c4c2ffebba55695d2dd80ffb8b82f7e6303f"
- integrity sha512-3Clt8ZMH75Ayjp9q4CorNeyjwIxHFcTkaektplKGl2A1jNGEUey8cKL0ZC5vJwfcD5GFGsNLImLG/NGzWIzoMQ==
-
-remark-lint-blockquote-indentation@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-blockquote-indentation/-/remark-lint-blockquote-indentation-3.1.1.tgz#756c099efd43a125f04df329bfe84398358758b6"
- integrity sha512-u9cjedM6zcK8vRicis5n/xeOSDIC3FGBCKc3K9pqw+nNrOjY85FwxDQKZZ/kx7rmkdRZEhgyHak+wzPBllcxBQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- pluralize "^8.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-checkbox-character-style@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-checkbox-character-style/-/remark-lint-checkbox-character-style-4.1.1.tgz#8d42edf52e7b359cf76ff7a6ba344dc70c933025"
- integrity sha512-KPSW3wfHfB8m9hzrtHiBHCTUIsOPX5nZR7VM+2pMjwqnhI6Mp94DKprkNo1ekNZALNeoZIDWZUSYxSiiwFfmVQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-code-block-style@^3.0.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/remark-lint-code-block-style/-/remark-lint-code-block-style-3.1.0.tgz#5a2d122d01f9175e762f81a144fc18e1a91a104c"
- integrity sha512-Hv4YQ8ueLGpjItla4CkcOkcfGj+nlquqylDgCm1/xKnW+Ke2a4qVTMVJrP9Krp4FWmXgktJLDHjhRH+pzhDXLg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-definition-case@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-definition-case/-/remark-lint-definition-case-3.1.1.tgz#583483e783d43b4b5e110864584dce48f23a4386"
- integrity sha512-dirX0BSfbm1Ixx4Hv4xRQliEP1rw8dDitw2Om3XcO2QqF8bWrzF06/xeMlDNAaT77Cxqb9S7bODo/q+CYUxyWQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-definition-spacing@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-definition-spacing/-/remark-lint-definition-spacing-3.1.1.tgz#403cb3a486cbc2cb703358e78115507f6ee1fc2b"
- integrity sha512-PR+cYvc0FMtFWjkaXePysW88r7Y7eIwbpUGPFDIWE48fiRiz8U3VIk05P3loQCpCkbmUeInAAYD8tIFPTg4Jlg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-emphasis-marker@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-emphasis-marker/-/remark-lint-emphasis-marker-3.1.1.tgz#3f3336ba4be97b8296eb1019338237d61b4e3db8"
- integrity sha512-VduuT+KAr0vA78xBLJdIcenCQja4mAd81aNACfdz7BUPLphIQa84D5uzl+nZatSaCXLebCNp5jP/bzVUsBmRKw==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-fenced-code-flag@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-fenced-code-flag/-/remark-lint-fenced-code-flag-3.1.1.tgz#b1fccd801a79c302543302dd3041fa325d1bd727"
- integrity sha512-FFVZmYsBccKIIEgOtgdZEpQdARtAat1LTLBydnIpyNIvcntzWwtrtlj9mtjL8ZoSRre8HtwmEnBFyOfmM/NWaA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-fenced-code-marker@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-fenced-code-marker/-/remark-lint-fenced-code-marker-3.1.1.tgz#ee977552bd130f1f1305301f97160d31ff6b7461"
- integrity sha512-x/t8sJWPvE46knKz6zW03j9VX5477srHUmRFbnXhZ3K8e37cYVUIvfbPhcPCAosSsOki9+dvGfZsWQiKuUNNfQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-file-extension@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-file-extension/-/remark-lint-file-extension-2.1.1.tgz#780ef3c3a2e5713a44f82f24eb45e075ce9ba428"
- integrity sha512-r6OMe27YZzr2NFjPMbBxgm8RZxigRwzeFSjapPlqcxk0Q0w/6sosJsceBNlGGlk00pltvv7NPqSexbXUjirrQQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-final-definition@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-final-definition/-/remark-lint-final-definition-3.1.1.tgz#c1077176e41b675302abf5057a82d7d5602df149"
- integrity sha512-94hRV+EBIuLVFooiimsZwh5ZPEcTqjy5wr7LgqxoUUWy+srTanndaLoki7bxQJeIcWUnomZncsJAyL0Lo7toxw==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-final-newline@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-final-newline/-/remark-lint-final-newline-2.1.1.tgz#dac4e5ae92638808fb6e2de6164c43890f1248a5"
- integrity sha512-cgKYaI7ujUse/kV4KajLv2j1kmi1CxpAu+w7wIU0/Faihhb3sZAf4a5ACf2Wu8NoTSIr1Q//3hDysG507PIoDg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-hard-break-spaces@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-hard-break-spaces/-/remark-lint-hard-break-spaces-3.1.1.tgz#daaa6fbc9d08a0501dc6e3d4a844dc4783bdfaea"
- integrity sha512-UfwFvESpX32qwyHJeluuUuRPWmxJDTkmjnWv2r49G9fC4Jrzm4crdJMs3sWsrGiQ3mSex6bgp/8rqDgtBng2IA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-heading-increment@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-heading-increment/-/remark-lint-heading-increment-3.1.1.tgz#d12c9c1965e9eb44f090202d5d808a144c8ee884"
- integrity sha512-DtiMwZNAE/iAZWuZGjTXxYjNDQ375r59C99aVeVp1nKaovIufKuHWAm9U/9FAGBJNgBx6Ovfdej4YwIxd0yAPw==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-heading-style@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-heading-style/-/remark-lint-heading-style-3.1.1.tgz#19e321db9dc6c697f3ef8bf514a8b15323422776"
- integrity sha512-Qm7ZAF+s46ns0Wo5TlHGIn/PPMMynytn8SSLEdMIo6Uo/+8PAcmQ3zU1pj57KYxfyDoN5iQPgPIwPYMLYQ2TSQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-heading-style "^2.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-link-title-style@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-link-title-style/-/remark-lint-link-title-style-3.1.1.tgz#eb1a773816b4bee43170745245e9fed776633a7d"
- integrity sha512-JWWiuUFy/N2iwQ3eWIxFy6olX8D7xCFw8LoM0vZI2CHTZJrmDMaWwnl8jziP+HHHheFX3wkVqsoaYod536ArRw==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
- vfile-location "^4.0.0"
-
-remark-lint-list-item-bullet-indent@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-list-item-bullet-indent/-/remark-lint-list-item-bullet-indent-4.1.1.tgz#1ff4498b680bb4a8ce94a4192a1b52eca4c9fe48"
- integrity sha512-NFvXVj1Nm12+Ma48NOjZCGb/D0IhmUcxyrTCpPp+UNJhEWrmFxM8nSyIiZgXadgXErnuv+xm2Atw7TAcZ9a1Cg==
- dependencies:
- "@types/mdast" "^3.0.0"
- pluralize "^8.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-list-item-content-indent@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-list-item-content-indent/-/remark-lint-list-item-content-indent-3.1.1.tgz#9fff6bf4e1a08e86d99430838b822b8209dca15e"
- integrity sha512-gcZhAXLd1onkutTEqQTybyANjdxvlOlu0y/AU4H3f6L99UGC85ymRhEeu5vGSkvsKKPR1FrMTEH6G2nNgtavgg==
- dependencies:
- "@types/mdast" "^3.0.0"
- pluralize "^8.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-list-item-indent@^3.0.0, remark-lint-list-item-indent@^3.1.1:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-list-item-indent/-/remark-lint-list-item-indent-3.1.1.tgz#1591d291a9f81c8f14219bdb63f226a5e9f271c3"
- integrity sha512-OSTG64e52v8XBmmeT0lefpiAfCMYHJxMMUrMnhTjLVyWAbEO0vqqR5bLvfLwzK+P4nY2D/8XKku0hw35dM86Rw==
- dependencies:
- "@types/mdast" "^3.0.0"
- pluralize "^8.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-list-item-spacing@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-list-item-spacing/-/remark-lint-list-item-spacing-4.1.1.tgz#93473e79965c3f21c0dc8830b18be790033485fd"
- integrity sha512-MqXmahPgYrvfA7SPqmcAC6fI40jIgXG33EeE/MhFvMLWh04k+fqGf2O2aH1KT664MlwM4oETbTI4xj3/KCIHZA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-maximum-heading-length@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-maximum-heading-length/-/remark-lint-maximum-heading-length-3.1.1.tgz#dd90ef7f18ff20789f9c533e2bdbcd4b4d92a7cd"
- integrity sha512-hTOvRDnULpu0S+k51lovT28TLBgtw8XR0qq+mECSsoyuT4C38UBjQRic5OPo68AZMH0ad/93uj6yvfFtH0K8Lg==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-to-string "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-maximum-line-length@^3.0.0:
- version "3.1.2"
- resolved "https://registry.yarnpkg.com/remark-lint-maximum-line-length/-/remark-lint-maximum-line-length-3.1.2.tgz#4c5c499279c80938878194d4e52102525b7a9e1b"
- integrity sha512-KwddpVmNifTHNXwTQQgVufuUvv0hhu9kJVvmpNdEvfEc7tc3wBkaavyi3kKsUB8WwMhGtZuXVWy6OdPC1axzhw==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-blockquote-without-marker@^5.0.0:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-blockquote-without-marker/-/remark-lint-no-blockquote-without-marker-5.1.1.tgz#e07233866a742c41368886663d7caebbdebb1074"
- integrity sha512-7jL7eKS25kKRhQ7SKKB5eRfNleDMWKWAmZ5Y/votJdDoM+6qsopLLumPWaSzP0onyV3dyHRhPfBtqelt3hvcyA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
- vfile-location "^4.0.0"
-
-remark-lint-no-consecutive-blank-lines@^4.0.0:
- version "4.1.2"
- resolved "https://registry.yarnpkg.com/remark-lint-no-consecutive-blank-lines/-/remark-lint-no-consecutive-blank-lines-4.1.2.tgz#77d5c433830c306898deefbab370c0c5732ff99a"
- integrity sha512-wRsR3kFgHaZ4mO3KASU43oXGLGezNZ64yNs1ChPUacKh0Bm7cwGnxN9GHGAbOXspwrYrN2eCDxzCbdPEZi2qKw==
- dependencies:
- "@types/mdast" "^3.0.0"
- "@types/unist" "^2.0.0"
- pluralize "^8.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-duplicate-definitions@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-duplicate-definitions/-/remark-lint-no-duplicate-definitions-3.1.1.tgz#2f5042b8d2274d94a9423767c6e714b57c6a2dbf"
- integrity sha512-9p+nBz8VvV+t4g/ALNLVN8naV+ffAzC4ADyg9QivzmKwLjyF93Avt4HYNlb2GZ+aoXRQSVG1wjjWFeDC9c7Tdg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-stringify-position "^3.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-duplicate-headings@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-duplicate-headings/-/remark-lint-no-duplicate-headings-3.1.1.tgz#5cee9867b01e296dda7940a7c2546cb43f2be523"
- integrity sha512-gSO/BngGkxF35Fsctzt3YMwGEZ8F7f71zx7h0Y97DylyL6WXVuWP4saCmQTlbB4FpD0UXEnRROJ6fBFDvJlzOA==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-to-string "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-stringify-position "^3.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-emphasis-as-heading@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-emphasis-as-heading/-/remark-lint-no-emphasis-as-heading-3.1.1.tgz#8279e3905fbc5117f195a65396ce50d08648d611"
- integrity sha512-F45yuLsYVP4r6OjVtePKk7Aymnf3rBLHXYjnSJggEaYn0j+72xOBLrqmj6ii5YGfDsBwG2pDNTBx4vm3xM7P0Q==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-file-name-articles@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-file-name-articles/-/remark-lint-no-file-name-articles-2.1.1.tgz#9a202242fae3d9f6d7037bb71821659887ee84a4"
- integrity sha512-7fiHKQUGvP4WOsieZ1dxm8WQWWjXjPj0Uix6pk2dSTJqxvaosjKH1AV0J/eVvliat0BGH8Cz4SUbuz5vG6YbdQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-no-file-name-consecutive-dashes@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-file-name-consecutive-dashes/-/remark-lint-no-file-name-consecutive-dashes-2.1.1.tgz#d0d36ae694a486a9d8a39d9f3823f11234ed45c2"
- integrity sha512-tM4IpURGuresyeIBsXT5jsY3lZakgO6IO59ixcFt015bFjTOW54MrBvdJxA60QHhf5DAyHzD8wGeULPSs7ZQfg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-no-file-name-irregular-characters@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-file-name-irregular-characters/-/remark-lint-no-file-name-irregular-characters-2.1.1.tgz#8f9dd0c22cf7ee5ca3860b949256e3eaf5baa5b0"
- integrity sha512-rVeCv1XRdLtp/rxLaiFKElaIHuIlokypV/c2aCG3VVYcQ4+ZmJxq018kEsolR2+Dv9m3vKp8Fy1482US4g4WKA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-no-file-name-mixed-case@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-file-name-mixed-case/-/remark-lint-no-file-name-mixed-case-2.1.1.tgz#adac709a0961609ba305b46dd01035b4fba4ae84"
- integrity sha512-mJU3hYzyXNo8NkoSafPcsgr+Gema+vDCzNWlLw05UdFXJK/cVy+6DVsbrEFjrz8L+WF7uQmUHBtTvd91SqoItg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-no-file-name-outer-dashes@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-file-name-outer-dashes/-/remark-lint-no-file-name-outer-dashes-2.1.1.tgz#d0956441d1df6fb0a04a0efd375a739729fe5213"
- integrity sha512-2kRcVNzZb0zS3jE+Iaa6MEpplhqXSdsHBILS+BxJ4cDGAAIdeipY8hKaDLdZi+34wvrfnDxNgvNLcHpgqO+OZA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
-
-remark-lint-no-heading-content-indent@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-heading-content-indent/-/remark-lint-no-heading-content-indent-4.1.1.tgz#e4afb9872d12b29805c183999f5cb3adca9f394c"
- integrity sha512-W4zF7MA72IDC5JB0qzciwsnioL5XlnoE0r1F7sDS0I5CJfQtHYOLlxb3UAIlgRCkBokPWCp0E4o1fsY/gQUKVg==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-heading-style "^2.0.0"
- pluralize "^8.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-heading-punctuation@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-heading-punctuation/-/remark-lint-no-heading-punctuation-3.1.1.tgz#ba2159170778bfdec8947e1a71d1e152431cd9ce"
