mirror of
https://github.com/outbackdingo/cozystack.git
synced 2026-01-29 18:19:00 +00:00
Compare commits
1 Commits
v0.2.0
...
project-do
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
236f3ce92f |
2
.gitignore
vendored
2
.gitignore
vendored
@@ -1,3 +1 @@
|
||||
_out
|
||||
.git
|
||||
.idea
|
||||
553
README.md
553
README.md
@@ -10,7 +10,7 @@
|
||||
|
||||
# Cozystack
|
||||
|
||||
**Cozystack** is a free PaaS platform and framework for building clouds.
|
||||
**Cozystack** is an open-source **PaaS platform** for cloud providers.
|
||||
|
||||
With Cozystack, you can transform your bunch of servers into an intelligent system with a simple REST API for spawning Kubernetes clusters, Database-as-a-Service, virtual machines, load balancers, HTTP caching services, and other services with ease.
|
||||
|
||||
@@ -18,55 +18,548 @@ You can use Cozystack to build your own cloud or to provide a cost-effective dev
|
||||
|
||||
## Use-Cases
|
||||
|
||||
* [**Using Cozystack to build public cloud**](https://cozystack.io/docs/use-cases/public-cloud/)
|
||||
You can use Cozystack as backend for a public cloud
|
||||
### As a backend for a public cloud
|
||||
|
||||
* [**Using Cozystack to build private cloud**](https://cozystack.io/docs/use-cases/private-cloud/)
|
||||
You can use Cozystack as platform to build a private cloud powered by Infrastructure-as-Code approach
|
||||
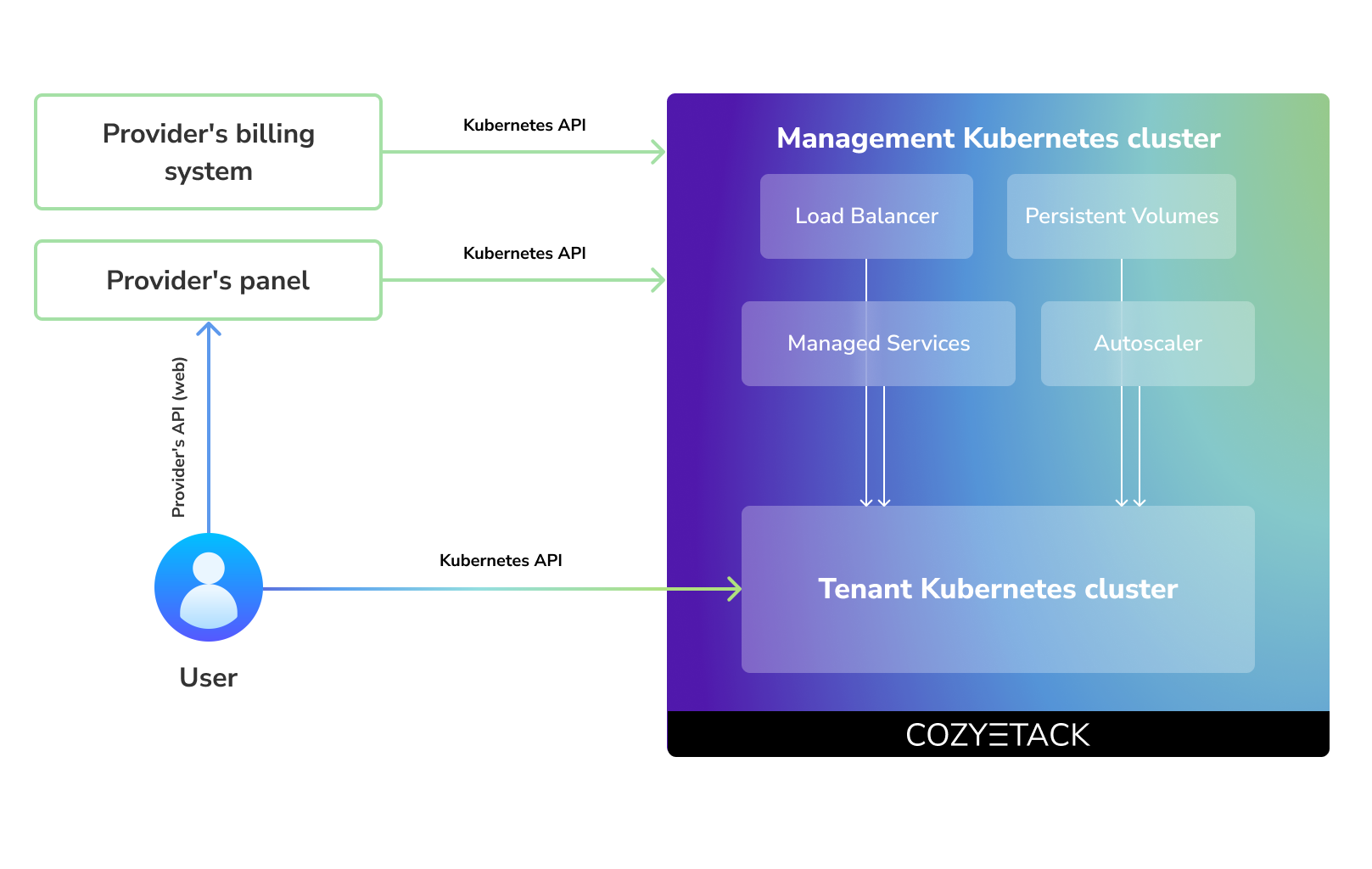
Cozystack positions itself as a kind of framework for building public clouds. The key word here is framework. In this case, it's important to understand that Cozystack is made for cloud providers, not for end users.
|
||||
|
||||
* [**Using Cozystack as Kubernetes distribution**](https://cozystack.io/docs/use-cases/kubernetes-distribution/)
|
||||
You can use Cozystack as Kubernetes distribution for Bare Metal
|
||||
Despite having a graphical interface, the current security model does not imply public user access to your management cluster.
|
||||
|
||||
Instead, end users get access to their own Kubernetes clusters, can order LoadBalancers and additional services from it, but they have no access and know nothing about your management cluster powered by Cozystack.
|
||||
|
||||
Thus, to integrate with your billing system, it's enough to teach your system to go to the management Kubernetes and place a YAML file signifying the service you're interested in. Cozystack will do the rest of the work for you.
|
||||
|
||||
|
||||
|
||||
### As a private cloud for Infrastructure-as-Code
|
||||
|
||||
One of the use cases is a self-portal for users within your company, where they can order the service they're interested in or a managed database.
|
||||
|
||||
You can implement best GitOps practices, where users will launch their own Kubernetes clusters and databases for their needs with a simple commit of configuration into your infrastructure Git repository.
|
||||
|
||||
Thanks to the standardization of the approach to deploying applications, you can expand the platform's capabilities using the functionality of standard Helm charts.
|
||||
|
||||
### As a Kubernetes distribution for Bare Metal
|
||||
|
||||
We created Cozystack primarily for our own needs, having vast experience in building reliable systems on bare metal infrastructure. This experience led to the formation of a separate boxed product, which is aimed at standardizing and providing a ready-to-use tool for managing your infrastructure.
|
||||
|
||||
Currently, Cozystack already solves a huge scope of infrastructure tasks: starting from provisioning bare metal servers, having a ready monitoring system, fast and reliable storage, a network fabric with the possibility of interconnect with your infrastructure, the ability to run virtual machines, databases, and much more right out of the box.
|
||||
|
||||
All this makes Cozystack a convenient platform for delivering and launching your application on Bare Metal.
|
||||
|
||||
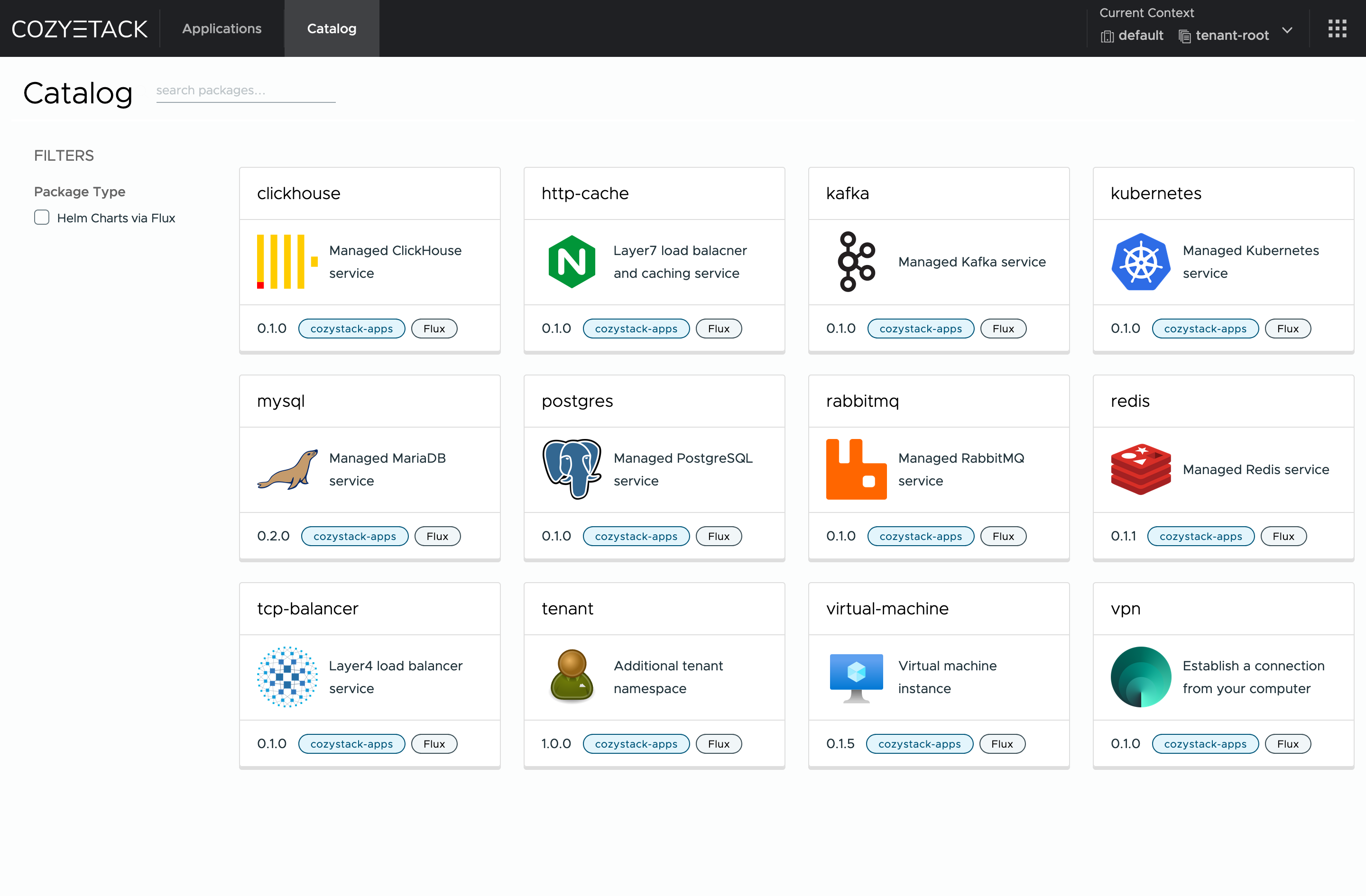
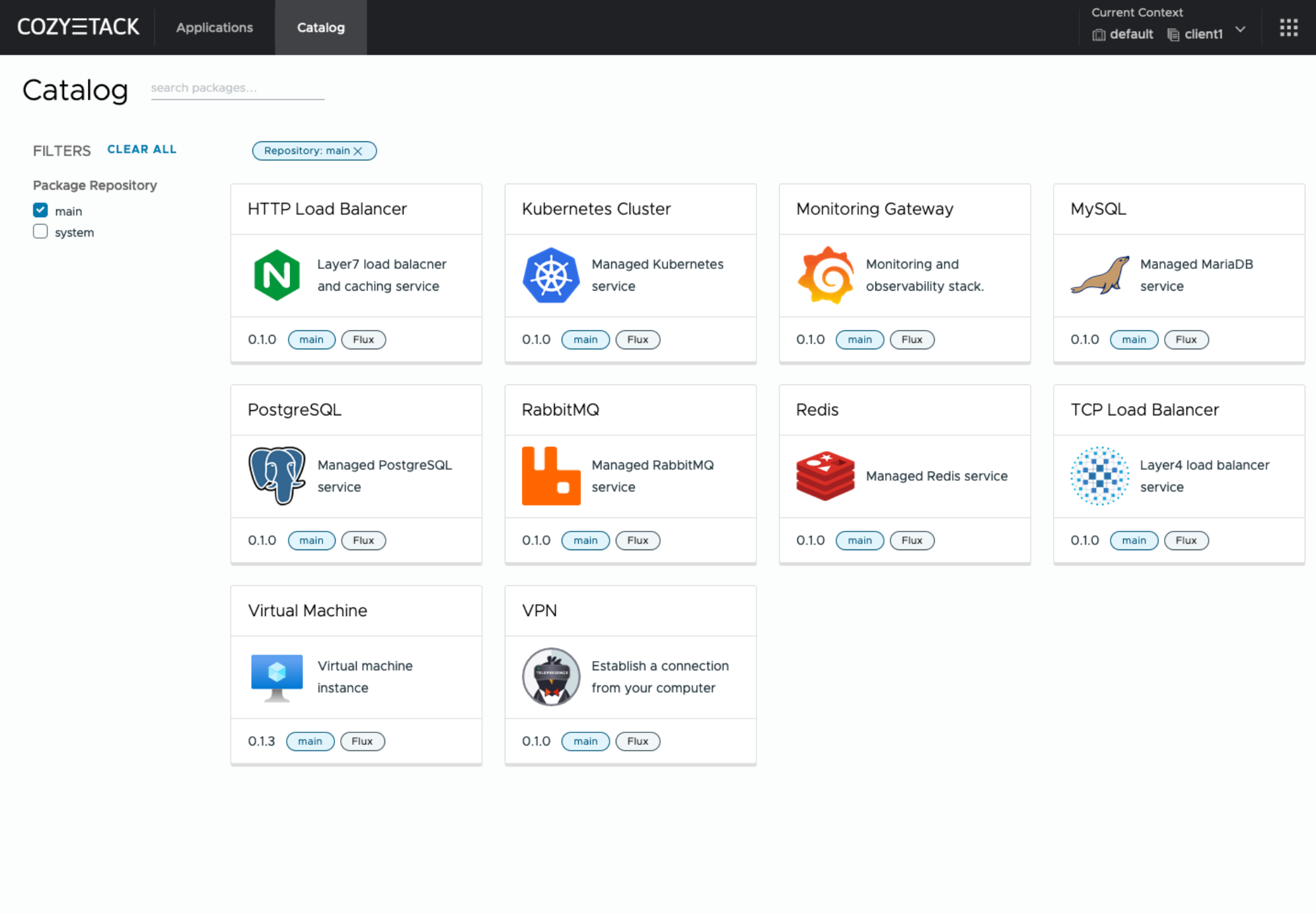
## Screenshot
|
||||
|
||||
|
||||
|
||||
|
||||
## Documentation
|
||||
## Core values
|
||||
|
||||
The documentation is located on official [cozystack.io](https://cozystack.io) website.
|
||||
### Standardization and unification
|
||||
All components of the platform are based on open source tools and technologies which are widely known in the industry.
|
||||
|
||||
Read [Get Started](https://cozystack.io/docs/get-started/) section for a quick start.
|
||||
### Collaborate, not compete
|
||||
If a feature being developed for the platform could be useful to a upstream project, it should be contributed to upstream project, rather than being implemented within the platform.
|
||||
|
||||
If you encounter any difficulties, start with the [troubleshooting guide](https://cozystack.io/docs/troubleshooting/), and work your way through the process that we've outlined.
|
||||
### API-first
|
||||
Cozystack is based on Kubernetes and involves close interaction with its API. We don't aim to completely hide the all elements behind a pretty UI or any sort of customizations; instead, we provide a standard interface and teach users how to work with basic primitives. The web interface is used solely for deploying applications and quickly diving into basic concepts of platform.
|
||||
|
||||
## Versioning
|
||||
## Quick Start
|
||||
|
||||
Versioning adheres to the [Semantic Versioning](http://semver.org/) principles.
|
||||
A full list of the available releases is available in the GitHub repository's [Release](https://github.com/aenix-io/cozystack/releases) section.
|
||||
### Prepare infrastructure
|
||||
|
||||
- [Roadmap](https://github.com/orgs/aenix-io/projects/2)
|
||||
|
||||
## Contributions
|
||||
|
||||
|
||||
Contributions are highly appreciated and very welcomed!
|
||||
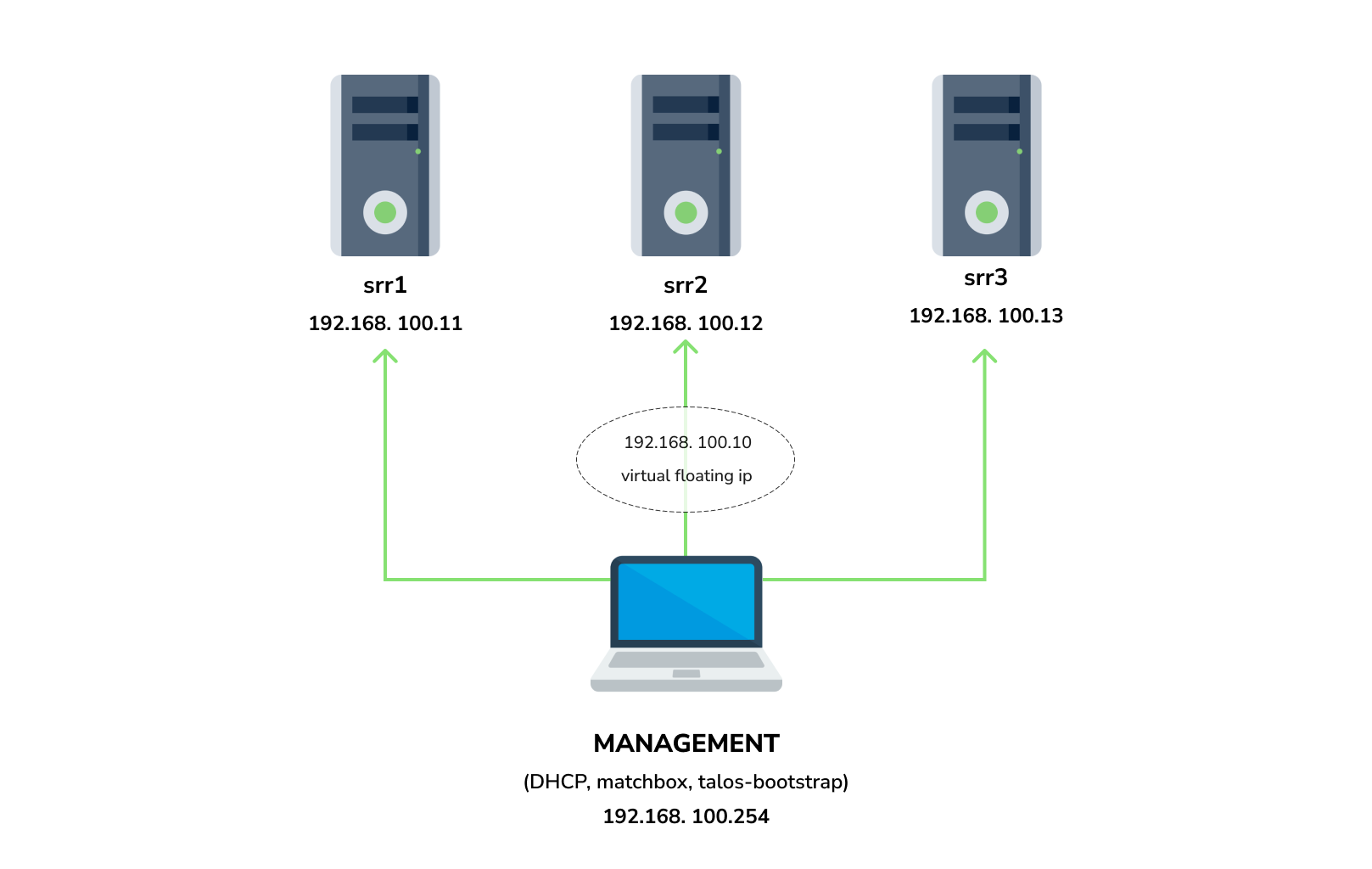
You need 3 physical servers or VMs with nested virtualisation:
|
||||
|
||||
In case of bugs, please, check if the issue has been already opened by checking the [GitHub Issues](https://github.com/aenix-io/cozystack/issues) section.
|
||||
In case it isn't, you can open a new one: a detailed report will help us to replicate it, assess it, and work on a fix.
|
||||
```
|
||||
CPU: 4 cores
|
||||
CPU model: host
|
||||
RAM: 8-16 GB
|
||||
HDD1: 32 GB
|
||||
HDD2: 100GB (raw)
|
||||
```
|
||||
|
||||
You can express your intention in working on the fix on your own.
|
||||
Commits are used to generate the changelog, and their author will be referenced in it.
|
||||
And one management VM or physical server connected to the same network.
|
||||
Any Linux system installed on it (eg. Ubuntu should be enough)
|
||||
|
||||
In case of **Feature Requests** please use the [Discussion's Feature Request section](https://github.com/aenix-io/cozystack/discussions/categories/feature-requests).
|
||||
**Note:** The VM should support `x86-64-v2` architecture, the most probably you can achieve this by setting cpu model to `host`
|
||||
|
||||
## License
|
||||
#### Install dependencies:
|
||||
|
||||
Cozystack is licensed under Apache 2.0.
|
||||
The code is provided as-is with no warranties.
|
||||
- `docker`
|
||||
- `talosctl`
|
||||
- `dialog`
|
||||
- `nmap`
|
||||
- `make`
|
||||
- `yq`
|
||||
- `kubectl`
|
||||
- `helm`
|
||||
|
||||
## Commercial Support
|
||||
### Netboot server
|
||||
|
||||
[**Ænix**](https://aenix.io) offers enterprise-grade support, available 24/7.
|
||||
Start matchbox with prebuilt Talos image for Cozystack:
|
||||
|
||||
We provide all types of assistance, including consultations, development of missing features, design, assistance with installation, and integration.
|
||||
```bash
|
||||
sudo docker run --name=matchbox -d --net=host ghcr.io/aenix-io/cozystack/matchbox:v0.0.2 \
|
||||
-address=:8080 \
|
||||
-log-level=debug
|
||||
```
|
||||
|
||||
[Contact us](https://aenix.io/contact/)
|
||||
Start DHCP-Server:
|
||||
```bash
|
||||
sudo docker run --name=dnsmasq -d --cap-add=NET_ADMIN --net=host quay.io/poseidon/dnsmasq \
|
||||
-d -q -p0 \
|
||||
--dhcp-range=192.168.100.3,192.168.100.254 \
|
||||
--dhcp-option=option:router,192.168.100.1 \
|
||||
--enable-tftp \
|
||||
--tftp-root=/var/lib/tftpboot \
|
||||
--dhcp-match=set:bios,option:client-arch,0 \
|
||||
--dhcp-boot=tag:bios,undionly.kpxe \
|
||||
--dhcp-match=set:efi32,option:client-arch,6 \
|
||||
--dhcp-boot=tag:efi32,ipxe.efi \
|
||||
--dhcp-match=set:efibc,option:client-arch,7 \
|
||||
--dhcp-boot=tag:efibc,ipxe.efi \
|
||||
--dhcp-match=set:efi64,option:client-arch,9 \
|
||||
--dhcp-boot=tag:efi64,ipxe.efi \
|
||||
--dhcp-userclass=set:ipxe,iPXE \
|
||||
--dhcp-boot=tag:ipxe,http://192.168.100.254:8080/boot.ipxe \
|
||||
--log-queries \
|
||||
--log-dhcp
|
||||
```
|
||||
|
||||
Where:
|
||||
- `192.168.100.3,192.168.100.254` range to allocate IPs from
|
||||
- `192.168.100.1` your gateway
|
||||
- `192.168.100.254` is address of your management server
|
||||
|
||||
Check status of containers:
|
||||
|
||||
```
|
||||
docker ps
|
||||
```
|
||||
|
||||
example output:
|
||||
|
||||
```console
|
||||
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
|
||||
22044f26f74d quay.io/poseidon/dnsmasq "/usr/sbin/dnsmasq -…" 6 seconds ago Up 5 seconds dnsmasq
|
||||
231ad81ff9e0 ghcr.io/aenix-io/cozystack/matchbox:v0.0.2 "/matchbox -address=…" 58 seconds ago Up 57 seconds matchbox
|
||||
```
|
||||
|
||||
### Bootstrap cluster
|
||||
|
||||
Write configuration for Cozystack:
|
||||
|
||||
```yaml
|
||||
cat > patch.yaml <<\EOT
|
||||
machine:
|
||||
kubelet:
|
||||
nodeIP:
|
||||
validSubnets:
|
||||
- 192.168.100.0/24
|
||||
kernel:
|
||||
modules:
|
||||
- name: openvswitch
|
||||
- name: drbd
|
||||
parameters:
|
||||
- usermode_helper=disabled
|
||||
- name: zfs
|
||||
install:
|
||||
image: ghcr.io/aenix-io/cozystack/talos:v1.6.4
|
||||
files:
|
||||
- content: |
|
||||
[plugins]
|
||||
[plugins."io.containerd.grpc.v1.cri"]
|
||||
device_ownership_from_security_context = true
|
||||
path: /etc/cri/conf.d/20-customization.part
|
||||
op: create
|
||||
|
||||
cluster:
|
||||
network:
|
||||
cni:
|
||||
name: none
|
||||
podSubnets:
|
||||
- 10.244.0.0/16
|
||||
serviceSubnets:
|
||||
- 10.96.0.0/16
|
||||
EOT
|
||||
|
||||
cat > patch-controlplane.yaml <<\EOT
|
||||
cluster:
|
||||
allowSchedulingOnControlPlanes: true
|
||||
controllerManager:
|
||||
extraArgs:
|
||||
bind-address: 0.0.0.0
|
||||
scheduler:
|
||||
extraArgs:
|
||||
bind-address: 0.0.0.0
|
||||
apiServer:
|
||||
certSANs:
|
||||
- 127.0.0.1
|
||||
proxy:
|
||||
disabled: true
|
||||
discovery:
|
||||
enabled: false
|
||||
etcd:
|
||||
advertisedSubnets:
|
||||
- 192.168.100.0/24
|
||||
EOT
|
||||
```
|
||||
|
||||
Run [talos-bootstrap](https://github.com/aenix-io/talos-bootstrap/) to deploy cluster:
|
||||
|
||||
```bash
|
||||
talos-bootstrap install
|
||||
```
|
||||
|
||||
Save admin kubeconfig to access your Kubernetes cluster:
|
||||
```bash
|
||||
cp -i kubeconfig ~/.kube/config
|
||||
```
|
||||
|
||||
Check connection:
|
||||
```bash
|
||||
kubectl get ns
|
||||
```
|
||||
|
||||
example output:
|
||||
```console
|
||||
NAME STATUS AGE
|
||||
default Active 7m56s
|
||||
kube-node-lease Active 7m56s
|
||||
kube-public Active 7m56s
|
||||
kube-system Active 7m56s
|
||||
```
|
||||
|
||||
|
||||
**Note:**: All nodes should currently show as "Not Ready", don't worry about that, this is because you disabled the default CNI plugin in the previous step. Cozystack will install it's own CNI-plugin on the next step.