- integrity sha512-ZexHx4rmsjKVF1/Fvdig0yOgpWl0wFa43+sqg880HT3PW9KmEczjSRkwlMaTlVgDzC0paNn2FXfQMuEQW4YDLg==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-to-string "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-inline-padding@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-inline-padding/-/remark-lint-no-inline-padding-4.1.1.tgz#2f1dda78556f1f8a98b4cad52ff74f6a56b55c58"
- integrity sha512-++IMm6ohOPKNOrybqjP9eiclEtVX/Rd2HpF2UD9icrC1X5nvrI6tlfN55tePaFvWAB7pe6MW4LzNEMnWse61Lw==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-to-string "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-literal-urls@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-literal-urls/-/remark-lint-no-literal-urls-3.1.1.tgz#9e3b71c013ffa3d3a493c98b54c3d5bd0ea0ad23"
- integrity sha512-tZZ4gtZMA//ZAf7GJTE8S9yjzqXUfUTlR/lvU7ffc7NeSurqCBwAtHqeXVCHiD39JnlHVSW2MLYhvHp53lBGvA==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-to-string "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-multiple-toplevel-headings@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-multiple-toplevel-headings/-/remark-lint-no-multiple-toplevel-headings-3.1.1.tgz#0a0058b03e5d8c3539230a5987e0ef11edd987f2"
- integrity sha512-bM//SIBvIkoGUpA8hR5QibJ+7C2R50PTIRrc4te93YNRG+ie8bJzjwuO9jIMedoDfJB6/+7EqO9FYBivjBZ3MA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-stringify-position "^3.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-shell-dollars@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-shell-dollars/-/remark-lint-no-shell-dollars-3.1.1.tgz#27deee278650d72bca795788e195927f03059f9d"
- integrity sha512-Q3Ad1TaOPxbYog5+Of/quPG3Fy+dMKiHjT8KsU7NDiHG6YJOnAJ3f3w+y13CIlNIaKc/MrisgcthhrZ7NsgXfA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-shortcut-reference-image@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-shortcut-reference-image/-/remark-lint-no-shortcut-reference-image-3.1.1.tgz#3714f31e98ca2063c43bb4cc4d7206e0581da501"
- integrity sha512-m8tH+loDagd1JUns/T4eyulVXgVvE+ZSs7owRUOmP+dgsKJuO5sl1AdN9eyKDVMEvxHF3Pm5WqE62QIRNM48mA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-shortcut-reference-link@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-shortcut-reference-link/-/remark-lint-no-shortcut-reference-link-3.1.1.tgz#b29bc4bfdb02b30a596b5fed235c99e470805130"
- integrity sha512-oDJ92/jXQ842HgrBGgZdP7FA+N2jBMCBU2+jRElkS+OWVut0UaDILtNavNy/e85B3SLPj3RoXKF96M4vfJ7B2A==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-no-table-indentation@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-table-indentation/-/remark-lint-no-table-indentation-4.1.1.tgz#985a0a1f7a533b58c9829db6579c7cac899e55e1"
- integrity sha512-eklvBxUSrkVbJxeokepOvFZ3n2V6zaJERIiOowR+y/Bz4dRHDMij1Ojg55AMO9yUMvxWPV3JPOeThliAcPmrMg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
- vfile-location "^4.0.0"
-
-remark-lint-no-undefined-references@^4.0.0:
- version "4.2.0"
- resolved "https://registry.yarnpkg.com/remark-lint-no-undefined-references/-/remark-lint-no-undefined-references-4.2.0.tgz#11a3e579b9107493d7781973dde8517793f52e0c"
- integrity sha512-EDV9B1ZXMLcKVtMQFvfvtbag4AkLcu8aUNGXoez5GJLcCAQ8Q+sG74yOtIW4xNVlVubEjl0vdkFhaKYLxvn2Sw==
- dependencies:
- "@types/mdast" "^3.0.0"
- micromark-util-normalize-identifier "^1.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
- vfile-location "^4.0.0"
-
-remark-lint-no-unused-definitions@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-no-unused-definitions/-/remark-lint-no-unused-definitions-3.1.1.tgz#584fcd0b1ad569d3e1933256e85b9fb308e88695"
- integrity sha512-/GtyBukhAxi5MEX/g/m+FzDEflSbTe2/cpe2H+tJZyDmiLhjGXRdwWnPRDp+mB9g1iIZgVRCk7T4v90RbQX/mw==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-ordered-list-marker-style@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-ordered-list-marker-style/-/remark-lint-ordered-list-marker-style-3.1.1.tgz#5431100f048ef44daa90a32251e8056f2de58449"
- integrity sha512-IWcWaJoaSb4yoSOuvDbj9B2uXp9kSj58DqtrMKo8MoRShmbj1onVfulTxoTLeLtI11NvW+mj3jPSpqjMjls+5Q==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-ordered-list-marker-value@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-ordered-list-marker-value/-/remark-lint-ordered-list-marker-value-3.1.1.tgz#fed1bafdaa8ada89d037e411e35d4c2b3f7cdda9"
- integrity sha512-+bQZbo+v/A8CuLrO71gobJuKR4/sfnPgWyEggSa+zq+LXPK1HiMDjap0Wr07uYgcUXsXIPh+HD/5J5by6JL+vg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-rule-style@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-rule-style/-/remark-lint-rule-style-3.1.1.tgz#163b4f394422496c065c95227970657a57c786cf"
- integrity sha512-+oZe0ph4DWHGwPkQ/FpqiGp4WULTXB1edftnnNbizYT+Wr+/ux7GNTx78oXH/PHwlnOtVIExMc4W/vDXrUj/DQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-strong-marker@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-strong-marker/-/remark-lint-strong-marker-3.1.1.tgz#4f77ba095cacbd8a8bcd7dd834dd792b50b1f3cb"
- integrity sha512-tX9Os2C48Hh8P8CouY4dcnAhGnR3trL+NCDqIvJvFDR9Rvm9yfNQaY2N4ZHWVY0iUicq9DpqEiJTgUsT8AGv/w==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-table-cell-padding@^4.0.0:
- version "4.1.2"
- resolved "https://registry.yarnpkg.com/remark-lint-table-cell-padding/-/remark-lint-table-cell-padding-4.1.2.tgz#a7087f4513523ca0473986a7a9348847d52e6dad"
- integrity sha512-cx5BXjHtpACa7Z51Vuqzy9BI4Z8Hnxz7vklhhrubkoB7mbctP/mR+Nh4B8eE5VtgFYJNHFwIltl96PuoctFCeQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- "@types/unist" "^2.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-table-pipe-alignment@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-table-pipe-alignment/-/remark-lint-table-pipe-alignment-3.1.1.tgz#dc9381f1b8437d3a96c3309ed8277ab003e84955"
- integrity sha512-WOHv2yL4ZwXHM06MIyQNnGFYKz9m2k/GFIA/6hpArF8Ph/3v8CF0J/Hb3Yyfg39e5nODw3D2G3okCO+xgyGQGA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-table-pipes@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-table-pipes/-/remark-lint-table-pipes-4.1.1.tgz#8a9badb0daed86d561db681c150966549eb8528d"
- integrity sha512-mJnB2FpjJTE4s9kE1JX8gcCjCFvtGPjzXUiQy0sbPHn2YM9EWG7kvFWYoqWK4w569CEQJyxZraEPltmhDjQTjg==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint-unordered-list-marker-style@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint-unordered-list-marker-style/-/remark-lint-unordered-list-marker-style-3.1.1.tgz#ad9a2aaa705bf3c1ec147f493c7b453ea612238f"
- integrity sha512-JwH8oIDi9f5Z8cTQLimhJ/fkbPwI3OpNSifjYyObNNuc4PG4/NUoe5ZuD10uPmPYHZW+713RZ8S5ucVCkI8dDA==
- dependencies:
- "@types/mdast" "^3.0.0"
- unified "^10.0.0"
- unified-lint-rule "^2.0.0"
- unist-util-generated "^2.0.0"
- unist-util-position "^4.0.0"
- unist-util-visit "^4.0.0"
-
-remark-lint@^9.0.0, remark-lint@^9.1.1:
- version "9.1.1"
- resolved "https://registry.yarnpkg.com/remark-lint/-/remark-lint-9.1.1.tgz#58c27adc4edeca93b7ce81e2861f05cbcecef72c"
- integrity sha512-zhe6twuqgkx/9KgZyNyaO0cceA4jQuJcyzMOBC+JZiAzMN6mFUmcssWZyY30ko8ut9vQDMX/pyQnolGn+Fg/Tw==
- dependencies:
- "@types/mdast" "^3.0.0"
- remark-message-control "^7.0.0"
- unified "^10.1.0"
-
-remark-mdx@1.6.22:
- version "1.6.22"
- resolved "https://registry.yarnpkg.com/remark-mdx/-/remark-mdx-1.6.22.tgz#06a8dab07dcfdd57f3373af7f86bd0e992108bbd"
- integrity sha512-phMHBJgeV76uyFkH4rvzCftLfKCr2RZuF+/gmVcaKrpsihyzmhXjA0BEMDaPTXG5y8qZOKPVo83NAOX01LPnOQ==
- dependencies:
- "@babel/core" "7.12.9"
- "@babel/helper-plugin-utils" "7.10.4"
- "@babel/plugin-proposal-object-rest-spread" "7.12.1"
- "@babel/plugin-syntax-jsx" "7.12.1"
- "@mdx-js/util" "1.6.22"
- is-alphabetical "1.0.4"
- remark-parse "8.0.3"
- unified "9.2.0"
-
-remark-mdx@^2.1.5:
- version "2.3.0"
- resolved "https://registry.yarnpkg.com/remark-mdx/-/remark-mdx-2.3.0.tgz#efe678025a8c2726681bde8bf111af4a93943db4"
- integrity sha512-g53hMkpM0I98MU266IzDFMrTD980gNF3BJnkyFcmN+dD873mQeD5rdMO3Y2X+x8umQfbSE0PcoEDl7ledSA+2g==
- dependencies:
- mdast-util-mdx "^2.0.0"
- micromark-extension-mdxjs "^1.0.0"
-
-remark-message-control@^7.0.0:
- version "7.1.1"
- resolved "https://registry.yarnpkg.com/remark-message-control/-/remark-message-control-7.1.1.tgz#71e9b757b835fad2ac14fafa8b432f51b9b9bf52"
- integrity sha512-xKRWl1NTBOKed0oEtCd8BUfH5m4s8WXxFFSoo7uUwx6GW/qdCy4zov5LfPyw7emantDmhfWn5PdIZgcbVcWMDQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-comment-marker "^2.0.0"
- unified "^10.0.0"
- unified-message-control "^4.0.0"
- vfile "^5.0.0"
-
-remark-parse@8.0.3:
- version "8.0.3"
- resolved "https://registry.yarnpkg.com/remark-parse/-/remark-parse-8.0.3.tgz#9c62aa3b35b79a486454c690472906075f40c7e1"
- integrity sha512-E1K9+QLGgggHxCQtLt++uXltxEprmWzNfg+MxpfHsZlrddKzZ/hZyWHDbK3/Ap8HJQqYJRXP+jHczdL6q6i85Q==
- dependencies:
- ccount "^1.0.0"
- collapse-white-space "^1.0.2"
- is-alphabetical "^1.0.0"
- is-decimal "^1.0.0"
- is-whitespace-character "^1.0.0"
- is-word-character "^1.0.0"
- markdown-escapes "^1.0.0"
- parse-entities "^2.0.0"
- repeat-string "^1.5.4"
- state-toggle "^1.0.0"
- trim "0.0.1"
- trim-trailing-lines "^1.0.0"
- unherit "^1.0.4"
- unist-util-remove-position "^2.0.0"
- vfile-location "^3.0.0"
- xtend "^4.0.1"
-
-remark-parse@^10.0.0:
- version "10.0.1"
- resolved "https://registry.yarnpkg.com/remark-parse/-/remark-parse-10.0.1.tgz#6f60ae53edbf0cf38ea223fe643db64d112e0775"
- integrity sha512-1fUyHr2jLsVOkhbvPRBJ5zTKZZyD6yZzYaWCS6BPBdQ8vEMBCH+9zNCDA6tET/zHCi/jLqjCWtlJZUPk+DbnFw==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-from-markdown "^1.0.0"
- unified "^10.0.0"
-
-remark-preset-lint-consistent@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/remark-preset-lint-consistent/-/remark-preset-lint-consistent-5.1.1.tgz#c870a2379e109cb6d7a10cd2d3b91f34e3f89e71"
- integrity sha512-DZQfomiVi/1x7NRByWrOiIC+olEGa1PpyykKrowvYp5qr/Seq60FqU7OjBJxtcOLzgnQcu9Y2JXdHxFi4AAPXQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- remark-lint "^9.0.0"
- remark-lint-blockquote-indentation "^3.0.0"
- remark-lint-checkbox-character-style "^4.0.0"
- remark-lint-code-block-style "^3.0.0"
- remark-lint-emphasis-marker "^3.0.0"
- remark-lint-fenced-code-marker "^3.0.0"
- remark-lint-heading-style "^3.0.0"
- remark-lint-link-title-style "^3.0.0"
- remark-lint-list-item-content-indent "^3.0.0"
- remark-lint-ordered-list-marker-style "^3.0.0"
- remark-lint-rule-style "^3.0.0"
- remark-lint-strong-marker "^3.0.0"
- remark-lint-table-cell-padding "^4.0.0"
- unified "^10.0.0"
-
-remark-preset-lint-markdown-style-guide@^5.1.2:
- version "5.1.2"
- resolved "https://registry.yarnpkg.com/remark-preset-lint-markdown-style-guide/-/remark-preset-lint-markdown-style-guide-5.1.2.tgz#877a837261df1f6c021557463aeda1e49506dd30"
- integrity sha512-MIAhnz0wDOq/MqLucSaAPquKGFE2I5SxqRjgWT+ZGK7TmqTxrro53e11/Pc19xPX4evmzI5CZdvaRnIoxP3ysQ==
- dependencies:
- "@types/mdast" "^3.0.0"
- remark-lint "^9.0.0"
- remark-lint-blockquote-indentation "^3.0.0"
- remark-lint-code-block-style "^3.0.0"
- remark-lint-definition-case "^3.0.0"
- remark-lint-definition-spacing "^3.0.0"
- remark-lint-emphasis-marker "^3.0.0"
- remark-lint-fenced-code-flag "^3.0.0"
- remark-lint-fenced-code-marker "^3.0.0"
- remark-lint-file-extension "^2.0.0"
- remark-lint-final-definition "^3.0.0"
- remark-lint-hard-break-spaces "^3.0.0"
- remark-lint-heading-increment "^3.0.0"
- remark-lint-heading-style "^3.0.0"
- remark-lint-link-title-style "^3.0.0"
- remark-lint-list-item-content-indent "^3.0.0"
- remark-lint-list-item-indent "^3.0.0"
- remark-lint-list-item-spacing "^4.0.0"
- remark-lint-maximum-heading-length "^3.0.0"
- remark-lint-maximum-line-length "^3.0.0"
- remark-lint-no-blockquote-without-marker "^5.0.0"
- remark-lint-no-consecutive-blank-lines "^4.0.0"
- remark-lint-no-duplicate-headings "^3.0.0"
- remark-lint-no-emphasis-as-heading "^3.0.0"
- remark-lint-no-file-name-articles "^2.0.0"
- remark-lint-no-file-name-consecutive-dashes "^2.0.0"
- remark-lint-no-file-name-irregular-characters "^2.0.0"
- remark-lint-no-file-name-mixed-case "^2.0.0"
- remark-lint-no-file-name-outer-dashes "^2.0.0"
- remark-lint-no-heading-punctuation "^3.0.0"
- remark-lint-no-inline-padding "^4.0.0"
- remark-lint-no-literal-urls "^3.0.0"
- remark-lint-no-multiple-toplevel-headings "^3.0.0"
- remark-lint-no-shell-dollars "^3.0.0"
- remark-lint-no-shortcut-reference-image "^3.0.0"
- remark-lint-no-shortcut-reference-link "^3.0.0"
- remark-lint-no-table-indentation "^4.0.0"
- remark-lint-ordered-list-marker-style "^3.0.0"
- remark-lint-ordered-list-marker-value "^3.0.0"
- remark-lint-rule-style "^3.0.0"
- remark-lint-strong-marker "^3.0.0"
- remark-lint-table-cell-padding "^4.0.0"
- remark-lint-table-pipe-alignment "^3.0.0"
- remark-lint-table-pipes "^4.0.0"
- remark-lint-unordered-list-marker-style "^3.0.0"
- unified "^10.0.0"
-
-remark-preset-lint-recommended@^6.1.2:
- version "6.1.2"
- resolved "https://registry.yarnpkg.com/remark-preset-lint-recommended/-/remark-preset-lint-recommended-6.1.2.tgz#268eeaab887cef79e6b22fde046e65cf11abcf67"
- integrity sha512-x9kWufNY8PNAhY4fsl+KD3atgQdo4imP3GDAQYbQ6ylWVyX13suPRLkqnupW0ODRynfUg8ZRt8pVX0wMHwgPAg==
- dependencies:
- "@types/mdast" "^3.0.0"
- remark-lint "^9.0.0"
- remark-lint-final-newline "^2.0.0"
- remark-lint-hard-break-spaces "^3.0.0"
- remark-lint-list-item-bullet-indent "^4.0.0"
- remark-lint-list-item-indent "^3.0.0"
- remark-lint-no-blockquote-without-marker "^5.0.0"
- remark-lint-no-duplicate-definitions "^3.0.0"
- remark-lint-no-heading-content-indent "^4.0.0"
- remark-lint-no-inline-padding "^4.0.0"
- remark-lint-no-literal-urls "^3.0.0"
- remark-lint-no-shortcut-reference-image "^3.0.0"
- remark-lint-no-shortcut-reference-link "^3.0.0"
- remark-lint-no-undefined-references "^4.0.0"
- remark-lint-no-unused-definitions "^3.0.0"
- remark-lint-ordered-list-marker-style "^3.0.0"
- unified "^10.0.0"
-
-remark-squeeze-paragraphs@4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/remark-squeeze-paragraphs/-/remark-squeeze-paragraphs-4.0.0.tgz#76eb0e085295131c84748c8e43810159c5653ead"
- integrity sha512-8qRqmL9F4nuLPIgl92XUuxI3pFxize+F1H0e/W3llTk0UsjJaj01+RrirkMw7P21RKe4X6goQhYRSvNWX+70Rw==
- dependencies:
- mdast-squeeze-paragraphs "^4.0.0"
-
-remark-stringify@^10.0.0:
- version "10.0.2"
- resolved "https://registry.yarnpkg.com/remark-stringify/-/remark-stringify-10.0.2.tgz#50414a6983f5008eb9e72eed05f980582d1f69d7"
- integrity sha512-6wV3pvbPvHkbNnWB0wdDvVFHOe1hBRAx1Q/5g/EpH4RppAII6J8Gnwe7VbHuXaoKIF6LAg6ExTel/+kNqSQ7lw==
- dependencies:
- "@types/mdast" "^3.0.0"
- mdast-util-to-markdown "^1.0.0"
- unified "^10.0.0"
-
-remark@^14.0.0:
- version "14.0.2"
- resolved "https://registry.yarnpkg.com/remark/-/remark-14.0.2.tgz#4a1833f7441a5c29e44b37bb1843fb820797b40f"
- integrity sha512-A3ARm2V4BgiRXaUo5K0dRvJ1lbogrbXnhkJRmD0yw092/Yl0kOCZt1k9ZeElEwkZsWGsMumz6qL5MfNJH9nOBA==
- dependencies:
- "@types/mdast" "^3.0.0"
- remark-parse "^10.0.0"
- remark-stringify "^10.0.0"
- unified "^10.0.0"
-
-renderkid@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/renderkid/-/renderkid-3.0.0.tgz#5fd823e4d6951d37358ecc9a58b1f06836b6268a"
- integrity sha512-q/7VIQA8lmM1hF+jn+sFSPWGlMkSAeNYcPLmDQx2zzuiDfaLrOmumR8iaUKlenFgh0XRPIUeSPlH3A+AW3Z5pg==
- dependencies:
- css-select "^4.1.3"
- dom-converter "^0.2.0"
- htmlparser2 "^6.1.0"
- lodash "^4.17.21"
- strip-ansi "^6.0.1"
-
-repeat-string@^1.5.4:
- version "1.6.1"
- resolved "https://registry.yarnpkg.com/repeat-string/-/repeat-string-1.6.1.tgz#8dcae470e1c88abc2d600fff4a776286da75e637"
- integrity sha512-PV0dzCYDNfRi1jCDbJzpW7jNNDRuCOG/jI5ctQcGKt/clZD+YcPS3yIlWuTJMmESC8aevCFmWJy5wjAFgNqN6w==
-
-require-from-string@^2.0.2:
- version "2.0.2"
- resolved "https://registry.yarnpkg.com/require-from-string/-/require-from-string-2.0.2.tgz#89a7fdd938261267318eafe14f9c32e598c36909"
- integrity sha512-Xf0nWe6RseziFMu+Ap9biiUbmplq6S9/p+7w7YXP/JBHhrUDDUhwa+vANyubuqfZWTveU//DYVGsDG7RKL/vEw==
-
-"require-like@>= 0.1.1":
- version "0.1.2"
- resolved "https://registry.yarnpkg.com/require-like/-/require-like-0.1.2.tgz#ad6f30c13becd797010c468afa775c0c0a6b47fa"
- integrity sha512-oyrU88skkMtDdauHDuKVrgR+zuItqr6/c//FXzvmxRGMexSDc6hNvJInGW3LL46n+8b50RykrvwSUIIQH2LQ5A==
-
-requires-port@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/requires-port/-/requires-port-1.0.0.tgz#925d2601d39ac485e091cf0da5c6e694dc3dcaff"
- integrity sha512-KigOCHcocU3XODJxsu8i/j8T9tzT4adHiecwORRQ0ZZFcp7ahwXuRU1m+yuO90C5ZUyGeGfocHDI14M3L3yDAQ==
-
-resolve-from@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/resolve-from/-/resolve-from-4.0.0.tgz#4abcd852ad32dd7baabfe9b40e00a36db5f392e6"
- integrity sha512-pb/MYmXstAkysRFx8piNI1tGFNQIFA3vkE3Gq4EuA1dF6gHp/+vgZqsCGJapvy8N3Q+4o7FwvquPJcnZ7RYy4g==
-
-resolve-pathname@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/resolve-pathname/-/resolve-pathname-3.0.0.tgz#99d02224d3cf263689becbb393bc560313025dcd"
- integrity sha512-C7rARubxI8bXFNB/hqcp/4iUeIXJhJZvFPFPiSPRnhU5UPxzMFIl+2E6yY6c4k9giDJAhtV+enfA+G89N6Csng==
-
-resolve@^1.1.6, resolve@^1.14.2, resolve@^1.3.2:
- version "1.22.1"
- resolved "https://registry.yarnpkg.com/resolve/-/resolve-1.22.1.tgz#27cb2ebb53f91abb49470a928bba7558066ac177"
- integrity sha512-nBpuuYuY5jFsli/JIs1oldw6fOQCBioohqWZg/2hiaOybXOft4lonv85uDOKXdf8rhyK159cxU5cDcK/NKk8zw==
- dependencies:
- is-core-module "^2.9.0"
- path-parse "^1.0.7"
- supports-preserve-symlinks-flag "^1.0.0"
-
-responselike@^1.0.2:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/responselike/-/responselike-1.0.2.tgz#918720ef3b631c5642be068f15ade5a46f4ba1e7"
- integrity sha512-/Fpe5guzJk1gPqdJLJR5u7eG/gNY4nImjbRDaVWVMRhne55TCmj2i9Q+54PBRfatRC8v/rIiv9BN0pMd9OV5EQ==
- dependencies:
- lowercase-keys "^1.0.0"
-
-retry@^0.13.1:
- version "0.13.1"
- resolved "https://registry.yarnpkg.com/retry/-/retry-0.13.1.tgz#185b1587acf67919d63b357349e03537b2484658"
- integrity sha512-XQBQ3I8W1Cge0Seh+6gjj03LbmRFWuoszgK9ooCpwYIrhhoO80pfq4cUkU5DkknwfOfFteRwlZ56PYOGYyFWdg==
-
-reusify@^1.0.4:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/reusify/-/reusify-1.0.4.tgz#90da382b1e126efc02146e90845a88db12925d76"
- integrity sha512-U9nH88a3fc/ekCF1l0/UP1IosiuIjyTh7hBvXVMHYgVcfGvt897Xguj2UOLDeI5BG2m7/uwyaLVT6fbtCwTyzw==
-
-rimraf@^3.0.2:
- version "3.0.2"
- resolved "https://registry.yarnpkg.com/rimraf/-/rimraf-3.0.2.tgz#f1a5402ba6220ad52cc1282bac1ae3aa49fd061a"
- integrity sha512-JZkJMZkAGFFPP2YqXZXPbMlMBgsxzE8ILs4lMIX/2o0L9UBw9O/Y3o6wFw/i9YLapcUJWwqbi3kdxIPdC62TIA==
- dependencies:
- glob "^7.1.3"
-
-rtl-detect@^1.0.4:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/rtl-detect/-/rtl-detect-1.0.4.tgz#40ae0ea7302a150b96bc75af7d749607392ecac6"
- integrity sha512-EBR4I2VDSSYr7PkBmFy04uhycIpDKp+21p/jARYXlCSjQksTBQcJ0HFUPOO79EPPH5JS6VAhiIQbycf0O3JAxQ==
-
-rtlcss@^3.5.0:
- version "3.5.0"
- resolved "https://registry.yarnpkg.com/rtlcss/-/rtlcss-3.5.0.tgz#c9eb91269827a102bac7ae3115dd5d049de636c3"
- integrity sha512-wzgMaMFHQTnyi9YOwsx9LjOxYXJPzS8sYnFaKm6R5ysvTkwzHiB0vxnbHwchHQT65PTdBjDG21/kQBWI7q9O7A==
- dependencies:
- find-up "^5.0.0"
- picocolors "^1.0.0"
- postcss "^8.3.11"
- strip-json-comments "^3.1.1"
-
-run-con@~1.2.10:
- version "1.2.11"
- resolved "https://registry.yarnpkg.com/run-con/-/run-con-1.2.11.tgz#0014ed430bad034a60568dfe7de2235f32e3f3c4"
- integrity sha512-NEMGsUT+cglWkzEr4IFK21P4Jca45HqiAbIIZIBdX5+UZTB24Mb/21iNGgz9xZa8tL6vbW7CXmq7MFN42+VjNQ==
- dependencies:
- deep-extend "^0.6.0"
- ini "~3.0.0"
- minimist "^1.2.6"
- strip-json-comments "~3.1.1"
-
-run-parallel@^1.1.9:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/run-parallel/-/run-parallel-1.2.0.tgz#66d1368da7bdf921eb9d95bd1a9229e7f21a43ee"
- integrity sha512-5l4VyZR86LZ/lDxZTR6jqL8AFE2S0IFLMP26AbjsLVADxHdhB/c0GUsH+y39UfCi3dzz8OlQuPmnaJOMoDHQBA==
- dependencies:
- queue-microtask "^1.2.2"
-
-rxjs@^7.5.4:
- version "7.8.0"
- resolved "https://registry.yarnpkg.com/rxjs/-/rxjs-7.8.0.tgz#90a938862a82888ff4c7359811a595e14e1e09a4"
- integrity sha512-F2+gxDshqmIub1KdvZkaEfGDwLNpPvk9Fs6LD/MyQxNgMds/WH9OdDDXOmxUZpME+iSK3rQCctkL0DYyytUqMg==
- dependencies:
- tslib "^2.1.0"
-
-sade@^1.7.3:
- version "1.8.1"
- resolved "https://registry.yarnpkg.com/sade/-/sade-1.8.1.tgz#0a78e81d658d394887be57d2a409bf703a3b2701"
- integrity sha512-xal3CZX1Xlo/k4ApwCFrHVACi9fBqJ7V+mwhBsuf/1IOKbBy098Fex+Wa/5QMubw09pSZ/u8EY8PWgevJsXp1A==
- dependencies:
- mri "^1.1.0"
-
-safe-buffer@5.1.2, safe-buffer@~5.1.0, safe-buffer@~5.1.1:
- version "5.1.2"
- resolved "https://registry.yarnpkg.com/safe-buffer/-/safe-buffer-5.1.2.tgz#991ec69d296e0313747d59bdfd2b745c35f8828d"
- integrity sha512-Gd2UZBJDkXlY7GbJxfsE8/nvKkUEU1G38c1siN6QP6a9PT9MmHB8GnpscSmMJSoF8LOIrt8ud/wPtojys4G6+g==
-
-safe-buffer@5.2.1, safe-buffer@>=5.1.0, safe-buffer@^5.1.0, safe-buffer@~5.2.0:
- version "5.2.1"
- resolved "https://registry.yarnpkg.com/safe-buffer/-/safe-buffer-5.2.1.tgz#1eaf9fa9bdb1fdd4ec75f58f9cdb4e6b7827eec6"
- integrity sha512-rp3So07KcdmmKbGvgaNxQSJr7bGVSVk5S9Eq1F+ppbRo70+YeaDxkw5Dd8NPN+GD6bjnYm2VuPuCXmpuYvmCXQ==
-
-"safer-buffer@>= 2.1.2 < 3":
- version "2.1.2"
- resolved "https://registry.yarnpkg.com/safer-buffer/-/safer-buffer-2.1.2.tgz#44fa161b0187b9549dd84bb91802f9bd8385cd6a"
- integrity sha512-YZo3K82SD7Riyi0E1EQPojLz7kpepnSQI9IyPbHHg1XXXevb5dJI7tpyN2ADxGcQbHG7vcyRHk0cbwqcQriUtg==
-
-sax@^1.2.4:
- version "1.2.4"
- resolved "https://registry.yarnpkg.com/sax/-/sax-1.2.4.tgz#2816234e2378bddc4e5354fab5caa895df7100d9"
- integrity sha512-NqVDv9TpANUjFm0N8uM5GxL36UgKi9/atZw+x7YFnQ8ckwFGKrl4xX4yWtrey3UJm5nP1kUbnYgLopqWNSRhWw==
-
-scheduler@^0.20.2:
- version "0.20.2"
- resolved "https://registry.yarnpkg.com/scheduler/-/scheduler-0.20.2.tgz#4baee39436e34aa93b4874bddcbf0fe8b8b50e91"
- integrity sha512-2eWfGgAqqWFGqtdMmcL5zCMK1U8KlXv8SQFGglL3CEtd0aDVDWgeF/YoCmvln55m5zSk3J/20hTaSBeSObsQDQ==
- dependencies:
- loose-envify "^1.1.0"
- object-assign "^4.1.1"
-
-schema-utils@2.7.0:
- version "2.7.0"
- resolved "https://registry.yarnpkg.com/schema-utils/-/schema-utils-2.7.0.tgz#17151f76d8eae67fbbf77960c33c676ad9f4efc7"
- integrity sha512-0ilKFI6QQF5nxDZLFn2dMjvc4hjg/Wkg7rHd3jK6/A4a1Hl9VFdQWvgB1UMGoU94pad1P/8N7fMcEnLnSiju8A==
- dependencies:
- "@types/json-schema" "^7.0.4"
- ajv "^6.12.2"
- ajv-keywords "^3.4.1"
-
-schema-utils@^2.6.5:
- version "2.7.1"
- resolved "https://registry.yarnpkg.com/schema-utils/-/schema-utils-2.7.1.tgz#1ca4f32d1b24c590c203b8e7a50bf0ea4cd394d7"
- integrity sha512-SHiNtMOUGWBQJwzISiVYKu82GiV4QYGePp3odlY1tuKO7gPtphAT5R/py0fA6xtbgLL/RvtJZnU9b8s0F1q0Xg==
- dependencies:
- "@types/json-schema" "^7.0.5"
- ajv "^6.12.4"
- ajv-keywords "^3.5.2"
-
-schema-utils@^3.0.0, schema-utils@^3.1.0, schema-utils@^3.1.1:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/schema-utils/-/schema-utils-3.1.1.tgz#bc74c4b6b6995c1d88f76a8b77bea7219e0c8281"
- integrity sha512-Y5PQxS4ITlC+EahLuXaY86TXfR7Dc5lw294alXOq86JAHCihAIZfqv8nNCWvaEJvaC51uN9hbLGeV0cFBdH+Fw==
- dependencies:
- "@types/json-schema" "^7.0.8"
- ajv "^6.12.5"
- ajv-keywords "^3.5.2"
-
-schema-utils@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/schema-utils/-/schema-utils-4.0.0.tgz#60331e9e3ae78ec5d16353c467c34b3a0a1d3df7"
- integrity sha512-1edyXKgh6XnJsJSQ8mKWXnN/BVaIbFMLpouRUrXgVq7WYne5kw3MW7UPhO44uRXQSIpTSXoJbmrR2X0w9kUTyg==
- dependencies:
- "@types/json-schema" "^7.0.9"
- ajv "^8.8.0"
- ajv-formats "^2.1.1"
- ajv-keywords "^5.0.0"
-
-section-matter@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/section-matter/-/section-matter-1.0.0.tgz#e9041953506780ec01d59f292a19c7b850b84167"
- integrity sha512-vfD3pmTzGpufjScBh50YHKzEu2lxBWhVEHsNGoEXmCmn2hKGfeNLYMzCJpe8cD7gqX7TJluOVpBkAequ6dgMmA==
- dependencies:
- extend-shallow "^2.0.1"
- kind-of "^6.0.0"
-
-select-hose@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/select-hose/-/select-hose-2.0.0.tgz#625d8658f865af43ec962bfc376a37359a4994ca"
- integrity sha512-mEugaLK+YfkijB4fx0e6kImuJdCIt2LxCRcbEYPqRGCs4F2ogyfZU5IAZRdjCP8JPq2AtdNoC/Dux63d9Kiryg==
-
-selfsigned@^2.1.1:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/selfsigned/-/selfsigned-2.1.1.tgz#18a7613d714c0cd3385c48af0075abf3f266af61"
- integrity sha512-GSL3aowiF7wa/WtSFwnUrludWFoNhftq8bUkH9pkzjpN2XSPOAYEgg6e0sS9s0rZwgJzJiQRPU18A6clnoW5wQ==
- dependencies:
- node-forge "^1"
-
-semver-diff@^3.1.1:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/semver-diff/-/semver-diff-3.1.1.tgz#05f77ce59f325e00e2706afd67bb506ddb1ca32b"
- integrity sha512-GX0Ix/CJcHyB8c4ykpHGIAvLyOwOobtM/8d+TQkAd81/bEjgPHrfba41Vpesr7jX/t8Uh+R3EX9eAS5be+jQYg==
- dependencies:
- semver "^6.3.0"
-
-semver@^5.4.1:
- version "5.7.1"
- resolved "https://registry.yarnpkg.com/semver/-/semver-5.7.1.tgz#a954f931aeba508d307bbf069eff0c01c96116f7"