|
||||
|
||||
|
||||
### Install Cozystack
|
||||
|
||||
|
||||
write config for cozystack:
|
||||
|
||||
**Note:** please make sure that you written the same setting specified in `patch.yaml` and `patch-controlplane.yaml` files.
|
||||
|
||||
```yaml
|
||||
cat > cozystack-config.yaml <<\EOT
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: cozystack
|
||||
namespace: cozy-system
|
||||
data:
|
||||
cluster-name: "cozystack"
|
||||
ipv4-pod-cidr: "10.244.0.0/16"
|
||||
ipv4-pod-gateway: "10.244.0.1"
|
||||
ipv4-svc-cidr: "10.96.0.0/16"
|
||||
ipv4-join-cidr: "100.64.0.0/16"
|
||||
EOT
|
||||
```
|
||||
|
||||
Create namesapce and install Cozystack system components:
|
||||
|
||||
```bash
|
||||
kubectl create ns cozy-system
|
||||
kubectl apply -f cozystack-config.yaml
|
||||
kubectl apply -f manifests/cozystack-installer.yaml
|
||||
```
|
||||
|
||||
(optional) You can track the logs of installer:
|
||||
```bash
|
||||
kubectl logs -n cozy-system deploy/cozystack -f
|
||||
```
|
||||
|
||||
Wait for a while, then check the status of installation:
|
||||
```bash
|
||||
kubectl get hr -A
|
||||
```
|
||||
|
||||
Wait until all releases become to `Ready` state:
|
||||
```console
|
||||
NAMESPACE NAME AGE READY STATUS
|
||||
cozy-cert-manager cert-manager 4m1s True Release reconciliation succeeded
|
||||
cozy-cert-manager cert-manager-issuers 4m1s True Release reconciliation succeeded
|
||||
cozy-cilium cilium 4m1s True Release reconciliation succeeded
|
||||
cozy-cluster-api capi-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-cluster-api capi-providers 4m1s True Release reconciliation succeeded
|
||||
cozy-dashboard dashboard 4m1s True Release reconciliation succeeded
|
||||
cozy-fluxcd cozy-fluxcd 4m1s True Release reconciliation succeeded
|
||||
cozy-grafana-operator grafana-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-kamaji kamaji 4m1s True Release reconciliation succeeded
|
||||
cozy-kubeovn kubeovn 4m1s True Release reconciliation succeeded
|
||||
cozy-kubevirt-cdi kubevirt-cdi 4m1s True Release reconciliation succeeded
|
||||
cozy-kubevirt-cdi kubevirt-cdi-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-kubevirt kubevirt 4m1s True Release reconciliation succeeded
|
||||
cozy-kubevirt kubevirt-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-linstor linstor 4m1s True Release reconciliation succeeded
|
||||
cozy-linstor piraeus-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-mariadb-operator mariadb-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-metallb metallb 4m1s True Release reconciliation succeeded
|
||||
cozy-monitoring monitoring 4m1s True Release reconciliation succeeded
|
||||
cozy-postgres-operator postgres-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-rabbitmq-operator rabbitmq-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-redis-operator redis-operator 4m1s True Release reconciliation succeeded
|
||||
cozy-telepresence telepresence 4m1s True Release reconciliation succeeded
|
||||
cozy-victoria-metrics-operator victoria-metrics-operator 4m1s True Release reconciliation succeeded
|
||||
tenant-root tenant-root 4m1s True Release reconciliation succeeded
|
||||
```
|
||||
|
||||
#### Configure Storage
|
||||
|
||||
Setup alias to access LINSTOR:
|
||||
```bash
|
||||
alias linstor='kubectl exec -n cozy-linstor deploy/linstor-controller -- linstor'
|
||||
```
|
||||
|
||||
list your nodes
|
||||
```bash
|
||||
linstor node list
|
||||
```
|
||||
|
||||
example output:
|
||||
|
||||
```console
|
||||
+-------------------------------------------------------+
|
||||
| Node | NodeType | Addresses | State |
|
||||
|=======================================================|
|
||||
| srv1 | SATELLITE | 192.168.100.11:3367 (SSL) | Online |
|
||||
| srv2 | SATELLITE | 192.168.100.12:3367 (SSL) | Online |
|
||||
| srv3 | SATELLITE | 192.168.100.13:3367 (SSL) | Online |
|
||||
+-------------------------------------------------------+
|
||||
```
|
||||
|
||||
list empty devices:
|
||||
|
||||
```bash
|
||||
linstor physical-storage list
|
||||
```
|
||||
|
||||
example output:
|
||||
```console
|
||||
+--------------------------------------------+
|
||||
| Size | Rotational | Nodes |
|
||||
|============================================|
|
||||
| 107374182400 | True | srv3[/dev/sdb] |
|
||||
| | | srv1[/dev/sdb] |
|
||||
| | | srv2[/dev/sdb] |
|
||||
+--------------------------------------------+
|
||||
```
|
||||
|
||||
|
||||
create storage pools:
|
||||
|
||||
```bash
|
||||
linstor ps cdp lvm srv1 /dev/sdb --pool-name data --storage-pool data
|
||||
linstor ps cdp lvm srv2 /dev/sdb --pool-name data --storage-pool data
|
||||
linstor ps cdp lvm srv3 /dev/sdb --pool-name data --storage-pool data
|
||||
```
|
||||
|
||||
list storage pools:
|
||||
|
||||
```bash
|
||||
linstor sp l
|
||||
```
|
||||
|
||||
example output:
|
||||
|
||||
```console
|
||||
+-------------------------------------------------------------------------------------------------------------------------------------+
|
||||
| StoragePool | Node | Driver | PoolName | FreeCapacity | TotalCapacity | CanSnapshots | State | SharedName |
|
||||
|=====================================================================================================================================|
|
||||
| DfltDisklessStorPool | srv1 | DISKLESS | | | | False | Ok | srv1;DfltDisklessStorPool |
|
||||
| DfltDisklessStorPool | srv2 | DISKLESS | | | | False | Ok | srv2;DfltDisklessStorPool |
|
||||
| DfltDisklessStorPool | srv3 | DISKLESS | | | | False | Ok | srv3;DfltDisklessStorPool |
|
||||
| data | srv1 | LVM | data | 100.00 GiB | 100.00 GiB | False | Ok | srv1;data |
|
||||
| data | srv2 | LVM | data | 100.00 GiB | 100.00 GiB | False | Ok | srv2;data |
|
||||
| data | srv3 | LVM | data | 100.00 GiB | 100.00 GiB | False | Ok | srv3;data |
|
||||
+-------------------------------------------------------------------------------------------------------------------------------------+
|
||||
```
|
||||
|
||||
|
||||
Create default storage classes:
|
||||
```yaml
|
||||
kubectl create -f- <<EOT
|
||||
---
|
||||
apiVersion: storage.k8s.io/v1
|
||||
kind: StorageClass
|
||||
metadata:
|
||||
name: local
|
||||
annotations:
|
||||
storageclass.kubernetes.io/is-default-class: "true"
|
||||
provisioner: linstor.csi.linbit.com
|
||||
parameters:
|
||||
linstor.csi.linbit.com/storagePool: "data"
|
||||
linstor.csi.linbit.com/layerList: "storage"
|
||||
linstor.csi.linbit.com/allowRemoteVolumeAccess: "false"
|
||||
volumeBindingMode: WaitForFirstConsumer
|
||||
allowVolumeExpansion: true
|
||||
---
|
||||
apiVersion: storage.k8s.io/v1
|
||||
kind: StorageClass
|
||||
metadata:
|
||||
name: replicated
|
||||
provisioner: linstor.csi.linbit.com
|
||||
parameters:
|
||||
linstor.csi.linbit.com/storagePool: "data"
|
||||
linstor.csi.linbit.com/autoPlace: "3"
|
||||
linstor.csi.linbit.com/layerList: "drbd storage"
|
||||
linstor.csi.linbit.com/allowRemoteVolumeAccess: "true"
|
||||
property.linstor.csi.linbit.com/DrbdOptions/auto-quorum: suspend-io
|
||||
property.linstor.csi.linbit.com/DrbdOptions/Resource/on-no-data-accessible: suspend-io
|
||||
property.linstor.csi.linbit.com/DrbdOptions/Resource/on-suspended-primary-outdated: force-secondary
|
||||
property.linstor.csi.linbit.com/DrbdOptions/Net/rr-conflict: retry-connect
|
||||
volumeBindingMode: WaitForFirstConsumer
|
||||
allowVolumeExpansion: true
|
||||
EOT
|
||||
```
|
||||
|
||||
list storageclasses:
|
||||
|
||||
```bash
|
||||
kubectl get storageclasses
|
||||
```
|
||||
|
||||
example output:
|
||||
```console
|
||||
NAME PROVISIONER RECLAIMPOLICY VOLUMEBINDINGMODE ALLOWVOLUMEEXPANSION AGE
|
||||
local (default) linstor.csi.linbit.com Delete WaitForFirstConsumer true 11m
|
||||
replicated linstor.csi.linbit.com Delete WaitForFirstConsumer true 11m
|
||||
```
|
||||
|
||||
#### Configure Networking interconnection
|
||||
|
||||
To access your services select the range of unused IPs, eg. `192.168.100.200-192.168.100.250`
|
||||
|
||||
**Note:** These IPs should be from the same network as nodes or they should have all necessary routes for them.
|
||||
|
||||
Configure MetalLB to use and announce this range:
|
||||
```yaml
|
||||
kubectl create -f- <<EOT
|
||||
---
|
||||
apiVersion: metallb.io/v1beta1
|
||||
kind: L2Advertisement
|
||||
metadata:
|
||||
name: cozystack
|
||||
namespace: cozy-metallb
|
||||
spec:
|
||||
ipAddressPools:
|
||||
- cozystack
|
||||
---
|
||||
apiVersion: metallb.io/v1beta1
|
||||
kind: IPAddressPool
|
||||
metadata:
|
||||
name: cozystack
|
||||
namespace: cozy-metallb
|
||||
spec:
|
||||
addresses:
|
||||
- 192.168.100.200-192.168.100.250
|
||||
autoAssign: true
|
||||
avoidBuggyIPs: false
|
||||
EOT
|
||||
```
|
||||
|
||||
#### Setup basic applications
|
||||
|
||||
Get token from `tenant-root`:
|
||||
```bash
|
||||
kubectl get secret -n tenant-root tenant-root -o go-template='{{ printf "%s\n" (index .data "token" | base64decode) }}'
|
||||
```
|
||||
|
||||
Enable port forward to cozy-dashboard:
|
||||
```bash
|
||||
kubectl port-forward -n cozy-dashboard svc/dashboard 8080:80
|
||||
```
|
||||
|
||||
Open: http://localhost:8080/
|
||||
|
||||
- Select `tenant-root`
|
||||
- Click `Upgrade` button
|
||||
- Write a domain into `host` which you wish to use as parent domain for all deployed applications
|
||||
**Note:**
|
||||
- if you have no domain yet, you can use `192.168.100.200.nip.io` where `192.168.100.200` is a first IP address in your network addresses range.
|
||||
- alternatively you can leave the default value, however you'll be need to modify your `/etc/hosts` every time you want to access specific application.
|
||||
- Set `etcd`, `monitoring` and `ingress` to enabled position
|
||||
- Click Deploy
|
||||
|
||||
|
||||
Check persistent volumes provisioned:
|
||||
|
||||
```bash
|
||||
kubectl get pvc -n tenant-root
|
||||
```
|
||||
|
||||
example output:
|
||||
```console
|
||||
NAME STATUS VOLUME CAPACITY ACCESS MODES STORAGECLASS VOLUMEATTRIBUTESCLASS AGE
|
||||
data-etcd-0 Bound pvc-4cbd29cc-a29f-453d-b412-451647cd04bf 10Gi RWO local <unset> 2m10s
|
||||
data-etcd-1 Bound pvc-1579f95a-a69d-4a26-bcc2-b15ccdbede0d 10Gi RWO local <unset> 115s
|
||||
data-etcd-2 Bound pvc-907009e5-88bf-4d18-91e7-b56b0dbfb97e 10Gi RWO local <unset> 91s
|
||||
grafana-db-1 Bound pvc-7b3f4e23-228a-46fd-b820-d033ef4679af 10Gi RWO local <unset> 2m41s
|
||||
grafana-db-2 Bound pvc-ac9b72a4-f40e-47e8-ad24-f50d843b55e4 10Gi RWO local <unset> 113s
|
||||
vmselect-cachedir-vmselect-longterm-0 Bound pvc-622fa398-2104-459f-8744-565eee0a13f1 2Gi RWO local <unset> 2m21s
|
||||
vmselect-cachedir-vmselect-longterm-1 Bound pvc-fc9349f5-02b2-4e25-8bef-6cbc5cc6d690 2Gi RWO local <unset> 2m21s
|
||||
vmselect-cachedir-vmselect-shortterm-0 Bound pvc-7acc7ff6-6b9b-4676-bd1f-6867ea7165e2 2Gi RWO local <unset> 2m41s
|
||||
vmselect-cachedir-vmselect-shortterm-1 Bound pvc-e514f12b-f1f6-40ff-9838-a6bda3580eb7 2Gi RWO local <unset> 2m40s
|
||||
vmstorage-db-vmstorage-longterm-0 Bound pvc-e8ac7fc3-df0d-4692-aebf-9f66f72f9fef 10Gi RWO local <unset> 2m21s
|
||||
vmstorage-db-vmstorage-longterm-1 Bound pvc-68b5ceaf-3ed1-4e5a-9568-6b95911c7c3a 10Gi RWO local <unset> 2m21s
|
||||
vmstorage-db-vmstorage-shortterm-0 Bound pvc-cee3a2a4-5680-4880-bc2a-85c14dba9380 10Gi RWO local <unset> 2m41s
|
||||
vmstorage-db-vmstorage-shortterm-1 Bound pvc-d55c235d-cada-4c4a-8299-e5fc3f161789 10Gi RWO local <unset> 2m41s
|
||||
```
|
||||
|
||||
Check all pods are running:
|
||||
|
||||
|
||||
```bash
|
||||
kubectl get pod -n tenant-root
|
||||
```
|
||||
|
||||
example output:
|
||||
```console
|
||||
NAME READY STATUS RESTARTS AGE
|
||||
etcd-0 1/1 Running 0 2m1s
|
||||
etcd-1 1/1 Running 0 106s
|
||||
etcd-2 1/1 Running 0 82s
|
||||
grafana-db-1 1/1 Running 0 119s
|
||||
grafana-db-2 1/1 Running 0 13s
|
||||
grafana-deployment-74b5656d6-5dcvn 1/1 Running 0 90s
|
||||
grafana-deployment-74b5656d6-q5589 1/1 Running 1 (105s ago) 111s
|
||||
root-ingress-controller-6ccf55bc6d-pg79l 2/2 Running 0 2m27s
|
||||
root-ingress-controller-6ccf55bc6d-xbs6x 2/2 Running 0 2m29s
|
||||
root-ingress-defaultbackend-686bcbbd6c-5zbvp 1/1 Running 0 2m29s
|
||||
vmalert-vmalert-644986d5c-7hvwk 2/2 Running 0 2m30s
|
||||
vmalertmanager-alertmanager-0 2/2 Running 0 2m32s
|
||||
vmalertmanager-alertmanager-1 2/2 Running 0 2m31s
|
||||
vminsert-longterm-75789465f-hc6cz 1/1 Running 0 2m10s
|
||||
vminsert-longterm-75789465f-m2v4t 1/1 Running 0 2m12s
|
||||
vminsert-shortterm-78456f8fd9-wlwww 1/1 Running 0 2m29s
|
||||
vminsert-shortterm-78456f8fd9-xg7cw 1/1 Running 0 2m28s
|
||||
vmselect-longterm-0 1/1 Running 0 2m12s
|
||||
vmselect-longterm-1 1/1 Running 0 2m12s
|
||||
vmselect-shortterm-0 1/1 Running 0 2m31s
|
||||
vmselect-shortterm-1 1/1 Running 0 2m30s
|
||||
vmstorage-longterm-0 1/1 Running 0 2m12s
|
||||
vmstorage-longterm-1 1/1 Running 0 2m12s
|
||||
vmstorage-shortterm-0 1/1 Running 0 2m32s
|
||||
vmstorage-shortterm-1 1/1 Running 0 2m31s
|
||||
```
|
||||
|
||||
Now you can get public IP of ingress controller:
|
||||
```
|
||||
kubectl get svc -n tenant-root root-ingress-controller
|
||||
```
|
||||
|
||||
example output:
|
||||
```console
|
||||
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
|
||||
root-ingress-controller LoadBalancer 10.96.16.141 192.168.100.200 80:31632/TCP,443:30113/TCP 3m33s
|
||||
```
|
||||
|
||||
Use `grafana.example.org` (under 192.168.100.200) to access system monitoring, where `example.org` is your domain specified for `tenant-root`
|
||||
|
||||
- login: `admin`
|
||||
- password:
|
||||
|
||||
```bash
|
||||
kubectl get secret -n tenant-root grafana-admin-password -o go-template='{{ printf "%s\n" (index .data "password" | base64decode) }}'
|
||||
```
|
||||
|
||||
@@ -3,7 +3,7 @@ set -e
|
||||
|
||||
if [ -e $1 ]; then
|
||||
echo "Please pass version in the first argument"
|
||||
echo "Example: $0 0.2.0"
|
||||
echo "Example: $0 v0.0.2"
|
||||
exit 1
|
||||
fi
|
||||
|
||||
@@ -12,14 +12,11 @@ talos_version=$(awk '/^version:/ {print $2}' packages/core/installer/images/talo
|
||||
|
||||
set -x
|
||||
|
||||
sed -i "/^TAG / s|=.*|= v${version}|" \
|
||||
sed -i "s|\(ghcr.io/aenix-io/cozystack/matchbox:\)v[^ ]\+|\1${version}|g" README.md
|
||||
sed -i "s|\(ghcr.io/aenix-io/cozystack/talos:\)v[^ ]\+|\1${talos_version}|g" README.md
|
||||
|
||||
sed -i "/^TAG / s|=.*|= ${version}|" \
|
||||
packages/apps/http-cache/Makefile \
|
||||
packages/apps/kubernetes/Makefile \
|
||||
packages/core/installer/Makefile \
|
||||
packages/system/dashboard/Makefile
|
||||
|
||||
sed -i "/^VERSION / s|=.*|= ${version}|" \
|
||||
packages/core/Makefile \
|
||||
packages/system/Makefile
|
||||
make -C packages/core fix-chartnames
|
||||
make -C packages/system fix-chartnames
|
||||
|
||||
@@ -61,6 +61,8 @@ spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
app: cozystack
|
||||
strategy:
|
||||
type: Recreate
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
@@ -70,26 +72,14 @@ spec:
|
||||
serviceAccountName: cozystack
|
||||
containers:
|
||||
- name: cozystack
|
||||
image: "ghcr.io/aenix-io/cozystack/cozystack:v0.2.0"
|
||||
image: "ghcr.io/aenix-io/cozystack/installer:v0.0.2"
|
||||
env:
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: localhost
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: "7445"
|
||||
- name: K8S_AWAIT_ELECTION_ENABLED
|
||||
value: "1"
|
||||
- name: K8S_AWAIT_ELECTION_NAME
|
||||
value: cozystack
|
||||
- name: K8S_AWAIT_ELECTION_LOCK_NAME
|
||||
value: cozystack
|
||||
- name: K8S_AWAIT_ELECTION_LOCK_NAMESPACE
|
||||
value: cozy-system
|
||||
- name: K8S_AWAIT_ELECTION_IDENTITY
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: metadata.name
|
||||
- name: darkhttpd
|
||||
image: "ghcr.io/aenix-io/cozystack/cozystack:v0.2.0"
|
||||
image: "ghcr.io/aenix-io/cozystack/installer:v0.0.2"
|
||||
command:
|
||||
- /usr/bin/darkhttpd
|
||||
- /cozystack/assets
|
||||
@@ -102,6 +92,3 @@ spec:
|
||||
- key: "node.kubernetes.io/not-ready"
|
||||
operator: "Exists"
|
||||
effect: "NoSchedule"
|
||||
- key: "node.cilium.io/agent-not-ready"
|
||||
operator: "Exists"
|
||||
effect: "NoSchedule"
|
||||
|
||||
@@ -2,7 +2,7 @@ PUSH := 1
|
||||
LOAD := 0
|
||||
REGISTRY := ghcr.io/aenix-io/cozystack
|
||||
NGINX_CACHE_TAG = v0.1.0
|
||||
TAG := v0.2.0
|
||||
TAG := v0.0.2
|
||||
|
||||
image: image-nginx
|
||||
|
||||
|
||||
@@ -1,4 +1,14 @@
|
||||
{
|
||||
"containerimage.config.digest": "sha256:0487fc50bb5f870720b05e947185424a400fad38b682af8f1ca4b418ed3c5b4b",
|
||||
"containerimage.digest": "sha256:be12f3834be0e2f129685f682fab83c871610985fc43668ce6a294c9de603798"
|
||||
"containerimage.config.digest": "sha256:f4ad0559a74749de0d11b1835823bf9c95332962b0909450251d849113f22c19",
|
||||
"containerimage.descriptor": {
|
||||
"mediaType": "application/vnd.docker.distribution.manifest.v2+json",
|
||||
"digest": "sha256:3a0e8d791e0ccf681711766387ea9278e7d39f1956509cead2f72aa0001797ef",
|
||||
"size": 1093,
|
||||
"platform": {
|
||||
"architecture": "amd64",
|
||||
"os": "linux"
|
||||
}
|
||||
},
|
||||
"containerimage.digest": "sha256:3a0e8d791e0ccf681711766387ea9278e7d39f1956509cead2f72aa0001797ef",
|
||||
"image.name": "ghcr.io/aenix-io/cozystack/nginx-cache:v0.1.0,ghcr.io/aenix-io/cozystack/nginx-cache:v0.1.0-v0.0.2"
|
||||
}
|
||||
@@ -1,7 +1,7 @@
|
||||
PUSH := 1
|
||||
LOAD := 0
|
||||
REGISTRY := ghcr.io/aenix-io/cozystack
|
||||
TAG := v0.2.0
|
||||
TAG := v0.0.2
|
||||
UBUNTU_CONTAINER_DISK_TAG = v1.29.1
|
||||
|
||||
image: image-ubuntu-container-disk
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{
|
||||
"containerimage.config.digest": "sha256:43d0bfd01c5e364ba961f1e3dc2c7ccd7fd4ca65bd26bc8c4a5298d7ff2c9f4f",
|
||||
"containerimage.digest": "sha256:908b3c186bee86f1c9476317eb6582d07f19776b291aa068e5642f8fd08fa9e7"
|
||||
"containerimage.config.digest": "sha256:e982cfa2320d3139ed311ae44bcc5ea18db7e4e76d2746e0af04c516288ff0f1",
|
||||
"containerimage.digest": "sha256:34f6aba5b5a2afbb46bbb891ef4ddc0855c2ffe4f9e5a99e8e553286ddd2c070"