- integrity sha512-sauaDf/PZdVgrLTNYHRtpXa1iRiKcaebiKQ1BJdpQlWH2lCvexQdX55snPFyK7QzpudqbCI0qXFfOasHdyNDGQ==
-
-semver@^6.0.0, semver@^6.1.1, semver@^6.1.2, semver@^6.2.0, semver@^6.3.0:
- version "6.3.0"
- resolved "https://registry.yarnpkg.com/semver/-/semver-6.3.0.tgz#ee0a64c8af5e8ceea67687b133761e1becbd1d3d"
- integrity sha512-b39TBaTSfV6yBrapU89p5fKekE2m/NwnDocOVruQFS1/veMgdzuPcnOM34M6CwxW8jH/lxEa5rBoDeUwu5HHTw==
-
-semver@^7.3.2, semver@^7.3.4, semver@^7.3.5, semver@^7.3.7, semver@^7.3.8:
- version "7.3.8"
- resolved "https://registry.yarnpkg.com/semver/-/semver-7.3.8.tgz#07a78feafb3f7b32347d725e33de7e2a2df67798"
- integrity sha512-NB1ctGL5rlHrPJtFDVIVzTyQylMLu9N9VICA6HSFJo8MCGVTMW6gfpicwKmmK/dAjTOrqu5l63JJOpDSrAis3A==
- dependencies:
- lru-cache "^6.0.0"
-
-send@0.18.0:
- version "0.18.0"
- resolved "https://registry.yarnpkg.com/send/-/send-0.18.0.tgz#670167cc654b05f5aa4a767f9113bb371bc706be"
- integrity sha512-qqWzuOjSFOuqPjFe4NOsMLafToQQwBSOEpS+FwEt3A2V3vKubTquT3vmLTQpFgMXp8AlFWFuP1qKaJZOtPpVXg==
- dependencies:
- debug "2.6.9"
- depd "2.0.0"
- destroy "1.2.0"
- encodeurl "~1.0.2"
- escape-html "~1.0.3"
- etag "~1.8.1"
- fresh "0.5.2"
- http-errors "2.0.0"
- mime "1.6.0"
- ms "2.1.3"
- on-finished "2.4.1"
- range-parser "~1.2.1"
- statuses "2.0.1"
-
-serialize-javascript@^6.0.0:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/serialize-javascript/-/serialize-javascript-6.0.1.tgz#b206efb27c3da0b0ab6b52f48d170b7996458e5c"
- integrity sha512-owoXEFjWRllis8/M1Q+Cw5k8ZH40e3zhp/ovX+Xr/vi1qj6QesbyXXViFbpNvWvPNAD62SutwEXavefrLJWj7w==
- dependencies:
- randombytes "^2.1.0"
-
-serve-handler@^6.1.3:
- version "6.1.5"
- resolved "https://registry.yarnpkg.com/serve-handler/-/serve-handler-6.1.5.tgz#a4a0964f5c55c7e37a02a633232b6f0d6f068375"
- integrity sha512-ijPFle6Hwe8zfmBxJdE+5fta53fdIY0lHISJvuikXB3VYFafRjMRpOffSPvCYsbKyBA7pvy9oYr/BT1O3EArlg==
- dependencies:
- bytes "3.0.0"
- content-disposition "0.5.2"
- fast-url-parser "1.1.3"
- mime-types "2.1.18"
- minimatch "3.1.2"
- path-is-inside "1.0.2"
- path-to-regexp "2.2.1"
- range-parser "1.2.0"
-
-serve-index@^1.9.1:
- version "1.9.1"
- resolved "https://registry.yarnpkg.com/serve-index/-/serve-index-1.9.1.tgz#d3768d69b1e7d82e5ce050fff5b453bea12a9239"
- integrity sha512-pXHfKNP4qujrtteMrSBb0rc8HJ9Ms/GrXwcUtUtD5s4ewDJI8bT3Cz2zTVRMKtri49pLx2e0Ya8ziP5Ya2pZZw==
- dependencies:
- accepts "~1.3.4"
- batch "0.6.1"
- debug "2.6.9"
- escape-html "~1.0.3"
- http-errors "~1.6.2"
- mime-types "~2.1.17"
- parseurl "~1.3.2"
-
-serve-static@1.15.0:
- version "1.15.0"
- resolved "https://registry.yarnpkg.com/serve-static/-/serve-static-1.15.0.tgz#faaef08cffe0a1a62f60cad0c4e513cff0ac9540"
- integrity sha512-XGuRDNjXUijsUL0vl6nSD7cwURuzEgglbOaFuZM9g3kwDXOWVTck0jLzjPzGD+TazWbboZYu52/9/XPdUgne9g==
- dependencies:
- encodeurl "~1.0.2"
- escape-html "~1.0.3"
- parseurl "~1.3.3"
- send "0.18.0"
-
-setimmediate@^1.0.5:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/setimmediate/-/setimmediate-1.0.5.tgz#290cbb232e306942d7d7ea9b83732ab7856f8285"
- integrity sha512-MATJdZp8sLqDl/68LfQmbP8zKPLQNV6BIZoIgrscFDQ+RsvK/BxeDQOgyxKKoh0y/8h3BqVFnCqQ/gd+reiIXA==
-
-setprototypeof@1.1.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/setprototypeof/-/setprototypeof-1.1.0.tgz#d0bd85536887b6fe7c0d818cb962d9d91c54e656"
- integrity sha512-BvE/TwpZX4FXExxOxZyRGQQv651MSwmWKZGqvmPcRIjDqWub67kTKuIMx43cZZrS/cBBzwBcNDWoFxt2XEFIpQ==
-
-setprototypeof@1.2.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/setprototypeof/-/setprototypeof-1.2.0.tgz#66c9a24a73f9fc28cbe66b09fed3d33dcaf1b424"
- integrity sha512-E5LDX7Wrp85Kil5bhZv46j8jOeboKq5JMmYM3gVGdGH8xFpPWXUMsNrlODCrkoxMEeNi/XZIwuRvY4XNwYMJpw==
-
-shallow-clone@^3.0.0:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/shallow-clone/-/shallow-clone-3.0.1.tgz#8f2981ad92531f55035b01fb230769a40e02efa3"
- integrity sha512-/6KqX+GVUdqPuPPd2LxDDxzX6CAbjJehAAOKlNpqqUpAqPM6HeL8f+o3a+JsyGjn2lv0WY8UsTgUJjU9Ok55NA==
- dependencies:
- kind-of "^6.0.2"
-
-shallowequal@^1.1.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/shallowequal/-/shallowequal-1.1.0.tgz#188d521de95b9087404fd4dcb68b13df0ae4e7f8"
- integrity sha512-y0m1JoUZSlPAjXVtPPW70aZWfIL/dSP7AFkRnniLCrK/8MDKog3TySTBmckD+RObVxH0v4Tox67+F14PdED2oQ==
-
-shebang-command@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/shebang-command/-/shebang-command-2.0.0.tgz#ccd0af4f8835fbdc265b82461aaf0c36663f34ea"
- integrity sha512-kHxr2zZpYtdmrN1qDjrrX/Z1rR1kG8Dx+gkpK1G4eXmvXswmcE1hTWBWYUzlraYw1/yZp6YuDY77YtvbN0dmDA==
- dependencies:
- shebang-regex "^3.0.0"
-
-shebang-regex@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/shebang-regex/-/shebang-regex-3.0.0.tgz#ae16f1644d873ecad843b0307b143362d4c42172"
- integrity sha512-7++dFhtcx3353uBaq8DDR4NuxBetBzC7ZQOhmTQInHEd6bSrXdiEyzCvG07Z44UYdLShWUyXt5M/yhz8ekcb1A==
-
-shell-quote@^1.7.3:
- version "1.8.0"
- resolved "https://registry.yarnpkg.com/shell-quote/-/shell-quote-1.8.0.tgz#20d078d0eaf71d54f43bd2ba14a1b5b9bfa5c8ba"
- integrity sha512-QHsz8GgQIGKlRi24yFc6a6lN69Idnx634w49ay6+jA5yFh7a1UY+4Rp6HPx/L/1zcEDPEij8cIsiqR6bQsE5VQ==
-
-shelljs@^0.8.5:
- version "0.8.5"
- resolved "https://registry.yarnpkg.com/shelljs/-/shelljs-0.8.5.tgz#de055408d8361bed66c669d2f000538ced8ee20c"
- integrity sha512-TiwcRcrkhHvbrZbnRcFYMLl30Dfov3HKqzp5tO5b4pt6G/SezKcYhmDg15zXVBswHmctSAQKznqNW2LO5tTDow==
- dependencies:
- glob "^7.0.0"
- interpret "^1.0.0"
- rechoir "^0.6.2"
-
-side-channel@^1.0.4:
- version "1.0.4"
- resolved "https://registry.yarnpkg.com/side-channel/-/side-channel-1.0.4.tgz#efce5c8fdc104ee751b25c58d4290011fa5ea2cf"
- integrity sha512-q5XPytqFEIKHkGdiMIrY10mvLRvnQh42/+GoBlFW3b2LXLE2xxJpZFdm94we0BaoV3RwJyGqg5wS7epxTv0Zvw==
- dependencies:
- call-bind "^1.0.0"
- get-intrinsic "^1.0.2"
- object-inspect "^1.9.0"
-
-signal-exit@^3.0.2, signal-exit@^3.0.3:
- version "3.0.7"
- resolved "https://registry.yarnpkg.com/signal-exit/-/signal-exit-3.0.7.tgz#a9a1767f8af84155114eaabd73f99273c8f59ad9"
- integrity sha512-wnD2ZE+l+SPC/uoS0vXeE9L1+0wuaMqKlfz9AMUo38JsyLSBWSFcHR1Rri62LZc12vLr1gb3jl7iwQhgwpAbGQ==
-
-sirv@^1.0.7:
- version "1.0.19"
- resolved "https://registry.yarnpkg.com/sirv/-/sirv-1.0.19.tgz#1d73979b38c7fe91fcba49c85280daa9c2363b49"
- integrity sha512-JuLThK3TnZG1TAKDwNIqNq6QA2afLOCcm+iE8D1Kj3GA40pSPsxQjjJl0J8X3tsR7T+CP1GavpzLwYkgVLWrZQ==
- dependencies:
- "@polka/url" "^1.0.0-next.20"
- mrmime "^1.0.0"
- totalist "^1.0.0"
-
-sisteransi@^1.0.5:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/sisteransi/-/sisteransi-1.0.5.tgz#134d681297756437cc05ca01370d3a7a571075ed"
- integrity sha512-bLGGlR1QxBcynn2d5YmDX4MGjlZvy2MRBDRNHLJ8VI6l6+9FUiyTFNJ0IveOSP0bcXgVDPRcfGqA0pjaqUpfVg==
-
-sitemap@^7.1.1:
- version "7.1.1"
- resolved "https://registry.yarnpkg.com/sitemap/-/sitemap-7.1.1.tgz#eeed9ad6d95499161a3eadc60f8c6dce4bea2bef"
- integrity sha512-mK3aFtjz4VdJN0igpIJrinf3EO8U8mxOPsTBzSsy06UtjZQJ3YY3o3Xa7zSc5nMqcMrRwlChHZ18Kxg0caiPBg==
- dependencies:
- "@types/node" "^17.0.5"
- "@types/sax" "^1.2.1"
- arg "^5.0.0"
- sax "^1.2.4"
-
-slash@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/slash/-/slash-3.0.0.tgz#6539be870c165adbd5240220dbe361f1bc4d4634"
- integrity sha512-g9Q1haeby36OSStwb4ntCGGGaKsaVSjQ68fBxoQcutl5fS1vuY18H3wSt3jFyFtrkx+Kz0V1G85A4MyAdDMi2Q==
-
-slash@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/slash/-/slash-4.0.0.tgz#2422372176c4c6c5addb5e2ada885af984b396a7"
- integrity sha512-3dOsAHXXUkQTpOYcoAxLIorMTp4gIQr5IW3iVb7A7lFIp0VHhnynm9izx6TssdrIcVIESAlVjtnO2K8bg+Coew==
-
-sockjs@^0.3.24:
- version "0.3.24"
- resolved "https://registry.yarnpkg.com/sockjs/-/sockjs-0.3.24.tgz#c9bc8995f33a111bea0395ec30aa3206bdb5ccce"
- integrity sha512-GJgLTZ7vYb/JtPSSZ10hsOYIvEYsjbNU+zPdIHcUaWVNUEPivzxku31865sSSud0Da0W4lEeOPlmw93zLQchuQ==
- dependencies:
- faye-websocket "^0.11.3"
- uuid "^8.3.2"
- websocket-driver "^0.7.4"
-
-solid-js@^1.3.0:
- version "1.6.11"
- resolved "https://registry.yarnpkg.com/solid-js/-/solid-js-1.6.11.tgz#263a512bf94efd89245a77f58dc18c195302237f"
- integrity sha512-JquQQHPArGq+i2PLURxJ99Pcz2/1docpbycSio/cKSA0SeI3z5zRjy0TNcH4NRYvbOLrcini+iovXwnexKabyw==
- dependencies:
- csstype "^3.1.0"
-
-sort-css-media-queries@2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/sort-css-media-queries/-/sort-css-media-queries-2.1.0.tgz#7c85e06f79826baabb232f5560e9745d7a78c4ce"
- integrity sha512-IeWvo8NkNiY2vVYdPa27MCQiR0MN0M80johAYFVxWWXQ44KU84WNxjslwBHmc/7ZL2ccwkM7/e6S5aiKZXm7jA==
-
-source-map-js@^1.0.2:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/source-map-js/-/source-map-js-1.0.2.tgz#adbc361d9c62df380125e7f161f71c826f1e490c"
- integrity sha512-R0XvVJ9WusLiqTCEiGCmICCMplcCkIwwR11mOSD9CR5u+IXYdiseeEuXCVAjS54zqwkLcPNnmU4OeJ6tUrWhDw==
-
-source-map-support@~0.5.20:
- version "0.5.21"
- resolved "https://registry.yarnpkg.com/source-map-support/-/source-map-support-0.5.21.tgz#04fe7c7f9e1ed2d662233c28cb2b35b9f63f6e4f"
- integrity sha512-uBHU3L3czsIyYXKX88fdrGovxdSCoTGDRZ6SYXtSRxLZUzHg5P/66Ht6uoUlHu9EZod+inXhKo3qQgwXUT/y1w==
- dependencies:
- buffer-from "^1.0.0"
- source-map "^0.6.0"
-
-source-map@^0.5.0:
- version "0.5.7"
- resolved "https://registry.yarnpkg.com/source-map/-/source-map-0.5.7.tgz#8a039d2d1021d22d1ea14c80d8ea468ba2ef3fcc"
- integrity sha512-LbrmJOMUSdEVxIKvdcJzQC+nQhe8FUZQTXQy6+I75skNgn3OoQ0DZA8YnFa7gp8tqtL3KPf1kmo0R5DoApeSGQ==
-
-source-map@^0.6.0, source-map@^0.6.1, source-map@~0.6.0:
- version "0.6.1"
- resolved "https://registry.yarnpkg.com/source-map/-/source-map-0.6.1.tgz#74722af32e9614e9c287a8d0bbde48b5e2f1a263"
- integrity sha512-UjgapumWlbMhkBgzT7Ykc5YXUT46F0iKu8SGXq0bcwP5dz/h0Plj6enJqjz1Zbq2l5WaqYnrVbwWOWMyF3F47g==
-
-space-separated-tokens@^1.0.0:
- version "1.1.5"
- resolved "https://registry.yarnpkg.com/space-separated-tokens/-/space-separated-tokens-1.1.5.tgz#85f32c3d10d9682007e917414ddc5c26d1aa6899"
- integrity sha512-q/JSVd1Lptzhf5bkYm4ob4iWPjx0KiRe3sRFBNrVqbJkFaBm5vbbowy1mymoPNLRa52+oadOhJ+K49wsSeSjTA==
-
-spdy-transport@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/spdy-transport/-/spdy-transport-3.0.0.tgz#00d4863a6400ad75df93361a1608605e5dcdcf31"
- integrity sha512-hsLVFE5SjA6TCisWeJXFKniGGOpBgMLmerfO2aCyCU5s7nJ/rpAepqmFifv/GCbSbueEeAJJnmSQ2rKC/g8Fcw==
- dependencies:
- debug "^4.1.0"
- detect-node "^2.0.4"
- hpack.js "^2.1.6"
- obuf "^1.1.2"
- readable-stream "^3.0.6"
- wbuf "^1.7.3"
-
-spdy@^4.0.2:
- version "4.0.2"
- resolved "https://registry.yarnpkg.com/spdy/-/spdy-4.0.2.tgz#b74f466203a3eda452c02492b91fb9e84a27677b"
- integrity sha512-r46gZQZQV+Kl9oItvl1JZZqJKGr+oEkB08A6BzkiR7593/7IbtuncXHd2YoYeTsG4157ZssMu9KYvUHLcjcDoA==
- dependencies:
- debug "^4.1.0"
- handle-thing "^2.0.0"
- http-deceiver "^1.2.7"
- select-hose "^2.0.0"
- spdy-transport "^3.0.0"
-
-sprintf-js@~1.0.2:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/sprintf-js/-/sprintf-js-1.0.3.tgz#04e6926f662895354f3dd015203633b857297e2c"
- integrity sha512-D9cPgkvLlV3t3IzL0D0YLvGA9Ahk4PcvVwUbN0dSGr1aP0Nrt4AEnTUbuGvquEC0mA64Gqt1fzirlRs5ibXx8g==
-
-stable@^0.1.8:
- version "0.1.8"
- resolved "https://registry.yarnpkg.com/stable/-/stable-0.1.8.tgz#836eb3c8382fe2936feaf544631017ce7d47a3cf"
- integrity sha512-ji9qxRnOVfcuLDySj9qzhGSEFVobyt1kIOSkj1qZzYLzq7Tos/oUUWvotUPQLlrsidqsK6tBH89Bc9kL5zHA6w==
-
-state-toggle@^1.0.0:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/state-toggle/-/state-toggle-1.0.3.tgz#e123b16a88e143139b09c6852221bc9815917dfe"
- integrity sha512-d/5Z4/2iiCnHw6Xzghyhb+GcmF89bxwgXG60wjIiZaxnymbyOmI8Hk4VqHXiVVp6u2ysaskFfXg3ekCj4WNftQ==
-
-statuses@2.0.1:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/statuses/-/statuses-2.0.1.tgz#55cb000ccf1d48728bd23c685a063998cf1a1b63"
- integrity sha512-RwNA9Z/7PrK06rYLIzFMlaF+l73iwpzsqRIFgbMLbTcLD6cOao82TaWefPXQvB2fOC4AjuYSEndS7N/mTCbkdQ==
-
-"statuses@>= 1.4.0 < 2":
- version "1.5.0"
- resolved "https://registry.yarnpkg.com/statuses/-/statuses-1.5.0.tgz#161c7dac177659fd9811f43771fa99381478628c"
- integrity sha512-OpZ3zP+jT1PI7I8nemJX4AKmAX070ZkYPVWV/AaKTJl+tXCTGyVdC1a4SL8RUQYEwk/f34ZX8UTykN68FwrqAA==
-
-std-env@^3.0.1:
- version "3.3.2"
- resolved "https://registry.yarnpkg.com/std-env/-/std-env-3.3.2.tgz#af27343b001616015534292178327b202b9ee955"
- integrity sha512-uUZI65yrV2Qva5gqE0+A7uVAvO40iPo6jGhs7s8keRfHCmtg+uB2X6EiLGCI9IgL1J17xGhvoOqSz79lzICPTA==