|
||||
}
|
||||
@@ -16,7 +16,7 @@ type: application
|
||||
# This is the chart version. This version number should be incremented each time you make changes
|
||||
# to the chart and its templates, including the app version.
|
||||
# Versions are expected to follow Semantic Versioning (https://semver.org/)
|
||||
version: 0.2.0
|
||||
version: 0.1.0
|
||||
|
||||
# This is the version number of the application being deployed. This version number should be
|
||||
# incremented each time you make changes to the application. Versions are not expected to
|
||||
|
||||
@@ -1,7 +1,7 @@
|
||||
{{- range $name := .Values.databases }}
|
||||
{{ $dnsName := replace "_" "-" $name }}
|
||||
---
|
||||
apiVersion: k8s.mariadb.com/v1alpha1
|
||||
apiVersion: mariadb.mmontes.io/v1alpha1
|
||||
kind: Database
|
||||
metadata:
|
||||
name: {{ $.Release.Name }}-{{ $dnsName }}
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
---
|
||||
apiVersion: k8s.mariadb.com/v1alpha1
|
||||
apiVersion: mariadb.mmontes.io/v1alpha1
|
||||
kind: MariaDB
|
||||
metadata:
|
||||
name: {{ .Release.Name }}
|
||||
@@ -35,9 +35,8 @@ spec:
|
||||
# automaticFailover: true
|
||||
|
||||
metrics:
|
||||
enabled: true
|
||||
exporter:
|
||||
image: prom/mysqld-exporter:v0.15.1
|
||||
image: prom/mysqld-exporter:v0.14.0
|
||||
resources:
|
||||
requests:
|
||||
cpu: 50m
|
||||
@@ -54,10 +53,14 @@ spec:
|
||||
name: {{ .Release.Name }}-my-cnf
|
||||
key: config
|
||||
|
||||
storage:
|
||||
size: {{ .Values.size }}
|
||||
resizeInUseVolumes: true
|
||||
waitForVolumeResize: true
|
||||
volumeClaimTemplate:
|
||||
resources:
|
||||
requests:
|
||||
storage: {{ .Values.size }}
|
||||
accessModes:
|
||||
- ReadWriteOnce
|
||||
|
||||
|
||||
|
||||
{{- if .Values.external }}
|
||||
primaryService:
|
||||
|
||||
@@ -2,7 +2,7 @@
|
||||
{{ if not (eq $name "root") }}
|
||||
{{ $dnsName := replace "_" "-" $name }}
|
||||
---
|
||||
apiVersion: k8s.mariadb.com/v1alpha1
|
||||
apiVersion: mariadb.mmontes.io/v1alpha1
|
||||
kind: User
|
||||
metadata:
|
||||
name: {{ $.Release.Name }}-{{ $dnsName }}
|
||||
@@ -15,7 +15,7 @@ spec:
|
||||
key: {{ $name }}-password
|
||||
maxUserConnections: {{ $u.maxUserConnections }}
|
||||
---
|
||||
apiVersion: k8s.mariadb.com/v1alpha1
|
||||
apiVersion: mariadb.mmontes.io/v1alpha1
|
||||
kind: Grant
|
||||
metadata:
|
||||
name: {{ $.Release.Name }}-{{ $dnsName }}
|
||||
|
||||
@@ -1,7 +1,6 @@
|
||||
http-cache 0.1.0 HEAD
|
||||
kubernetes 0.1.0 HEAD
|
||||
mysql 0.1.0 f642698
|
||||
mysql 0.2.0 HEAD
|
||||
mysql 0.1.0 HEAD
|
||||
postgres 0.1.0 HEAD
|
||||
rabbitmq 0.1.0 HEAD
|
||||
redis 0.1.1 HEAD
|
||||
|
||||
@@ -1,6 +1,4 @@
|
||||
VERSION := 0.2.0
|
||||
|
||||
gen: fix-chartnames
|
||||
|
||||
fix-chartnames:
|
||||
find . -name Chart.yaml -maxdepth 2 | awk -F/ '{print $$2}' | while read i; do printf "name: cozy-%s\nversion: $(VERSION)\n" "$$i" > "$$i/Chart.yaml"; done
|
||||
find . -name Chart.yaml -maxdepth 2 | awk -F/ '{print $$2}' | while read i; do printf "name: cozy-%s\nversion: 1.0.0\n" "$$i" > "$$i/Chart.yaml"; done
|
||||
|
||||
@@ -1,13 +0,0 @@
|
||||
NAMESPACE=cozy-fluxcd
|
||||
NAME=fluxcd
|
||||
|
||||
API_VERSIONS_FLAGS=$(addprefix -a ,$(shell kubectl api-versions))
|
||||
|
||||
show:
|
||||
helm template -n $(NAMESPACE) $(NAME) . --no-hooks --dry-run=server $(API_VERSIONS_FLAGS)
|
||||
|
||||
apply:
|
||||
helm template -n $(NAMESPACE) $(NAME) . --no-hooks --dry-run=server $(API_VERSIONS_FLAGS) | kubectl apply -n $(NAMESPACE) -f-
|
||||
|
||||
diff:
|
||||
helm template -n $(NAMESPACE) $(NAME) . --no-hooks --dry-run=server $(API_VERSIONS_FLAGS) | kubectl diff -n $(NAMESPACE) -f-
|
||||
File diff suppressed because it is too large
Load Diff
@@ -1,2 +1,2 @@
|
||||
name: cozy-installer
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
NAMESPACE=cozy-system
|
||||
NAMESPACE=cozy-installer
|
||||
NAME=installer
|
||||
PUSH := 1
|
||||
LOAD := 0
|
||||
REGISTRY := ghcr.io/aenix-io/cozystack
|
||||
TAG := v0.2.0
|
||||
TAG := v0.0.2
|
||||
TALOS_VERSION=$(shell awk '/^version:/ {print $$2}' images/talos/profiles/installer.yaml)
|
||||
|
||||
show:
|
||||
@@ -18,19 +18,18 @@ diff:
|
||||
update:
|
||||
hack/gen-profiles.sh
|
||||
|
||||
image: image-cozystack image-talos image-matchbox
|
||||
image: image-installer image-talos image-matchbox
|
||||
|
||||
image-cozystack:
|
||||
make -C ../../.. repos
|
||||
docker buildx build -f images/cozystack/Dockerfile ../../.. \
|
||||
image-installer:
|
||||
docker buildx build -f images/installer/Dockerfile ../../.. \
|
||||
--provenance false \
|
||||
--tag $(REGISTRY)/cozystack:$(TAG) \
|
||||
--cache-from type=registry,ref=$(REGISTRY)/cozystack:$(TAG) \
|
||||
--tag $(REGISTRY)/installer:$(TAG) \
|
||||
--cache-from type=registry,ref=$(REGISTRY)/installer:$(TAG) \
|
||||
--cache-to type=inline \
|
||||
--metadata-file images/cozystack.json \
|
||||
--metadata-file images/installer.json \
|
||||
--push=$(PUSH) \
|
||||
--load=$(LOAD)
|
||||
echo "$(REGISTRY)/cozystack:$(TAG)" > images/cozystack.tag
|
||||
echo "$(REGISTRY)/installer:$(TAG)" > images/installer.tag
|
||||
|
||||
image-talos:
|
||||
test -f ../../../_out/assets/installer-amd64.tar || make talos-installer
|
||||
@@ -44,18 +43,14 @@ image-matchbox:
|
||||
docker buildx build -f images/matchbox/Dockerfile ../../.. \
|
||||
--provenance false \
|
||||
--tag $(REGISTRY)/matchbox:$(TAG) \
|
||||
--tag $(REGISTRY)/matchbox:$(TALOS_VERSION)-$(TAG) \
|
||||
--cache-from type=registry,ref=$(REGISTRY)/matchbox:$(TALOS_VERSION) \
|
||||
--cache-from type=registry,ref=$(REGISTRY)/matchbox:$(TAG) \
|
||||
--cache-to type=inline \
|
||||
--metadata-file images/matchbox.json \
|
||||
--push=$(PUSH) \
|
||||
--load=$(LOAD)
|
||||
echo "$(REGISTRY)/matchbox:$(TALOS_VERSION)" > images/matchbox.tag
|
||||
echo "$(REGISTRY)/matchbox:$(TAG)" > images/matchbox.tag
|
||||
|
||||
assets: talos-iso
|
||||
|
||||
talos-initramfs talos-kernel talos-installer talos-iso:
|
||||
mkdir -p ../../../_out/assets
|
||||
cat images/talos/profiles/$(subst talos-,,$@).yaml | \
|
||||
docker run --rm -i -v /dev:/dev --privileged "ghcr.io/siderolabs/imager:$(TALOS_VERSION)" --tar-to-stdout - | \
|
||||
tar -C ../../../_out/assets -xzf-
|
||||
cat images/talos/profiles/$(subst talos-,,$@).yaml | docker run --rm -i -v $${PWD}/../../../_out/assets:/out -v /dev:/dev --privileged "ghcr.io/siderolabs/imager:$(TALOS_VERSION)" -
|
||||
|
||||
@@ -1,4 +0,0 @@
|
||||
{
|
||||
"containerimage.config.digest": "sha256:326a169fb5d4277a5c3b0359e0c885b31d1360b58475bbc316be1971c710cd8d",
|
||||
"containerimage.digest": "sha256:a608bdb75b3e06f6365f5f0b3fea82ac93c564d11f316f17e3d46e8a497a321d"
|
||||
}
|
||||
@@ -1 +0,0 @@
|
||||
ghcr.io/aenix-io/cozystack/cozystack:v0.2.0
|
||||
14
packages/core/installer/images/installer.json
Normal file
14
packages/core/installer/images/installer.json
Normal file
@@ -0,0 +1,14 @@
|
||||
{
|
||||
"containerimage.config.digest": "sha256:5c7f51a9cbc945c13d52157035eba6ba4b6f3b68b76280f8e64b4f6ba239db1a",
|
||||
"containerimage.descriptor": {
|
||||
"mediaType": "application/vnd.docker.distribution.manifest.v2+json",
|
||||
"digest": "sha256:7cda3480faf0539ed4a3dd252aacc7a997645d3a390ece377c36cf55f9e57e11",
|
||||
"size": 2074,
|
||||
"platform": {
|
||||
"architecture": "amd64",
|
||||
"os": "linux"
|
||||
}
|
||||
},
|
||||
"containerimage.digest": "sha256:7cda3480faf0539ed4a3dd252aacc7a997645d3a390ece377c36cf55f9e57e11",
|
||||
"image.name": "ghcr.io/aenix-io/cozystack/installer:v0.0.2"
|
||||
}
|
||||
1
packages/core/installer/images/installer.tag
Normal file
1
packages/core/installer/images/installer.tag
Normal file
@@ -0,0 +1 @@
|
||||
ghcr.io/aenix-io/cozystack/installer:v0.0.2
|
||||
@@ -1,15 +1,3 @@
|
||||
FROM golang:alpine3.19 as k8s-await-election-builder
|
||||
|
||||
ARG K8S_AWAIT_ELECTION_GITREPO=https://github.com/LINBIT/k8s-await-election
|
||||
ARG K8S_AWAIT_ELECTION_VERSION=0.4.1
|
||||
|
||||
RUN apk add --no-cache git make
|
||||
RUN git clone ${K8S_AWAIT_ELECTION_GITREPO} /usr/local/go/k8s-await-election/ \
|
||||
&& cd /usr/local/go/k8s-await-election \
|
||||
&& git reset --hard v${K8S_AWAIT_ELECTION_VERSION} \
|
||||
&& make \
|
||||
&& mv ./out/k8s-await-election-amd64 /k8s-await-election
|
||||
|
||||
FROM alpine:3.19 AS builder
|
||||
|
||||
RUN apk add --no-cache make git
|
||||
@@ -30,8 +18,7 @@ COPY scripts /cozystack/scripts
|
||||
COPY --from=builder /src/packages/core /cozystack/packages/core
|
||||
COPY --from=builder /src/packages/system /cozystack/packages/system
|
||||
COPY --from=builder /src/_out/repos /cozystack/assets/repos
|
||||
COPY --from=k8s-await-election-builder /k8s-await-election /usr/bin/k8s-await-election
|
||||
COPY dashboards /cozystack/assets/dashboards
|
||||
|
||||
WORKDIR /cozystack
|
||||
ENTRYPOINT ["/usr/bin/k8s-await-election", "/cozystack/scripts/installer.sh" ]
|
||||
ENTRYPOINT [ "/cozystack/scripts/installer.sh" ]
|
||||
@@ -1,4 +1,14 @@
|
||||
{
|
||||
"containerimage.config.digest": "sha256:dc584f743bb73e04dcbebca7ab4f602f2c067190fd9609c3fd84412e83c20445",
|
||||
"containerimage.digest": "sha256:39ab0bf769b269a8082eeb31a9672e39caa61dd342ba2157b954c642f54a32ff"
|
||||
"containerimage.config.digest": "sha256:cb8cb211017e51f6eb55604287c45cbf6ed8add5df482aaebff3d493a11b5a76",
|
||||
"containerimage.descriptor": {
|
||||
"mediaType": "application/vnd.docker.distribution.manifest.v2+json",
|
||||
"digest": "sha256:3be72cdce2f4ab4886a70fb7b66e4518a1fe4ba0771319c96fa19a0d6f409602",
|
||||
"size": 1488,
|
||||
"platform": {
|
||||
"architecture": "amd64",
|
||||
"os": "linux"
|
||||
}
|
||||
},
|
||||
"containerimage.digest": "sha256:3be72cdce2f4ab4886a70fb7b66e4518a1fe4ba0771319c96fa19a0d6f409602",
|
||||
"image.name": "ghcr.io/aenix-io/cozystack/matchbox:v0.0.2"
|
||||
}
|
||||
@@ -1 +1 @@
|
||||
ghcr.io/aenix-io/cozystack/matchbox:v1.6.4
|
||||
ghcr.io/aenix-io/cozystack/matchbox:v0.0.2
|
||||
|
||||
@@ -41,6 +41,8 @@ spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
app: cozystack
|
||||
strategy:
|
||||
type: Recreate
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
@@ -50,26 +52,14 @@ spec:
|
||||
serviceAccountName: cozystack
|
||||
containers:
|
||||
- name: cozystack
|
||||
image: "{{ .Files.Get "images/cozystack.tag" | trim }}@{{ index (.Files.Get "images/cozystack.json" | fromJson) "containerimage.digest" }}"
|
||||
image: "{{ .Files.Get "images/installer.tag" | trim }}@{{ index (.Files.Get "images/installer.json" | fromJson) "containerimage.digest" }}"
|
||||
env:
|
||||
- name: KUBERNETES_SERVICE_HOST
|
||||
value: localhost
|
||||
- name: KUBERNETES_SERVICE_PORT
|
||||
value: "7445"
|
||||
- name: K8S_AWAIT_ELECTION_ENABLED
|
||||
value: "1"
|
||||
- name: K8S_AWAIT_ELECTION_NAME
|
||||
value: cozystack
|
||||
- name: K8S_AWAIT_ELECTION_LOCK_NAME
|
||||
value: cozystack
|
||||
- name: K8S_AWAIT_ELECTION_LOCK_NAMESPACE
|
||||
value: cozy-system
|
||||
- name: K8S_AWAIT_ELECTION_IDENTITY
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: metadata.name
|
||||
- name: darkhttpd
|
||||
image: "{{ .Files.Get "images/cozystack.tag" | trim }}@{{ index (.Files.Get "images/cozystack.json" | fromJson) "containerimage.digest" }}"
|
||||
image: "{{ .Files.Get "images/installer.tag" | trim }}@{{ index (.Files.Get "images/installer.json" | fromJson) "containerimage.digest" }}"
|
||||
command:
|
||||
- /usr/bin/darkhttpd
|
||||
- /cozystack/assets
|
||||
@@ -82,9 +72,6 @@ spec:
|
||||
- key: "node.kubernetes.io/not-ready"
|
||||
operator: "Exists"
|
||||
effect: "NoSchedule"
|
||||
- key: "node.cilium.io/agent-not-ready"
|
||||
operator: "Exists"
|
||||
effect: "NoSchedule"
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-platform
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -13,7 +13,7 @@ namespaces-show:
|
||||
helm template -n $(NAMESPACE) $(NAME) . --dry-run=server $(API_VERSIONS_FLAGS) -s templates/namespaces.yaml
|
||||
|
||||
namespaces-apply:
|
||||
helm template -n $(NAMESPACE) $(NAME) . --dry-run=server $(API_VERSIONS_FLAGS) -s templates/namespaces.yaml | kubectl apply -n $(NAMESPACE) -f-
|
||||
helm template -n $(NAMESPACE) $(NAME) . --dry-run=server $(API_VERSIONS_FLAGS) -s templates/namespaces.yaml | kubectl apply -f-
|
||||
|
||||
diff:
|
||||
helm template -n $(NAMESPACE) $(NAME) . --dry-run=server $(API_VERSIONS_FLAGS) | kubectl diff -f-
|
||||
helm template -n $(NAMESPACE) $(NAME) . --dry-run=server $(API_VERSIONS_FLAGS) -s templates/namespaces.yaml | kubectl diff -f-
|
||||
|
||||
@@ -1,102 +0,0 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
|
||||
releases:
|
||||
- name: cilium
|
||||
releaseName: cilium
|
||||
chart: cozy-cilium
|
||||
namespace: cozy-cilium
|
||||
privileged: true
|
||||
dependsOn: []
|
||||
values:
|
||||
cilium:
|
||||
bpf:
|
||||
masquerade: true
|
||||
cni:
|
||||
chainingMode: ~
|
||||
customConf: false
|
||||
configMap: ""
|
||||
enableIPv4Masquerade: true
|
||||
enableIdentityMark: true
|
||||
ipv4NativeRoutingCIDR: "{{ index $cozyConfig.data "ipv4-pod-cidr" }}"
|
||||
autoDirectNodeRoutes: true
|
||||
|
||||
- name: cert-manager
|
||||
releaseName: cert-manager
|
||||
chart: cozy-cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: [cilium]
|
||||
|
||||
- name: cert-manager-issuers
|
||||
releaseName: cert-manager-issuers
|
||||
chart: cozy-cert-manager-issuers
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: [cilium,cert-manager]
|
||||
|
||||
- name: victoria-metrics-operator
|
||||
releaseName: victoria-metrics-operator
|
||||
chart: cozy-victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
dependsOn: [cilium,cert-manager]
|
||||
|
||||
- name: monitoring
|
||||
releaseName: monitoring
|
||||
chart: cozy-monitoring
|
||||
namespace: cozy-monitoring
|
||||
privileged: true
|
||||
dependsOn: [cilium,victoria-metrics-operator]
|
||||
|
||||
- name: metallb
|
||||
releaseName: metallb
|
||||
chart: cozy-metallb
|
||||
namespace: cozy-metallb
|
||||
privileged: true
|
||||
dependsOn: [cilium]
|
||||
|
||||
- name: grafana-operator
|
||||
releaseName: grafana-operator
|
||||
chart: cozy-grafana-operator
|
||||
namespace: cozy-grafana-operator
|
||||
dependsOn: [cilium]
|
||||
|
||||
- name: mariadb-operator
|
||||
releaseName: mariadb-operator
|
||||
chart: cozy-mariadb-operator
|
||||
namespace: cozy-mariadb-operator
|
||||
dependsOn: [cilium,cert-manager,victoria-metrics-operator]
|
||||
|
||||
- name: postgres-operator
|
||||
releaseName: postgres-operator
|
||||
chart: cozy-postgres-operator
|
||||
namespace: cozy-postgres-operator
|
||||
dependsOn: [cilium,cert-manager]
|
||||
|
||||
- name: rabbitmq-operator
|
||||
releaseName: rabbitmq-operator
|
||||
chart: cozy-rabbitmq-operator
|
||||
namespace: cozy-rabbitmq-operator
|
||||
dependsOn: [cilium]
|
||||
|
||||
- name: redis-operator
|
||||
releaseName: redis-operator
|
||||
chart: cozy-redis-operator
|
||||
namespace: cozy-redis-operator
|
||||
dependsOn: [cilium]
|
||||
|
||||
- name: piraeus-operator
|
||||
releaseName: piraeus-operator
|
||||
chart: cozy-piraeus-operator
|
||||
namespace: cozy-linstor
|
||||
dependsOn: [cilium,cert-manager]
|
||||
|
||||
- name: linstor
|
||||
releaseName: linstor
|
||||
chart: cozy-linstor
|
||||
namespace: cozy-linstor
|
||||
privileged: true
|
||||
dependsOn: [piraeus-operator,cilium,cert-manager]
|
||||
|
||||
- name: telepresence
|
||||
releaseName: traffic-manager
|
||||
chart: cozy-telepresence
|
||||
namespace: cozy-telepresence
|
||||
dependsOn: []
|
||||
@@ -1,63 +0,0 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
|
||||
releases:
|
||||
- name: cert-manager
|
||||
releaseName: cert-manager
|
||||
chart: cozy-cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: []
|
||||
|
||||
- name: cert-manager-issuers
|
||||
releaseName: cert-manager-issuers
|
||||
chart: cozy-cert-manager-issuers
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: victoria-metrics-operator
|
||||
releaseName: victoria-metrics-operator
|
||||
chart: cozy-victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: monitoring
|
||||
releaseName: monitoring
|
||||
chart: cozy-monitoring
|
||||
namespace: cozy-monitoring
|
||||
privileged: true
|
||||
dependsOn: [victoria-metrics-operator]
|
||||
|
||||
- name: grafana-operator
|
||||
releaseName: grafana-operator
|
||||
chart: cozy-grafana-operator
|
||||
namespace: cozy-grafana-operator
|
||||
dependsOn: []
|
||||
|
||||
- name: mariadb-operator
|
||||
releaseName: mariadb-operator
|
||||
chart: cozy-mariadb-operator
|
||||
namespace: cozy-mariadb-operator
|
||||
dependsOn: [victoria-metrics-operator]
|
||||
|
||||
- name: postgres-operator
|
||||
releaseName: postgres-operator
|
||||
chart: cozy-postgres-operator
|
||||
namespace: cozy-postgres-operator
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: rabbitmq-operator
|
||||
releaseName: rabbitmq-operator
|
||||
chart: cozy-rabbitmq-operator
|
||||
namespace: cozy-rabbitmq-operator
|
||||
dependsOn: []
|
||||
|
||||
- name: redis-operator
|
||||
releaseName: redis-operator
|
||||
chart: cozy-redis-operator
|
||||
namespace: cozy-redis-operator
|
||||
dependsOn: []
|
||||
|
||||
- name: telepresence
|
||||
releaseName: traffic-manager
|
||||
chart: cozy-telepresence
|
||||
namespace: cozy-telepresence
|
||||
dependsOn: []
|
||||
@@ -1,171 +0,0 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
|
||||
releases:
|
||||
- name: cilium
|
||||
releaseName: cilium
|
||||
chart: cozy-cilium
|
||||
namespace: cozy-cilium
|
||||
privileged: true
|
||||
dependsOn: []
|
||||
|
||||
- name: kubeovn
|
||||
releaseName: kubeovn
|
||||
chart: cozy-kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
privileged: true
|
||||
dependsOn: [cilium]
|
||||
values:
|
||||
cozystack:
|
||||
nodesHash: {{ include "cozystack.master-node-ips" . | sha256sum }}
|
||||
kube-ovn:
|
||||
ipv4:
|
||||
POD_CIDR: "{{ index $cozyConfig.data "ipv4-pod-cidr" }}"
|
||||
POD_GATEWAY: "{{ index $cozyConfig.data "ipv4-pod-gateway" }}"
|
||||
SVC_CIDR: "{{ index $cozyConfig.data "ipv4-svc-cidr" }}"
|
||||
JOIN_CIDR: "{{ index $cozyConfig.data "ipv4-join-cidr" }}"
|
||||
|
||||
- name: cert-manager
|
||||
releaseName: cert-manager
|
||||
chart: cozy-cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: cert-manager-issuers
|
||||
releaseName: cert-manager-issuers
|
||||
chart: cozy-cert-manager-issuers
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: [cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: victoria-metrics-operator
|
||||
releaseName: victoria-metrics-operator
|
||||
chart: cozy-victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
dependsOn: [cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: monitoring
|
||||
releaseName: monitoring
|
||||
chart: cozy-monitoring
|
||||
namespace: cozy-monitoring
|
||||
privileged: true
|
||||
dependsOn: [cilium,kubeovn,victoria-metrics-operator]
|
||||
|
||||
- name: kubevirt-operator
|
||||
releaseName: kubevirt-operator
|
||||
chart: cozy-kubevirt-operator
|
||||
namespace: cozy-kubevirt
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: kubevirt
|
||||
releaseName: kubevirt
|
||||
chart: cozy-kubevirt
|
||||
namespace: cozy-kubevirt
|
||||
privileged: true
|
||||
dependsOn: [cilium,kubeovn,kubevirt-operator]
|
||||
|
||||
- name: kubevirt-cdi-operator
|
||||
releaseName: kubevirt-cdi-operator
|
||||
chart: cozy-kubevirt-cdi-operator
|
||||
namespace: cozy-kubevirt-cdi
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: kubevirt-cdi
|
||||
releaseName: kubevirt-cdi
|
||||
chart: cozy-kubevirt-cdi
|
||||
namespace: cozy-kubevirt-cdi
|
||||
dependsOn: [cilium,kubeovn,kubevirt-cdi-operator]
|
||||
|
||||
- name: metallb
|
||||
releaseName: metallb
|
||||
chart: cozy-metallb
|
||||
namespace: cozy-metallb
|
||||
privileged: true
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: grafana-operator
|
||||
releaseName: grafana-operator
|
||||
chart: cozy-grafana-operator
|
||||
namespace: cozy-grafana-operator
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: mariadb-operator
|
||||
releaseName: mariadb-operator
|
||||
chart: cozy-mariadb-operator
|
||||
namespace: cozy-mariadb-operator
|
||||
dependsOn: [cilium,kubeovn,cert-manager,victoria-metrics-operator]
|
||||
|
||||
- name: postgres-operator
|
||||
releaseName: postgres-operator
|
||||
chart: cozy-postgres-operator
|
||||
namespace: cozy-postgres-operator
|
||||
dependsOn: [cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: rabbitmq-operator
|
||||
releaseName: rabbitmq-operator
|
||||
chart: cozy-rabbitmq-operator
|
||||
namespace: cozy-rabbitmq-operator
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: redis-operator
|
||||
releaseName: redis-operator
|
||||
chart: cozy-redis-operator
|
||||
namespace: cozy-redis-operator
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: piraeus-operator
|
||||
releaseName: piraeus-operator
|
||||
chart: cozy-piraeus-operator
|
||||
namespace: cozy-linstor
|
||||
dependsOn: [cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: linstor
|
||||
releaseName: linstor
|
||||
chart: cozy-linstor
|
||||
namespace: cozy-linstor
|
||||
privileged: true
|
||||
dependsOn: [piraeus-operator,cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: telepresence
|
||||
releaseName: traffic-manager
|
||||
chart: cozy-telepresence
|
||||
namespace: cozy-telepresence
|
||||
dependsOn: [cilium,kubeovn]
|
||||
|
||||
- name: dashboard
|
||||
releaseName: dashboard
|
||||
chart: cozy-dashboard
|
||||
namespace: cozy-dashboard
|
||||
dependsOn: [cilium,kubeovn]
|
||||
{{- if .Capabilities.APIVersions.Has "source.toolkit.fluxcd.io/v1beta2" }}
|
||||
{{- with (lookup "source.toolkit.fluxcd.io/v1beta2" "HelmRepository" "cozy-public" "").items }}
|
||||
values:
|
||||
kubeapps:
|
||||
redis:
|
||||
master:
|
||||
podAnnotations:
|
||||
{{- range $index, $repo := . }}
|
||||
{{- with (($repo.status).artifact).revision }}
|
||||
repository.cozystack.io/{{ $repo.metadata.name }}: {{ quote . }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
- name: kamaji
|
||||
releaseName: kamaji
|
||||
chart: cozy-kamaji
|
||||
namespace: cozy-kamaji
|
||||
dependsOn: [cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: capi-operator
|
||||
releaseName: capi-operator
|
||||
chart: cozy-capi-operator
|
||||
namespace: cozy-cluster-api
|
||||
privileged: true
|
||||
dependsOn: [cilium,kubeovn,cert-manager]
|
||||
|
||||
- name: capi-providers
|
||||
releaseName: capi-providers
|
||||
chart: cozy-capi-providers
|
||||
namespace: cozy-cluster-api
|
||||
privileged: true
|
||||
dependsOn: [cilium,kubeovn,capi-operator]
|
||||
@@ -1,89 +0,0 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
|
||||
releases:
|
||||
- name: cert-manager
|
||||
releaseName: cert-manager
|
||||
chart: cozy-cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: []
|
||||
|
||||
- name: cert-manager-issuers
|
||||
releaseName: cert-manager-issuers
|
||||
chart: cozy-cert-manager-issuers
|
||||
namespace: cozy-cert-manager
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: victoria-metrics-operator
|
||||
releaseName: victoria-metrics-operator
|
||||
chart: cozy-victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: monitoring
|
||||
releaseName: monitoring
|
||||
chart: cozy-monitoring
|
||||
namespace: cozy-monitoring
|
||||
privileged: true
|
||||
dependsOn: [victoria-metrics-operator]
|
||||
|
||||
- name: grafana-operator
|
||||
releaseName: grafana-operator
|
||||
chart: cozy-grafana-operator
|
||||
namespace: cozy-grafana-operator
|
||||
dependsOn: []
|
||||
|
||||
- name: mariadb-operator
|
||||
releaseName: mariadb-operator
|
||||
chart: cozy-mariadb-operator
|
||||
namespace: cozy-mariadb-operator
|
||||
dependsOn: [cert-manager,victoria-metrics-operator]
|
||||
|
||||
- name: postgres-operator
|
||||
releaseName: postgres-operator
|
||||
chart: cozy-postgres-operator
|
||||
namespace: cozy-postgres-operator
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: rabbitmq-operator
|
||||
releaseName: rabbitmq-operator
|
||||
chart: cozy-rabbitmq-operator
|
||||
namespace: cozy-rabbitmq-operator
|
||||
dependsOn: []
|
||||
|
||||
- name: redis-operator
|
||||
releaseName: redis-operator
|
||||
chart: cozy-redis-operator
|
||||
namespace: cozy-redis-operator
|
||||
dependsOn: []
|
||||
|
||||
- name: piraeus-operator
|
||||
releaseName: piraeus-operator
|
||||
chart: cozy-piraeus-operator
|
||||
namespace: cozy-linstor
|
||||
dependsOn: [cert-manager]
|
||||
|
||||
- name: telepresence
|
||||
releaseName: traffic-manager
|
||||
chart: cozy-telepresence
|
||||
namespace: cozy-telepresence
|
||||
dependsOn: []
|
||||
|
||||
- name: dashboard
|
||||
releaseName: dashboard
|
||||
chart: cozy-dashboard
|
||||
namespace: cozy-dashboard
|
||||
dependsOn: []
|
||||
{{- if .Capabilities.APIVersions.Has "source.toolkit.fluxcd.io/v1beta2" }}
|
||||
{{- with (lookup "source.toolkit.fluxcd.io/v1beta2" "HelmRepository" "cozy-public" "").items }}
|
||||
values:
|
||||
kubeapps:
|
||||
redis:
|
||||
master:
|
||||
podAnnotations:
|
||||
{{- range $index, $repo := . }}
|
||||
{{- with (($repo.status).artifact).revision }}
|
||||
repository.cozystack.io/{{ $repo.metadata.name }}: {{ quote . }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -1,7 +1,7 @@
|
||||
{{/*
|
||||
Get IP-addresses of master nodes
|
||||
*/}}
|
||||
{{- define "cozystack.master-node-ips" -}}
|
||||
{{- define "master.nodeIPs" -}}
|
||||
{{- $nodes := lookup "v1" "Node" "" "" -}}
|
||||
{{- $ips := list -}}
|
||||
{{- range $node := $nodes.items -}}
|
||||
|
||||
@@ -1,10 +1,7 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
{{- $bundleName := index $cozyConfig.data "bundle-name" }}
|
||||
{{- $bundle := tpl (.Files.Get (printf "bundles/%s.yaml" $bundleName)) . | fromYaml }}
|
||||
{{- $host := "example.org" }}
|
||||
{{- $tenantRoot := list }}
|
||||
{{- if .Capabilities.APIVersions.Has "helm.toolkit.fluxcd.io/v2beta2" }}
|
||||
{{- $tenantRoot = lookup "helm.toolkit.fluxcd.io/v2beta2" "HelmRelease" "tenant-root" "tenant-root" }}
|
||||
{{- if .Capabilities.APIVersions.Has "helm.toolkit.fluxcd.io/v2beta1" }}
|
||||
{{- $tenantRoot = lookup "helm.toolkit.fluxcd.io/v2beta1" "HelmRelease" "tenant-root" "tenant-root" }}
|
||||
{{- end }}
|
||||
{{- if and $tenantRoot $tenantRoot.spec $tenantRoot.spec.values $tenantRoot.spec.values.host }}
|
||||
{{- $host = $tenantRoot.spec.values.host }}
|
||||
@@ -22,7 +19,7 @@ metadata:
|
||||
namespace.cozystack.io/host: "{{ $host }}"
|
||||
name: tenant-root
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta2
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: tenant-root
|
||||
@@ -48,9 +45,7 @@ spec:
|
||||
values:
|
||||
host: "{{ $host }}"
|
||||
dependsOn:
|
||||
{{- range $x := $bundle.releases }}
|
||||
{{- if has $x.name (list "cilium" "kubeovn") }}
|
||||
- name: {{ $x.name }}
|
||||
namespace: {{ $x.namespace }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
|
||||
@@ -1,27 +1,13 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
{{- $bundleName := index $cozyConfig.data "bundle-name" }}
|
||||
{{- $bundle := tpl (.Files.Get (printf "bundles/%s.yaml" $bundleName)) . | fromYaml }}
|
||||
{{- $dependencyNamespaces := dict }}
|
||||
{{- $disabledComponents := splitList "," ((index $cozyConfig.data "bundle-disable") | default "") }}
|
||||
|
||||
{{/* collect dependency namespaces from releases */}}
|
||||
{{- range $x := $bundle.releases }}
|
||||
{{- $_ := set $dependencyNamespaces $x.name $x.namespace }}
|
||||
{{- end }}
|
||||
|
||||
{{- range $x := $bundle.releases }}
|
||||
{{- if not (has $x.name $disabledComponents) }}
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta2
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: {{ $x.name }}
|
||||
namespace: {{ $x.namespace }}
|
||||
name: cilium
|
||||
namespace: cozy-cilium
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: {{ $x.releaseName | default $x.name }}
|
||||
releaseName: cilium
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
@@ -30,31 +16,729 @@ spec:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: {{ $x.chart }}
|
||||
chart: cozy-cilium
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: kubeovn
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-kubeovn
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
{{- $values := dict }}
|
||||
{{- with $x.values }}
|
||||
{{- $values = merge . $values }}
|
||||
{{- end }}
|
||||
{{- with index $cozyConfig.data (printf "values-%s" $x.name) }}
|
||||
{{- $values = merge (fromYaml .) $values }}
|
||||
{{- end }}
|
||||
{{- with $values }}
|
||||
values:
|
||||
{{- toYaml . | nindent 4}}
|
||||
{{- end }}
|
||||
{{- with $x.dependsOn }}
|
||||
cozystack:
|
||||
configHash: {{ index (lookup "v1" "ConfigMap" "cozy-system" "cozystack") "data" | toJson | sha256sum }}
|
||||
nodesHash: {{ include "master.nodeIPs" . | sha256sum }}
|
||||
dependsOn:
|
||||
{{- range $dep := . }}
|
||||
{{- if not (has $dep $disabledComponents) }}
|
||||
- name: {{ $dep }}
|
||||
namespace: {{ index $dependencyNamespaces $dep }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: cozy-fluxcd
|
||||
namespace: cozy-fluxcd
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: fluxcd
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-fluxcd
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: cert-manager
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-cert-manager
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: cert-manager-issuers
|
||||
namespace: cozy-cert-manager
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: cert-manager-issuers
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-cert-manager-issuers
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: victoria-metrics-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-victoria-metrics-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: monitoring
|
||||
namespace: cozy-monitoring
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: monitoring
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-monitoring
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: kubevirt-operator
|
||||
namespace: cozy-kubevirt
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: kubevirt-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-kubevirt-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: kubevirt
|
||||
namespace: cozy-kubevirt
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: kubevirt
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-kubevirt
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: kubevirt-operator
|
||||
namespace: cozy-kubevirt
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: kubevirt-cdi-operator
|
||||
namespace: cozy-kubevirt-cdi
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: kubevirt-cdi-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-kubevirt-cdi-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: kubevirt-cdi
|
||||
namespace: cozy-kubevirt-cdi
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: kubevirt-cdi
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-kubevirt-cdi
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: kubevirt-cdi-operator
|
||||
namespace: cozy-kubevirt-cdi
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: metallb
|
||||
namespace: cozy-metallb
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: metallb
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-metallb
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: grafana-operator
|
||||
namespace: cozy-grafana-operator
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: grafana-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-grafana-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: mariadb-operator
|
||||
namespace: cozy-mariadb-operator
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: mariadb-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-mariadb-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
- name: victoria-metrics-operator
|
||||
namespace: cozy-victoria-metrics-operator
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: postgres-operator
|
||||
namespace: cozy-postgres-operator
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: postgres-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-postgres-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: rabbitmq-operator
|
||||
namespace: cozy-rabbitmq-operator
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: rabbitmq-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-rabbitmq-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: redis-operator
|
||||
namespace: cozy-redis-operator
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: redis-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-redis-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: piraeus-operator
|
||||
namespace: cozy-linstor
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: piraeus-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-piraeus-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: linstor
|
||||
namespace: cozy-linstor
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: linstor
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-linstor
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: piraeus-operator
|
||||
namespace: cozy-linstor
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: telepresence
|
||||
namespace: cozy-telepresence
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: traffic-manager
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-telepresence
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: dashboard
|
||||
namespace: cozy-dashboard
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: dashboard
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-dashboard
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: kamaji
|
||||
namespace: cozy-kamaji
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: kamaji
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-kamaji
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: capi-operator
|
||||
namespace: cozy-cluster-api
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: capi-operator
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-capi-operator
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
- name: cert-manager
|
||||
namespace: cozy-cert-manager
|
||||
---
|
||||
apiVersion: helm.toolkit.fluxcd.io/v2beta1
|
||||
kind: HelmRelease
|
||||
metadata:
|
||||
name: capi-providers
|
||||
namespace: cozy-cluster-api
|
||||
labels:
|
||||
cozystack.io/repository: system
|
||||
spec:
|
||||
interval: 1m
|
||||
releaseName: capi-providers
|
||||
install:
|
||||
remediation:
|
||||
retries: -1
|
||||
upgrade:
|
||||
remediation:
|
||||
retries: -1
|
||||
chart:
|
||||
spec:
|
||||
chart: cozy-capi-providers
|
||||
reconcileStrategy: Revision
|
||||
sourceRef:
|
||||
kind: HelmRepository
|
||||
name: cozystack-system
|
||||
namespace: cozy-system
|
||||
dependsOn:
|
||||
- name: capi-operator
|
||||
namespace: cozy-cluster-api
|
||||
- name: cilium
|
||||
namespace: cozy-cilium
|
||||
- name: kubeovn
|
||||
namespace: cozy-kubeovn
|
||||
|
||||
@@ -1,33 +1,13 @@
|
||||
{{- $cozyConfig := lookup "v1" "ConfigMap" "cozy-system" "cozystack" }}
|
||||
{{- $bundleName := index $cozyConfig.data "bundle-name" }}
|
||||
{{- $bundle := tpl (.Files.Get (printf "bundles/%s.yaml" $bundleName)) . | fromYaml }}
|
||||
{{- $namespaces := dict }}
|
||||
|
||||
{{/* collect namespaces from releases */}}
|
||||
{{- range $x := $bundle.releases }}
|
||||
{{- if not (hasKey $namespaces $x.namespace) }}
|
||||
{{- $_ := set $namespaces $x.namespace false }}
|
||||
{{- end }}
|
||||
{{/* if at least one release requires a privileged namespace, then it should be privileged */}}
|
||||
{{- if or $x.privileged (index $namespaces $x.namespace) }}
|
||||
{{- $_ := set $namespaces $x.namespace true }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{/* Add extra namespaces */}}
|
||||
{{- $_ := set $namespaces "cozy-public" false }}
|
||||
{{- $_ := set $namespaces "cozy-fluxcd" false }}
|
||||
|
||||
{{- range $namespace, $privileged := $namespaces }}
|
||||
{{- range $ns := .Values.namespaces }}
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Namespace
|
||||
metadata:
|
||||
annotations:
|
||||
"helm.sh/resource-policy": keep
|
||||
{{- if $privileged }}
|
||||
{{- if $ns.privileged }}
|
||||
labels:
|
||||
pod-security.kubernetes.io/enforce: privileged
|
||||
{{- end }}
|
||||
name: {{ $namespace }}
|
||||
name: {{ $ns.name }}
|
||||
{{- end }}
|
||||
|
||||
30
packages/core/platform/values.yaml
Normal file
30
packages/core/platform/values.yaml
Normal file
@@ -0,0 +1,30 @@
|
||||
namespaces:
|
||||
- name: cozy-public
|
||||
- name: cozy-system
|
||||
privileged: true
|
||||
- name: cozy-cert-manager
|
||||
- name: cozy-cilium
|
||||
privileged: true
|
||||
- name: cozy-fluxcd
|
||||
- name: cozy-grafana-operator
|
||||
- name: cozy-kamaji
|
||||
- name: cozy-cluster-api
|
||||
privileged: true # for capk only
|
||||
- name: cozy-dashboard
|
||||
- name: cozy-kubeovn
|
||||
privileged: true
|
||||
- name: cozy-kubevirt
|
||||
privileged: true
|
||||
- name: cozy-kubevirt-cdi
|
||||
- name: cozy-linstor
|
||||
privileged: true
|
||||
- name: cozy-mariadb-operator
|
||||
- name: cozy-metallb
|
||||
privileged: true
|
||||
- name: cozy-monitoring
|
||||
privileged: true
|
||||
- name: cozy-postgres-operator
|
||||
- name: cozy-rabbitmq-operator
|
||||
- name: cozy-redis-operator
|
||||
- name: cozy-telepresence
|
||||
- name: cozy-victoria-metrics-operator
|
||||
@@ -1,5 +1,4 @@
|
||||
OUT=../../_out/repos/system
|
||||
VERSION := 0.2.0
|
||||
|
||||
gen: fix-chartnames
|
||||
|
||||
@@ -10,4 +9,4 @@ repo: fix-chartnames
|
||||
cd "$(OUT)" && helm repo index .
|
||||
|
||||
fix-chartnames:
|
||||
find . -name Chart.yaml -maxdepth 2 | awk -F/ '{print $$2}' | while read i; do printf "name: cozy-%s\nversion: $(VERSION)\n" "$$i" > "$$i/Chart.yaml"; done
|
||||
find . -name Chart.yaml -maxdepth 2 | awk -F/ '{print $$2}' | while read i; do printf "name: cozy-%s\nversion: 1.0.0\n" "$$i" > "$$i/Chart.yaml"; done
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-capi-operator
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-capi-providers
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-cert-manager-issuers
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-cert-manager
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-cilium
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -2,18 +2,18 @@ NAMESPACE=cozy-cilium
|
||||
NAME=cilium
|
||||
|
||||
show:
|
||||
kubectl get hr -n cozy-cilium cilium -o jsonpath='{.spec.values}' | helm template --dry-run=server -n $(NAMESPACE) $(NAME) . -f -
|
||||
helm template --dry-run=server -n $(NAMESPACE) $(NAME) .
|
||||
|
||||
apply:
|
||||
kubectl get hr -n cozy-cilium cilium -o jsonpath='{.spec.values}' | helm upgrade -i -n $(NAMESPACE) $(NAME) . -f -
|
||||
helm upgrade -i -n $(NAMESPACE) $(NAME) .
|
||||
|
||||
diff:
|
||||
kubectl get hr -n cozy-cilium cilium -o jsonpath='{.spec.values}' | helm diff upgrade --allow-unreleased --normalize-manifests -n $(NAMESPACE) $(NAME) . -f -
|
||||
helm diff upgrade --allow-unreleased --normalize-manifests -n $(NAMESPACE) $(NAME) .
|
||||
|
||||
update:
|
||||
rm -rf charts
|
||||
helm repo add cilium https://helm.cilium.io/
|
||||
helm repo update cilium
|
||||
helm pull cilium/cilium --untar --untardir charts --version 1.14
|
||||
helm pull cilium/cilium --untar --untardir charts
|
||||
sed -i -e '/Used in iptables/d' -e '/SYS_MODULE/d' charts/cilium/values.yaml
|
||||
patch -p3 --no-backup-if-mismatch < patches/fix-cgroups.patch
|
||||
patch -p3 < patches/fix-cgroups.patch
|
||||
|
||||
@@ -122,7 +122,7 @@ annotations:
|
||||
description: |
|
||||
CiliumPodIPPool defines an IP pool that can be used for pooled IPAM (i.e. the multi-pool IPAM mode).
|
||||
apiVersion: v2
|
||||
appVersion: 1.14.9
|
||||
appVersion: 1.14.5
|
||||
description: eBPF-based Networking, Security, and Observability
|
||||
home: https://cilium.io/
|
||||
icon: https://cdn.jsdelivr.net/gh/cilium/cilium@v1.14/Documentation/images/logo-solo.svg
|
||||
@@ -138,4 +138,4 @@ kubeVersion: '>= 1.16.0-0'
|
||||
name: cilium
|
||||
sources:
|
||||
- https://github.com/cilium/cilium
|
||||
version: 1.14.9
|
||||
version: 1.14.5
|
||||
|
||||
@@ -1,6 +1,6 @@
|
||||
# cilium
|
||||
|
||||
 
|
||||
 
|
||||
|
||||
Cilium is open source software for providing and transparently securing
|
||||
network connectivity and loadbalancing between application workloads such as
|
||||
@@ -76,7 +76,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| authentication.mutual.spire.install.agent.securityContext | object | `{}` | Security context to be added to spire agent containers. SecurityContext holds pod-level security attributes and common container settings. ref: https://kubernetes.io/docs/tasks/configure-pod-container/security-context/#set-the-security-context-for-a-container |
|
||||
| authentication.mutual.spire.install.agent.serviceAccount | object | `{"create":true,"name":"spire-agent"}` | SPIRE agent service account |
|
||||
| authentication.mutual.spire.install.agent.skipKubeletVerification | bool | `true` | SPIRE Workload Attestor kubelet verification. |
|
||||
| authentication.mutual.spire.install.agent.tolerations | list | `[{"effect":"NoSchedule","key":"node.kubernetes.io/not-ready"},{"effect":"NoSchedule","key":"node-role.kubernetes.io/master"},{"effect":"NoSchedule","key":"node-role.kubernetes.io/control-plane"},{"effect":"NoSchedule","key":"node.cloudprovider.kubernetes.io/uninitialized","value":"true"},{"key":"CriticalAddonsOnly","operator":"Exists"}]` | SPIRE agent tolerations configuration By default it follows the same tolerations as the agent itself to allow the Cilium agent on this node to connect to SPIRE. ref: https://kubernetes.io/docs/concepts/scheduling-eviction/taint-and-toleration/ |
|
||||
| authentication.mutual.spire.install.agent.tolerations | list | `[]` | SPIRE agent tolerations configuration ref: https://kubernetes.io/docs/concepts/scheduling-eviction/taint-and-toleration/ |
|
||||
| authentication.mutual.spire.install.enabled | bool | `true` | Enable SPIRE installation. This will only take effect only if authentication.mutual.spire.enabled is true |
|
||||
| authentication.mutual.spire.install.namespace | string | `"cilium-spire"` | SPIRE namespace to install into |
|
||||
| authentication.mutual.spire.install.server.affinity | object | `{}` | SPIRE server affinity configuration |
|
||||
@@ -155,12 +155,12 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| clustermesh.apiserver.extraEnv | list | `[]` | Additional clustermesh-apiserver environment variables. |
|
||||
| clustermesh.apiserver.extraVolumeMounts | list | `[]` | Additional clustermesh-apiserver volumeMounts. |
|
||||
| clustermesh.apiserver.extraVolumes | list | `[]` | Additional clustermesh-apiserver volumes. |
|
||||
| clustermesh.apiserver.image | object | `{"digest":"sha256:5c16f8b8e22ce41e11998e70846fbcecea3a6b683a38253809ead8d871f6d8a3","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/clustermesh-apiserver","tag":"v1.14.9","useDigest":true}` | Clustermesh API server image. |
|
||||
| clustermesh.apiserver.image | object | `{"digest":"sha256:7eaa35cf5452c43b1f7d0cde0d707823ae7e49965bcb54c053e31ea4e04c3d96","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/clustermesh-apiserver","tag":"v1.14.5","useDigest":true}` | Clustermesh API server image. |
|
||||
| clustermesh.apiserver.kvstoremesh.enabled | bool | `false` | Enable KVStoreMesh. KVStoreMesh caches the information retrieved from the remote clusters in the local etcd instance. |
|
||||
| clustermesh.apiserver.kvstoremesh.extraArgs | list | `[]` | Additional KVStoreMesh arguments. |
|
||||
| clustermesh.apiserver.kvstoremesh.extraEnv | list | `[]` | Additional KVStoreMesh environment variables. |
|
||||
| clustermesh.apiserver.kvstoremesh.extraVolumeMounts | list | `[]` | Additional KVStoreMesh volumeMounts. |
|
||||
| clustermesh.apiserver.kvstoremesh.image | object | `{"digest":"sha256:9d9efb25806660f3663b9cd803fb8679f2b115763470002a9770e2c1eb1e5b22","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/kvstoremesh","tag":"v1.14.9","useDigest":true}` | KVStoreMesh image. |
|
||||
| clustermesh.apiserver.kvstoremesh.image | object | `{"digest":"sha256:d7137edd0efa2b1407b20088af3980a9993bb616d85bf9b55ea2891d1b99023a","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/kvstoremesh","tag":"v1.14.5","useDigest":true}` | KVStoreMesh image. |
|
||||
| clustermesh.apiserver.kvstoremesh.resources | object | `{}` | Resource requests and limits for the KVStoreMesh container |
|
||||
| clustermesh.apiserver.kvstoremesh.securityContext | object | `{"allowPrivilegeEscalation":false,"capabilities":{"drop":["ALL"]}}` | KVStoreMesh Security context |
|
||||
| clustermesh.apiserver.metrics.enabled | bool | `true` | Enables exporting apiserver metrics in OpenMetrics format. |
|
||||
@@ -300,7 +300,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| eni.subnetIDsFilter | list | `[]` | Filter via subnet IDs which will dictate which subnets are going to be used to create new ENIs Important note: This requires that each instance has an ENI with a matching subnet attached when Cilium is deployed. If you only want to control subnets for ENIs attached by Cilium, use the CNI configuration file settings (cni.customConf) instead. |
|
||||
| eni.subnetTagsFilter | list | `[]` | Filter via tags (k=v) which will dictate which subnets are going to be used to create new ENIs Important note: This requires that each instance has an ENI with a matching subnet attached when Cilium is deployed. If you only want to control subnets for ENIs attached by Cilium, use the CNI configuration file settings (cni.customConf) instead. |
|
||||
| eni.updateEC2AdapterLimitViaAPI | bool | `true` | Update ENI Adapter limits from the EC2 API |
|
||||
| envoy.affinity | object | `{"nodeAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":{"nodeSelectorTerms":[{"matchExpressions":[{"key":"cilium.io/no-schedule","operator":"NotIn","values":["true"]}]}]}},"podAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"cilium"}},"topologyKey":"kubernetes.io/hostname"}]},"podAntiAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"cilium-envoy"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for cilium-envoy. |
|
||||
| envoy.affinity | object | `{"podAntiAffinity":{"requiredDuringSchedulingIgnoredDuringExecution":[{"labelSelector":{"matchLabels":{"k8s-app":"cilium-envoy"}},"topologyKey":"kubernetes.io/hostname"}]}}` | Affinity for cilium-envoy. |
|
||||
| envoy.connectTimeoutSeconds | int | `2` | Time in seconds after which a TCP connection attempt times out |
|
||||
| envoy.dnsPolicy | string | `nil` | DNS policy for Cilium envoy pods. Ref: https://kubernetes.io/docs/concepts/services-networking/dns-pod-service/#pod-s-dns-policy |
|
||||
| envoy.enabled | bool | `false` | Enable Envoy Proxy in standalone DaemonSet. |
|
||||
@@ -312,7 +312,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| envoy.extraVolumes | list | `[]` | Additional envoy volumes. |
|
||||
| envoy.healthPort | int | `9878` | TCP port for the health API. |
|
||||
| envoy.idleTimeoutDurationSeconds | int | `60` | Set Envoy upstream HTTP idle connection timeout seconds. Does not apply to connections with pending requests. Default 60s |
|
||||
| envoy.image | object | `{"digest":"sha256:39b75548447978230dedcf25da8940e4d3540c741045ef391a8e74dbb9661a86","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium-envoy","tag":"v1.26.7-bbde4095997ea57ead209f56158790d47224a0f5","useDigest":true}` | Envoy container image. |
|
||||
| envoy.image | object | `{"digest":"sha256:992998398dadfff7117bfa9fdb7c9474fefab7f0237263f7c8114e106c67baca","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium-envoy","tag":"v1.26.6-ad82c7c56e88989992fd25d8d67747de865c823b","useDigest":true}` | Envoy container image. |
|
||||
| envoy.livenessProbe.failureThreshold | int | `10` | failure threshold of liveness probe |
|
||||
| envoy.livenessProbe.periodSeconds | int | `30` | interval between checks of the liveness probe |
|
||||
| envoy.log.format | string | `"[%Y-%m-%d %T.%e][%t][%l][%n] [%g:%#] %v"` | The format string to use for laying out the log message metadata of Envoy. |
|
||||
@@ -324,15 +324,14 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| envoy.podLabels | object | `{}` | Labels to be added to envoy pods |
|
||||
| envoy.podSecurityContext | object | `{}` | Security Context for cilium-envoy pods. |
|
||||
| envoy.priorityClassName | string | `nil` | The priority class to use for cilium-envoy. |
|
||||
| envoy.prometheus | object | `{"enabled":true,"port":"9964","serviceMonitor":{"annotations":{},"enabled":false,"interval":"10s","labels":{},"metricRelabelings":null,"relabelings":[{"replacement":"${1}","sourceLabels":["__meta_kubernetes_pod_node_name"],"targetLabel":"node"}]}}` | Configure Cilium Envoy Prometheus options. Note that some of these apply to either cilium-agent or cilium-envoy. |