-
-string-width@^4.0.0, string-width@^4.1.0, string-width@^4.2.0, string-width@^4.2.2:
- version "4.2.3"
- resolved "https://registry.yarnpkg.com/string-width/-/string-width-4.2.3.tgz#269c7117d27b05ad2e536830a8ec895ef9c6d010"
- integrity sha512-wKyQRQpjJ0sIp62ErSZdGsjMJWsap5oRNihHhu6G7JVO/9jIB6UyevL+tXuOqrng8j/cxKTWyWUwvSTriiZz/g==
- dependencies:
- emoji-regex "^8.0.0"
- is-fullwidth-code-point "^3.0.0"
- strip-ansi "^6.0.1"
-
-string-width@^5.0.0, string-width@^5.0.1:
- version "5.1.2"
- resolved "https://registry.yarnpkg.com/string-width/-/string-width-5.1.2.tgz#14f8daec6d81e7221d2a357e668cab73bdbca794"
- integrity sha512-HnLOCR3vjcY8beoNLtcjZ5/nxn2afmME6lhrDrebokqMap+XbeW8n9TXpPDOqdGK5qcI3oT0GKTW6wC7EMiVqA==
- dependencies:
- eastasianwidth "^0.2.0"
- emoji-regex "^9.2.2"
- strip-ansi "^7.0.1"
-
-string_decoder@^1.1.1:
- version "1.3.0"
- resolved "https://registry.yarnpkg.com/string_decoder/-/string_decoder-1.3.0.tgz#42f114594a46cf1a8e30b0a84f56c78c3edac21e"
- integrity sha512-hkRX8U1WjJFd8LsDJ2yQ/wWWxaopEsABU1XfkM8A+j0+85JAGppt16cr1Whg6KIbb4okU6Mql6BOj+uup/wKeA==
- dependencies:
- safe-buffer "~5.2.0"
-
-string_decoder@~1.1.1:
- version "1.1.1"
- resolved "https://registry.yarnpkg.com/string_decoder/-/string_decoder-1.1.1.tgz#9cf1611ba62685d7030ae9e4ba34149c3af03fc8"
- integrity sha512-n/ShnvDi6FHbbVfviro+WojiFzv+s8MPMHBczVePfUpDJLwoLT0ht1l4YwBCbi8pJAveEEdnkHyPyTP/mzRfwg==
- dependencies:
- safe-buffer "~5.1.0"
-
-stringify-entities@^4.0.0:
- version "4.0.3"
- resolved "https://registry.yarnpkg.com/stringify-entities/-/stringify-entities-4.0.3.tgz#cfabd7039d22ad30f3cc435b0ca2c1574fc88ef8"
- integrity sha512-BP9nNHMhhfcMbiuQKCqMjhDP5yBCAxsPu4pHFFzJ6Alo9dZgY4VLDPutXqIjpRiMoKdp7Av85Gr73Q5uH9k7+g==
- dependencies:
- character-entities-html4 "^2.0.0"
- character-entities-legacy "^3.0.0"
-
-stringify-object@^3.3.0:
- version "3.3.0"
- resolved "https://registry.yarnpkg.com/stringify-object/-/stringify-object-3.3.0.tgz#703065aefca19300d3ce88af4f5b3956d7556629"
- integrity sha512-rHqiFh1elqCQ9WPLIC8I0Q/g/wj5J1eMkyoiD6eoQApWHP0FtlK7rqnhmabL5VUY9JQCcqwwvlOaSuutekgyrw==
- dependencies:
- get-own-enumerable-property-symbols "^3.0.0"
- is-obj "^1.0.1"
- is-regexp "^1.0.0"
-
-strip-ansi@^6.0.0, strip-ansi@^6.0.1:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/strip-ansi/-/strip-ansi-6.0.1.tgz#9e26c63d30f53443e9489495b2105d37b67a85d9"
- integrity sha512-Y38VPSHcqkFrCpFnQ9vuSXmquuv5oXOKpGeT6aGrr3o3Gc9AlVa6JBfUSOCnbxGGZF+/0ooI7KrPuUSztUdU5A==
- dependencies:
- ansi-regex "^5.0.1"
-
-strip-ansi@^7.0.1:
- version "7.0.1"
- resolved "https://registry.yarnpkg.com/strip-ansi/-/strip-ansi-7.0.1.tgz#61740a08ce36b61e50e65653f07060d000975fb2"
- integrity sha512-cXNxvT8dFNRVfhVME3JAe98mkXDYN2O1l7jmcwMnOslDeESg1rF/OZMtK0nRAhiari1unG5cD4jG3rapUAkLbw==
- dependencies:
- ansi-regex "^6.0.1"
-
-strip-bom-string@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/strip-bom-string/-/strip-bom-string-1.0.0.tgz#e5211e9224369fbb81d633a2f00044dc8cedad92"
- integrity sha512-uCC2VHvQRYu+lMh4My/sFNmF2klFymLX1wHJeXnbEJERpV/ZsVuonzerjfrGpIGF7LBVa1O7i9kjiWvJiFck8g==
-
-strip-final-newline@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/strip-final-newline/-/strip-final-newline-2.0.0.tgz#89b852fb2fcbe936f6f4b3187afb0a12c1ab58ad"
- integrity sha512-BrpvfNAE3dcvq7ll3xVumzjKjZQ5tI1sEUIKr3Uoks0XUl45St3FlatVqef9prk4jRDzhW6WZg+3bk93y6pLjA==
-
-strip-json-comments@^3.1.1, strip-json-comments@~3.1.1:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/strip-json-comments/-/strip-json-comments-3.1.1.tgz#31f1281b3832630434831c310c01cccda8cbe006"
- integrity sha512-6fPc+R4ihwqP6N/aIv2f1gMH8lOVtWQHoqC4yK6oSDVVocumAsfCqjkXnqiYMhmMwS/mEHLp7Vehlt3ql6lEig==
-
-strip-json-comments@~2.0.1:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/strip-json-comments/-/strip-json-comments-2.0.1.tgz#3c531942e908c2697c0ec344858c286c7ca0a60a"
- integrity sha512-4gB8na07fecVVkOI6Rs4e7T6NOTki5EmL7TUduTs6bu3EdnSycntVJ4re8kgZA+wx9IueI2Y11bfbgwtzuE0KQ==
-
-style-to-object@0.3.0, style-to-object@^0.3.0:
- version "0.3.0"
- resolved "https://registry.yarnpkg.com/style-to-object/-/style-to-object-0.3.0.tgz#b1b790d205991cc783801967214979ee19a76e46"
- integrity sha512-CzFnRRXhzWIdItT3OmF8SQfWyahHhjq3HwcMNCNLn+N7klOOqPjMeG/4JSu77D7ypZdGvSzvkrbyeTMizz2VrA==
- dependencies:
- inline-style-parser "0.1.1"
-
-stylehacks@^5.1.1:
- version "5.1.1"
- resolved "https://registry.yarnpkg.com/stylehacks/-/stylehacks-5.1.1.tgz#7934a34eb59d7152149fa69d6e9e56f2fc34bcc9"
- integrity sha512-sBpcd5Hx7G6seo7b1LkpttvTz7ikD0LlH5RmdcBNb6fFR0Fl7LQwHDFr300q4cwUqi+IYrFGmsIHieMBfnN/Bw==
- dependencies:
- browserslist "^4.21.4"
- postcss-selector-parser "^6.0.4"
-
-supports-color@^5.3.0:
- version "5.5.0"
- resolved "https://registry.yarnpkg.com/supports-color/-/supports-color-5.5.0.tgz#e2e69a44ac8772f78a1ec0b35b689df6530efc8f"
- integrity sha512-QjVjwdXIt408MIiAqCX4oUKsgU2EqAGzs2Ppkm4aQYbjm+ZEWEcW4SfFNTr4uMNZma0ey4f5lgLrkB0aX0QMow==
- dependencies:
- has-flag "^3.0.0"
-
-supports-color@^7.1.0:
- version "7.2.0"
- resolved "https://registry.yarnpkg.com/supports-color/-/supports-color-7.2.0.tgz#1b7dcdcb32b8138801b3e478ba6a51caa89648da"
- integrity sha512-qpCAvRl9stuOHveKsn7HncJRvv501qIacKzQlO/+Lwxc9+0q2wLyv4Dfvt80/DPn2pqOBsJdDiogXGR9+OvwRw==
- dependencies:
- has-flag "^4.0.0"
-
-supports-color@^8.0.0:
- version "8.1.1"
- resolved "https://registry.yarnpkg.com/supports-color/-/supports-color-8.1.1.tgz#cd6fc17e28500cff56c1b86c0a7fd4a54a73005c"
- integrity sha512-MpUEN2OodtUzxvKQl72cUF7RQ5EiHsGvSsVG0ia9c5RbWGL2CI4C7EpPS8UTBIplnlzZiNuV56w+FuNxy3ty2Q==
- dependencies:
- has-flag "^4.0.0"
-
-supports-color@^9.0.0:
- version "9.3.1"
- resolved "https://registry.yarnpkg.com/supports-color/-/supports-color-9.3.1.tgz#34e4ad3c71c9a39dae3254ecc46c9b74e89e15a6"
- integrity sha512-knBY82pjmnIzK3NifMo3RxEIRD9E0kIzV4BKcyTZ9+9kWgLMxd4PrsTSMoFQUabgRBbF8KOLRDCyKgNV+iK44Q==
-
-supports-preserve-symlinks-flag@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/supports-preserve-symlinks-flag/-/supports-preserve-symlinks-flag-1.0.0.tgz#6eda4bd344a3c94aea376d4cc31bc77311039e09"
- integrity sha512-ot0WnXS9fgdkgIcePe6RHNk1WA8+muPa6cSjeR3V8K27q9BB1rTE3R1p7Hv0z1ZyAc8s6Vvv8DIyWf681MAt0w==
-
-svg-parser@^2.0.4:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/svg-parser/-/svg-parser-2.0.4.tgz#fdc2e29e13951736140b76cb122c8ee6630eb6b5"
- integrity sha512-e4hG1hRwoOdRb37cIMSgzNsxyzKfayW6VOflrwvR+/bzrkyxY/31WkbgnQpgtrNp1SdpJvpUAGTa/ZoiPNDuRQ==
-
-svgo@^2.7.0, svgo@^2.8.0:
- version "2.8.0"
- resolved "https://registry.yarnpkg.com/svgo/-/svgo-2.8.0.tgz#4ff80cce6710dc2795f0c7c74101e6764cfccd24"
- integrity sha512-+N/Q9kV1+F+UeWYoSiULYo4xYSDQlTgb+ayMobAXPwMnLvop7oxKMo9OzIrX5x3eS4L4f2UHhc9axXwY8DpChg==
- dependencies:
- "@trysound/sax" "0.2.0"
- commander "^7.2.0"
- css-select "^4.1.3"
- css-tree "^1.1.3"
- csso "^4.2.0"
- picocolors "^1.0.0"
- stable "^0.1.8"
-
-tapable@^1.0.0:
- version "1.1.3"
- resolved "https://registry.yarnpkg.com/tapable/-/tapable-1.1.3.tgz#a1fccc06b58db61fd7a45da2da44f5f3a3e67ba2"
- integrity sha512-4WK/bYZmj8xLr+HUCODHGF1ZFzsYffasLUgEiMBY4fgtltdO6B4WJtlSbPaDTLpYTcGVwM2qLnFTICEcNxs3kA==
-
-tapable@^2.0.0, tapable@^2.1.1, tapable@^2.2.0:
- version "2.2.1"
- resolved "https://registry.yarnpkg.com/tapable/-/tapable-2.2.1.tgz#1967a73ef4060a82f12ab96af86d52fdb76eeca0"
- integrity sha512-GNzQvQTOIP6RyTfE2Qxb8ZVlNmw0n88vp1szwWRimP02mnTsx3Wtn5qRdqY9w2XduFNUgvOwhNnQsjwCp+kqaQ==
-
-terser-webpack-plugin@^5.1.3, terser-webpack-plugin@^5.3.3:
- version "5.3.6"
- resolved "https://registry.yarnpkg.com/terser-webpack-plugin/-/terser-webpack-plugin-5.3.6.tgz#5590aec31aa3c6f771ce1b1acca60639eab3195c"
- integrity sha512-kfLFk+PoLUQIbLmB1+PZDMRSZS99Mp+/MHqDNmMA6tOItzRt+Npe3E+fsMs5mfcM0wCtrrdU387UnV+vnSffXQ==
- dependencies:
- "@jridgewell/trace-mapping" "^0.3.14"
- jest-worker "^27.4.5"
- schema-utils "^3.1.1"
- serialize-javascript "^6.0.0"
- terser "^5.14.1"
-
-terser@^5.10.0, terser@^5.14.1:
- version "5.16.3"
- resolved "https://registry.yarnpkg.com/terser/-/terser-5.16.3.tgz#3266017a9b682edfe019b8ecddd2abaae7b39c6b"
- integrity sha512-v8wWLaS/xt3nE9dgKEWhNUFP6q4kngO5B8eYFUuebsu7Dw/UNAnpUod6UHo04jSSkv8TzKHjZDSd7EXdDQAl8Q==
- dependencies:
- "@jridgewell/source-map" "^0.3.2"
- acorn "^8.5.0"
- commander "^2.20.0"
- source-map-support "~0.5.20"
-
-text-table@^0.2.0:
- version "0.2.0"
- resolved "https://registry.yarnpkg.com/text-table/-/text-table-0.2.0.tgz#7f5ee823ae805207c00af2df4a84ec3fcfa570b4"
- integrity sha512-N+8UisAXDGk8PFXP4HAzVR9nbfmVJ3zYLAWiTIoqC5v5isinhr+r5uaO8+7r3BMfuNIufIsA7RdpVgacC2cSpw==
-
-thunky@^1.0.2:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/thunky/-/thunky-1.1.0.tgz#5abaf714a9405db0504732bbccd2cedd9ef9537d"
- integrity sha512-eHY7nBftgThBqOyHGVN+l8gF0BucP09fMo0oO/Lb0w1OF80dJv+lDVpXG60WMQvkcxAkNybKsrEIE3ZtKGmPrA==
-
-tiny-invariant@^1.0.2:
- version "1.3.1"
- resolved "https://registry.yarnpkg.com/tiny-invariant/-/tiny-invariant-1.3.1.tgz#8560808c916ef02ecfd55e66090df23a4b7aa642"
- integrity sha512-AD5ih2NlSssTCwsMznbvwMZpJ1cbhkGd2uueNxzv2jDlEeZdU04JQfRnggJQ8DrcVBGjAsCKwFBbDlVNtEMlzw==
-
-tiny-warning@^1.0.0:
- version "1.0.3"
- resolved "https://registry.yarnpkg.com/tiny-warning/-/tiny-warning-1.0.3.tgz#94a30db453df4c643d0fd566060d60a875d84754"
- integrity sha512-lBN9zLN/oAf68o3zNXYrdCt1kP8WsiGW8Oo2ka41b2IM5JL/S1CTyX1rW0mb/zSuJun0ZUrDxx4sqvYS2FWzPA==
-
-to-fast-properties@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/to-fast-properties/-/to-fast-properties-2.0.0.tgz#dc5e698cbd079265bc73e0377681a4e4e83f616e"
- integrity sha512-/OaKK0xYrs3DmxRYqL/yDc+FxFUVYhDlXMhRmv3z915w2HF1tnN1omB354j8VUGO/hbRzyD6Y3sA7v7GS/ceog==
-
-to-readable-stream@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/to-readable-stream/-/to-readable-stream-1.0.0.tgz#ce0aa0c2f3df6adf852efb404a783e77c0475771"
- integrity sha512-Iq25XBt6zD5npPhlLVXGFN3/gyR2/qODcKNNyTMd4vbm39HUaOiAM4PMq0eMVC/Tkxz+Zjdsc55g9yyz+Yq00Q==
-
-to-regex-range@^5.0.1:
- version "5.0.1"
- resolved "https://registry.yarnpkg.com/to-regex-range/-/to-regex-range-5.0.1.tgz#1648c44aae7c8d988a326018ed72f5b4dd0392e4"
- integrity sha512-65P7iz6X5yEr1cwcgvQxbbIw7Uk3gOy5dIdtZ4rDveLqhrdJP+Li/Hx6tyK0NEb+2GCyneCMJiGqrADCSNk8sQ==
- dependencies:
- is-number "^7.0.0"
-
-to-vfile@^7.0.0:
- version "7.2.4"
- resolved "https://registry.yarnpkg.com/to-vfile/-/to-vfile-7.2.4.tgz#b97ecfcc15905ffe020bc975879053928b671378"
- integrity sha512-2eQ+rJ2qGbyw3senPI0qjuM7aut8IYXK6AEoOWb+fJx/mQYzviTckm1wDjq91QYHAPBTYzmdJXxMFA6Mk14mdw==
- dependencies:
- is-buffer "^2.0.0"
- vfile "^5.1.0"
-
-toidentifier@1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/toidentifier/-/toidentifier-1.0.1.tgz#3be34321a88a820ed1bd80dfaa33e479fbb8dd35"
- integrity sha512-o5sSPKEkg/DIQNmH43V0/uerLrpzVedkUh8tGNvaeXpfpuwjKenlSox/2O/BTlZUtEe+JG7s5YhEz608PlAHRA==
-
-totalist@^1.0.0:
- version "1.1.0"
- resolved "https://registry.yarnpkg.com/totalist/-/totalist-1.1.0.tgz#a4d65a3e546517701e3e5c37a47a70ac97fe56df"
- integrity sha512-gduQwd1rOdDMGxFG1gEvhV88Oirdo2p+KjoYFU7k2g+i7n6AFFbDQ5kMPUsW0pNbfQsB/cwXvT1i4Bue0s9g5g==
-
-tr46@~0.0.3:
- version "0.0.3"
- resolved "https://registry.yarnpkg.com/tr46/-/tr46-0.0.3.tgz#8184fd347dac9cdc185992f3a6622e14b9d9ab6a"
- integrity sha512-N3WMsuqV66lT30CrXNbEjx4GEwlow3v6rr4mCcv6prnfwhS01rkgyFdjPNBYd9br7LpXV1+Emh01fHnq2Gdgrw==
-
-trim-trailing-lines@^1.0.0:
- version "1.1.4"
- resolved "https://registry.yarnpkg.com/trim-trailing-lines/-/trim-trailing-lines-1.1.4.tgz#bd4abbec7cc880462f10b2c8b5ce1d8d1ec7c2c0"
- integrity sha512-rjUWSqnfTNrjbB9NQWfPMH/xRK1deHeGsHoVfpxJ++XeYXE0d6B1En37AHfw3jtfTU7dzMzZL2jjpe8Qb5gLIQ==
-
-trim@0.0.1:
- version "0.0.1"
- resolved "https://registry.yarnpkg.com/trim/-/trim-0.0.1.tgz#5858547f6b290757ee95cccc666fb50084c460dd"
- integrity sha512-YzQV+TZg4AxpKxaTHK3c3D+kRDCGVEE7LemdlQZoQXn0iennk10RsIoY6ikzAqJTc9Xjl9C1/waHom/J86ziAQ==
-
-trough@^1.0.0:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/trough/-/trough-1.0.5.tgz#b8b639cefad7d0bb2abd37d433ff8293efa5f406"
- integrity sha512-rvuRbTarPXmMb79SmzEp8aqXNKcK+y0XaB298IXueQ8I2PsrATcPBCSPyK/dDNa2iWOhKlfNnOjdAOTBU/nkFA==
-
-trough@^2.0.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/trough/-/trough-2.1.0.tgz#0f7b511a4fde65a46f18477ab38849b22c554876"