|
||||
| envoy.prometheus.enabled | bool | `true` | Enable prometheus metrics for cilium-envoy |
|
||||
| envoy.prometheus.port | string | `"9964"` | Serve prometheus metrics for cilium-envoy on the configured port |
|
||||
| envoy.prometheus.serviceMonitor.annotations | object | `{}` | Annotations to add to ServiceMonitor cilium-envoy |
|
||||
| envoy.prometheus.serviceMonitor.enabled | bool | `false` | Enable service monitors. This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/main/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml) Note that this setting applies to both cilium-envoy _and_ cilium-agent with Envoy enabled. |
|
||||
| envoy.prometheus.serviceMonitor.enabled | bool | `false` | Enable service monitors. This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/main/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml) |
|
||||
| envoy.prometheus.serviceMonitor.interval | string | `"10s"` | Interval for scrape metrics. |
|
||||
| envoy.prometheus.serviceMonitor.labels | object | `{}` | Labels to add to ServiceMonitor cilium-envoy |
|
||||
| envoy.prometheus.serviceMonitor.metricRelabelings | string | `nil` | Metrics relabeling configs for the ServiceMonitor cilium-envoy or for cilium-agent with Envoy configured. |
|
||||
| envoy.prometheus.serviceMonitor.relabelings | list | `[{"replacement":"${1}","sourceLabels":["__meta_kubernetes_pod_node_name"],"targetLabel":"node"}]` | Relabeling configs for the ServiceMonitor cilium-envoy or for cilium-agent with Envoy configured. |
|
||||
| envoy.prometheus.serviceMonitor.metricRelabelings | string | `nil` | Metrics relabeling configs for the ServiceMonitor cilium-envoy |
|
||||
| envoy.prometheus.serviceMonitor.relabelings | list | `[{"replacement":"${1}","sourceLabels":["__meta_kubernetes_pod_node_name"],"targetLabel":"node"}]` | Relabeling configs for the ServiceMonitor cilium-envoy |
|
||||
| envoy.readinessProbe.failureThreshold | int | `3` | failure threshold of readiness probe |
|
||||
| envoy.readinessProbe.periodSeconds | int | `30` | interval between checks of the readiness probe |
|
||||
| envoy.resources | object | `{}` | Envoy resource limits & requests ref: https://kubernetes.io/docs/concepts/configuration/manage-resources-containers/ |
|
||||
@@ -419,7 +418,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| hubble.relay.extraVolumes | list | `[]` | Additional hubble-relay volumes. |
|
||||
| hubble.relay.gops.enabled | bool | `true` | Enable gops for hubble-relay |
|
||||
| hubble.relay.gops.port | int | `9893` | Configure gops listen port for hubble-relay |
|
||||
| hubble.relay.image | object | `{"digest":"sha256:f506f3c6e0a979437cde79eb781654fda4f10ddb5642cebc4dc81254cfb7eeaa","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-relay","tag":"v1.14.9","useDigest":true}` | Hubble-relay container image. |
|
||||
| hubble.relay.image | object | `{"digest":"sha256:dbef89f924a927043d02b40c18e417c1ea0e8f58b44523b80fef7e3652db24d4","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-relay","tag":"v1.14.5","useDigest":true}` | Hubble-relay container image. |
|
||||
| hubble.relay.listenHost | string | `""` | Host to listen to. Specify an empty string to bind to all the interfaces. |
|
||||
| hubble.relay.listenPort | string | `"4245"` | Port to listen to. |
|
||||
| hubble.relay.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for pod assignment ref: https://kubernetes.io/docs/concepts/scheduling-eviction/assign-pod-node/#nodeselector |
|
||||
@@ -476,7 +475,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| hubble.ui.backend.extraEnv | list | `[]` | Additional hubble-ui backend environment variables. |
|
||||
| hubble.ui.backend.extraVolumeMounts | list | `[]` | Additional hubble-ui backend volumeMounts. |
|
||||
| hubble.ui.backend.extraVolumes | list | `[]` | Additional hubble-ui backend volumes. |
|
||||
| hubble.ui.backend.image | object | `{"digest":"sha256:1e7657d997c5a48253bb8dc91ecee75b63018d16ff5e5797e5af367336bc8803","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-ui-backend","tag":"v0.13.0","useDigest":true}` | Hubble-ui backend image. |
|
||||
| hubble.ui.backend.image | object | `{"digest":"sha256:1f86f3400827a0451e6332262467f894eeb7caf0eb8779bd951e2caa9d027cbe","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-ui-backend","tag":"v0.12.1","useDigest":true}` | Hubble-ui backend image. |
|
||||
| hubble.ui.backend.resources | object | `{}` | Resource requests and limits for the 'backend' container of the 'hubble-ui' deployment. |
|
||||
| hubble.ui.backend.securityContext | object | `{}` | Hubble-ui backend security context. |
|
||||
| hubble.ui.baseUrl | string | `"/"` | Defines base url prefix for all hubble-ui http requests. It needs to be changed in case if ingress for hubble-ui is configured under some sub-path. Trailing `/` is required for custom path, ex. `/service-map/` |
|
||||
@@ -484,7 +483,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| hubble.ui.frontend.extraEnv | list | `[]` | Additional hubble-ui frontend environment variables. |
|
||||
| hubble.ui.frontend.extraVolumeMounts | list | `[]` | Additional hubble-ui frontend volumeMounts. |
|
||||
| hubble.ui.frontend.extraVolumes | list | `[]` | Additional hubble-ui frontend volumes. |
|
||||
| hubble.ui.frontend.image | object | `{"digest":"sha256:7d663dc16538dd6e29061abd1047013a645e6e69c115e008bee9ea9fef9a6666","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-ui","tag":"v0.13.0","useDigest":true}` | Hubble-ui frontend image. |
|
||||
| hubble.ui.frontend.image | object | `{"digest":"sha256:9e5f81ee747866480ea1ac4630eb6975ff9227f9782b7c93919c081c33f38267","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/hubble-ui","tag":"v0.12.1","useDigest":true}` | Hubble-ui frontend image. |
|
||||
| hubble.ui.frontend.resources | object | `{}` | Resource requests and limits for the 'frontend' container of the 'hubble-ui' deployment. |
|
||||
| hubble.ui.frontend.securityContext | object | `{}` | Hubble-ui frontend security context. |
|
||||
| hubble.ui.frontend.server.ipv6 | object | `{"enabled":true}` | Controls server listener for ipv6 |
|
||||
@@ -511,7 +510,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| hubble.ui.updateStrategy | object | `{"rollingUpdate":{"maxUnavailable":1},"type":"RollingUpdate"}` | hubble-ui update strategy. |
|
||||
| identityAllocationMode | string | `"crd"` | Method to use for identity allocation (`crd` or `kvstore`). |
|
||||
| identityChangeGracePeriod | string | `"5s"` | Time to wait before using new identity on endpoint identity change. |
|
||||
| image | object | `{"digest":"sha256:4ef1eb7a3bc39d0fefe14685e6c0d4e01301c40df2a89bc93ffca9a1ab927301","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium","tag":"v1.14.9","useDigest":true}` | Agent container image. |
|
||||
| image | object | `{"digest":"sha256:d3b287029755b6a47dee01420e2ea469469f1b174a2089c10af7e5e9289ef05b","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium","tag":"v1.14.5","useDigest":true}` | Agent container image. |
|
||||
| imagePullSecrets | string | `nil` | Configure image pull secrets for pulling container images |
|
||||
| ingressController.default | bool | `false` | Set cilium ingress controller to be the default ingress controller This will let cilium ingress controller route entries without ingress class set |
|
||||
| ingressController.defaultSecretName | string | `nil` | Default secret name for ingresses without .spec.tls[].secretName set. |
|
||||
@@ -619,7 +618,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| operator.extraVolumes | list | `[]` | Additional cilium-operator volumes. |
|
||||
| operator.identityGCInterval | string | `"15m0s"` | Interval for identity garbage collection. |
|
||||
| operator.identityHeartbeatTimeout | string | `"30m0s"` | Timeout for identity heartbeats. |
|
||||
| operator.image | object | `{"alibabacloudDigest":"sha256:765314779093b54750f83280f009229f20fe1f28466a633d9bb4143d2ad669c5","awsDigest":"sha256:041ad5b49ae63ba0f1974e1a1d9ebf9f52541cd2813088fa687f9d544125a1ec","azureDigest":"sha256:2d3b9d868eb03fa9256d34192a734a2abab283f527a9c97b7cefcd3401649d17","genericDigest":"sha256:1552d653870dd8ebbd16ee985a5497dd78a2097370978b0cfbd2da2072f30712","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/operator","suffix":"","tag":"v1.14.9","useDigest":true}` | cilium-operator image. |
|
||||
| operator.image | object | `{"alibabacloudDigest":"sha256:e0152c498ba73c56a82eee2a706c8f400e9a6999c665af31a935bdf08e659bc3","awsDigest":"sha256:785ccf1267d0ed3ba9e4bd8166577cb4f9e4ce996af26b27c9d5c554a0d5b09a","azureDigest":"sha256:9203f5583aa34e716d7a6588ebd144e43ce3b77873f578fc12b2679e33591353","genericDigest":"sha256:303f9076bdc73b3fc32aaedee64a14f6f44c8bb08ee9e3956d443021103ebe7a","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/operator","suffix":"","tag":"v1.14.5","useDigest":true}` | cilium-operator image. |
|
||||
| operator.nodeGCInterval | string | `"5m0s"` | Interval for cilium node garbage collection. |
|
||||
| operator.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for cilium-operator pod assignment ref: https://kubernetes.io/docs/concepts/scheduling-eviction/assign-pod-node/#nodeselector |
|
||||
| operator.podAnnotations | object | `{}` | Annotations to be added to cilium-operator pods |
|
||||
@@ -666,7 +665,7 @@ contributors across the globe, there is almost always someone available to help.
|
||||
| preflight.extraEnv | list | `[]` | Additional preflight environment variables. |
|
||||
| preflight.extraVolumeMounts | list | `[]` | Additional preflight volumeMounts. |
|
||||
| preflight.extraVolumes | list | `[]` | Additional preflight volumes. |
|
||||
| preflight.image | object | `{"digest":"sha256:4ef1eb7a3bc39d0fefe14685e6c0d4e01301c40df2a89bc93ffca9a1ab927301","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium","tag":"v1.14.9","useDigest":true}` | Cilium pre-flight image. |
|
||||
| preflight.image | object | `{"digest":"sha256:d3b287029755b6a47dee01420e2ea469469f1b174a2089c10af7e5e9289ef05b","override":null,"pullPolicy":"IfNotPresent","repository":"quay.io/cilium/cilium","tag":"v1.14.5","useDigest":true}` | Cilium pre-flight image. |
|
||||
| preflight.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for preflight pod assignment ref: https://kubernetes.io/docs/concepts/scheduling-eviction/assign-pod-node/#nodeselector |
|
||||
| preflight.podAnnotations | object | `{}` | Annotations to be added to preflight pods |
|
||||
| preflight.podDisruptionBudget.enabled | bool | `false` | enable PodDisruptionBudget ref: https://kubernetes.io/docs/concepts/workloads/pods/disruptions/ |
|
||||
|
||||
@@ -11,9 +11,9 @@ set -o nounset
|
||||
# dependencies on anything that is part of the startup script
|
||||
# itself, and can be safely run multiple times per node (e.g. in
|
||||
# case of a restart).
|
||||
if [[ "$(iptables-save | grep -E -c 'AWS-SNAT-CHAIN|AWS-CONNMARK-CHAIN')" != "0" ]];
|
||||
if [[ "$(iptables-save | grep -c 'AWS-SNAT-CHAIN|AWS-CONNMARK-CHAIN')" != "0" ]];
|
||||
then
|
||||
echo 'Deleting iptables rules created by the AWS CNI VPC plugin'
|
||||
iptables-save | grep -E -v 'AWS-SNAT-CHAIN|AWS-CONNMARK-CHAIN' | iptables-restore
|
||||
iptables-save | grep -v 'AWS-SNAT-CHAIN|AWS-CONNMARK-CHAIN' | iptables-restore
|
||||
fi
|
||||
echo 'Done!'
|
||||
|
||||
@@ -100,7 +100,7 @@ then
|
||||
# Since that version containerd no longer allows missing configuration for the CNI,
|
||||
# not even for pods with hostNetwork set to true. Thus, we add a temporary one.
|
||||
# This will be replaced with the real config by the agent pod.
|
||||
echo -e '{\n\t"cniVersion": "0.3.1",\n\t"name": "cilium",\n\t"type": "cilium-cni"\n}' > /etc/cni/net.d/05-cilium.conf
|
||||
echo -e "{\n\t"cniVersion": "0.3.1",\n\t"name": "cilium",\n\t"type": "cilium-cni"\n}" > /etc/cni/net.d/05-cilium.conf
|
||||
fi
|
||||
|
||||
# Start containerd. It won't create it's CNI configuration file anymore.
|
||||
|
||||
@@ -447,9 +447,6 @@ spec:
|
||||
volumeMounts:
|
||||
- name: tmp
|
||||
mountPath: /tmp
|
||||
{{- with .Values.extraVolumeMounts }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
terminationMessagePolicy: FallbackToLogsOnError
|
||||
{{- if .Values.cgroup.autoMount.enabled }}
|
||||
# Required to mount cgroup2 filesystem on the underlying Kubernetes node.
|
||||
|
||||
@@ -34,20 +34,6 @@ spec:
|
||||
metricRelabelings:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- if .Values.envoy.prometheus.serviceMonitor.enabled }}
|
||||
- port: envoy-metrics
|
||||
interval: {{ .Values.envoy.prometheus.serviceMonitor.interval | quote }}
|
||||
honorLabels: true
|
||||
path: /metrics
|
||||
{{- with .Values.envoy.prometheus.serviceMonitor.relabelings }}
|
||||
relabelings:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- with .Values.envoy.prometheus.serviceMonitor.metricRelabelings }}
|
||||
metricRelabelings:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
targetLabels:
|
||||
- k8s-app
|
||||
{{- end }}
|
||||
|
||||
@@ -13,7 +13,6 @@
|
||||
{{- $fragmentTracking := "true" -}}
|
||||
{{- $defaultKubeProxyReplacement := "false" -}}
|
||||
{{- $azureUsePrimaryAddress := "true" -}}
|
||||
{{- $defaultDNSProxyEnableTransparentMode := "false" -}}
|
||||
|
||||
{{- /* Default values when 1.8 was initially deployed */ -}}
|
||||
{{- if semverCompare ">=1.8" (default "1.8" .Values.upgradeCompatibility) -}}
|
||||
@@ -49,7 +48,6 @@
|
||||
{{- $azureUsePrimaryAddress = "false" -}}
|
||||
{{- end }}
|
||||
{{- $defaultKubeProxyReplacement = "disabled" -}}
|
||||
{{- $defaultDNSProxyEnableTransparentMode = "true" -}}
|
||||
{{- end -}}
|
||||
|
||||
{{- /* Default values when 1.14 was initially deployed */ -}}
|
||||
@@ -432,16 +430,10 @@ data:
|
||||
# - vxlan (default)
|
||||
# - geneve
|
||||
{{- if .Values.gke.enabled }}
|
||||
{{- if ne (.Values.routingMode | default "native") "native" }}
|
||||
{{- fail (printf "RoutingMode must be set to native when gke.enabled=true" )}}
|
||||
{{- end }}
|
||||
routing-mode: "native"
|
||||
enable-endpoint-routes: "true"
|
||||
enable-local-node-route: "false"
|
||||
{{- else if .Values.aksbyocni.enabled }}
|
||||
{{- if ne (.Values.routingMode | default "tunnel") "tunnel" }}
|
||||
{{- fail (printf "RoutingMode must be set to tunnel when aksbyocni.enabled=true" )}}
|
||||
{{- end }}
|
||||
routing-mode: "tunnel"
|
||||
tunnel-protocol: "vxlan"
|
||||
{{- else if .Values.routingMode }}
|
||||
@@ -1100,13 +1092,6 @@ data:
|
||||
{{- end }}
|
||||
|
||||
{{- if .Values.dnsProxy }}
|
||||
{{- if hasKey .Values.dnsProxy "enableTransparentMode" }}
|
||||
# explicit setting gets precedence
|
||||
dnsproxy-enable-transparent-mode: {{ .Values.dnsProxy.enableTransparentMode | quote }}
|
||||
{{- else if eq $cniChainingMode "none" }}
|
||||
# default DNS proxy to transparent mode in non-chaining modes
|
||||
dnsproxy-enable-transparent-mode: {{ $defaultDNSProxyEnableTransparentMode | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.dnsProxy.dnsRejectResponseCode }}
|
||||
tofqdns-dns-reject-response-code: {{ .Values.dnsProxy.dnsRejectResponseCode | quote }}
|
||||
{{- end }}
|
||||
|
||||
@@ -82,7 +82,7 @@ spec:
|
||||
{{- if semverCompare ">=1.20-0" .Capabilities.KubeVersion.Version }}
|
||||
startupProbe:
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
host: "localhost"
|
||||
path: /healthz
|
||||
port: {{ .Values.envoy.healthPort }}
|
||||
scheme: HTTP
|
||||
@@ -92,7 +92,7 @@ spec:
|
||||
{{- end }}
|
||||
livenessProbe:
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
host: "localhost"
|
||||
path: /healthz
|
||||
port: {{ .Values.envoy.healthPort }}
|
||||
scheme: HTTP
|
||||
@@ -110,7 +110,7 @@ spec:
|
||||
timeoutSeconds: 5
|
||||
readinessProbe:
|
||||
httpGet:
|
||||
host: {{ .Values.ipv4.enabled | ternary "127.0.0.1" "::1" | quote }}
|
||||
host: "localhost"
|
||||
path: /healthz
|
||||
port: {{ .Values.envoy.healthPort }}
|
||||
scheme: HTTP
|
||||
|
||||
@@ -7,7 +7,6 @@ metadata:
|
||||
namespace: {{ .Values.envoy.prometheus.serviceMonitor.namespace | default .Release.Namespace }}
|
||||
labels:
|
||||
app.kubernetes.io/part-of: cilium
|
||||
app.kubernetes.io/name: cilium-envoy
|
||||
{{- with .Values.envoy.prometheus.serviceMonitor.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
@@ -23,7 +22,7 @@ spec:
|
||||
matchNames:
|
||||
- {{ .Release.Namespace }}
|
||||
endpoints:
|
||||
- port: envoy-metrics
|
||||
- port: metrics
|
||||
interval: {{ .Values.envoy.prometheus.serviceMonitor.interval | quote }}
|
||||
honorLabels: true
|
||||
path: /metrics
|
||||
|
||||
@@ -66,13 +66,8 @@ spec:
|
||||
- /tmp/ready
|
||||
initialDelaySeconds: 5
|
||||
periodSeconds: 5
|
||||
env:
|
||||
- name: K8S_NODE_NAME
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
apiVersion: v1
|
||||
fieldPath: spec.nodeName
|
||||
{{- with .Values.preflight.extraEnv }}
|
||||
env:
|
||||
{{- toYaml . | trim | nindent 12 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
|
||||
@@ -88,12 +88,10 @@ spec:
|
||||
nodeSelector:
|
||||
{{- toYaml . | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- with .Values.authentication.mutual.spire.install.agent.tolerations }}
|
||||
tolerations:
|
||||
{{- with .Values.authentication.mutual.spire.install.agent.tolerations }}
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
- key: {{ .Values.agentNotReadyTaintKey | default "node.cilium.io/agent-not-ready" }}
|
||||
effect: NoSchedule
|
||||
{{- toYaml . | trim | nindent 8 }}
|
||||
{{- end }}
|
||||
volumes:
|
||||
- name: spire-config
|
||||
configMap:
|
||||
|
||||
@@ -143,10 +143,10 @@ rollOutCiliumPods: false
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/cilium"
|
||||
tag: "v1.14.9"
|
||||
tag: "v1.14.5"
|
||||
pullPolicy: "IfNotPresent"
|
||||
# cilium-digest
|
||||
digest: "sha256:4ef1eb7a3bc39d0fefe14685e6c0d4e01301c40df2a89bc93ffca9a1ab927301"
|
||||
digest: "sha256:d3b287029755b6a47dee01420e2ea469469f1b174a2089c10af7e5e9289ef05b"
|
||||
useDigest: true
|
||||
|
||||
# -- Affinity for cilium-agent.
|
||||
@@ -1109,9 +1109,9 @@ hubble:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/hubble-relay"
|
||||
tag: "v1.14.9"
|
||||
tag: "v1.14.5"
|
||||
# hubble-relay-digest
|
||||
digest: "sha256:f506f3c6e0a979437cde79eb781654fda4f10ddb5642cebc4dc81254cfb7eeaa"
|
||||
digest: "sha256:dbef89f924a927043d02b40c18e417c1ea0e8f58b44523b80fef7e3652db24d4"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
|
||||
@@ -1337,8 +1337,8 @@ hubble:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/hubble-ui-backend"
|
||||
tag: "v0.13.0"
|
||||
digest: "sha256:1e7657d997c5a48253bb8dc91ecee75b63018d16ff5e5797e5af367336bc8803"
|
||||
tag: "v0.12.1"
|
||||
digest: "sha256:1f86f3400827a0451e6332262467f894eeb7caf0eb8779bd951e2caa9d027cbe"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
|
||||
@@ -1368,8 +1368,8 @@ hubble:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/hubble-ui"
|
||||
tag: "v0.13.0"
|
||||
digest: "sha256:7d663dc16538dd6e29061abd1047013a645e6e69c115e008bee9ea9fef9a6666"
|
||||
tag: "v0.12.1"
|
||||
digest: "sha256:9e5f81ee747866480ea1ac4630eb6975ff9227f9782b7c93919c081c33f38267"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
|
||||
@@ -1853,9 +1853,9 @@ envoy:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/cilium-envoy"
|
||||
tag: "v1.26.7-bbde4095997ea57ead209f56158790d47224a0f5"
|
||||
tag: "v1.26.6-ad82c7c56e88989992fd25d8d67747de865c823b"
|
||||
pullPolicy: "IfNotPresent"
|
||||
digest: "sha256:39b75548447978230dedcf25da8940e4d3540c741045ef391a8e74dbb9661a86"
|
||||
digest: "sha256:992998398dadfff7117bfa9fdb7c9474fefab7f0237263f7c8114e106c67baca"
|
||||
useDigest: true
|
||||
|
||||
# -- Additional containers added to the cilium Envoy DaemonSet.
|
||||
@@ -1968,20 +1968,7 @@ envoy:
|
||||
labelSelector:
|
||||
matchLabels:
|
||||
k8s-app: cilium-envoy
|
||||
podAffinity:
|
||||
requiredDuringSchedulingIgnoredDuringExecution:
|
||||
- topologyKey: kubernetes.io/hostname
|
||||
labelSelector:
|
||||
matchLabels:
|
||||
k8s-app: cilium
|
||||
nodeAffinity:
|
||||
requiredDuringSchedulingIgnoredDuringExecution:
|
||||
nodeSelectorTerms:
|
||||
- matchExpressions:
|
||||
- key: cilium.io/no-schedule
|
||||
operator: NotIn
|
||||
values:
|
||||
- "true"
|
||||
|
||||
# -- Node selector for cilium-envoy.
|
||||
nodeSelector:
|
||||
kubernetes.io/os: linux
|
||||
@@ -2002,16 +1989,12 @@ envoy:
|
||||
# Ref: https://kubernetes.io/docs/concepts/services-networking/dns-pod-service/#pod-s-dns-policy
|
||||
dnsPolicy: ~
|
||||
|
||||
# -- Configure Cilium Envoy Prometheus options.
|
||||
# Note that some of these apply to either cilium-agent or cilium-envoy.
|
||||
prometheus:
|
||||
# -- Enable prometheus metrics for cilium-envoy
|
||||
enabled: true
|
||||
serviceMonitor:
|
||||
# -- Enable service monitors.
|
||||
# This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/main/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml)
|
||||
# Note that this setting applies to both cilium-envoy _and_ cilium-agent
|
||||
# with Envoy enabled.
|
||||
enabled: false
|
||||
# -- Labels to add to ServiceMonitor cilium-envoy
|
||||
labels: {}
|
||||
@@ -2023,14 +2006,12 @@ envoy:
|
||||
# service monitors configured.
|
||||
# namespace: ""
|
||||
# -- Relabeling configs for the ServiceMonitor cilium-envoy
|
||||
# or for cilium-agent with Envoy configured.
|
||||
relabelings:
|
||||
- sourceLabels:
|
||||
- __meta_kubernetes_pod_node_name
|
||||
targetLabel: node
|
||||
replacement: ${1}
|
||||
# -- Metrics relabeling configs for the ServiceMonitor cilium-envoy
|
||||
# or for cilium-agent with Envoy configured.
|
||||
metricRelabelings: ~
|
||||
# -- Serve prometheus metrics for cilium-envoy on the configured port
|
||||
port: "9964"
|
||||
@@ -2269,15 +2250,15 @@ operator:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/operator"
|
||||
tag: "v1.14.9"
|
||||
tag: "v1.14.5"
|
||||
# operator-generic-digest
|
||||
genericDigest: "sha256:1552d653870dd8ebbd16ee985a5497dd78a2097370978b0cfbd2da2072f30712"
|
||||
genericDigest: "sha256:303f9076bdc73b3fc32aaedee64a14f6f44c8bb08ee9e3956d443021103ebe7a"
|
||||
# operator-azure-digest
|
||||
azureDigest: "sha256:2d3b9d868eb03fa9256d34192a734a2abab283f527a9c97b7cefcd3401649d17"
|
||||
azureDigest: "sha256:9203f5583aa34e716d7a6588ebd144e43ce3b77873f578fc12b2679e33591353"
|
||||
# operator-aws-digest
|
||||
awsDigest: "sha256:041ad5b49ae63ba0f1974e1a1d9ebf9f52541cd2813088fa687f9d544125a1ec"
|
||||
awsDigest: "sha256:785ccf1267d0ed3ba9e4bd8166577cb4f9e4ce996af26b27c9d5c554a0d5b09a"
|
||||
# operator-alibabacloud-digest
|
||||
alibabacloudDigest: "sha256:765314779093b54750f83280f009229f20fe1f28466a633d9bb4143d2ad669c5"
|
||||
alibabacloudDigest: "sha256:e0152c498ba73c56a82eee2a706c8f400e9a6999c665af31a935bdf08e659bc3"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
suffix: ""
|
||||
@@ -2554,9 +2535,9 @@ preflight:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/cilium"
|
||||
tag: "v1.14.9"
|
||||
tag: "v1.14.5"
|
||||
# cilium-digest
|
||||
digest: "sha256:4ef1eb7a3bc39d0fefe14685e6c0d4e01301c40df2a89bc93ffca9a1ab927301"
|
||||
digest: "sha256:d3b287029755b6a47dee01420e2ea469469f1b174a2089c10af7e5e9289ef05b"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
|
||||
@@ -2704,9 +2685,9 @@ clustermesh:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/clustermesh-apiserver"
|
||||
tag: "v1.14.9"
|
||||
tag: "v1.14.5"
|
||||
# clustermesh-apiserver-digest
|
||||
digest: "sha256:5c16f8b8e22ce41e11998e70846fbcecea3a6b683a38253809ead8d871f6d8a3"
|
||||
digest: "sha256:7eaa35cf5452c43b1f7d0cde0d707823ae7e49965bcb54c053e31ea4e04c3d96"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
|
||||
@@ -2751,9 +2732,9 @@ clustermesh:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/kvstoremesh"
|
||||
tag: "v1.14.9"
|
||||
tag: "v1.14.5"
|
||||
# kvstoremesh-digest
|
||||
digest: "sha256:9d9efb25806660f3663b9cd803fb8679f2b115763470002a9770e2c1eb1e5b22"
|
||||
digest: "sha256:d7137edd0efa2b1407b20088af3980a9993bb616d85bf9b55ea2891d1b99023a"
|
||||
useDigest: true
|
||||
pullPolicy: "IfNotPresent"
|
||||
|
||||
@@ -3105,8 +3086,6 @@ dnsProxy:
|
||||
proxyPort: 0
|
||||
# -- The maximum time the DNS proxy holds an allowed DNS response before sending it along. Responses are sent as soon as the datapath is updated with the new IP information.
|
||||
proxyResponseMaxDelay: 100ms
|
||||
# -- DNS proxy operation mode (true/false, or unset to use version dependent defaults)
|
||||
# enableTransparentMode: true
|
||||
|
||||
# -- SCTP Configuration Values
|
||||
sctp:
|
||||
@@ -3157,21 +3136,8 @@ authentication:
|
||||
# -- SPIRE Workload Attestor kubelet verification.
|
||||
skipKubeletVerification: true
|
||||
# -- SPIRE agent tolerations configuration
|
||||
# By default it follows the same tolerations as the agent itself
|
||||
# to allow the Cilium agent on this node to connect to SPIRE.
|
||||
# ref: https://kubernetes.io/docs/concepts/scheduling-eviction/taint-and-toleration/
|
||||
tolerations:
|
||||
- key: node.kubernetes.io/not-ready
|
||||
effect: NoSchedule
|
||||
- key: node-role.kubernetes.io/master
|
||||
effect: NoSchedule
|
||||
- key: node-role.kubernetes.io/control-plane
|
||||
effect: NoSchedule
|
||||
- key: node.cloudprovider.kubernetes.io/uninitialized
|
||||
effect: NoSchedule
|
||||
value: "true"
|
||||
- key: CriticalAddonsOnly
|
||||
operator: "Exists"
|
||||
tolerations: []
|
||||
# -- SPIRE agent affinity configuration
|
||||
affinity: {}
|
||||
# -- SPIRE agent nodeSelector configuration
|
||||
|
||||
@@ -1854,9 +1854,9 @@ envoy:
|
||||
image:
|
||||
override: ~
|
||||
repository: "quay.io/cilium/cilium-envoy"
|
||||
tag: "v1.26.7-bbde4095997ea57ead209f56158790d47224a0f5"
|
||||
tag: "v1.26.6-ad82c7c56e88989992fd25d8d67747de865c823b"
|
||||
pullPolicy: "${PULL_POLICY}"
|
||||
digest: "sha256:39b75548447978230dedcf25da8940e4d3540c741045ef391a8e74dbb9661a86"
|
||||
digest: "sha256:992998398dadfff7117bfa9fdb7c9474fefab7f0237263f7c8114e106c67baca"
|
||||
useDigest: true
|
||||
|
||||
# -- Additional containers added to the cilium Envoy DaemonSet.
|
||||
@@ -1969,20 +1969,7 @@ envoy:
|
||||
labelSelector:
|
||||
matchLabels:
|
||||
k8s-app: cilium-envoy
|
||||
podAffinity:
|
||||
requiredDuringSchedulingIgnoredDuringExecution:
|
||||
- topologyKey: kubernetes.io/hostname
|
||||
labelSelector:
|
||||
matchLabels:
|
||||
k8s-app: cilium
|
||||
nodeAffinity:
|
||||
requiredDuringSchedulingIgnoredDuringExecution:
|
||||
nodeSelectorTerms:
|
||||
- matchExpressions:
|
||||
- key: cilium.io/no-schedule
|
||||
operator: NotIn
|
||||
values:
|
||||
- "true"
|
||||
|
||||
# -- Node selector for cilium-envoy.
|
||||
nodeSelector:
|
||||
kubernetes.io/os: linux
|
||||
@@ -2003,16 +1990,12 @@ envoy:
|
||||
# Ref: https://kubernetes.io/docs/concepts/services-networking/dns-pod-service/#pod-s-dns-policy
|
||||
dnsPolicy: ~
|
||||
|
||||
# -- Configure Cilium Envoy Prometheus options.
|
||||
# Note that some of these apply to either cilium-agent or cilium-envoy.
|
||||
prometheus:
|
||||
# -- Enable prometheus metrics for cilium-envoy
|
||||
enabled: true
|
||||
serviceMonitor:
|
||||
# -- Enable service monitors.
|
||||
# This requires the prometheus CRDs to be available (see https://github.com/prometheus-operator/prometheus-operator/blob/main/example/prometheus-operator-crd/monitoring.coreos.com_servicemonitors.yaml)
|
||||
# Note that this setting applies to both cilium-envoy _and_ cilium-agent
|
||||
# with Envoy enabled.
|
||||
enabled: false
|
||||
# -- Labels to add to ServiceMonitor cilium-envoy
|
||||
labels: {}
|
||||
@@ -2024,14 +2007,12 @@ envoy:
|
||||
# service monitors configured.
|
||||
# namespace: ""
|
||||
# -- Relabeling configs for the ServiceMonitor cilium-envoy
|
||||
# or for cilium-agent with Envoy configured.
|
||||
relabelings:
|
||||
- sourceLabels:
|
||||
- __meta_kubernetes_pod_node_name
|
||||
targetLabel: node
|
||||
replacement: ${1}
|
||||
# -- Metrics relabeling configs for the ServiceMonitor cilium-envoy
|
||||
# or for cilium-agent with Envoy configured.
|
||||
metricRelabelings: ~
|
||||
# -- Serve prometheus metrics for cilium-envoy on the configured port
|
||||
port: "9964"
|
||||
@@ -3108,8 +3089,6 @@ dnsProxy:
|
||||
proxyPort: 0
|
||||
# -- The maximum time the DNS proxy holds an allowed DNS response before sending it along. Responses are sent as soon as the datapath is updated with the new IP information.
|
||||
proxyResponseMaxDelay: 100ms
|
||||
# -- DNS proxy operation mode (true/false, or unset to use version dependent defaults)
|
||||
# enableTransparentMode: true
|
||||
|
||||
# -- SCTP Configuration Values
|
||||
sctp:
|
||||
@@ -3160,21 +3139,8 @@ authentication:
|
||||
# -- SPIRE Workload Attestor kubelet verification.
|
||||
skipKubeletVerification: true
|
||||
# -- SPIRE agent tolerations configuration
|
||||
# By default it follows the same tolerations as the agent itself
|
||||
# to allow the Cilium agent on this node to connect to SPIRE.
|
||||
# ref: https://kubernetes.io/docs/concepts/scheduling-eviction/taint-and-toleration/
|
||||
tolerations:
|
||||
- key: node.kubernetes.io/not-ready
|
||||
effect: NoSchedule
|
||||
- key: node-role.kubernetes.io/master
|
||||
effect: NoSchedule
|
||||
- key: node-role.kubernetes.io/control-plane
|
||||
effect: NoSchedule
|
||||
- key: node.cloudprovider.kubernetes.io/uninitialized
|
||||
effect: NoSchedule
|
||||
value: "true"
|
||||
- key: CriticalAddonsOnly
|
||||
operator: "Exists"
|
||||
tolerations: []
|
||||
# -- SPIRE agent affinity configuration
|
||||
affinity: {}
|
||||
# -- SPIRE agent nodeSelector configuration
|
||||
|
||||
@@ -3,10 +3,11 @@ cilium:
|
||||
enabled: false
|
||||
externalIPs:
|
||||
enabled: true
|
||||
tunnel: disabled
|
||||
autoDirectNodeRoutes: false
|
||||
kubeProxyReplacement: strict
|
||||
bpf:
|
||||
masquerade: false
|
||||
masquerade: true
|
||||
loadBalancer:
|
||||
algorithm: maglev
|
||||
cgroup:
|
||||
@@ -24,4 +25,3 @@ cilium:
|
||||
configMap: cni-configuration
|
||||
routingMode: native
|
||||
enableIPv4Masquerade: false
|
||||
enableIdentityMark: false
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
name: cozy-dashboard
|
||||
version: 0.2.0
|
||||
version: 1.0.0
|
||||
|
||||
@@ -3,7 +3,7 @@ NAMESPACE=cozy-dashboard
|
||||
PUSH := 1
|
||||
LOAD := 0
|
||||
REPOSITORY := ghcr.io/aenix-io/cozystack
|
||||
TAG := v0.2.0
|
||||
TAG := v0.0.2
|
||||
|
||||
show:
|
||||
helm template --dry-run=server -n $(NAMESPACE) $(NAME) .
|
||||
|
||||
@@ -22,5 +22,3 @@
|
||||
.project
|
||||
.idea/
|
||||
*.tmproj
|
||||
# img folder
|
||||
img/
|
||||
|
||||
@@ -1,12 +1,12 @@
|
||||
dependencies:
|
||||
- name: redis
|
||||
repository: oci://registry-1.docker.io/bitnamicharts
|
||||
version: 18.19.2
|
||||
version: 18.4.0
|
||||
- name: postgresql
|
||||
repository: oci://registry-1.docker.io/bitnamicharts
|
||||
version: 13.4.6
|
||||
version: 13.2.14
|
||||
- name: common
|
||||
repository: oci://registry-1.docker.io/bitnamicharts
|
||||
version: 2.19.0
|
||||
digest: sha256:b4965a22517e61212e78abb8d1cbe86e800c8664b3139e2047f4bd62b3e55b24
|
||||
generated: "2024-03-13T11:51:34.216594+01:00"
|
||||
version: 2.13.3
|
||||
digest: sha256:7bede05a463745ea72d332aaaf406d84e335d8af09dce403736f4e4e14c3554d
|
||||
generated: "2023-11-21T18:18:20.024990735Z"
|
||||
|
||||
@@ -2,21 +2,21 @@ annotations:
|
||||
category: Infrastructure
|
||||
images: |
|
||||
- name: kubeapps-apis
|
||||
image: docker.io/bitnami/kubeapps-apis:2.9.0-debian-12-r19
|
||||
image: docker.io/bitnami/kubeapps-apis:2.9.0-debian-11-r13
|
||||
- name: kubeapps-apprepository-controller
|
||||
image: docker.io/bitnami/kubeapps-apprepository-controller:2.9.0-debian-12-r18
|
||||
image: docker.io/bitnami/kubeapps-apprepository-controller:2.9.0-debian-11-r12
|
||||
- name: kubeapps-asset-syncer
|
||||
image: docker.io/bitnami/kubeapps-asset-syncer:2.9.0-debian-12-r19
|
||||
- name: kubeapps-dashboard
|
||||
image: docker.io/bitnami/kubeapps-dashboard:2.9.0-debian-12-r18
|
||||
image: docker.io/bitnami/kubeapps-asset-syncer:2.9.0-debian-11-r13
|
||||
- name: kubeapps-oci-catalog
|
||||
image: docker.io/bitnami/kubeapps-oci-catalog:2.9.0-debian-12-r17
|
||||
image: docker.io/bitnami/kubeapps-oci-catalog:2.9.0-debian-11-r6
|
||||
- name: kubeapps-pinniped-proxy
|
||||
image: docker.io/bitnami/kubeapps-pinniped-proxy:2.9.0-debian-12-r17
|
||||
image: docker.io/bitnami/kubeapps-pinniped-proxy:2.9.0-debian-11-r10
|
||||
- name: kubeapps-dashboard
|
||||
image: docker.io/bitnami/kubeapps-dashboard:2.9.0-debian-11-r16
|
||||
- name: nginx
|
||||
image: docker.io/bitnami/nginx:1.25.4-debian-12-r3
|
||||
image: docker.io/bitnami/nginx:1.25.3-debian-11-r1
|
||||
- name: oauth2-proxy
|
||||
image: docker.io/bitnami/oauth2-proxy:7.6.0-debian-12-r4
|
||||
image: docker.io/bitnami/oauth2-proxy:7.5.1-debian-11-r11
|
||||
licenses: Apache-2.0
|
||||
apiVersion: v2
|
||||
appVersion: 2.9.0
|
||||
@@ -51,4 +51,4 @@ maintainers:
|
||||
name: kubeapps
|
||||
sources:
|
||||
- https://github.com/bitnami/charts/tree/main/bitnami/kubeapps
|
||||
version: 14.7.2
|
||||
version: 14.1.2
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@@ -20,5 +20,3 @@
|
||||
.idea/
|
||||
*.tmproj
|
||||
.vscode/
|
||||
# img folder
|
||||
img/
|
||||
|
||||
@@ -2,7 +2,7 @@ annotations:
|
||||
category: Infrastructure
|
||||
licenses: Apache-2.0
|
||||
apiVersion: v2
|
||||
appVersion: 2.19.0
|
||||
appVersion: 2.13.3
|
||||
description: A Library Helm Chart for grouping common logic between bitnami charts.
|
||||
This chart is not deployable by itself.
|
||||
home: https://bitnami.com
|
||||
@@ -20,4 +20,4 @@ name: common
|
||||
sources:
|
||||
- https://github.com/bitnami/charts
|
||||
type: library
|
||||
version: 2.19.0
|
||||
version: 2.13.3
|
||||
|
||||
@@ -24,14 +24,14 @@ data:
|
||||
myvalue: "Hello World"
|
||||
```
|
||||
|
||||
Looking to use our applications in production? Try [VMware Tanzu Application Catalog](https://bitnami.com/enterprise), the enterprise edition of Bitnami Application Catalog.
|
||||
|
||||
## Introduction
|
||||
|
||||
This chart provides a common template helpers which can be used to develop new charts using [Helm](https://helm.sh) package manager.
|
||||
|
||||
Bitnami charts can be used with [Kubeapps](https://kubeapps.dev/) for deployment and management of Helm Charts in clusters.
|
||||
|
||||
Looking to use our applications in production? Try [VMware Application Catalog](https://bitnami.com/enterprise), the enterprise edition of Bitnami Application Catalog.
|
||||
|
||||
## Prerequisites
|
||||
|
||||
- Kubernetes 1.23+
|
||||
@@ -220,7 +220,7 @@ helm install test mychart --set path.to.value00="",path.to.value01=""
|
||||
|
||||
## License
|
||||
|
||||
Copyright © 2024 Broadcom. The term "Broadcom" refers to Broadcom Inc. and/or its subsidiaries.
|
||||
Copyright © 2023 VMware, Inc.
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
|
||||
@@ -1,39 +0,0 @@
|
||||
{{/*
|
||||
Copyright VMware, Inc.
|
||||
SPDX-License-Identifier: APACHE-2.0
|
||||
*/}}
|
||||
|
||||
{{/* vim: set filetype=mustache: */}}
|
||||
|
||||
{{/*
|
||||
Return true if the detected platform is Openshift
|
||||
Usage:
|
||||
{{- include "common.compatibility.isOpenshift" . -}}
|
||||
*/}}
|
||||
{{- define "common.compatibility.isOpenshift" -}}
|
||||
{{- if .Capabilities.APIVersions.Has "security.openshift.io/v1" -}}
|
||||
{{- true -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Render a compatible securityContext depending on the platform. By default it is maintained as it is. In other platforms like Openshift we remove default user/group values that do not work out of the box with the restricted-v1 SCC
|
||||
Usage:
|
||||
{{- include "common.compatibility.renderSecurityContext" (dict "secContext" .Values.containerSecurityContext "context" $) -}}
|
||||
*/}}
|
||||
{{- define "common.compatibility.renderSecurityContext" -}}
|
||||
{{- $adaptedContext := .secContext -}}
|
||||
{{- if .context.Values.global.compatibility -}}
|
||||
{{- if .context.Values.global.compatibility.openshift -}}
|
||||
{{- if or (eq .context.Values.global.compatibility.openshift.adaptSecurityContext "force") (and (eq .context.Values.global.compatibility.openshift.adaptSecurityContext "auto") (include "common.compatibility.isOpenshift" .context)) -}}
|
||||
{{/* Remove incompatible user/group values that do not work in Openshift out of the box */}}
|
||||
{{- $adaptedContext = omit $adaptedContext "fsGroup" "runAsUser" "runAsGroup" -}}
|
||||
{{- if not .secContext.seLinuxOptions -}}
|
||||
{{/* If it is an empty object, we remove it from the resulting context because it causes validation issues */}}
|
||||
{{- $adaptedContext = omit $adaptedContext "seLinuxOptions" -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- omit $adaptedContext "enabled" | toYaml -}}
|
||||
{{- end -}}
|
||||
@@ -1,50 +0,0 @@
|
||||
{{/*
|
||||
Copyright VMware, Inc.
|
||||
SPDX-License-Identifier: APACHE-2.0
|
||||
*/}}
|
||||
|
||||
{{/* vim: set filetype=mustache: */}}
|
||||
|
||||
{{/*
|
||||
Return a resource request/limit object based on a given preset.
|
||||
These presets are for basic testing and not meant to be used in production
|
||||
{{ include "common.resources.preset" (dict "type" "nano") -}}
|
||||
*/}}
|
||||
{{- define "common.resources.preset" -}}
|
||||
{{/* The limits are the requests increased by 50% (except ephemeral-storage)*/}}
|
||||
{{- $presets := dict
|
||||
"nano" (dict
|
||||
"requests" (dict "cpu" "100m" "memory" "128Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "150m" "memory" "192Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"micro" (dict
|
||||
"requests" (dict "cpu" "250m" "memory" "256Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "375m" "memory" "384Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"small" (dict
|
||||
"requests" (dict "cpu" "500m" "memory" "512Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "750m" "memory" "768Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"medium" (dict
|
||||
"requests" (dict "cpu" "500m" "memory" "1024Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "750m" "memory" "1536Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"large" (dict
|
||||
"requests" (dict "cpu" "1.0" "memory" "2048Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "1.5" "memory" "3072Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"xlarge" (dict
|
||||
"requests" (dict "cpu" "2.0" "memory" "4096Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "3.0" "memory" "6144Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"2xlarge" (dict
|
||||
"requests" (dict "cpu" "4.0" "memory" "8192Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "6.0" "memory" "12288Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
}}
|
||||
{{- if hasKey $presets .type -}}
|
||||
{{- index $presets .type | toYaml -}}
|
||||
{{- else -}}
|
||||
{{- printf "ERROR: Preset key '%s' invalid. Allowed values are %s" .type (join "," (keys $presets)) | fail -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
@@ -78,8 +78,6 @@ Params:
|
||||
- chartName - String - Optional - Name of the chart used when said chart is deployed as a subchart.
|
||||
- context - Context - Required - Parent context.
|
||||
- failOnNew - Boolean - Optional - Default to true. If set to false, skip errors adding new keys to existing secrets.
|
||||
- skipB64enc - Boolean - Optional - Default to false. If set to true, no the secret will not be base64 encrypted.
|
||||
- skipQuote - Boolean - Optional - Default to false. If set to true, no quotes will be added around the secret.
|
||||
The order in which this function returns a secret password:
|
||||
1. Already existing 'Secret' resource
|
||||
(If a 'Secret' resource is found under the name provided to the 'secret' parameter to this function and that 'Secret' resource contains a key with the name passed as the 'key' parameter to this function then the value of this existing secret password will be returned)
|
||||
@@ -93,6 +91,7 @@ The order in which this function returns a secret password:
|
||||
|
||||
{{- $password := "" }}
|
||||
{{- $subchart := "" }}
|
||||
{{- $failOnNew := default true .failOnNew }}
|
||||
{{- $chartName := default "" .chartName }}
|
||||
{{- $passwordLength := default 10 .length }}
|
||||
{{- $providedPasswordKey := include "common.utils.getKeyFromList" (dict "keys" .providedValues "context" $.context) }}
|
||||
@@ -100,14 +99,12 @@ The order in which this function returns a secret password:
|
||||
{{- $secretData := (lookup "v1" "Secret" (include "common.names.namespace" .context) .secret).data }}
|
||||
{{- if $secretData }}
|
||||
{{- if hasKey $secretData .key }}
|
||||
{{- $password = index $secretData .key | b64dec }}
|
||||
{{- else if not (eq .failOnNew false) }}
|
||||
{{- $password = index $secretData .key | quote }}
|
||||
{{- else if $failOnNew }}
|
||||
{{- printf "\nPASSWORDS ERROR: The secret \"%s\" does not contain the key \"%s\"\n" .secret .key | fail -}}
|
||||
{{- else if $providedPasswordValue }}
|
||||
{{- $password = $providedPasswordValue | toString }}
|
||||
{{- end -}}
|
||||
{{- else if $providedPasswordValue }}
|
||||
{{- $password = $providedPasswordValue | toString }}
|
||||
{{- $password = $providedPasswordValue | toString | b64enc | quote }}
|
||||
{{- else }}
|
||||
|
||||
{{- if .context.Values.enabled }}
|
||||
@@ -123,19 +120,12 @@ The order in which this function returns a secret password:
|
||||
{{- $subStr := list (lower (randAlpha 1)) (randNumeric 1) (upper (randAlpha 1)) | join "_" }}
|
||||
{{- $password = randAscii $passwordLength }}
|
||||
{{- $password = regexReplaceAllLiteral "\\W" $password "@" | substr 5 $passwordLength }}
|
||||
{{- $password = printf "%s%s" $subStr $password | toString | shuffle }}
|
||||
{{- $password = printf "%s%s" $subStr $password | toString | shuffle | b64enc | quote }}
|
||||
{{- else }}
|
||||
{{- $password = randAlphaNum $passwordLength }}
|
||||
{{- $password = randAlphaNum $passwordLength | b64enc | quote }}
|
||||
{{- end }}
|
||||
{{- end -}}
|
||||
{{- if not .skipB64enc }}
|
||||
{{- $password = $password | b64enc }}
|
||||
{{- end -}}
|
||||
{{- if .skipQuote -}}
|
||||
{{- printf "%s" $password -}}
|
||||
{{- else -}}
|
||||
{{- printf "%s" $password | quote -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
|
||||
@@ -13,70 +13,7 @@ Usage:
|
||||
|
||||
{{- if and (contains "bitnami/" .repository) (not (.tag | toString | regexFind "-r\\d+$|sha256:")) }}
|
||||
WARNING: Rolling tag detected ({{ .repository }}:{{ .tag }}), please note that it is strongly recommended to avoid using rolling tags in a production environment.
|
||||
+info https://docs.bitnami.com/tutorials/understand-rolling-tags-containers
|
||||
+info https://docs.bitnami.com/containers/how-to/understand-rolling-tags-containers/
|
||||
{{- end }}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Warning about not setting the resource object in all deployments.
|
||||
Usage:
|
||||
{{ include "common.warnings.resources" (dict "sections" (list "path1" "path2") context $) }}
|
||||
Example:
|
||||
{{- include "common.warnings.resources" (dict "sections" (list "csiProvider.provider" "server" "volumePermissions" "") "context" $) }}
|
||||
The list in the example assumes that the following values exist:
|
||||
- csiProvider.provider.resources
|
||||
- server.resources
|
||||
- volumePermissions.resources
|
||||
- resources
|
||||
*/}}
|
||||
{{- define "common.warnings.resources" -}}
|
||||
{{- $values := .context.Values -}}
|
||||
{{- $printMessage := false -}}
|
||||
{{ $affectedSections := list -}}
|
||||
{{- range .sections -}}
|
||||
{{- if eq . "" -}}
|
||||
{{/* Case where the resources section is at the root (one main deployment in the chart) */}}
|
||||
{{- if not (index $values "resources") -}}
|
||||
{{- $affectedSections = append $affectedSections "resources" -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- else -}}
|
||||
{{/* Case where the are multiple resources sections (more than one main deployment in the chart) */}}
|
||||
{{- $keys := split "." . -}}
|
||||
{{/* We iterate through the different levels until arriving to the resource section. Example: a.b.c.resources */}}
|
||||
{{- $section := $values -}}
|
||||
{{- range $keys -}}
|
||||
{{- $section = index $section . -}}
|
||||
{{- end -}}
|
||||
{{- if not (index $section "resources") -}}
|
||||
{{/* If the section has enabled=false or replicaCount=0, do not include it */}}
|
||||
{{- if and (hasKey $section "enabled") -}}
|
||||
{{- if index $section "enabled" -}}
|
||||
{{/* enabled=true */}}
|
||||
{{- $affectedSections = append $affectedSections (printf "%s.resources" .) -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- else if and (hasKey $section "replicaCount") -}}
|
||||
{{/* We need a casting to int because number 0 is not treated as an int by default */}}
|
||||
{{- if (gt (index $section "replicaCount" | int) 0) -}}
|
||||
{{/* replicaCount > 0 */}}
|
||||
{{- $affectedSections = append $affectedSections (printf "%s.resources" .) -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- else -}}
|
||||
{{/* Default case, add it to the affected sections */}}
|
||||
{{- $affectedSections = append $affectedSections (printf "%s.resources" .) -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- if $printMessage }}
|
||||
|
||||
WARNING: There are "resources" sections in the chart not set. Using "resourcesPreset" is not recommended for production. For production installations, please set the following values according to your workload needs:
|
||||
{{- range $affectedSections }}
|
||||
- {{ . }}
|
||||
{{- end }}
|
||||
+info https://kubernetes.io/docs/concepts/configuration/manage-resources-containers/
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
@@ -19,5 +19,3 @@
|
||||
.project
|
||||
.idea/
|
||||
*.tmproj
|
||||
# img folder
|
||||
img/
|
||||
|
||||
@@ -1,6 +1,6 @@
|
||||
dependencies:
|
||||
- name: common
|
||||
repository: oci://registry-1.docker.io/bitnamicharts
|
||||
version: 2.19.0
|
||||
digest: sha256:ac559eb57710d8904e266424ee364cd686d7e24517871f0c5c67f7c4500c2bcc
|
||||
generated: "2024-03-08T15:56:40.04210215Z"
|
||||
version: 2.13.3
|
||||
digest: sha256:9a971689db0c66ea95ac2e911c05014c2b96c6077c991131ff84f2982f88fb83
|
||||
generated: "2023-10-19T12:32:36.790999138Z"
|
||||
|
||||
@@ -1,19 +1,17 @@
|
||||
annotations:
|
||||
category: Database
|
||||
images: |
|
||||
- name: kubectl
|
||||
image: docker.io/bitnami/kubectl:1.29.2-debian-12-r3
|
||||
- name: os-shell
|
||||
image: docker.io/bitnami/os-shell:12-debian-12-r16
|
||||
- name: redis
|
||||
image: docker.io/bitnami/redis:7.2.4-debian-12-r9
|
||||
image: docker.io/bitnami/os-shell:11-debian-11-r91
|
||||
- name: redis-exporter
|
||||
image: docker.io/bitnami/redis-exporter:1.58.0-debian-12-r4
|
||||
image: docker.io/bitnami/redis-exporter:1.55.0-debian-11-r2
|
||||
- name: redis-sentinel
|
||||
image: docker.io/bitnami/redis-sentinel:7.2.4-debian-12-r7
|
||||
image: docker.io/bitnami/redis-sentinel:7.2.3-debian-11-r1
|
||||
- name: redis
|
||||
image: docker.io/bitnami/redis:7.2.3-debian-11-r1
|
||||
licenses: Apache-2.0
|
||||
apiVersion: v2
|
||||
appVersion: 7.2.4
|
||||
appVersion: 7.2.3
|
||||
dependencies:
|
||||
- name: common
|
||||
repository: oci://registry-1.docker.io/bitnamicharts
|
||||
@@ -35,4 +33,4 @@ maintainers:
|
||||
name: redis
|
||||
sources:
|
||||
- https://github.com/bitnami/charts/tree/main/bitnami/redis
|
||||
version: 18.19.2
|
||||
version: 18.4.0
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@@ -20,5 +20,3 @@
|
||||
.idea/
|
||||
*.tmproj
|
||||
.vscode/
|
||||
# img folder
|
||||
img/
|
||||
|
||||
@@ -2,7 +2,7 @@ annotations:
|
||||
category: Infrastructure
|
||||
licenses: Apache-2.0
|
||||
apiVersion: v2
|
||||
appVersion: 2.19.0
|
||||
appVersion: 2.13.3
|
||||
description: A Library Helm Chart for grouping common logic between bitnami charts.