- integrity sha512-AqTiAOLcj85xS7vQ8QkAV41hPDIJ71XJB4RCUrzo/1GM2CQwhkJGaf9Hgr7BOugMRpgGUrqRg/DrBDl4H40+8g==
-
-tslib@^2.0.3, tslib@^2.1.0, tslib@^2.4.0:
- version "2.5.0"
- resolved "https://registry.yarnpkg.com/tslib/-/tslib-2.5.0.tgz#42bfed86f5787aeb41d031866c8f402429e0fddf"
- integrity sha512-336iVw3rtn2BUK7ORdIAHTyxHGRIHVReokCR3XjbckJMK7ms8FysBfhLR8IXnAgy7T0PTPNBWKiH514FOW/WSg==
-
-type-fest@^0.20.2:
- version "0.20.2"
- resolved "https://registry.yarnpkg.com/type-fest/-/type-fest-0.20.2.tgz#1bf207f4b28f91583666cb5fbd327887301cd5f4"
- integrity sha512-Ne+eE4r0/iWnpAxD852z3A+N0Bt5RN//NjJwRd2VFHEmrywxf5vsZlh4R6lixl6B+wz/8d+maTSAkN1FIkI3LQ==
-
-type-fest@^2.5.0:
- version "2.19.0"
- resolved "https://registry.yarnpkg.com/type-fest/-/type-fest-2.19.0.tgz#88068015bb33036a598b952e55e9311a60fd3a9b"
- integrity sha512-RAH822pAdBgcNMAfWnCBU3CFZcfZ/i1eZjwFU/dsLKumyuuP3niueg2UAukXYF0E2AAoc82ZSSf9J0WQBinzHA==
-
-type-is@~1.6.18:
- version "1.6.18"
- resolved "https://registry.yarnpkg.com/type-is/-/type-is-1.6.18.tgz#4e552cd05df09467dcbc4ef739de89f2cf37c131"
- integrity sha512-TkRKr9sUTxEH8MdfuCSP7VizJyzRNMjj2J2do2Jr3Kym598JVdEksuzPQCnlFPW4ky9Q+iA+ma9BGm06XQBy8g==
- dependencies:
- media-typer "0.3.0"
- mime-types "~2.1.24"
-
-typedarray-to-buffer@^3.1.5:
- version "3.1.5"
- resolved "https://registry.yarnpkg.com/typedarray-to-buffer/-/typedarray-to-buffer-3.1.5.tgz#a97ee7a9ff42691b9f783ff1bc5112fe3fca9080"
- integrity sha512-zdu8XMNEDepKKR+XYOXAVPtWui0ly0NtohUscw+UmaHiAWT8hrV1rr//H6V+0DvJ3OQ19S979M0laLfX8rm82Q==
- dependencies:
- is-typedarray "^1.0.0"
-
-typedarray@^0.0.6:
- version "0.0.6"
- resolved "https://registry.yarnpkg.com/typedarray/-/typedarray-0.0.6.tgz#867ac74e3864187b1d3d47d996a78ec5c8830777"
- integrity sha512-/aCDEGatGvZ2BIk+HmLf4ifCJFwvKFNb9/JeZPMulfgFracn9QFcAf5GO8B/mweUjSoblS5In0cWhqpfs/5PQA==
-
-typescript@^4.7.4:
- version "4.9.5"
- resolved "https://registry.yarnpkg.com/typescript/-/typescript-4.9.5.tgz#095979f9bcc0d09da324d58d03ce8f8374cbe65a"
- integrity sha512-1FXk9E2Hm+QzZQ7z+McJiHL4NW1F2EzMu9Nq9i3zAaGqibafqYwCVU6WyWAuyQRRzOlxou8xZSyXLEN8oKj24g==
-
-ua-parser-js@^0.7.30:
- version "0.7.33"
- resolved "https://registry.yarnpkg.com/ua-parser-js/-/ua-parser-js-0.7.33.tgz#1d04acb4ccef9293df6f70f2c3d22f3030d8b532"
- integrity sha512-s8ax/CeZdK9R/56Sui0WM6y9OFREJarMRHqLB2EwkovemBxNQ+Bqu8GAsUnVcXKgphb++ghr/B2BZx4mahujPw==
-
-uc.micro@^1.0.1, uc.micro@^1.0.5:
- version "1.0.6"
- resolved "https://registry.yarnpkg.com/uc.micro/-/uc.micro-1.0.6.tgz#9c411a802a409a91fc6cf74081baba34b24499ac"
- integrity sha512-8Y75pvTYkLJW2hWQHXxoqRgV7qb9B+9vFEtidML+7koHUFapnVJAZ6cKs+Qjz5Aw3aZWHMC6u0wJE3At+nSGwA==
-
-unherit@^1.0.4:
- version "1.1.3"
- resolved "https://registry.yarnpkg.com/unherit/-/unherit-1.1.3.tgz#6c9b503f2b41b262330c80e91c8614abdaa69c22"
- integrity sha512-Ft16BJcnapDKp0+J/rqFC3Rrk6Y/Ng4nzsC028k2jdDII/rdZ7Wd3pPT/6+vIIxRagwRc9K0IUX0Ra4fKvw+WQ==
- dependencies:
- inherits "^2.0.0"
- xtend "^4.0.0"
-
-unicode-canonical-property-names-ecmascript@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/unicode-canonical-property-names-ecmascript/-/unicode-canonical-property-names-ecmascript-2.0.0.tgz#301acdc525631670d39f6146e0e77ff6bbdebddc"
- integrity sha512-yY5PpDlfVIU5+y/BSCxAJRBIS1Zc2dDG3Ujq+sR0U+JjUevW2JhocOF+soROYDSaAezOzOKuyyixhD6mBknSmQ==
-
-unicode-match-property-ecmascript@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/unicode-match-property-ecmascript/-/unicode-match-property-ecmascript-2.0.0.tgz#54fd16e0ecb167cf04cf1f756bdcc92eba7976c3"
- integrity sha512-5kaZCrbp5mmbz5ulBkDkbY0SsPOjKqVS35VpL9ulMPfSl0J0Xsm+9Evphv9CoIZFwre7aJoa94AY6seMKGVN5Q==
- dependencies:
- unicode-canonical-property-names-ecmascript "^2.0.0"
- unicode-property-aliases-ecmascript "^2.0.0"
-
-unicode-match-property-value-ecmascript@^2.1.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/unicode-match-property-value-ecmascript/-/unicode-match-property-value-ecmascript-2.1.0.tgz#cb5fffdcd16a05124f5a4b0bf7c3770208acbbe0"
- integrity sha512-qxkjQt6qjg/mYscYMC0XKRn3Rh0wFPlfxB0xkt9CfyTvpX1Ra0+rAmdX2QyAobptSEvuy4RtpPRui6XkV+8wjA==
-
-unicode-property-aliases-ecmascript@^2.0.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/unicode-property-aliases-ecmascript/-/unicode-property-aliases-ecmascript-2.1.0.tgz#43d41e3be698bd493ef911077c9b131f827e8ccd"
- integrity sha512-6t3foTQI9qne+OZoVQB/8x8rk2k1eVy1gRXhV3oFQ5T6R1dqQ1xtin3XqSlx3+ATBkliTaR/hHyJBm+LVPNM8w==
-
-unified-args@^10.0.0:
- version "10.0.0"
- resolved "https://registry.yarnpkg.com/unified-args/-/unified-args-10.0.0.tgz#95994c5558fea83ff07006cb560fd88cdcf31134"
- integrity sha512-PqsqxwkXpGSLiMkbjNnKU33Ffm6gso6rAvz1TlBGzMBx3gpx7ewIhViBX8HEWmy0v7pebA5PM6RkRWWaYmtfYw==
- dependencies:
- "@types/text-table" "^0.2.0"
- camelcase "^7.0.0"
- chalk "^5.0.0"
- chokidar "^3.0.0"
- fault "^2.0.0"
- json5 "^2.0.0"
- minimist "^1.0.0"
- text-table "^0.2.0"
- unified-engine "^10.0.0"
-
-unified-engine@^10.0.0:
- version "10.1.0"
- resolved "https://registry.yarnpkg.com/unified-engine/-/unified-engine-10.1.0.tgz#6899f00d1f53ee9af94f7abd0ec21242aae3f56c"
- integrity sha512-5+JDIs4hqKfHnJcVCxTid1yBoI/++FfF/1PFdSMpaftZZZY+qg2JFruRbf7PaIwa9KgLotXQV3gSjtY0IdcFGQ==
- dependencies:
- "@types/concat-stream" "^2.0.0"
- "@types/debug" "^4.0.0"
- "@types/is-empty" "^1.0.0"
- "@types/node" "^18.0.0"
- "@types/unist" "^2.0.0"
- concat-stream "^2.0.0"
- debug "^4.0.0"
- fault "^2.0.0"
- glob "^8.0.0"
- ignore "^5.0.0"
- is-buffer "^2.0.0"
- is-empty "^1.0.0"
- is-plain-obj "^4.0.0"
- load-plugin "^5.0.0"
- parse-json "^6.0.0"
- to-vfile "^7.0.0"
- trough "^2.0.0"
- unist-util-inspect "^7.0.0"
- vfile-message "^3.0.0"
- vfile-reporter "^7.0.0"
- vfile-statistics "^2.0.0"
- yaml "^2.0.0"
-
-unified-lint-rule@^2.0.0:
- version "2.1.1"
- resolved "https://registry.yarnpkg.com/unified-lint-rule/-/unified-lint-rule-2.1.1.tgz#2363f27064f0b44675d11119bb573a738e346f24"
- integrity sha512-vsLHyLZFstqtGse2gvrGwasOmH8M2y+r2kQMoDSWzSqUkQx2MjHjvZuGSv5FUaiv4RQO1bHRajy7lSGp7XWq5A==
- dependencies:
- "@types/unist" "^2.0.0"
- trough "^2.0.0"
- unified "^10.0.0"
- vfile "^5.0.0"
-
-unified-message-control@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/unified-message-control/-/unified-message-control-4.0.0.tgz#7cd313df526fc660f218b19a56377bb6957019a8"
- integrity sha512-1b92N+VkPHftOsvXNOtkJm4wHlr+UDmTBF2dUzepn40oy9NxanJ9xS1RwUBTjXJwqr2K0kMbEyv1Krdsho7+Iw==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^5.0.0"
- unist-util-visit "^3.0.0"
- vfile "^5.0.0"
- vfile-location "^4.0.0"
- vfile-message "^3.0.0"
-
-unified@9.2.0:
- version "9.2.0"
- resolved "https://registry.yarnpkg.com/unified/-/unified-9.2.0.tgz#67a62c627c40589edebbf60f53edfd4d822027f8"
- integrity sha512-vx2Z0vY+a3YoTj8+pttM3tiJHCwY5UFbYdiWrwBEbHmK8pvsPj2rtAX2BFfgXen8T39CJWblWRDT4L5WGXtDdg==
- dependencies:
- bail "^1.0.0"
- extend "^3.0.0"
- is-buffer "^2.0.0"
- is-plain-obj "^2.0.0"
- trough "^1.0.0"
- vfile "^4.0.0"
-
-unified@^10.0.0, unified@^10.1.0:
- version "10.1.2"
- resolved "https://registry.yarnpkg.com/unified/-/unified-10.1.2.tgz#b1d64e55dafe1f0b98bb6c719881103ecf6c86df"
- integrity sha512-pUSWAi/RAnVy1Pif2kAoeWNBa3JVrx0MId2LASj8G+7AiHWoKZNTomq6LG326T68U7/e263X6fTdcXIy7XnF7Q==
- dependencies:
- "@types/unist" "^2.0.0"
- bail "^2.0.0"
- extend "^3.0.0"
- is-buffer "^2.0.0"
- is-plain-obj "^4.0.0"
- trough "^2.0.0"
- vfile "^5.0.0"
-
-unified@^9.2.2:
- version "9.2.2"
- resolved "https://registry.yarnpkg.com/unified/-/unified-9.2.2.tgz#67649a1abfc3ab85d2969502902775eb03146975"
- integrity sha512-Sg7j110mtefBD+qunSLO1lqOEKdrwBFBrR6Qd8f4uwkhWNlbkaqwHse6e7QvD3AP/MNoJdEDLaf8OxYyoWgorQ==
- dependencies:
- bail "^1.0.0"
- extend "^3.0.0"
- is-buffer "^2.0.0"
- is-plain-obj "^2.0.0"
- trough "^1.0.0"
- vfile "^4.0.0"
-
-unique-string@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/unique-string/-/unique-string-2.0.0.tgz#39c6451f81afb2749de2b233e3f7c5e8843bd89d"
- integrity sha512-uNaeirEPvpZWSgzwsPGtU2zVSTrn/8L5q/IexZmH0eH6SA73CmAA5U4GwORTxQAZs95TAXLNqeLoPPNO5gZfWg==
- dependencies:
- crypto-random-string "^2.0.0"
-
-unist-builder@2.0.3, unist-builder@^2.0.0:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/unist-builder/-/unist-builder-2.0.3.tgz#77648711b5d86af0942f334397a33c5e91516436"
- integrity sha512-f98yt5pnlMWlzP539tPc4grGMsFaQQlP/vM396b00jngsiINumNmsY8rkXjfoi1c6QaM8nQ3vaGDuoKWbe/1Uw==
-
-unist-util-generated@^1.0.0:
- version "1.1.6"
- resolved "https://registry.yarnpkg.com/unist-util-generated/-/unist-util-generated-1.1.6.tgz#5ab51f689e2992a472beb1b35f2ce7ff2f324d4b"
- integrity sha512-cln2Mm1/CZzN5ttGK7vkoGw+RZ8VcUH6BtGbq98DDtRGquAAOXig1mrBQYelOwMXYS8rK+vZDyyojSjp7JX+Lg==
-
-unist-util-generated@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/unist-util-generated/-/unist-util-generated-2.0.1.tgz#e37c50af35d3ed185ac6ceacb6ca0afb28a85cae"
- integrity sha512-qF72kLmPxAw0oN2fwpWIqbXAVyEqUzDHMsbtPvOudIlUzXYFIeQIuxXQCRCFh22B7cixvU0MG7m3MW8FTq/S+A==
-
-unist-util-inspect@^7.0.0:
- version "7.0.2"
- resolved "https://registry.yarnpkg.com/unist-util-inspect/-/unist-util-inspect-7.0.2.tgz#858e4f02ee4053f7c6ada8bc81662901a0ee1893"
- integrity sha512-Op0XnmHUl6C2zo/yJCwhXQSm/SmW22eDZdWP2qdf4WpGrgO1ZxFodq+5zFyeRGasFjJotAnLgfuD1jkcKqiH1Q==
- dependencies:
- "@types/unist" "^2.0.0"
-
-unist-util-is@^4.0.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/unist-util-is/-/unist-util-is-4.1.0.tgz#976e5f462a7a5de73d94b706bac1b90671b57797"
- integrity sha512-ZOQSsnce92GrxSqlnEEseX0gi7GH9zTJZ0p9dtu87WRb/37mMPO2Ilx1s/t9vBHrFhbgweUwb+t7cIn5dxPhZg==
-
-unist-util-is@^5.0.0:
- version "5.2.0"
- resolved "https://registry.yarnpkg.com/unist-util-is/-/unist-util-is-5.2.0.tgz#37eed0617b76c114fd34d44c201aa96fd928b309"
- integrity sha512-Glt17jWwZeyqrFqOK0pF1Ded5U3yzJnFr8CG1GMjCWTp9zDo2p+cmD6pWbZU8AgM5WU3IzRv6+rBwhzsGh6hBQ==
-
-unist-util-position-from-estree@^1.0.0, unist-util-position-from-estree@^1.1.0:
- version "1.1.2"
- resolved "https://registry.yarnpkg.com/unist-util-position-from-estree/-/unist-util-position-from-estree-1.1.2.tgz#8ac2480027229de76512079e377afbcabcfcce22"
- integrity sha512-poZa0eXpS+/XpoQwGwl79UUdea4ol2ZuCYguVaJS4qzIOMDzbqz8a3erUCOmubSZkaOuGamb3tX790iwOIROww==
- dependencies:
- "@types/unist" "^2.0.0"
-
-unist-util-position@^3.0.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/unist-util-position/-/unist-util-position-3.1.0.tgz#1c42ee6301f8d52f47d14f62bbdb796571fa2d47"
- integrity sha512-w+PkwCbYSFw8vpgWD0v7zRCl1FpY3fjDSQ3/N/wNd9Ffa4gPi8+4keqt99N3XW6F99t/mUzp2xAhNmfKWp95QA==
-
-unist-util-position@^4.0.0:
- version "4.0.4"
- resolved "https://registry.yarnpkg.com/unist-util-position/-/unist-util-position-4.0.4.tgz#93f6d8c7d6b373d9b825844645877c127455f037"
- integrity sha512-kUBE91efOWfIVBo8xzh/uZQ7p9ffYRtUbMRZBNFYwf0RK8koUMx6dGUfwylLOKmaT2cs4wSW96QoYUSXAyEtpg==
- dependencies:
- "@types/unist" "^2.0.0"
-
-unist-util-remove-position@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/unist-util-remove-position/-/unist-util-remove-position-2.0.1.tgz#5d19ca79fdba712301999b2b73553ca8f3b352cc"
- integrity sha512-fDZsLYIe2uT+oGFnuZmy73K6ZxOPG/Qcm+w7jbEjaFcJgbQ6cqjs/eSPzXhsmGpAsWPkqZM9pYjww5QTn3LHMA==
- dependencies:
- unist-util-visit "^2.0.0"
-
-unist-util-remove-position@^4.0.0:
- version "4.0.2"
- resolved "https://registry.yarnpkg.com/unist-util-remove-position/-/unist-util-remove-position-4.0.2.tgz#a89be6ea72e23b1a402350832b02a91f6a9afe51"
- integrity sha512-TkBb0HABNmxzAcfLf4qsIbFbaPDvMO6wa3b3j4VcEzFVaw1LBKwnW4/sRJ/atSLSzoIg41JWEdnE7N6DIhGDGQ==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-visit "^4.0.0"
-
-unist-util-remove@^2.0.0:
- version "2.1.0"
- resolved "https://registry.yarnpkg.com/unist-util-remove/-/unist-util-remove-2.1.0.tgz#b0b4738aa7ee445c402fda9328d604a02d010588"
- integrity sha512-J8NYPyBm4baYLdCbjmf1bhPu45Cr1MWTm77qd9istEkzWpnN6O9tMsEbB2JhNnBCqGENRqEWomQ+He6au0B27Q==
- dependencies:
- unist-util-is "^4.0.0"
-
-unist-util-stringify-position@^2.0.0:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/unist-util-stringify-position/-/unist-util-stringify-position-2.0.3.tgz#cce3bfa1cdf85ba7375d1d5b17bdc4cada9bd9da"
- integrity sha512-3faScn5I+hy9VleOq/qNbAd6pAx7iH5jYBMS9I1HgQVijz/4mv5Bvw5iw1sC/90CODiKo81G/ps8AJrISn687g==
- dependencies:
- "@types/unist" "^2.0.2"