|
||||
This chart is not deployable by itself.
|
||||
home: https://bitnami.com
|
||||
@@ -20,4 +20,4 @@ name: common
|
||||
sources:
|
||||
- https://github.com/bitnami/charts
|
||||
type: library
|
||||
version: 2.19.0
|
||||
version: 2.13.3
|
||||
|
||||
@@ -24,14 +24,14 @@ data:
|
||||
myvalue: "Hello World"
|
||||
```
|
||||
|
||||
Looking to use our applications in production? Try [VMware Tanzu Application Catalog](https://bitnami.com/enterprise), the enterprise edition of Bitnami Application Catalog.
|
||||
|
||||
## Introduction
|
||||
|
||||
This chart provides a common template helpers which can be used to develop new charts using [Helm](https://helm.sh) package manager.
|
||||
|
||||
Bitnami charts can be used with [Kubeapps](https://kubeapps.dev/) for deployment and management of Helm Charts in clusters.
|
||||
|
||||
Looking to use our applications in production? Try [VMware Application Catalog](https://bitnami.com/enterprise), the enterprise edition of Bitnami Application Catalog.
|
||||
|
||||
## Prerequisites
|
||||
|
||||
- Kubernetes 1.23+
|
||||
@@ -220,7 +220,7 @@ helm install test mychart --set path.to.value00="",path.to.value01=""
|
||||
|
||||
## License
|
||||
|
||||
Copyright © 2024 Broadcom. The term "Broadcom" refers to Broadcom Inc. and/or its subsidiaries.
|
||||
Copyright © 2023 VMware, Inc.
|
||||
|
||||
Licensed under the Apache License, Version 2.0 (the "License");
|
||||
you may not use this file except in compliance with the License.
|
||||
|
||||
@@ -1,39 +0,0 @@
|
||||
{{/*
|
||||
Copyright VMware, Inc.
|
||||
SPDX-License-Identifier: APACHE-2.0
|
||||
*/}}
|
||||
|
||||
{{/* vim: set filetype=mustache: */}}
|
||||
|
||||
{{/*
|
||||
Return true if the detected platform is Openshift
|
||||
Usage:
|
||||
{{- include "common.compatibility.isOpenshift" . -}}
|
||||
*/}}
|
||||
{{- define "common.compatibility.isOpenshift" -}}
|
||||
{{- if .Capabilities.APIVersions.Has "security.openshift.io/v1" -}}
|
||||
{{- true -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Render a compatible securityContext depending on the platform. By default it is maintained as it is. In other platforms like Openshift we remove default user/group values that do not work out of the box with the restricted-v1 SCC
|
||||
Usage:
|
||||
{{- include "common.compatibility.renderSecurityContext" (dict "secContext" .Values.containerSecurityContext "context" $) -}}
|
||||
*/}}
|
||||
{{- define "common.compatibility.renderSecurityContext" -}}
|
||||
{{- $adaptedContext := .secContext -}}
|
||||
{{- if .context.Values.global.compatibility -}}
|
||||
{{- if .context.Values.global.compatibility.openshift -}}
|
||||
{{- if or (eq .context.Values.global.compatibility.openshift.adaptSecurityContext "force") (and (eq .context.Values.global.compatibility.openshift.adaptSecurityContext "auto") (include "common.compatibility.isOpenshift" .context)) -}}
|
||||
{{/* Remove incompatible user/group values that do not work in Openshift out of the box */}}
|
||||
{{- $adaptedContext = omit $adaptedContext "fsGroup" "runAsUser" "runAsGroup" -}}
|
||||
{{- if not .secContext.seLinuxOptions -}}
|
||||
{{/* If it is an empty object, we remove it from the resulting context because it causes validation issues */}}
|
||||
{{- $adaptedContext = omit $adaptedContext "seLinuxOptions" -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- omit $adaptedContext "enabled" | toYaml -}}
|
||||
{{- end -}}
|
||||
@@ -1,50 +0,0 @@
|
||||
{{/*
|
||||
Copyright VMware, Inc.
|
||||
SPDX-License-Identifier: APACHE-2.0
|
||||
*/}}
|
||||
|
||||
{{/* vim: set filetype=mustache: */}}
|
||||
|
||||
{{/*
|
||||
Return a resource request/limit object based on a given preset.
|
||||
These presets are for basic testing and not meant to be used in production
|
||||
{{ include "common.resources.preset" (dict "type" "nano") -}}
|
||||
*/}}
|
||||
{{- define "common.resources.preset" -}}
|
||||
{{/* The limits are the requests increased by 50% (except ephemeral-storage)*/}}
|
||||
{{- $presets := dict
|
||||
"nano" (dict
|
||||
"requests" (dict "cpu" "100m" "memory" "128Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "150m" "memory" "192Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"micro" (dict
|
||||
"requests" (dict "cpu" "250m" "memory" "256Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "375m" "memory" "384Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"small" (dict
|
||||
"requests" (dict "cpu" "500m" "memory" "512Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "750m" "memory" "768Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"medium" (dict
|
||||
"requests" (dict "cpu" "500m" "memory" "1024Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "750m" "memory" "1536Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"large" (dict
|
||||
"requests" (dict "cpu" "1.0" "memory" "2048Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "1.5" "memory" "3072Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"xlarge" (dict
|
||||
"requests" (dict "cpu" "2.0" "memory" "4096Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "3.0" "memory" "6144Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
"2xlarge" (dict
|
||||
"requests" (dict "cpu" "4.0" "memory" "8192Mi" "ephemeral-storage" "50Mi")
|
||||
"limits" (dict "cpu" "6.0" "memory" "12288Mi" "ephemeral-storage" "1024Mi")
|
||||
)
|
||||
}}
|
||||
{{- if hasKey $presets .type -}}
|
||||
{{- index $presets .type | toYaml -}}
|
||||
{{- else -}}
|
||||
{{- printf "ERROR: Preset key '%s' invalid. Allowed values are %s" .type (join "," (keys $presets)) | fail -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
@@ -78,8 +78,6 @@ Params:
|
||||
- chartName - String - Optional - Name of the chart used when said chart is deployed as a subchart.
|
||||
- context - Context - Required - Parent context.
|
||||
- failOnNew - Boolean - Optional - Default to true. If set to false, skip errors adding new keys to existing secrets.
|
||||
- skipB64enc - Boolean - Optional - Default to false. If set to true, no the secret will not be base64 encrypted.
|
||||
- skipQuote - Boolean - Optional - Default to false. If set to true, no quotes will be added around the secret.
|
||||
The order in which this function returns a secret password:
|
||||
1. Already existing 'Secret' resource
|
||||
(If a 'Secret' resource is found under the name provided to the 'secret' parameter to this function and that 'Secret' resource contains a key with the name passed as the 'key' parameter to this function then the value of this existing secret password will be returned)
|
||||
@@ -93,6 +91,7 @@ The order in which this function returns a secret password:
|
||||
|
||||
{{- $password := "" }}
|
||||
{{- $subchart := "" }}
|
||||
{{- $failOnNew := default true .failOnNew }}
|
||||
{{- $chartName := default "" .chartName }}
|
||||
{{- $passwordLength := default 10 .length }}
|
||||
{{- $providedPasswordKey := include "common.utils.getKeyFromList" (dict "keys" .providedValues "context" $.context) }}
|
||||
@@ -100,14 +99,12 @@ The order in which this function returns a secret password:
|
||||
{{- $secretData := (lookup "v1" "Secret" (include "common.names.namespace" .context) .secret).data }}
|
||||
{{- if $secretData }}
|
||||
{{- if hasKey $secretData .key }}
|
||||
{{- $password = index $secretData .key | b64dec }}
|
||||
{{- else if not (eq .failOnNew false) }}
|
||||
{{- $password = index $secretData .key | quote }}
|
||||
{{- else if $failOnNew }}
|
||||
{{- printf "\nPASSWORDS ERROR: The secret \"%s\" does not contain the key \"%s\"\n" .secret .key | fail -}}
|
||||
{{- else if $providedPasswordValue }}
|
||||
{{- $password = $providedPasswordValue | toString }}
|
||||
{{- end -}}
|
||||
{{- else if $providedPasswordValue }}
|
||||
{{- $password = $providedPasswordValue | toString }}
|
||||
{{- $password = $providedPasswordValue | toString | b64enc | quote }}
|
||||
{{- else }}
|
||||
|
||||
{{- if .context.Values.enabled }}
|
||||
@@ -123,19 +120,12 @@ The order in which this function returns a secret password:
|
||||
{{- $subStr := list (lower (randAlpha 1)) (randNumeric 1) (upper (randAlpha 1)) | join "_" }}
|
||||
{{- $password = randAscii $passwordLength }}
|
||||
{{- $password = regexReplaceAllLiteral "\\W" $password "@" | substr 5 $passwordLength }}
|
||||
{{- $password = printf "%s%s" $subStr $password | toString | shuffle }}
|
||||
{{- $password = printf "%s%s" $subStr $password | toString | shuffle | b64enc | quote }}
|
||||
{{- else }}
|
||||
{{- $password = randAlphaNum $passwordLength }}
|
||||
{{- $password = randAlphaNum $passwordLength | b64enc | quote }}
|
||||
{{- end }}
|
||||
{{- end -}}
|
||||
{{- if not .skipB64enc }}
|
||||
{{- $password = $password | b64enc }}
|
||||
{{- end -}}
|
||||
{{- if .skipQuote -}}
|
||||
{{- printf "%s" $password -}}
|
||||
{{- else -}}
|
||||
{{- printf "%s" $password | quote -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
|
||||
@@ -13,70 +13,7 @@ Usage:
|
||||
|
||||
{{- if and (contains "bitnami/" .repository) (not (.tag | toString | regexFind "-r\\d+$|sha256:")) }}
|
||||
WARNING: Rolling tag detected ({{ .repository }}:{{ .tag }}), please note that it is strongly recommended to avoid using rolling tags in a production environment.
|
||||
+info https://docs.bitnami.com/tutorials/understand-rolling-tags-containers
|
||||
+info https://docs.bitnami.com/containers/how-to/understand-rolling-tags-containers/
|
||||
{{- end }}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Warning about not setting the resource object in all deployments.
|
||||
Usage:
|
||||
{{ include "common.warnings.resources" (dict "sections" (list "path1" "path2") context $) }}
|
||||
Example:
|
||||
{{- include "common.warnings.resources" (dict "sections" (list "csiProvider.provider" "server" "volumePermissions" "") "context" $) }}
|
||||
The list in the example assumes that the following values exist:
|
||||
- csiProvider.provider.resources
|
||||
- server.resources
|
||||
- volumePermissions.resources
|
||||
- resources
|
||||
*/}}
|
||||
{{- define "common.warnings.resources" -}}
|
||||
{{- $values := .context.Values -}}
|
||||
{{- $printMessage := false -}}
|
||||
{{ $affectedSections := list -}}
|
||||
{{- range .sections -}}
|
||||
{{- if eq . "" -}}
|
||||
{{/* Case where the resources section is at the root (one main deployment in the chart) */}}
|
||||
{{- if not (index $values "resources") -}}
|
||||
{{- $affectedSections = append $affectedSections "resources" -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- else -}}
|
||||
{{/* Case where the are multiple resources sections (more than one main deployment in the chart) */}}
|
||||
{{- $keys := split "." . -}}
|
||||
{{/* We iterate through the different levels until arriving to the resource section. Example: a.b.c.resources */}}
|
||||
{{- $section := $values -}}
|
||||
{{- range $keys -}}
|
||||
{{- $section = index $section . -}}
|
||||
{{- end -}}
|
||||
{{- if not (index $section "resources") -}}
|
||||
{{/* If the section has enabled=false or replicaCount=0, do not include it */}}
|
||||
{{- if and (hasKey $section "enabled") -}}
|
||||
{{- if index $section "enabled" -}}
|
||||
{{/* enabled=true */}}
|
||||
{{- $affectedSections = append $affectedSections (printf "%s.resources" .) -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- else if and (hasKey $section "replicaCount") -}}
|
||||
{{/* We need a casting to int because number 0 is not treated as an int by default */}}
|
||||
{{- if (gt (index $section "replicaCount" | int) 0) -}}
|
||||
{{/* replicaCount > 0 */}}
|
||||
{{- $affectedSections = append $affectedSections (printf "%s.resources" .) -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- else -}}
|
||||
{{/* Default case, add it to the affected sections */}}
|
||||
{{- $affectedSections = append $affectedSections (printf "%s.resources" .) -}}
|
||||
{{- $printMessage = true -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- if $printMessage }}
|
||||
|
||||
WARNING: There are "resources" sections in the chart not set. Using "resourcesPreset" is not recommended for production. For production installations, please set the following values according to your workload needs:
|
||||
{{- range $affectedSections }}
|
||||
- {{ . }}
|
||||
{{- end }}
|
||||
+info https://kubernetes.io/docs/concepts/configuration/manage-resources-containers/
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
Binary file not shown.
|
After Width: | Height: | Size: 11 KiB |
Binary file not shown.
|
After Width: | Height: | Size: 9.5 KiB |
@@ -12,11 +12,11 @@ The chart has been deployed in diagnostic mode. All probes have been disabled an
|
||||
|
||||
Get the list of pods by executing:
|
||||
|
||||
kubectl get pods --namespace {{ include "common.names.namespace" . }} -l app.kubernetes.io/instance={{ .Release.Name }}
|
||||
kubectl get pods --namespace {{ .Release.Namespace }} -l app.kubernetes.io/instance={{ .Release.Name }}
|
||||
|
||||
Access the pod you want to debug by executing
|
||||
|
||||
kubectl exec --namespace {{ include "common.names.namespace" . }} -ti <NAME OF THE POD> -- bash
|
||||
kubectl exec --namespace {{ .Release.Namespace }} -ti <NAME OF THE POD> -- bash
|
||||
|
||||
In order to replicate the container startup scripts execute this command:
|
||||
|
||||
@@ -53,28 +53,12 @@ For Redis Sentinel:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
{{- if and .Values.auth.usePasswordFiles (not .Values.auth.usePasswordFileFromSecret) (or (empty .Values.master.initContainers) (empty .Values.replica.initContainers)) }}
|
||||
|
||||
-------------------------------------------------------------------------------
|
||||
WARNING
|
||||
|
||||
By specifying ".Values.auth.usePasswordFiles=true" and ".Values.auth.usePasswordFileFromSecret=false"
|
||||
Redis is expecting that the password is mounted as a file in each pod
|
||||
(by default in /opt/bitnami/redis/secrets/redis-password)
|
||||
|
||||
Ensure that you specify the respective initContainers in
|
||||
both .Values.master.initContainers and .Values.replica.initContainers
|
||||
in order to populate the contents of this file.
|
||||
|
||||
-------------------------------------------------------------------------------
|
||||
{{- end }}
|
||||
|
||||
{{- if eq .Values.architecture "replication" }}
|
||||
{{- if .Values.sentinel.enabled }}
|
||||
|
||||
Redis® can be accessed via port {{ .Values.sentinel.service.ports.redis }} on the following DNS name from within your cluster:
|
||||
|
||||
{{ template "common.names.fullname" . }}.{{ include "common.names.namespace" . }}.svc.{{ .Values.clusterDomain }} for read only operations
|
||||
{{ template "common.names.fullname" . }}.{{ .Release.Namespace }}.svc.{{ .Values.clusterDomain }} for read only operations
|
||||
|
||||
For read/write operations, first access the Redis® Sentinel cluster, which is available in port {{ .Values.sentinel.service.ports.sentinel }} using the same domain name above.
|
||||
|
||||
@@ -82,15 +66,15 @@ For read/write operations, first access the Redis® Sentinel cluster, which i
|
||||
|
||||
Redis® can be accessed on the following DNS names from within your cluster:
|
||||
|
||||
{{ printf "%s-master.%s.svc.%s" (include "common.names.fullname" .) (include "common.names.namespace" . ) .Values.clusterDomain }} for read/write operations (port {{ .Values.master.service.ports.redis }})
|
||||
{{ printf "%s-replicas.%s.svc.%s" (include "common.names.fullname" .) (include "common.names.namespace" . ) .Values.clusterDomain }} for read-only operations (port {{ .Values.replica.service.ports.redis }})
|
||||
{{ printf "%s-master.%s.svc.%s" (include "common.names.fullname" .) .Release.Namespace .Values.clusterDomain }} for read/write operations (port {{ .Values.master.service.ports.redis }})
|
||||
{{ printf "%s-replicas.%s.svc.%s" (include "common.names.fullname" .) .Release.Namespace .Values.clusterDomain }} for read-only operations (port {{ .Values.replica.service.ports.redis }})
|
||||
|
||||
{{- end }}
|
||||
{{- else }}
|
||||
|
||||
Redis® can be accessed via port {{ .Values.master.service.ports.redis }} on the following DNS name from within your cluster:
|
||||
|
||||
{{ template "common.names.fullname" . }}-master.{{ include "common.names.namespace" . }}.svc.{{ .Values.clusterDomain }}
|
||||
{{ template "common.names.fullname" . }}-master.{{ .Release.Namespace }}.svc.{{ .Values.clusterDomain }}
|
||||
|
||||
{{- end }}
|
||||
|
||||
@@ -98,7 +82,7 @@ Redis® can be accessed via port {{ .Values.master.service.ports.redis }} on
|
||||
|
||||
To get your password run:
|
||||
|
||||
export REDIS_PASSWORD=$(kubectl get secret --namespace {{ include "common.names.namespace" . }} {{ template "redis.secretName" . }} -o jsonpath="{.data.redis-password}" | base64 -d)
|
||||
export REDIS_PASSWORD=$(kubectl get secret --namespace {{ .Release.Namespace }} {{ template "redis.secretName" . }} -o jsonpath="{.data.redis-password}" | base64 -d)
|
||||
|
||||
{{- end }}
|
||||
|
||||
@@ -106,15 +90,15 @@ To connect to your Redis® server:
|
||||
|
||||
1. Run a Redis® pod that you can use as a client:
|
||||
|
||||
kubectl run --namespace {{ include "common.names.namespace" . }} redis-client --restart='Never' {{ if .Values.auth.enabled }} --env REDIS_PASSWORD=$REDIS_PASSWORD {{ end }} --image {{ template "redis.image" . }} --command -- sleep infinity
|
||||
kubectl run --namespace {{ .Release.Namespace }} redis-client --restart='Never' {{ if .Values.auth.enabled }} --env REDIS_PASSWORD=$REDIS_PASSWORD {{ end }} --image {{ template "redis.image" . }} --command -- sleep infinity
|
||||
|
||||
{{- if .Values.tls.enabled }}
|
||||
|
||||
Copy your TLS certificates to the pod:
|
||||
|
||||
kubectl cp --namespace {{ include "common.names.namespace" . }} /path/to/client.cert redis-client:/tmp/client.cert
|
||||
kubectl cp --namespace {{ include "common.names.namespace" . }} /path/to/client.key redis-client:/tmp/client.key
|
||||
kubectl cp --namespace {{ include "common.names.namespace" . }} /path/to/CA.cert redis-client:/tmp/CA.cert
|
||||
kubectl cp --namespace {{ .Release.Namespace }} /path/to/client.cert redis-client:/tmp/client.cert
|
||||
kubectl cp --namespace {{ .Release.Namespace }} /path/to/client.key redis-client:/tmp/client.key
|
||||
kubectl cp --namespace {{ .Release.Namespace }} /path/to/CA.cert redis-client:/tmp/CA.cert
|
||||
|
||||
{{- end }}
|
||||
|
||||
@@ -122,7 +106,7 @@ To connect to your Redis® server:
|
||||
|
||||
kubectl exec --tty -i redis-client \
|
||||
{{- if and (.Values.networkPolicy.enabled) (not .Values.networkPolicy.allowExternal) }}--labels="{{ template "common.names.fullname" . }}-client=true" \{{- end }}
|
||||
--namespace {{ include "common.names.namespace" . }} -- bash
|
||||
--namespace {{ .Release.Namespace }} -- bash
|
||||
|
||||
2. Connect using the Redis® CLI:
|
||||
|
||||
@@ -149,42 +133,42 @@ To connect to your database from outside the cluster execute the following comma
|
||||
{{- if and (eq .Values.architecture "replication") .Values.sentinel.enabled }}
|
||||
{{- if contains "NodePort" .Values.sentinel.service.type }}
|
||||
|
||||
export NODE_IP=$(kubectl get nodes --namespace {{ include "common.names.namespace" . }} -o jsonpath="{.items[0].status.addresses[0].address}")
|
||||
export NODE_PORT=$(kubectl get --namespace {{ include "common.names.namespace" . }} -o jsonpath="{.spec.ports[0].nodePort}" services {{ template "common.names.fullname" . }})
|
||||
export NODE_IP=$(kubectl get nodes --namespace {{ .Release.Namespace }} -o jsonpath="{.items[0].status.addresses[0].address}")
|
||||
export NODE_PORT=$(kubectl get --namespace {{ .Release.Namespace }} -o jsonpath="{.spec.ports[0].nodePort}" services {{ template "common.names.fullname" . }})
|
||||
{{ if .Values.auth.enabled }}REDISCLI_AUTH="$REDIS_PASSWORD" {{ end }}redis-cli -h $NODE_IP -p $NODE_PORT {{- if .Values.tls.enabled }} --tls --cert /tmp/client.cert --key /tmp/client.key --cacert /tmp/CA.cert{{ end }}
|
||||
|
||||
{{- else if contains "LoadBalancer" .Values.sentinel.service.type }}
|
||||
|
||||
NOTE: It may take a few minutes for the LoadBalancer IP to be available.
|
||||
Watch the status with: 'kubectl get svc --namespace {{ include "common.names.namespace" . }} -w {{ template "common.names.fullname" . }}'
|
||||
Watch the status with: 'kubectl get svc --namespace {{ .Release.Namespace }} -w {{ template "common.names.fullname" . }}'
|
||||
|
||||
export SERVICE_IP=$(kubectl get svc --namespace {{ include "common.names.namespace" . }} {{ template "common.names.fullname" . }} --template "{{ "{{ range (index .status.loadBalancer.ingress 0) }}{{ . }}{{ end }}" }}")
|
||||
export SERVICE_IP=$(kubectl get svc --namespace {{ .Release.Namespace }} {{ template "common.names.fullname" . }} --template "{{ "{{ range (index .status.loadBalancer.ingress 0) }}{{ . }}{{ end }}" }}")
|
||||
{{ if .Values.auth.enabled }}REDISCLI_AUTH="$REDIS_PASSWORD" {{ end }}redis-cli -h $SERVICE_IP -p {{ .Values.sentinel.service.ports.redis }} {{- if .Values.tls.enabled }} --tls --cert /tmp/client.cert --key /tmp/client.key --cacert /tmp/CA.cert{{ end }}
|
||||
|
||||
{{- else if contains "ClusterIP" .Values.sentinel.service.type }}
|
||||
|
||||
kubectl port-forward --namespace {{ include "common.names.namespace" . }} svc/{{ template "common.names.fullname" . }} {{ .Values.sentinel.service.ports.redis }}:{{ .Values.sentinel.service.ports.redis }} &
|
||||
kubectl port-forward --namespace {{ .Release.Namespace }} svc/{{ template "common.names.fullname" . }} {{ .Values.sentinel.service.ports.redis }}:{{ .Values.sentinel.service.ports.redis }} &
|
||||
{{ if .Values.auth.enabled }}REDISCLI_AUTH="$REDIS_PASSWORD" {{ end }}redis-cli -h 127.0.0.1 -p {{ .Values.sentinel.service.ports.redis }} {{- if .Values.tls.enabled }} --tls --cert /tmp/client.cert --key /tmp/client.key --cacert /tmp/CA.cert{{ end }}
|
||||
|
||||
{{- end }}
|
||||
{{- else }}
|
||||
{{- if contains "NodePort" .Values.master.service.type }}
|
||||
|
||||
export NODE_IP=$(kubectl get nodes --namespace {{ include "common.names.namespace" . }} -o jsonpath="{.items[0].status.addresses[0].address}")
|
||||
export NODE_PORT=$(kubectl get --namespace {{ include "common.names.namespace" . }} -o jsonpath="{.spec.ports[0].nodePort}" services {{ printf "%s-master" (include "common.names.fullname" .) }})
|
||||
export NODE_IP=$(kubectl get nodes --namespace {{ .Release.Namespace }} -o jsonpath="{.items[0].status.addresses[0].address}")
|
||||
export NODE_PORT=$(kubectl get --namespace {{ .Release.Namespace }} -o jsonpath="{.spec.ports[0].nodePort}" services {{ printf "%s-master" (include "common.names.fullname" .) }})
|
||||
{{ if .Values.auth.enabled }}REDISCLI_AUTH="$REDIS_PASSWORD" {{ end }}redis-cli -h $NODE_IP -p $NODE_PORT {{- if .Values.tls.enabled }} --tls --cert /tmp/client.cert --key /tmp/client.key --cacert /tmp/CA.cert{{ end }}
|
||||
|
||||
{{- else if contains "LoadBalancer" .Values.master.service.type }}
|
||||
|
||||
NOTE: It may take a few minutes for the LoadBalancer IP to be available.
|
||||
Watch the status with: 'kubectl get svc --namespace {{ include "common.names.namespace" . }} -w {{ template "common.names.fullname" . }}'
|
||||
Watch the status with: 'kubectl get svc --namespace {{ .Release.Namespace }} -w {{ template "common.names.fullname" . }}'
|
||||
|
||||
export SERVICE_IP=$(kubectl get svc --namespace {{ include "common.names.namespace" . }} {{ printf "%s-master" (include "common.names.fullname" .) }} --template "{{ "{{ range (index .status.loadBalancer.ingress 0) }}{{ . }}{{ end }}" }}")
|
||||
export SERVICE_IP=$(kubectl get svc --namespace {{ .Release.Namespace }} {{ printf "%s-master" (include "common.names.fullname" .) }} --template "{{ "{{ range (index .status.loadBalancer.ingress 0) }}{{ . }}{{ end }}" }}")
|
||||
{{ if .Values.auth.enabled }}REDISCLI_AUTH="$REDIS_PASSWORD" {{ end }}redis-cli -h $SERVICE_IP -p {{ .Values.master.service.ports.redis }} {{- if .Values.tls.enabled }} --tls --cert /tmp/client.cert --key /tmp/client.key --cacert /tmp/CA.cert{{ end }}
|
||||
|
||||
{{- else if contains "ClusterIP" .Values.master.service.type }}
|
||||
|
||||
kubectl port-forward --namespace {{ include "common.names.namespace" . }} svc/{{ printf "%s-master" (include "common.names.fullname" .) }} {{ .Values.master.service.ports.redis }}:{{ .Values.master.service.ports.redis }} &
|
||||
kubectl port-forward --namespace {{ .Release.Namespace }} svc/{{ printf "%s-master" (include "common.names.fullname" .) }} {{ .Values.master.service.ports.redis }}:{{ .Values.master.service.ports.redis }} &
|
||||
{{ if .Values.auth.enabled }}REDISCLI_AUTH="$REDIS_PASSWORD" {{ end }}redis-cli -h 127.0.0.1 -p {{ .Values.master.service.ports.redis }} {{- if .Values.tls.enabled }} --tls --cert /tmp/client.cert --key /tmp/client.key --cacert /tmp/CA.cert{{ end }}
|
||||
|
||||
{{- end }}
|
||||
@@ -205,4 +189,3 @@ No need to upgrade, ports and nodeports have been set from values
|
||||
YOU NEED TO PERFORM AN UPGRADE FOR THE SERVICES AND WORKLOAD TO BE CREATED
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- include "common.warnings.resources" (dict "sections" (list "master" "metrics" "replica" "sentinel" "sysctl" "volumePermissions") "context" $) }}
|
||||
|
||||
@@ -33,13 +33,6 @@ Return the proper image name (for the init container volume-permissions image)
|
||||
{{ include "common.images.image" (dict "imageRoot" .Values.volumePermissions.image "global" .Values.global) }}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return kubectl image
|
||||
*/}}
|
||||
{{- define "redis.kubectl.image" -}}
|
||||
{{ include "common.images.image" (dict "imageRoot" .Values.kubectl.image "global" .Values.global) }}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Return sysctl image
|
||||
*/}}
|
||||
@@ -247,7 +240,7 @@ Return Redis® password
|
||||
{{- else if not (empty .Values.auth.password) -}}
|
||||
{{- .Values.auth.password -}}
|
||||
{{- else -}}
|
||||
{{- include "getValueFromSecret" (dict "Namespace" (include "common.names.namespace" .) "Name" (include "redis.secretName" .) "Length" 10 "Key" (include "redis.secretPasswordKey" .)) -}}
|
||||
{{- include "getValueFromSecret" (dict "Namespace" .Release.Namespace "Name" (include "redis.secretName" .) "Length" 10 "Key" (include "redis.secretPasswordKey" .)) -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
{{- end }}
|
||||
@@ -268,7 +261,6 @@ Compile all warnings into a single message, and call fail.
|
||||
{{- $messages := append $messages (include "redis.validateValues.architecture" .) -}}
|
||||
{{- $messages := append $messages (include "redis.validateValues.podSecurityPolicy.create" .) -}}
|
||||
{{- $messages := append $messages (include "redis.validateValues.tls" .) -}}
|
||||
{{- $messages := append $messages (include "redis.validateValues.createMaster" .) -}}
|
||||
{{- $messages := without $messages "" -}}
|
||||
{{- $message := join "\n" $messages -}}
|
||||
|
||||
@@ -320,16 +312,6 @@ redis: tls.enabled
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/* Validate values of Redis® - master service enabled */}}
|
||||
{{- define "redis.validateValues.createMaster" -}}
|
||||
{{- if and .Values.sentinel.service.createMaster (or (not .Values.rbac.create) (not .Values.replica.automountServiceAccountToken) (not .Values.serviceAccount.create)) }}
|
||||
redis: sentinel.service.createMaster
|
||||
In order to redirect requests only to the master pod via the service, you also need to
|
||||
create rbac and serviceAccount. In addition, you need to enable
|
||||
replica.automountServiceAccountToken.
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/* Define the suffix utilized for external-dns */}}
|
||||
{{- define "redis.externalDNS.suffix" -}}
|
||||
{{ printf "%s.%s" (include "common.names.fullname" .) .Values.useExternalDNS.suffix }}
|
||||
|
||||
@@ -8,7 +8,7 @@ apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: {{ printf "%s-configuration" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.commonAnnotations }}
|
||||
annotations: {{- include "common.tplvalues.render" ( dict "value" .Values.commonAnnotations "context" $ ) | nindent 4 }}
|
||||
@@ -48,13 +48,10 @@ data:
|
||||
sentinel.conf: |-
|
||||
dir "/tmp"
|
||||
port {{ .Values.sentinel.containerPorts.sentinel }}
|
||||
sentinel monitor {{ .Values.sentinel.masterSet }} {{ template "common.names.fullname" . }}-node-0.{{ template "common.names.fullname" . }}-headless.{{ include "common.names.namespace" . }}.svc.{{ .Values.clusterDomain }} {{ .Values.sentinel.service.ports.redis }} {{ .Values.sentinel.quorum }}
|
||||
sentinel monitor {{ .Values.sentinel.masterSet }} {{ template "common.names.fullname" . }}-node-0.{{ template "common.names.fullname" . }}-headless.{{ .Release.Namespace }}.svc.{{ .Values.clusterDomain }} {{ .Values.sentinel.service.ports.redis }} {{ .Values.sentinel.quorum }}
|
||||
sentinel down-after-milliseconds {{ .Values.sentinel.masterSet }} {{ .Values.sentinel.downAfterMilliseconds }}
|
||||
sentinel failover-timeout {{ .Values.sentinel.masterSet }} {{ .Values.sentinel.failoverTimeout }}
|
||||
sentinel parallel-syncs {{ .Values.sentinel.masterSet }} {{ .Values.sentinel.parallelSyncs }}
|
||||
{{- if .Values.sentinel.service.createMaster}}
|
||||
sentinel client-reconfig-script {{ .Values.sentinel.masterSet }} /opt/bitnami/scripts/start-scripts/push-master-label.sh
|
||||
{{- end }}
|
||||
# User-supplied sentinel configuration:
|
||||
{{- if .Values.sentinel.configuration }}
|
||||
{{- include "common.tplvalues.render" ( dict "value" .Values.sentinel.configuration "context" $ ) | nindent 4 }}
|
||||
|
||||
@@ -7,16 +7,14 @@ apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: {{ printf "%s-headless" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if or .Values.sentinel.service.headless.annotations .Values.commonAnnotations (include "redis.externalDNS.annotations" .) }}
|
||||
annotations:
|
||||
{{- if or .Values.sentinel.service.headless.annotations .Values.commonAnnotations }}
|
||||
{{- $annotations := include "common.tplvalues.merge" ( dict "values" ( list .Values.sentinel.service.headless.annotations .Values.commonAnnotations ) "context" . ) }}
|
||||
{{- include "common.tplvalues.render" ( dict "value" $annotations "context" $) | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- include "redis.externalDNS.annotations" . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
type: ClusterIP
|
||||
clusterIP: None
|
||||
|
||||
@@ -7,7 +7,7 @@ apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: {{ printf "%s-health" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.commonAnnotations }}
|
||||
annotations: {{- include "common.tplvalues.render" ( dict "value" .Values.commonAnnotations "context" $ ) | nindent 4 }}
|
||||
|
||||
@@ -9,7 +9,7 @@ apiVersion: {{ include "common.capabilities.statefulset.apiVersion" . }}
|
||||
kind: {{ .Values.master.kind }}
|
||||
metadata:
|
||||
name: {{ printf "%s-master" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
app.kubernetes.io/component: master
|
||||
{{- if .Values.commonAnnotations }}
|
||||
@@ -62,10 +62,10 @@ spec:
|
||||
hostAliases: {{- include "common.tplvalues.render" (dict "value" .Values.master.hostAliases "context" $) | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.master.podSecurityContext.enabled }}
|
||||
securityContext: {{- include "common.compatibility.renderSecurityContext" (dict "secContext" .Values.master.podSecurityContext "context" $) | nindent 8 }}
|
||||
securityContext: {{- omit .Values.master.podSecurityContext "enabled" | toYaml | nindent 8 }}
|
||||
{{- end }}
|
||||
serviceAccountName: {{ template "redis.masterServiceAccountName" . }}
|
||||
automountServiceAccountToken: {{ .Values.master.automountServiceAccountToken }}
|
||||
automountServiceAccountToken: {{ .Values.master.serviceAccount.automountServiceAccountToken }}
|
||||
{{- if .Values.master.priorityClassName }}
|
||||
priorityClassName: {{ .Values.master.priorityClassName | quote }}
|
||||
{{- end }}
|
||||
@@ -108,7 +108,7 @@ spec:
|
||||
lifecycle: {{- include "common.tplvalues.render" (dict "value" .Values.master.lifecycleHooks "context" $) | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.master.containerSecurityContext.enabled }}
|
||||
securityContext: {{- include "common.compatibility.renderSecurityContext" (dict "secContext" .Values.master.containerSecurityContext "context" $) | nindent 12 }}
|
||||
securityContext: {{- omit .Values.master.containerSecurityContext "enabled" | toYaml | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.diagnosticMode.enabled }}
|
||||
command: {{- include "common.tplvalues.render" (dict "value" .Values.diagnosticMode.command "context" $) | nindent 12 }}
|
||||
@@ -226,8 +226,6 @@ spec:
|
||||
{{- end }}
|
||||
{{- if .Values.master.resources }}
|
||||
resources: {{- toYaml .Values.master.resources | nindent 12 }}
|
||||
{{- else if ne .Values.master.resourcesPreset "none" }}
|
||||
resources: {{- include "common.resources.preset" (dict "type" .Values.master.resourcesPreset) | nindent 12 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: start-scripts
|
||||
@@ -247,12 +245,10 @@ spec:
|
||||
{{- end }}
|
||||
- name: config
|
||||
mountPath: /opt/bitnami/redis/mounted-etc
|
||||
- name: empty-dir
|
||||
- name: redis-tmp-conf
|
||||
mountPath: /opt/bitnami/redis/etc/
|
||||
subPath: app-conf-dir
|
||||
- name: empty-dir
|
||||
- name: tmp
|
||||
mountPath: /tmp
|
||||
subPath: tmp-dir
|
||||
{{- if .Values.tls.enabled }}
|
||||
- name: redis-certificates
|
||||
mountPath: /opt/bitnami/redis/certs
|
||||
@@ -266,7 +262,7 @@ spec:
|
||||
image: {{ include "redis.metrics.image" . }}
|
||||
imagePullPolicy: {{ .Values.metrics.image.pullPolicy | quote }}
|
||||
{{- if .Values.metrics.containerSecurityContext.enabled }}
|
||||
securityContext: {{- include "common.compatibility.renderSecurityContext" (dict "secContext" .Values.metrics.containerSecurityContext "context" $) | nindent 12 }}
|
||||
securityContext: {{- omit .Values.metrics.containerSecurityContext "enabled" | toYaml | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.diagnosticMode.enabled }}
|
||||
command: {{- include "common.tplvalues.render" (dict "value" .Values.diagnosticMode.command "context" $) | nindent 12 }}
|
||||
@@ -288,8 +284,6 @@ spec:
|
||||
env:
|
||||
- name: REDIS_ALIAS
|
||||
value: {{ template "common.names.fullname" . }}
|
||||
- name: REDIS_EXPORTER_WEB_LISTEN_ADDRESS
|
||||
value: {{ printf ":%v" .Values.metrics.containerPorts.http }}
|
||||
{{- if .Values.auth.enabled }}
|
||||
- name: REDIS_USER
|
||||
value: default
|
||||
@@ -318,7 +312,7 @@ spec:
|
||||
{{- end }}
|
||||
ports:
|
||||
- name: metrics
|
||||
containerPort: {{ .Values.metrics.containerPorts.http }}
|
||||
containerPort: 9121
|
||||
{{- if not .Values.diagnosticMode.enabled }}
|
||||
{{- if .Values.metrics.customStartupProbe }}
|
||||
startupProbe: {{- include "common.tplvalues.render" (dict "value" .Values.metrics.customStartupProbe "context" $) | nindent 12 }}
|
||||
@@ -345,13 +339,8 @@ spec:
|
||||
{{- end }}
|
||||
{{- if .Values.metrics.resources }}
|
||||
resources: {{- toYaml .Values.metrics.resources | nindent 12 }}
|
||||
{{- else if ne .Values.metrics.resourcesPreset "none" }}
|
||||
resources: {{- include "common.resources.preset" (dict "type" .Values.metrics.resourcesPreset) | nindent 12 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: empty-dir
|
||||
mountPath: /tmp
|
||||
subPath: app-tmp-dir
|
||||
{{- if .Values.auth.usePasswordFiles }}
|
||||
- name: redis-password
|
||||
mountPath: /secrets/
|
||||
@@ -394,13 +383,8 @@ spec:
|
||||
{{- end }}
|
||||
{{- if .Values.volumePermissions.resources }}
|
||||
resources: {{- toYaml .Values.volumePermissions.resources | nindent 12 }}
|
||||
{{- else if ne .Values.volumePermissions.resourcesPreset "none" }}
|
||||
resources: {{- include "common.resources.preset" (dict "type" .Values.volumePermissions.resourcesPreset) | nindent 12 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: empty-dir
|
||||
mountPath: /tmp
|
||||
subPath: tmp-dir
|
||||
- name: redis-data
|
||||
mountPath: {{ .Values.master.persistence.path }}
|
||||
{{- if .Values.master.persistence.subPath }}
|
||||
@@ -421,14 +405,9 @@ spec:
|
||||
{{- end }}
|
||||
{{- if .Values.sysctl.resources }}
|
||||
resources: {{- toYaml .Values.sysctl.resources | nindent 12 }}
|
||||
{{- else if ne .Values.sysctl.resourcesPreset "none" }}
|
||||
resources: {{- include "common.resources.preset" (dict "type" .Values.sysctl.resourcesPreset) | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.sysctl.mountHostSys }}
|
||||
volumeMounts:
|
||||
- name: empty-dir
|
||||
mountPath: /tmp
|
||||
subPath: tmp-dir
|
||||
- name: host-sys
|
||||
mountPath: /host-sys
|
||||
{{- end }}
|
||||
@@ -445,15 +424,11 @@ spec:
|
||||
defaultMode: 0755
|
||||
{{- if .Values.auth.usePasswordFiles }}
|
||||
- name: redis-password
|
||||
{{ if .Values.auth.usePasswordFileFromSecret }}
|
||||
secret:
|
||||
secretName: {{ template "redis.secretName" . }}
|
||||
items:
|
||||
- key: {{ template "redis.secretPasswordKey" . }}
|
||||
path: redis-password
|
||||
{{- else }}
|
||||
emptyDir: {}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- name: config
|
||||
configMap:
|
||||
@@ -463,7 +438,19 @@ spec:
|
||||
hostPath:
|
||||
path: /sys
|
||||
{{- end }}
|
||||
- name: empty-dir
|
||||
- name: redis-tmp-conf
|
||||
{{- if or .Values.master.persistence.medium .Values.master.persistence.sizeLimit }}
|
||||
emptyDir:
|
||||
{{- if .Values.master.persistence.medium }}
|
||||
medium: {{ .Values.master.persistence.medium | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.master.persistence.sizeLimit }}
|
||||
sizeLimit: {{ .Values.master.persistence.sizeLimit | quote }}
|
||||
{{- end }}
|
||||
{{- else }}
|
||||
emptyDir: {}
|
||||
{{- end }}
|
||||
- name: tmp
|
||||
{{- if or .Values.master.persistence.medium .Values.master.persistence.sizeLimit }}
|
||||
emptyDir:
|
||||
{{- if .Values.master.persistence.medium }}
|
||||
|
||||
@@ -8,7 +8,7 @@ apiVersion: policy/v1beta1
|
||||
kind: PodSecurityPolicy
|
||||
metadata:
|
||||
name: {{ printf "%s-master" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.commonAnnotations }}
|
||||
annotations: {{- include "common.tplvalues.render" ( dict "value" .Values.commonAnnotations "context" $ ) | nindent 4 }}
|
||||
|
||||
@@ -8,7 +8,7 @@ kind: PersistentVolumeClaim
|
||||
apiVersion: v1
|
||||
metadata:
|
||||
name: {{ printf "redis-data-%s-master" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
{{- $labels := include "common.tplvalues.merge" ( dict "values" ( list .Values.master.persistence.labels .Values.commonLabels ) "context" . ) }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" $labels "context" $ ) | nindent 4 }}
|
||||
app.kubernetes.io/component: master
|
||||
|
||||
@@ -8,7 +8,7 @@ apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: {{ printf "%s-master" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
app.kubernetes.io/component: master
|
||||
{{- if or .Values.master.service.annotations .Values.commonAnnotations }}
|
||||
@@ -26,9 +26,6 @@ spec:
|
||||
{{- if and (eq .Values.master.service.type "LoadBalancer") (not (empty .Values.master.service.loadBalancerIP)) }}
|
||||
loadBalancerIP: {{ .Values.master.service.loadBalancerIP }}
|
||||
{{- end }}
|
||||
{{- if and (eq .Values.master.service.type "LoadBalancer") .Values.master.service.loadBalancerClass }}
|
||||
loadBalancerClass: {{ .Values.master.service.loadBalancerClass }}
|
||||
{{- end }}
|
||||
{{- if and (eq .Values.master.service.type "LoadBalancer") (not (empty .Values.master.service.loadBalancerSourceRanges)) }}
|
||||
loadBalancerSourceRanges: {{ toYaml .Values.master.service.loadBalancerSourceRanges | nindent 4 }}
|
||||
{{- end }}
|
||||
|
||||
@@ -3,13 +3,13 @@ Copyright VMware, Inc.
|
||||
SPDX-License-Identifier: APACHE-2.0
|
||||
*/}}
|
||||
|
||||
{{- if and .Values.master.serviceAccount.create (or (not (eq .Values.architecture "replication")) (not .Values.sentinel.enabled)) }}
|
||||
{{- if .Values.master.serviceAccount.create }}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
automountServiceAccountToken: {{ .Values.master.serviceAccount.automountServiceAccountToken }}
|
||||
metadata:
|
||||
name: {{ template "redis.masterServiceAccountName" . }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if or .Values.master.serviceAccount.annotations .Values.commonAnnotations }}
|
||||
{{- $annotations := include "common.tplvalues.merge" ( dict "values" ( list .Values.master.serviceAccount.annotations .Values.commonAnnotations ) "context" . ) }}
|
||||
|
||||
@@ -3,12 +3,12 @@ Copyright VMware, Inc.
|
||||
SPDX-License-Identifier: APACHE-2.0
|
||||
*/}}
|
||||
|
||||
{{- if and .Values.metrics.enabled .Values.metrics.service.enabled }}
|
||||
{{- if .Values.metrics.enabled }}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
name: {{ printf "%s-metrics" (include "common.names.fullname" .) }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
app.kubernetes.io/component: metrics
|
||||
{{- if or .Values.metrics.service.annotations .Values.commonAnnotations }}
|
||||
@@ -26,15 +26,12 @@ spec:
|
||||
{{- if and (eq .Values.metrics.service.type "LoadBalancer") .Values.metrics.service.loadBalancerIP }}
|
||||
loadBalancerIP: {{ .Values.metrics.service.loadBalancerIP }}
|
||||
{{- end }}
|
||||
{{- if and (eq .Values.metrics.service.type "LoadBalancer") .Values.metrics.service.loadBalancerClass }}
|
||||
loadBalancerClass: {{ .Values.metrics.service.loadBalancerClass }}
|
||||
{{- end }}
|
||||
{{- if and (eq .Values.metrics.service.type "LoadBalancer") .Values.metrics.service.loadBalancerSourceRanges }}
|
||||
loadBalancerSourceRanges: {{- toYaml .Values.metrics.service.loadBalancerSourceRanges | nindent 4 }}
|
||||
{{- end }}
|
||||
ports:
|
||||
- name: http-metrics
|
||||
port: {{ coalesce .Values.metrics.service.ports.http .Values.metrics.service.port }}
|
||||
port: {{ .Values.metrics.service.port }}
|
||||
protocol: TCP
|
||||
targetPort: metrics
|
||||
{{- if .Values.metrics.service.extraPorts }}
|
||||
|
||||
@@ -8,7 +8,7 @@ kind: NetworkPolicy
|
||||
apiVersion: {{ template "networkPolicy.apiVersion" . }}
|
||||
metadata:
|
||||
name: {{ template "common.names.fullname" . }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.commonAnnotations }}
|
||||
annotations: {{- include "common.tplvalues.render" ( dict "value" .Values.commonAnnotations "context" $ ) | nindent 4 }}
|
||||
@@ -18,11 +18,8 @@ spec:
|
||||
matchLabels: {{- include "common.labels.matchLabels" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 6 }}
|
||||
policyTypes:
|
||||
- Ingress
|
||||
{{- if or (eq .Values.architecture "replication") .Values.networkPolicy.extraEgress }}
|
||||
- Egress
|
||||
{{- if .Values.networkPolicy.allowExternalEgress }}
|
||||
egress:
|
||||
- {}
|
||||
{{- else }}
|
||||
egress:
|
||||
{{- if eq .Values.architecture "replication" }}
|
||||
# Allow dns resolution
|
||||
@@ -79,7 +76,7 @@ spec:
|
||||
{{- if .Values.metrics.enabled }}
|
||||
# Allow prometheus scrapes for metrics
|
||||
- ports:
|
||||
- port: {{ .Values.metrics.containerPorts.http }}
|
||||
- port: 9121
|
||||
{{- if not .Values.networkPolicy.metrics.allowExternal }}
|
||||
from:
|
||||
{{- if or .Values.networkPolicy.metrics.ingressNSMatchLabels .Values.networkPolicy.metrics.ingressNSPodMatchLabels }}
|
||||
|
||||
@@ -8,7 +8,7 @@ apiVersion: {{ include "common.capabilities.policy.apiVersion" . }}
|
||||
kind: PodDisruptionBudget
|
||||
metadata:
|
||||
name: {{ template "common.names.fullname" . }}
|
||||
namespace: {{ include "common.names.namespace" . | quote }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.commonAnnotations }}
|
||||
annotations: {{- include "common.tplvalues.render" ( dict "value" .Values.commonAnnotations "context" $ ) | nindent 4 }}
|
||||
|
||||
@@ -8,7 +8,7 @@ apiVersion: monitoring.coreos.com/v1
|
||||
kind: PodMonitor
|
||||
metadata:
|
||||
name: {{ template "common.names.fullname" . }}
|
||||
namespace: {{ default (include "common.names.namespace" .) .Values.metrics.podMonitor.namespace | quote }}
|
||||
namespace: {{ default .Release.Namespace .Values.metrics.podMonitor.namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.metrics.podMonitor.additionalLabels }}
|
||||
{{- include "common.tplvalues.render" (dict "value" .Values.metrics.podMonitor.additionalLabels "context" $) | nindent 4 }}
|
||||
@@ -18,7 +18,7 @@ metadata:
|
||||
{{- end }}
|
||||
spec:
|
||||
podMetricsEndpoints:
|
||||
- port: {{ .Values.metrics.podMonitor.port }}
|
||||
- port: http-metrics
|
||||
{{- if .Values.metrics.podMonitor.interval }}
|
||||
interval: {{ .Values.metrics.podMonitor.interval }}
|
||||
{{- end }}
|
||||
@@ -34,36 +34,6 @@ spec:
|
||||
{{- if .Values.metrics.podMonitor.metricRelabelings }}
|
||||
metricRelabelings: {{- toYaml .Values.metrics.podMonitor.metricRelabelings | nindent 6 }}
|
||||
{{- end }}
|
||||
{{- range .Values.metrics.podMonitor.additionalEndpoints }}
|
||||
- port: {{ .port }}
|
||||
{{- if .interval }}
|
||||
interval: {{ .interval }}
|
||||
{{- end }}
|
||||
{{- if .path }}
|
||||
path: {{ .path }}
|
||||
{{- end }}
|
||||
{{- if .honorLabels }}
|
||||
honorLabels: {{ .honorLabels }}
|
||||
{{- end }}
|
||||
{{- if .relabellings }}
|
||||
relabelings: {{- toYaml .relabellings | nindent 6 }}
|
||||
{{- end }}
|
||||
{{- if .metricRelabelings }}
|
||||
metricRelabelings: {{- toYaml .metricRelabelings | nindent 6 }}
|
||||
{{- end }}
|
||||
{{- if .scrapeTimeout }}
|
||||
scrapeTimeout: {{ .scrapeTimeout }}
|
||||
{{- end }}
|
||||
{{- if .params }}
|
||||
params:
|
||||
{{- range $key, $value := .params }}
|
||||
{{ $key }}:
|
||||
{{- range $value }}
|
||||
- {{ . | quote }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.metrics.serviceMonitor.podTargetLabels }}
|
||||
podTargetLabels: {{- toYaml .Values.metrics.podMonitor.podTargetLabels | nindent 4 }}
|
||||
{{- end }}
|
||||
@@ -75,7 +45,8 @@ spec:
|
||||
{{- end }}
|
||||
namespaceSelector:
|
||||
matchNames:
|
||||
- {{ include "common.names.namespace" . | quote }}
|
||||
- {{ .Release.Namespace }}
|
||||
selector:
|
||||
matchLabels: {{- include "common.labels.matchLabels" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 6 }}
|
||||
app.kubernetes.io/component: metrics
|
||||
{{- end }}
|
||||
|
||||
@@ -8,7 +8,7 @@ apiVersion: monitoring.coreos.com/v1
|
||||
kind: PrometheusRule
|
||||
metadata:
|
||||
name: {{ template "common.names.fullname" . }}
|
||||
namespace: {{ default (include "common.names.namespace" .) .Values.metrics.prometheusRule.namespace | quote }}
|
||||
namespace: {{ default .Release.Namespace .Values.metrics.prometheusRule.namespace | quote }}
|
||||
labels: {{- include "common.labels.standard" ( dict "customLabels" .Values.commonLabels "context" $ ) | nindent 4 }}
|
||||
{{- if .Values.metrics.prometheusRule.additionalLabels }}
|
||||
{{- include "common.tplvalues.render" (dict "value" .Values.metrics.prometheusRule.additionalLabels "context" $) | nindent 4 }}
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user