-
-unist-util-stringify-position@^3.0.0:
- version "3.0.3"
- resolved "https://registry.yarnpkg.com/unist-util-stringify-position/-/unist-util-stringify-position-3.0.3.tgz#03ad3348210c2d930772d64b489580c13a7db39d"
- integrity sha512-k5GzIBZ/QatR8N5X2y+drfpWG8IDBzdnVj6OInRNWm1oXrzydiaAT2OQiA8DPRRZyAKb9b6I2a6PxYklZD0gKg==
- dependencies:
- "@types/unist" "^2.0.0"
-
-unist-util-visit-parents@^3.0.0:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/unist-util-visit-parents/-/unist-util-visit-parents-3.1.1.tgz#65a6ce698f78a6b0f56aa0e88f13801886cdaef6"
- integrity sha512-1KROIZWo6bcMrZEwiH2UrXDyalAa0uqzWCxCJj6lPOvTve2WkfgCytoDTPaMnodXh1WrXOq0haVYHj99ynJlsg==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^4.0.0"
-
-unist-util-visit-parents@^4.0.0:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/unist-util-visit-parents/-/unist-util-visit-parents-4.1.1.tgz#e83559a4ad7e6048a46b1bdb22614f2f3f4724f2"
- integrity sha512-1xAFJXAKpnnJl8G7K5KgU7FY55y3GcLIXqkzUj5QF/QVP7biUm0K0O2oqVkYsdjzJKifYeWn9+o6piAK2hGSHw==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^5.0.0"
-
-unist-util-visit-parents@^5.1.1:
- version "5.1.3"
- resolved "https://registry.yarnpkg.com/unist-util-visit-parents/-/unist-util-visit-parents-5.1.3.tgz#b4520811b0ca34285633785045df7a8d6776cfeb"
- integrity sha512-x6+y8g7wWMyQhL1iZfhIPhDAs7Xwbn9nRosDXl7qoPTSCy0yNxnKc+hWokFifWQIDGi154rdUqKvbCa4+1kLhg==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^5.0.0"
-
-unist-util-visit@2.0.3, unist-util-visit@^2.0.0, unist-util-visit@^2.0.3:
- version "2.0.3"
- resolved "https://registry.yarnpkg.com/unist-util-visit/-/unist-util-visit-2.0.3.tgz#c3703893146df47203bb8a9795af47d7b971208c"
- integrity sha512-iJ4/RczbJMkD0712mGktuGpm/U4By4FfDonL7N/9tATGIF4imikjOuagyMY53tnZq3NP6BcmlrHhEKAfGWjh7Q==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^4.0.0"
- unist-util-visit-parents "^3.0.0"
-
-unist-util-visit@^3.0.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/unist-util-visit/-/unist-util-visit-3.1.0.tgz#9420d285e1aee938c7d9acbafc8e160186dbaf7b"
- integrity sha512-Szoh+R/Ll68QWAyQyZZpQzZQm2UPbxibDvaY8Xc9SUtYgPsDzx5AWSk++UUt2hJuow8mvwR+rG+LQLw+KsuAKA==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^5.0.0"
- unist-util-visit-parents "^4.0.0"
-
-unist-util-visit@^4.0.0:
- version "4.1.2"
- resolved "https://registry.yarnpkg.com/unist-util-visit/-/unist-util-visit-4.1.2.tgz#125a42d1eb876283715a3cb5cceaa531828c72e2"
- integrity sha512-MSd8OUGISqHdVvfY9TPhyK2VdUrPgxkUtWSuMHF6XAAFuL4LokseigBnZtPnJMu+FbynTkFNnFlyjxpVKujMRg==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-is "^5.0.0"
- unist-util-visit-parents "^5.1.1"
-
-universalify@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/universalify/-/universalify-2.0.0.tgz#75a4984efedc4b08975c5aeb73f530d02df25717"
- integrity sha512-hAZsKq7Yy11Zu1DE0OzWjw7nnLZmJZYTDZZyEFHZdUhV8FkH5MCfoU1XMaxXovpyW5nq5scPqq0ZDP9Zyl04oQ==
-
-unpipe@1.0.0, unpipe@~1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/unpipe/-/unpipe-1.0.0.tgz#b2bf4ee8514aae6165b4817829d21b2ef49904ec"
- integrity sha512-pjy2bYhSsufwWlKwPc+l3cN7+wuJlK6uz0YdJEOlQDbl6jo/YlPi4mb8agUkVC8BF7V8NuzeyPNqRksA3hztKQ==
-
-update-browserslist-db@^1.0.10:
- version "1.0.10"
- resolved "https://registry.yarnpkg.com/update-browserslist-db/-/update-browserslist-db-1.0.10.tgz#0f54b876545726f17d00cd9a2561e6dade943ff3"
- integrity sha512-OztqDenkfFkbSG+tRxBeAnCVPckDBcvibKd35yDONx6OU8N7sqgwc7rCbkJ/WcYtVRZ4ba68d6byhC21GFh7sQ==
- dependencies:
- escalade "^3.1.1"
- picocolors "^1.0.0"
-
-update-notifier@^5.1.0:
- version "5.1.0"
- resolved "https://registry.yarnpkg.com/update-notifier/-/update-notifier-5.1.0.tgz#4ab0d7c7f36a231dd7316cf7729313f0214d9ad9"
- integrity sha512-ItnICHbeMh9GqUy31hFPrD1kcuZ3rpxDZbf4KUDavXwS0bW5m7SLbDQpGX3UYr072cbrF5hFUs3r5tUsPwjfHw==
- dependencies:
- boxen "^5.0.0"
- chalk "^4.1.0"
- configstore "^5.0.1"
- has-yarn "^2.1.0"
- import-lazy "^2.1.0"
- is-ci "^2.0.0"
- is-installed-globally "^0.4.0"
- is-npm "^5.0.0"
- is-yarn-global "^0.3.0"
- latest-version "^5.1.0"
- pupa "^2.1.1"
- semver "^7.3.4"
- semver-diff "^3.1.1"
- xdg-basedir "^4.0.0"
-
-uri-js@^4.2.2:
- version "4.4.1"
- resolved "https://registry.yarnpkg.com/uri-js/-/uri-js-4.4.1.tgz#9b1a52595225859e55f669d928f88c6c57f2a77e"
- integrity sha512-7rKUyy33Q1yc98pQ1DAmLtwX109F7TIfWlW1Ydo8Wl1ii1SeHieeh0HHfPeL2fMXK6z0s8ecKs9frCuLJvndBg==
- dependencies:
- punycode "^2.1.0"
-
-url-loader@^4.1.1:
- version "4.1.1"
- resolved "https://registry.yarnpkg.com/url-loader/-/url-loader-4.1.1.tgz#28505e905cae158cf07c92ca622d7f237e70a4e2"
- integrity sha512-3BTV812+AVHHOJQO8O5MkWgZ5aosP7GnROJwvzLS9hWDj00lZ6Z0wNak423Lp9PBZN05N+Jk/N5Si8jRAlGyWA==
- dependencies:
- loader-utils "^2.0.0"
- mime-types "^2.1.27"
- schema-utils "^3.0.0"
-
-url-parse-lax@^3.0.0:
- version "3.0.0"
- resolved "https://registry.yarnpkg.com/url-parse-lax/-/url-parse-lax-3.0.0.tgz#16b5cafc07dbe3676c1b1999177823d6503acb0c"
- integrity sha512-NjFKA0DidqPa5ciFcSrXnAltTtzz84ogy+NebPvfEgAck0+TNg4UJ4IN+fB7zRZfbgUf0syOo9MDxFkDSMuFaQ==
- dependencies:
- prepend-http "^2.0.0"
-
-use-composed-ref@^1.3.0:
- version "1.3.0"
- resolved "https://registry.yarnpkg.com/use-composed-ref/-/use-composed-ref-1.3.0.tgz#3d8104db34b7b264030a9d916c5e94fbe280dbda"
- integrity sha512-GLMG0Jc/jiKov/3Ulid1wbv3r54K9HlMW29IWcDFPEqFkSO2nS0MuefWgMJpeHQ9YJeXDL3ZUF+P3jdXlZX/cQ==
-
-use-isomorphic-layout-effect@^1.1.1:
- version "1.1.2"
- resolved "https://registry.yarnpkg.com/use-isomorphic-layout-effect/-/use-isomorphic-layout-effect-1.1.2.tgz#497cefb13d863d687b08477d9e5a164ad8c1a6fb"
- integrity sha512-49L8yCO3iGT/ZF9QttjwLF/ZD9Iwto5LnH5LmEdk/6cFmXddqi2ulF0edxTwjj+7mqvpVVGQWvbXZdn32wRSHA==
-
-use-latest@^1.2.1:
- version "1.2.1"
- resolved "https://registry.yarnpkg.com/use-latest/-/use-latest-1.2.1.tgz#d13dfb4b08c28e3e33991546a2cee53e14038cf2"
- integrity sha512-xA+AVm/Wlg3e2P/JiItTziwS7FK92LWrDB0p+hgXloIMuVCeJJ8v6f0eeHyPZaJrM+usM1FkFfbNCrJGs8A/zw==
- dependencies:
- use-isomorphic-layout-effect "^1.1.1"
-
-use-sync-external-store@^1.2.0:
- version "1.2.0"
- resolved "https://registry.yarnpkg.com/use-sync-external-store/-/use-sync-external-store-1.2.0.tgz#7dbefd6ef3fe4e767a0cf5d7287aacfb5846928a"
- integrity sha512-eEgnFxGQ1Ife9bzYs6VLi8/4X6CObHMw9Qr9tPY43iKwsPw8xE8+EFsf/2cFZ5S3esXgpWgtSCtLNS41F+sKPA==
-
-util-deprecate@^1.0.1, util-deprecate@^1.0.2, util-deprecate@~1.0.1:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/util-deprecate/-/util-deprecate-1.0.2.tgz#450d4dc9fa70de732762fbd2d4a28981419a0ccf"
- integrity sha512-EPD5q1uXyFxJpCrLnCc1nHnq3gOa6DZBocAIiI2TaSCA7VCJ1UJDMagCzIkXNsUYfD1daK//LTEQ8xiIbrHtcw==
-
-utila@~0.4:
- version "0.4.0"
- resolved "https://registry.yarnpkg.com/utila/-/utila-0.4.0.tgz#8a16a05d445657a3aea5eecc5b12a4fa5379772c"
- integrity sha512-Z0DbgELS9/L/75wZbro8xAnT50pBVFQZ+hUEueGDU5FN51YSCYM+jdxsfCiHjwNP/4LCDD0i/graKpeBnOXKRA==
-
-utility-types@^3.10.0:
- version "3.10.0"
- resolved "https://registry.yarnpkg.com/utility-types/-/utility-types-3.10.0.tgz#ea4148f9a741015f05ed74fd615e1d20e6bed82b"
- integrity sha512-O11mqxmi7wMKCo6HKFt5AhO4BwY3VV68YU07tgxfz8zJTIxr4BpsezN49Ffwy9j3ZpwwJp4fkRwjRzq3uWE6Rg==
-
-utils-merge@1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/utils-merge/-/utils-merge-1.0.1.tgz#9f95710f50a267947b2ccc124741c1028427e713"
- integrity sha512-pMZTvIkT1d+TFGvDOqodOclx0QWkkgi6Tdoa8gC8ffGAAqz9pzPTZWAybbsHHoED/ztMtkv/VoYTYyShUn81hA==
-
-uuid@^8.3.2:
- version "8.3.2"
- resolved "https://registry.yarnpkg.com/uuid/-/uuid-8.3.2.tgz#80d5b5ced271bb9af6c445f21a1a04c606cefbe2"
- integrity sha512-+NYs2QeMWy+GWFOEm9xnn6HCDp0l7QBD7ml8zLUmJ+93Q5NF0NocErnwkTkXVFNiX3/fpC6afS8Dhb/gz7R7eg==
-
-uvu@^0.5.0:
- version "0.5.6"
- resolved "https://registry.yarnpkg.com/uvu/-/uvu-0.5.6.tgz#2754ca20bcb0bb59b64e9985e84d2e81058502df"
- integrity sha512-+g8ENReyr8YsOc6fv/NVJs2vFdHBnBNdfE49rshrTzDWOlUx4Gq7KOS2GD8eqhy2j+Ejq29+SbKH8yjkAqXqoA==
- dependencies:
- dequal "^2.0.0"
- diff "^5.0.0"
- kleur "^4.0.3"
- sade "^1.7.3"
-
-value-equal@^1.0.1:
- version "1.0.1"
- resolved "https://registry.yarnpkg.com/value-equal/-/value-equal-1.0.1.tgz#1e0b794c734c5c0cade179c437d356d931a34d6c"
- integrity sha512-NOJ6JZCAWr0zlxZt+xqCHNTEKOsrks2HQd4MqhP1qy4z1SkbEP467eNx6TgDKXMvUOb+OENfJCZwM+16n7fRfw==
-
-vary@~1.1.2:
- version "1.1.2"
- resolved "https://registry.yarnpkg.com/vary/-/vary-1.1.2.tgz#2299f02c6ded30d4a5961b0b9f74524a18f634fc"
- integrity sha512-BNGbWLfd0eUPabhkXUVm0j8uuvREyTh5ovRa/dyow/BqAbZJyC+5fU+IzQOzmAKzYqYRAISoRhdQr3eIZ/PXqg==
-
-vfile-location@^3.0.0, vfile-location@^3.2.0:
- version "3.2.0"
- resolved "https://registry.yarnpkg.com/vfile-location/-/vfile-location-3.2.0.tgz#d8e41fbcbd406063669ebf6c33d56ae8721d0f3c"
- integrity sha512-aLEIZKv/oxuCDZ8lkJGhuhztf/BW4M+iHdCwglA/eWc+vtuRFJj8EtgceYFX4LRjOhCAAiNHsKGssC6onJ+jbA==
-
-vfile-location@^4.0.0:
- version "4.1.0"
- resolved "https://registry.yarnpkg.com/vfile-location/-/vfile-location-4.1.0.tgz#69df82fb9ef0a38d0d02b90dd84620e120050dd0"
- integrity sha512-YF23YMyASIIJXpktBa4vIGLJ5Gs88UB/XePgqPmTa7cDA+JeO3yclbpheQYCHjVHBn/yePzrXuygIL+xbvRYHw==
- dependencies:
- "@types/unist" "^2.0.0"
- vfile "^5.0.0"
-
-vfile-message@^2.0.0:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/vfile-message/-/vfile-message-2.0.4.tgz#5b43b88171d409eae58477d13f23dd41d52c371a"
- integrity sha512-DjssxRGkMvifUOJre00juHoP9DPWuzjxKuMDrhNbk2TdaYYBNMStsNhEOt3idrtI12VQYM/1+iM0KOzXi4pxwQ==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-stringify-position "^2.0.0"
-
-vfile-message@^3.0.0:
- version "3.1.4"
- resolved "https://registry.yarnpkg.com/vfile-message/-/vfile-message-3.1.4.tgz#15a50816ae7d7c2d1fa87090a7f9f96612b59dea"
- integrity sha512-fa0Z6P8HUrQN4BZaX05SIVXic+7kE3b05PWAtPuYP9QLHsLKYR7/AlLW3NtOrpXRLeawpDLMsVkmk5DG0NXgWw==
- dependencies:
- "@types/unist" "^2.0.0"
- unist-util-stringify-position "^3.0.0"
-
-vfile-reporter@^7.0.0:
- version "7.0.5"
- resolved "https://registry.yarnpkg.com/vfile-reporter/-/vfile-reporter-7.0.5.tgz#a0cbf3922c08ad428d6db1161ec64a53b5725785"
- integrity sha512-NdWWXkv6gcd7AZMvDomlQbK3MqFWL1RlGzMn++/O2TI+68+nqxCPTvLugdOtfSzXmjh+xUyhp07HhlrbJjT+mw==
- dependencies:
- "@types/supports-color" "^8.0.0"
- string-width "^5.0.0"
- supports-color "^9.0.0"
- unist-util-stringify-position "^3.0.0"
- vfile "^5.0.0"
- vfile-message "^3.0.0"
- vfile-sort "^3.0.0"
- vfile-statistics "^2.0.0"
-
-vfile-sort@^3.0.0:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/vfile-sort/-/vfile-sort-3.0.1.tgz#4b06ec63e2946749b0bb514e736554cd75e441a2"
- integrity sha512-1os1733XY6y0D5x0ugqSeaVJm9lYgj0j5qdcZQFyxlZOSy1jYarL77lLyb5gK4Wqr1d5OxmuyflSO3zKyFnTFw==
- dependencies:
- vfile "^5.0.0"
- vfile-message "^3.0.0"
-
-vfile-statistics@^2.0.0:
- version "2.0.1"
- resolved "https://registry.yarnpkg.com/vfile-statistics/-/vfile-statistics-2.0.1.tgz#2e1adae1cd3a45c1ed4f2a24bd103c3d71e4bce3"
- integrity sha512-W6dkECZmP32EG/l+dp2jCLdYzmnDBIw6jwiLZSER81oR5AHRcVqL+k3Z+pfH1R73le6ayDkJRMk0sutj1bMVeg==
- dependencies:
- vfile "^5.0.0"
- vfile-message "^3.0.0"
-
-vfile@^4.0.0:
- version "4.2.1"
- resolved "https://registry.yarnpkg.com/vfile/-/vfile-4.2.1.tgz#03f1dce28fc625c625bc6514350fbdb00fa9e624"
- integrity sha512-O6AE4OskCG5S1emQ/4gl8zK586RqA3srz3nfK/Viy0UPToBc5Trp9BVFb1u0CjsKrAWwnpr4ifM/KBXPWwJbCA==
- dependencies:
- "@types/unist" "^2.0.0"
- is-buffer "^2.0.0"
- unist-util-stringify-position "^2.0.0"
- vfile-message "^2.0.0"
-
-vfile@^5.0.0, vfile@^5.1.0:
- version "5.3.7"
- resolved "https://registry.yarnpkg.com/vfile/-/vfile-5.3.7.tgz#de0677e6683e3380fafc46544cfe603118826ab7"
- integrity sha512-r7qlzkgErKjobAmyNIkkSpizsFPYiUPuJb5pNW1RB4JcYVZhs4lIbVqk8XPk033CV/1z8ss5pkax8SuhGpcG8g==
- dependencies:
- "@types/unist" "^2.0.0"
- is-buffer "^2.0.0"
- unist-util-stringify-position "^3.0.0"
- vfile-message "^3.0.0"
-
-wait-on@^6.0.1:
- version "6.0.1"
- resolved "https://registry.yarnpkg.com/wait-on/-/wait-on-6.0.1.tgz#16bbc4d1e4ebdd41c5b4e63a2e16dbd1f4e5601e"
- integrity sha512-zht+KASY3usTY5u2LgaNqn/Cd8MukxLGjdcZxT2ns5QzDmTFc4XoWBgC+C/na+sMRZTuVygQoMYwdcVjHnYIVw==
- dependencies:
- axios "^0.25.0"
- joi "^17.6.0"
- lodash "^4.17.21"
- minimist "^1.2.5"
- rxjs "^7.5.4"
-
-walk-up-path@^1.0.0:
- version "1.0.0"
- resolved "https://registry.yarnpkg.com/walk-up-path/-/walk-up-path-1.0.0.tgz#d4745e893dd5fd0dbb58dd0a4c6a33d9c9fec53e"
- integrity sha512-hwj/qMDUEjCU5h0xr90KGCf0tg0/LgJbmOWgrWKYlcJZM7XvquvUJZ0G/HMGr7F7OQMOUuPHWP9JpriinkAlkg==
-
-watchpack@^2.4.0:
- version "2.4.0"
- resolved "https://registry.yarnpkg.com/watchpack/-/watchpack-2.4.0.tgz#fa33032374962c78113f93c7f2fb4c54c9862a5d"
- integrity sha512-Lcvm7MGST/4fup+ifyKi2hjyIAwcdI4HRgtvTpIUxBRhB+RFtUh8XtDOxUfctVCnhVi+QQj49i91OyvzkJl6cg==
- dependencies:
- glob-to-regexp "^0.4.1"
- graceful-fs "^4.1.2"
-
-wbuf@^1.1.0, wbuf@^1.7.3:
- version "1.7.3"
- resolved "https://registry.yarnpkg.com/wbuf/-/wbuf-1.7.3.tgz#c1d8d149316d3ea852848895cb6a0bfe887b87df"
- integrity sha512-O84QOnr0icsbFGLS0O3bI5FswxzRr8/gHwWkDlQFskhSPryQXvrTMxjxGP4+iWYoauLoBvfDpkrOauZ+0iZpDA==
- dependencies:
- minimalistic-assert "^1.0.0"
-
-web-namespaces@^1.0.0:
- version "1.1.4"
- resolved "https://registry.yarnpkg.com/web-namespaces/-/web-namespaces-1.1.4.tgz#bc98a3de60dadd7faefc403d1076d529f5e030ec"
- integrity sha512-wYxSGajtmoP4WxfejAPIr4l0fVh+jeMXZb08wNc0tMg6xsfZXj3cECqIK0G7ZAqUq0PP8WlMDtaOGVBTAWztNw==
-
-webidl-conversions@^3.0.0:
- version "3.0.1"
- resolved "https://registry.yarnpkg.com/webidl-conversions/-/webidl-conversions-3.0.1.tgz#24534275e2a7bc6be7bc86611cc16ae0a5654871"
- integrity sha512-2JAn3z8AR6rjK8Sm8orRC0h/bcl/DqL7tRPdGZ4I1CjdF+EaMLmYxBHyXuKL849eucPFhvBoxMsflfOb8kxaeQ==
-
-webpack-bundle-analyzer@^4.5.0:
- version "4.8.0"
- resolved "https://registry.yarnpkg.com/webpack-bundle-analyzer/-/webpack-bundle-analyzer-4.8.0.tgz#951b8aaf491f665d2ae325d8b84da229157b1d04"
- integrity sha512-ZzoSBePshOKhr+hd8u6oCkZVwpVaXgpw23ScGLFpR6SjYI7+7iIWYarjN6OEYOfRt8o7ZyZZQk0DuMizJ+LEIg==
- dependencies:
- "@discoveryjs/json-ext" "0.5.7"
- acorn "^8.0.4"
- acorn-walk "^8.0.0"
- chalk "^4.1.0"
- commander "^7.2.0"
- gzip-size "^6.0.0"
- lodash "^4.17.20"
- opener "^1.5.2"
- sirv "^1.0.7"
- ws "^7.3.1"
-
-webpack-dev-middleware@^5.3.1:
- version "5.3.3"
- resolved "https://registry.yarnpkg.com/webpack-dev-middleware/-/webpack-dev-middleware-5.3.3.tgz#efae67c2793908e7311f1d9b06f2a08dcc97e51f"
- integrity sha512-hj5CYrY0bZLB+eTO+x/j67Pkrquiy7kWepMHmUMoPsmcUaeEnQJqFzHJOyxgWlq746/wUuA64p9ta34Kyb01pA==
- dependencies:
- colorette "^2.0.10"
- memfs "^3.4.3"
- mime-types "^2.1.31"
- range-parser "^1.2.1"
- schema-utils "^4.0.0"
-
-webpack-dev-server@^4.9.3:
- version "4.11.1"
- resolved "https://registry.yarnpkg.com/webpack-dev-server/-/webpack-dev-server-4.11.1.tgz#ae07f0d71ca0438cf88446f09029b92ce81380b5"
- integrity sha512-lILVz9tAUy1zGFwieuaQtYiadImb5M3d+H+L1zDYalYoDl0cksAB1UNyuE5MMWJrG6zR1tXkCP2fitl7yoUJiw==
- dependencies:
- "@types/bonjour" "^3.5.9"
- "@types/connect-history-api-fallback" "^1.3.5"
- "@types/express" "^4.17.13"
- "@types/serve-index" "^1.9.1"
- "@types/serve-static" "^1.13.10"
- "@types/sockjs" "^0.3.33"
- "@types/ws" "^8.5.1"
- ansi-html-community "^0.0.8"
- bonjour-service "^1.0.11"
- chokidar "^3.5.3"
- colorette "^2.0.10"
- compression "^1.7.4"
- connect-history-api-fallback "^2.0.0"
- default-gateway "^6.0.3"
- express "^4.17.3"
- graceful-fs "^4.2.6"
- html-entities "^2.3.2"
- http-proxy-middleware "^2.0.3"
- ipaddr.js "^2.0.1"
- open "^8.0.9"
- p-retry "^4.5.0"
- rimraf "^3.0.2"
- schema-utils "^4.0.0"
- selfsigned "^2.1.1"
- serve-index "^1.9.1"
- sockjs "^0.3.24"
- spdy "^4.0.2"
- webpack-dev-middleware "^5.3.1"
- ws "^8.4.2"
-
-webpack-merge@^5.8.0:
- version "5.8.0"
- resolved "https://registry.yarnpkg.com/webpack-merge/-/webpack-merge-5.8.0.tgz#2b39dbf22af87776ad744c390223731d30a68f61"
- integrity sha512-/SaI7xY0831XwP6kzuwhKWVKDP9t1QY1h65lAFLbZqMPIuYcD9QAW4u9STIbU9kaJbPBB/geU/gLr1wDjOhQ+Q==
- dependencies:
- clone-deep "^4.0.1"
- wildcard "^2.0.0"
-
-webpack-sources@^3.2.2, webpack-sources@^3.2.3:
- version "3.2.3"
- resolved "https://registry.yarnpkg.com/webpack-sources/-/webpack-sources-3.2.3.tgz#2d4daab8451fd4b240cc27055ff6a0c2ccea0cde"
- integrity sha512-/DyMEOrDgLKKIG0fmvtz+4dUX/3Ghozwgm6iPp8KRhvn+eQf9+Q7GWxVNMk3+uCPWfdXYC4ExGBckIXdFEfH1w==
-
-webpack@^5.73.0:
- version "5.75.0"
- resolved "https://registry.yarnpkg.com/webpack/-/webpack-5.75.0.tgz#1e440468647b2505860e94c9ff3e44d5b582c152"
- integrity sha512-piaIaoVJlqMsPtX/+3KTTO6jfvrSYgauFVdt8cr9LTHKmcq/AMd4mhzsiP7ZF/PGRNPGA8336jldh9l2Kt2ogQ==
- dependencies:
- "@types/eslint-scope" "^3.7.3"
- "@types/estree" "^0.0.51"
- "@webassemblyjs/ast" "1.11.1"
- "@webassemblyjs/wasm-edit" "1.11.1"
- "@webassemblyjs/wasm-parser" "1.11.1"
- acorn "^8.7.1"
- acorn-import-assertions "^1.7.6"
- browserslist "^4.14.5"
- chrome-trace-event "^1.0.2"
- enhanced-resolve "^5.10.0"
- es-module-lexer "^0.9.0"
- eslint-scope "5.1.1"
- events "^3.2.0"
- glob-to-regexp "^0.4.1"
- graceful-fs "^4.2.9"
- json-parse-even-better-errors "^2.3.1"
- loader-runner "^4.2.0"
- mime-types "^2.1.27"
- neo-async "^2.6.2"
- schema-utils "^3.1.0"
- tapable "^2.1.1"
- terser-webpack-plugin "^5.1.3"
- watchpack "^2.4.0"
- webpack-sources "^3.2.3"
-
-webpackbar@^5.0.2:
- version "5.0.2"
- resolved "https://registry.yarnpkg.com/webpackbar/-/webpackbar-5.0.2.tgz#d3dd466211c73852741dfc842b7556dcbc2b0570"
- integrity sha512-BmFJo7veBDgQzfWXl/wwYXr/VFus0614qZ8i9znqcl9fnEdiVkdbi0TedLQ6xAK92HZHDJ0QmyQ0fmuZPAgCYQ==
- dependencies:
- chalk "^4.1.0"
- consola "^2.15.3"
- pretty-time "^1.1.0"
- std-env "^3.0.1"
-
-websocket-driver@>=0.5.1, websocket-driver@^0.7.4:
- version "0.7.4"
- resolved "https://registry.yarnpkg.com/websocket-driver/-/websocket-driver-0.7.4.tgz#89ad5295bbf64b480abcba31e4953aca706f5760"
- integrity sha512-b17KeDIQVjvb0ssuSDF2cYXSg2iztliJ4B9WdsuB6J952qCPKmnVq4DyW5motImXHDC1cBT/1UezrJVsKw5zjg==
- dependencies:
- http-parser-js ">=0.5.1"
- safe-buffer ">=5.1.0"
- websocket-extensions ">=0.1.1"
-
-websocket-extensions@>=0.1.1:
- version "0.1.4"
- resolved "https://registry.yarnpkg.com/websocket-extensions/-/websocket-extensions-0.1.4.tgz#7f8473bc839dfd87608adb95d7eb075211578a42"
- integrity sha512-OqedPIGOfsDlo31UNwYbCFMSaO9m9G/0faIHj5/dZFDMFqPTcx6UwqyOy3COEaEOg/9VsGIpdqn62W5KhoKSpg==
-
-whatwg-url@^5.0.0:
- version "5.0.0"
- resolved "https://registry.yarnpkg.com/whatwg-url/-/whatwg-url-5.0.0.tgz#966454e8765462e37644d3626f6742ce8b70965d"
- integrity sha512-saE57nupxk6v3HY35+jzBwYa0rKSy0XR8JSxZPwgLr7ys0IBzhGviA1/TUGJLmSVqs8pb9AnvICXEuOHLprYTw==
- dependencies:
- tr46 "~0.0.3"
- webidl-conversions "^3.0.0"
-
-which@^1.3.1:
- version "1.3.1"
- resolved "https://registry.yarnpkg.com/which/-/which-1.3.1.tgz#a45043d54f5805316da8d62f9f50918d3da70b0a"
- integrity sha512-HxJdYWq1MTIQbJ3nw0cqssHoTNU267KlrDuGZ1WYlxDStUtKUhOaJmh112/TZmHxxUfuJqPXSOm7tDyas0OSIQ==
- dependencies:
- isexe "^2.0.0"
-
-which@^2.0.1:
- version "2.0.2"
- resolved "https://registry.yarnpkg.com/which/-/which-2.0.2.tgz#7c6a8dd0a636a0327e10b59c9286eee93f3f51b1"
- integrity sha512-BLI3Tl1TW3Pvl70l3yq3Y64i+awpwXqsGBYWkkqMtnbXgrMD+yj7rhW0kuEDxzJaYXGjEW5ogapKNMEKNMjibA==
- dependencies:
- isexe "^2.0.0"
-
-widest-line@^3.1.0:
- version "3.1.0"
- resolved "https://registry.yarnpkg.com/widest-line/-/widest-line-3.1.0.tgz#8292333bbf66cb45ff0de1603b136b7ae1496eca"
- integrity sha512-NsmoXalsWVDMGupxZ5R08ka9flZjjiLvHVAWYOKtiKM8ujtZWr9cRffak+uSE48+Ob8ObalXpwyeUiyDD6QFgg==
- dependencies:
- string-width "^4.0.0"
-
-widest-line@^4.0.1:
- version "4.0.1"
- resolved "https://registry.yarnpkg.com/widest-line/-/widest-line-4.0.1.tgz#a0fc673aaba1ea6f0a0d35b3c2795c9a9cc2ebf2"
- integrity sha512-o0cyEG0e8GPzT4iGHphIOh0cJOV8fivsXxddQasHPHfoZf1ZexrfeA21w2NaEN1RHE+fXlfISmOE8R9N3u3Qig==
- dependencies:
- string-width "^5.0.1"
-
-wildcard@^2.0.0:
- version "2.0.0"
- resolved "https://registry.yarnpkg.com/wildcard/-/wildcard-2.0.0.tgz#a77d20e5200c6faaac979e4b3aadc7b3dd7f8fec"
- integrity sha512-JcKqAHLPxcdb9KM49dufGXn2x3ssnfjbcaQdLlfZsL9rH9wgDQjUtDxbo8NE0F6SFvydeu1VhZe7hZuHsB2/pw==
-
-wrap-ansi@^7.0.0:
- version "7.0.0"
- resolved "https://registry.yarnpkg.com/wrap-ansi/-/wrap-ansi-7.0.0.tgz#67e145cff510a6a6984bdf1152911d69d2eb9e43"
- integrity sha512-YVGIj2kamLSTxw6NsZjoBxfSwsn0ycdesmc4p+Q21c5zPuZ1pl+NfxVdxPtdHvmNVOQ6XSYG4AUtyt/Fi7D16Q==
- dependencies:
- ansi-styles "^4.0.0"
- string-width "^4.1.0"
- strip-ansi "^6.0.0"
-
-wrap-ansi@^8.0.1:
- version "8.1.0"
- resolved "https://registry.yarnpkg.com/wrap-ansi/-/wrap-ansi-8.1.0.tgz#56dc22368ee570face1b49819975d9b9a5ead214"
- integrity sha512-si7QWI6zUMq56bESFvagtmzMdGOtoxfR+Sez11Mobfc7tm+VkUckk9bW2UeffTGVUbOksxmSw0AA2gs8g71NCQ==
- dependencies:
- ansi-styles "^6.1.0"
- string-width "^5.0.1"
- strip-ansi "^7.0.1"
-
-wrappy@1:
- version "1.0.2"
- resolved "https://registry.yarnpkg.com/wrappy/-/wrappy-1.0.2.tgz#b5243d8f3ec1aa35f1364605bc0d1036e30ab69f"
- integrity sha512-l4Sp/DRseor9wL6EvV2+TuQn63dMkPjZ/sp9XkghTEbV9KlPS1xUsZ3u7/IQO4wxtcFB4bgpQPRcR3QCvezPcQ==
-
-write-file-atomic@^3.0.0:
- version "3.0.3"
- resolved "https://registry.yarnpkg.com/write-file-atomic/-/write-file-atomic-3.0.3.tgz#56bd5c5a5c70481cd19c571bd39ab965a5de56e8"
- integrity sha512-AvHcyZ5JnSfq3ioSyjrBkH9yW4m7Ayk8/9My/DD9onKeu/94fwrMocemO2QAJFAlnnDN+ZDS+ZjAR5ua1/PV/Q==
- dependencies:
- imurmurhash "^0.1.4"
- is-typedarray "^1.0.0"
- signal-exit "^3.0.2"
- typedarray-to-buffer "^3.1.5"
-
-ws@^7.3.1:
- version "7.5.9"
- resolved "https://registry.yarnpkg.com/ws/-/ws-7.5.9.tgz#54fa7db29f4c7cec68b1ddd3a89de099942bb591"
- integrity sha512-F+P9Jil7UiSKSkppIiD94dN07AwvFixvLIj1Og1Rl9GGMuNipJnV9JzjD6XuqmAeiswGvUmNLjr5cFuXwNS77Q==
-
-ws@^8.4.2:
- version "8.12.1"
- resolved "https://registry.yarnpkg.com/ws/-/ws-8.12.1.tgz#c51e583d79140b5e42e39be48c934131942d4a8f"
- integrity sha512-1qo+M9Ba+xNhPB+YTWUlK6M17brTut5EXbcBaMRN5pH5dFrXz7lzz1ChFSUq3bOUl8yEvSenhHmYUNJxFzdJew==
-
-xdg-basedir@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/xdg-basedir/-/xdg-basedir-4.0.0.tgz#4bc8d9984403696225ef83a1573cbbcb4e79db13"
- integrity sha512-PSNhEJDejZYV7h50BohL09Er9VaIefr2LMAf3OEmpCkjOi34eYyQYAXUTjEQtZJTKcF0E2UKTh+osDLsgNim9Q==
-
-xml-js@^1.6.11:
- version "1.6.11"
- resolved "https://registry.yarnpkg.com/xml-js/-/xml-js-1.6.11.tgz#927d2f6947f7f1c19a316dd8eea3614e8b18f8e9"
- integrity sha512-7rVi2KMfwfWFl+GpPg6m80IVMWXLRjO+PxTq7V2CDhoGak0wzYzFgUY2m4XJ47OGdXd8eLE8EmwfAmdjw7lC1g==
- dependencies:
- sax "^1.2.4"
-
-xtend@^4.0.0, xtend@^4.0.1:
- version "4.0.2"
- resolved "https://registry.yarnpkg.com/xtend/-/xtend-4.0.2.tgz#bb72779f5fa465186b1f438f674fa347fdb5db54"
- integrity sha512-LKYU1iAXJXUgAXn9URjiu+MWhyUXHsvfp7mcuYm9dSUKK0/CjtrUwFAxD82/mCWbtLsGjFIad0wIsod4zrTAEQ==
-
-yallist@^3.0.2:
- version "3.1.1"
- resolved "https://registry.yarnpkg.com/yallist/-/yallist-3.1.1.tgz#dbb7daf9bfd8bac9ab45ebf602b8cbad0d5d08fd"
- integrity sha512-a4UGQaWPH59mOXUYnAG2ewncQS4i4F43Tv3JoAM+s2VDAmS9NsK8GpDMLrCHPksFT7h3K6TOoUNn2pb7RoXx4g==
-
-yallist@^4.0.0:
- version "4.0.0"
- resolved "https://registry.yarnpkg.com/yallist/-/yallist-4.0.0.tgz#9bb92790d9c0effec63be73519e11a35019a3a72"
- integrity sha512-3wdGidZyq5PB084XLES5TpOSRA3wjXAlIWMhum2kRcv/41Sn2emQ0dycQW4uZXLejwKvg6EsvbdlVL+FYEct7A==
-
-yaml@^1.10.0, yaml@^1.10.2, yaml@^1.7.2:
- version "1.10.2"
- resolved "https://registry.yarnpkg.com/yaml/-/yaml-1.10.2.tgz#2301c5ffbf12b467de8da2333a459e29e7920e4b"
- integrity sha512-r3vXyErRCYJ7wg28yvBY5VSoAF8ZvlcW9/BwUzEtUsjvX/DKs24dIkuwjtuprwJJHsbyUbLApepYTR1BN4uHrg==
-
-yaml@^2.0.0:
- version "2.2.1"
- resolved "https://registry.yarnpkg.com/yaml/-/yaml-2.2.1.tgz#3014bf0482dcd15147aa8e56109ce8632cd60ce4"
- integrity sha512-e0WHiYql7+9wr4cWMx3TVQrNwejKaEe7/rHNmQmqRjazfOP5W8PB6Jpebb5o6fIapbz9o9+2ipcaTM2ZwDI6lw==
-
-yocto-queue@^0.1.0:
- version "0.1.0"
- resolved "https://registry.yarnpkg.com/yocto-queue/-/yocto-queue-0.1.0.tgz#0294eb3dee05028d31ee1a5fa2c556a6aaf10a1b"
- integrity sha512-rVksvsnNCdJ/ohGc6xgPwyN8eheCxsiLM8mxuE/t/mOVqJewPuO1miLpTHQiRgTKCLexL4MeAFVagts7HmNZ2Q==
-
-zwitch@^1.0.0:
- version "1.0.5"
- resolved "https://registry.yarnpkg.com/zwitch/-/zwitch-1.0.5.tgz#d11d7381ffed16b742f6af7b3f223d5cd9fe9920"
- integrity sha512-V50KMwwzqJV0NpZIZFwfOD5/lyny3WlSzRiXgA0G7VUnRlqttta1L6UQIHzd6EuBY/cHGfwTIck7w1yH6Q5zUw==
-
-zwitch@^2.0.0:
- version "2.0.4"
- resolved "https://registry.yarnpkg.com/zwitch/-/zwitch-2.0.4.tgz#c827d4b0acb76fc3e685a4c6ec2902d51070e9d7"
- integrity sha512-bXE4cR/kVZhKZX/RjPEflHaKVhUVl85noU3v6b8apfQEc1x4A+zBxjZ4lN8LqGd6WZ3dl98pY4o717VFmoPp+A==
 -
- -
- -
- -
- -
- -
- -
- -
-